SOC 2 might sound like a technical hurdle, but its impact reaches far beyond IT teams. Here’s the shocker. Businesses with SOC 2 Type 2 compliance see a 30 percent faster sales cycle and a 60 percent drop in compliance fines. Most people focus on the checklist and audit, but that focus misses the real story. SOC 2 is quickly becoming the gold standard for winning client trust and unlocking business growth—not just meeting another security requirement.
Table of Contents
- What SOC 2 Stands For And Its Purpose
- SOC 2 Trust Principles Explained Simply
- SOC 2 Compliance Checklist And Key Steps
- Benefits Of Achieving SOC 2 For Your Business
Quick Summary
| Takeaway | Explanation |
|---|---|
| SOC 2 Represents a Commitment to Data Security | SOC 2 is a framework that demonstrates an organization's dedication to protecting customer data through rigorous security standards and operational excellence. |
| Five Core Trust Principles Are Essential | The five principles—Security, Availability, Processing Integrity, Confidentiality, and Privacy—provide a detailed roadmap for organizations to manage information security effectively. |
| Achieving SOC 2 Compliance Requires Structured Preparation | The compliance process involves initial assessments, gap analyses, and the implementation of robust security controls, emphasizing thorough documentation and continuous improvement. |
| SOC 2 Certification Enhances Customer Trust | Obtaining SOC 2 compliance signals to clients and stakeholders that an organization maintains high security standards, which is crucial for building trust in today's market. |
| Long-Term Benefits Include Business Growth and Risk Mitigation | SOC 2 compliance not only accelerates sales cycles but also helps in reducing compliance-related fines and enhancing overall security framework within the organization. |
What SOC 2 Stands For and Its Purpose
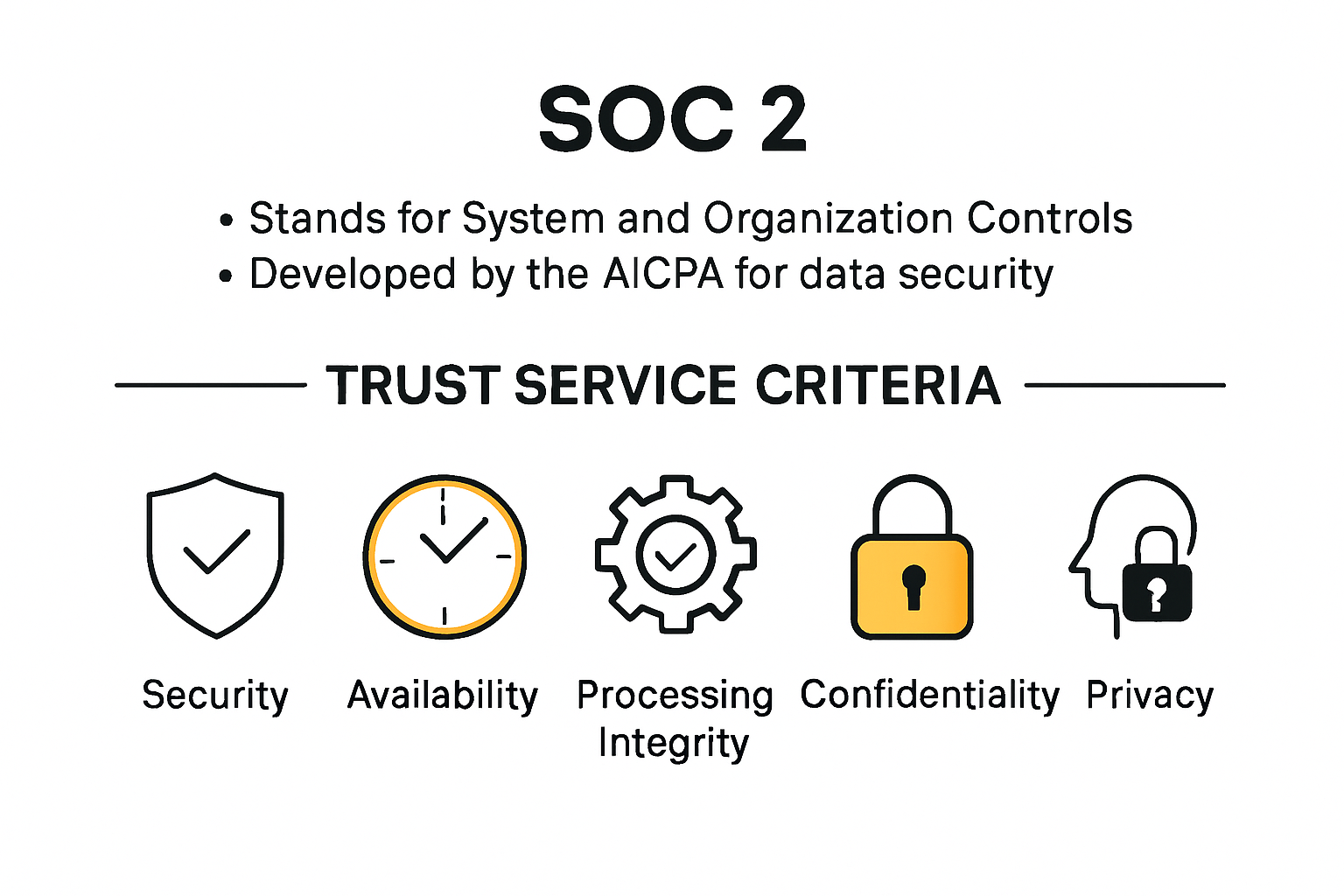
SOC 2 represents a critical framework for organizations seeking to demonstrate their commitment to data security and operational excellence. At its core, SOC 2 stands for System and Organization Controls 2, a comprehensive standard developed by the American Institute of Certified Public Accountants (AICPA) to evaluate how companies protect customer data.
The Fundamental Definition and Origin
The acronym SOC 2 might seem technical, but its purpose is straightforward: establishing trust through rigorous security controls. According to Secureframe, the standard was specifically designed to address the unique challenges of modern cloud-based service organizations. Unlike generic compliance frameworks, SOC 2 focuses on five key trust service criteria that matter most in today's digital ecosystem.
Core Trust Service Criteria
When an organization pursues SOC 2 compliance, they commit to demonstrating excellence across five critical dimensions:
- Security: Protecting systems against unauthorized access and potential breaches
- Availability: Ensuring systems are operational and accessible as promised
- Processing Integrity: Confirming data processing occurs completely, accurately, and in a timely manner
- Confidentiality: Safeguarding sensitive information from unauthorized disclosure
- Privacy: Managing personal information according to established privacy principles
Research from AuditBoard highlights that while SOC 2 compliance is voluntary, it has become a de facto standard for technology and cloud service providers. Companies voluntarily undergo a rigorous third-party audit to demonstrate their commitment to robust security practices.
The purpose of SOC 2 extends beyond mere compliance. It serves as a powerful mechanism for building customer confidence. When an organization successfully obtains a SOC 2 report, it signals to potential clients that they have implemented comprehensive internal controls designed to protect sensitive data and maintain operational excellence.
Unlike one-size-fits-all security certifications, SOC 2 recognizes that each organization's security needs are unique. The framework allows companies to design controls that align specifically with their business model, technology infrastructure, and risk profile. This flexibility makes SOC 2 particularly valuable for businesses across various industries, from cloud computing and software as a service (SaaS) to financial technology and healthcare.
For businesses considering SOC 2 certification, the process involves a comprehensive evaluation by an independent certified public accountant. These auditors meticulously examine an organization's systems, policies, and procedures to verify that the implemented controls meet the stringent SOC 2 standards.
Ultimately, SOC 2 stands as more than just an acronym. It represents a commitment to transparency, security, and continuous improvement in an increasingly digital world where data protection is not just a technical requirement but a fundamental business responsibility.
SOC 2 Trust Principles Explained Simply
The SOC 2 Trust Principles provide a comprehensive framework for organizations to demonstrate their commitment to protecting and managing critical information systems. According to CertPro, these principles offer a nuanced approach to information security that goes far beyond traditional compliance checklists.
The Five Core Trust Principles
Understanding the SOC 2 Trust Principles is like having a detailed roadmap for organizational data protection. Secureframe outlines five key principles, with Security being the only mandatory criterion for all SOC 2 audits:
- Security: The foundational principle that protects against unauthorized access and potential system vulnerabilities
- Availability: Ensuring systems are operational and accessible as promised to users
- Processing Integrity: Confirming data processing is accurate, timely, and complete
- Confidentiality: Safeguarding sensitive information from unauthorized disclosure
- Privacy: Managing personal information according to established privacy principles
Diving Deeper into Each Principle
Each Trust Principle represents a critical aspect of organizational data management. ISMS Online explains that organizations can strategically select which principles to include based on their specific business needs and risk profile.
The Security principle is the cornerstone of SOC 2 compliance. It requires organizations to implement robust protection mechanisms against unauthorized access, potential data breaches, and system vulnerabilities. This goes beyond simple password protection, encompassing comprehensive security controls that safeguard an organization's entire information ecosystem.
Availability focuses on ensuring that systems are consistently operational and accessible. This principle is crucial for organizations that rely on continuous service delivery. It addresses system performance, maintenance, and the ability to recover quickly from potential disruptions.
Processing Integrity ensures that data processing is accurate, complete, and occurs within specified timeframes. This principle is particularly important for organizations handling critical data processing tasks, guaranteeing that information is managed with precision and reliability.
Confidentiality addresses the protection of sensitive information designated as confidential. This principle requires organizations to implement strict controls preventing unauthorized access or disclosure of critical business or customer information.
Privacy is the most comprehensive principle, focusing on how personal information is collected, used, retained, and disclosed. It ensures organizations adhere to established privacy principles, protecting individual rights and maintaining transparency in data handling.
The beauty of the SOC 2 Trust Principles lies in their flexibility. Unlike rigid compliance frameworks, they allow organizations to tailor their approach to information security based on their unique operational context. Companies can select the principles most relevant to their business, creating a customized framework that addresses their specific security and operational challenges.
Ultimately, these principles represent more than just a compliance checklist. They embody a holistic approach to information management, demonstrating an organization's commitment to protecting data, maintaining operational excellence, and building trust with customers and stakeholders.
SOC 2 Compliance Checklist and Key Steps
Navigating the SOC 2 compliance process requires a structured and strategic approach. According to BitSight, organizations must follow a comprehensive roadmap to successfully demonstrate their commitment to robust security and data protection practices.
Initial Preparation and Assessment
Drata highlights that the SOC 2 compliance journey begins with critical preparatory steps. The first phase involves determining your specific compliance objectives and understanding which Trust Service Criteria are most relevant to your organization.
Key initial steps include:
- Defining the precise scope of your SOC 2 audit
- Identifying which Trust Service Criteria apply to your business
- Selecting between Type 1 (point-in-time) or Type 2 (ongoing) report
- Assembling a dedicated compliance team
Comprehensive Gap Analysis and Readiness Assessment
A thorough gap analysis is the cornerstone of successful SOC 2 compliance. BitSight recommends a systematic approach to evaluating existing security controls and identifying areas requiring improvement. This process involves:
- Conducting a comprehensive internal security assessment
- Mapping current policies and procedures against SOC 2 requirements
- Identifying potential vulnerabilities in existing systems
- Developing a detailed remediation plan to address control gaps
The readiness assessment is particularly crucial. It provides organizations with a clear roadmap for addressing potential compliance challenges before the formal audit. This proactive approach helps minimize potential findings and demonstrates a commitment to continuous security improvement.
Implementation and Documentation
Successful SOC 2 compliance goes beyond merely identifying gaps. Organizations must implement robust security controls and create detailed documentation that demonstrates their commitment to protecting sensitive information.
Key implementation steps include:
- Developing comprehensive security policies
- Establishing clear access control mechanisms
- Creating incident response and business continuity plans
- Implementing robust third-party vendor risk management processes
- Documenting all security controls and procedures
The documentation process is critical. Auditors will require extensive evidence showing that security controls are not just implemented but consistently maintained. This means creating detailed records of security practices, including policy documentation, access logs, incident reports, and ongoing monitoring mechanisms.
Organizations should also prepare for the formal audit by:
- Selecting a qualified independent auditor
- Ensuring all team members understand compliance requirements
- Conducting internal mock audits to identify potential issues
- Maintaining transparency and open communication throughout the audit process
SOC 2 compliance is not a one-time achievement but an ongoing commitment to maintaining high security standards. Successful organizations view this process as an opportunity to enhance their overall security posture, build customer trust, and demonstrate their dedication to protecting sensitive information.
Ultimately, the SOC 2 compliance journey requires patience, thoroughness, and a strategic approach. By following a structured checklist and maintaining a commitment to continuous improvement, organizations can successfully navigate the complex landscape of information security compliance.
Benefits of Achieving SOC 2 for Your Business
SOC 2 compliance represents far more than a technical certification. It is a strategic investment that delivers tangible business advantages across multiple dimensions of organizational performance. According to CG Compliance, businesses that successfully achieve SOC 2 certification unlock significant competitive and operational benefits.
Enhanced Customer Trust and Credibility
In an era where data breaches and cybersecurity incidents are increasingly common, SOC 2 certification serves as a powerful trust signal. Deloitte research reveals that 85% of clients consider SOC 2 compliance a critical factor when selecting a service provider. This certification demonstrates a robust commitment to protecting sensitive information and maintaining high security standards.
Key trust-building benefits include:
- Proving rigorous security protocols
- Demonstrating proactive risk management
- Providing transparent evidence of data protection practices
- Differentiating from competitors without similar certifications
Accelerated Sales and Business Growth
Gartner market analysis indicates that businesses with SOC 2 Type 2 compliance experience a 30% faster sales cycle. This acceleration stems from the immediate credibility and confidence the certification instills in potential clients and partners.
Business growth advantages encompass:
- Reduced sales friction
- Faster contract negotiations
- Expanded market access
- Increased customer confidence
Risk Mitigation and Financial Protection
Beyond trust and sales acceleration, SOC 2 compliance provides substantial risk management benefits. Industry research shows that companies in regulated industries report a 60% reduction in compliance-related fines after achieving SOC 2 Type 2 attestation.
Risk mitigation benefits include:
- Identifying and addressing potential security vulnerabilities
- Reducing likelihood of data breaches
- Minimizing potential regulatory penalties
- Creating a comprehensive security framework
The SOC 2 compliance process forces organizations to develop robust internal controls, systematic documentation, and proactive security measures. This comprehensive approach goes beyond mere checkbox compliance, transforming an organization's entire approach to data protection and operational integrity.
For technology companies, cloud service providers, and businesses handling sensitive customer information, SOC 2 is not just a certification but a strategic differentiator. It signals to customers, investors, and partners that an organization takes data security seriously and has implemented world-class protective measures.
Moreover, the continuous improvement mindset embedded in SOC 2 compliance ensures that organizations remain adaptive and responsive to evolving cybersecurity challenges. By regularly reviewing and updating security protocols, businesses can stay ahead of potential threats and maintain a strong security posture.
Ultimately, SOC 2 certification is an investment in an organization's reputation, operational excellence, and long-term sustainability. It represents a commitment to transparency, security, and building lasting trust with stakeholders in an increasingly complex digital ecosystem.
Frequently Asked Questions
What does SOC 2 stand for?
SOC 2 stands for System and Organization Controls 2. It is a framework developed by the American Institute of Certified Public Accountants (AICPA) that evaluates how companies protect customer data through stringent security standards.
What are the core principles of SOC 2 compliance?
SOC 2 compliance is based on five core trust principles: Security, Availability, Processing Integrity, Confidentiality, and Privacy. These principles ensure that organizations effectively manage data protection and security.
Why is SOC 2 compliance important for businesses?
Achieving SOC 2 compliance is crucial for businesses as it enhances customer trust, accelerates sales cycles, and reduces the likelihood of compliance-related fines. It signals a commitment to high security standards and operational excellence.
What steps are involved in obtaining SOC 2 compliance?
The steps to obtain SOC 2 compliance include initial preparation and assessment, a comprehensive gap analysis, the implementation of robust security controls, and thorough documentation to demonstrate adherence to SOC 2 standards.
Accelerate SOC 2 Readiness and Eliminate Security Questionnaire Stress
Achieving SOC 2 compliance unlocks faster sales and builds customer trust, but completing endless security questionnaires can quickly drain your team’s time and energy. Many organizations struggle with manual answers, missed deadlines, and repetitive proof requests, keeping you from fully realizing those business growth benefits the article describes. There is a smarter, faster way to prove your commitment to the SOC 2 trust principles and security excellence.

Let Skypher’s AI Questionnaire Automation Tool transform how you handle SOC 2 security reviews. Get your team collaborating in real time, auto-fill complex forms with ease, and centralize your proof in a customizable Trust Center. Top tech and finance companies use Skypher to cut through delays and win deals—but these wins only come when you act. Visit Skypher and experience hassle-free, accurate SOC 2 responses before your next sales cycle starts.
