SOC 2 Type 1 certification is a game changer for organizations committed to safeguarding sensitive data. It offers a snapshot assessment of your internal controls, verifying their design effectiveness at a specific point in time. But here’s the twist: although many view it as just a box-ticking exercise, it carries far more weight than that. The real value lies in how it builds customer trust and sets the foundation for ongoing security excellence.
Table of Contents
- Understanding Soc 2 Type 1
- Soc 2 Type 1 Certification Process
- Implementing Key Compliance Controls
- Boosting Security And Trust
Quick Summary
| Takeaway | Explanation |
|---|---|
| SOC 2 Type 1 provides a snapshot assessment. | SOC 2 Type 1 evaluates an organization's internal controls at a specific point in time, confirming whether they are suitably designed to meet Trust Service Criteria. |
| Preparation is key for certification success. | Organizations must perform a readiness assessment, gap analysis, and develop comprehensive documentation, including a management assertion, system description, and controls matrix, to prepare for the audit process. |
| SOC 2 Type 1 certification boosts customer trust. | Achieving SOC 2 Type 1 certification demonstrates a commitment to data security, enhancing customer confidence and potentially streamlining the vendor selection process. |
| It serves as a stepping stone to SOC 2 Type 2. | SOC 2 Type 1 certification helps organizations establish well-designed controls and positions them for more comprehensive evaluations of control effectiveness, as seen in SOC 2 Type 2. |
| Implementing robust controls strengthens security posture. | The certification process enhances internal security practices and fosters a culture of security awareness, leading to operational improvements and better protection for sensitive information. |
Understanding SOC 2 Type 1
SOC 2 Type 1 certification represents a critical milestone for service organizations looking to demonstrate their commitment to data security and privacy. It serves as a validation that an organization has implemented appropriate controls to protect sensitive information. Let's delve deeper into what SOC 2 Type 1 entails and why it matters.
What Is SOC 2 Type 1 Certification?
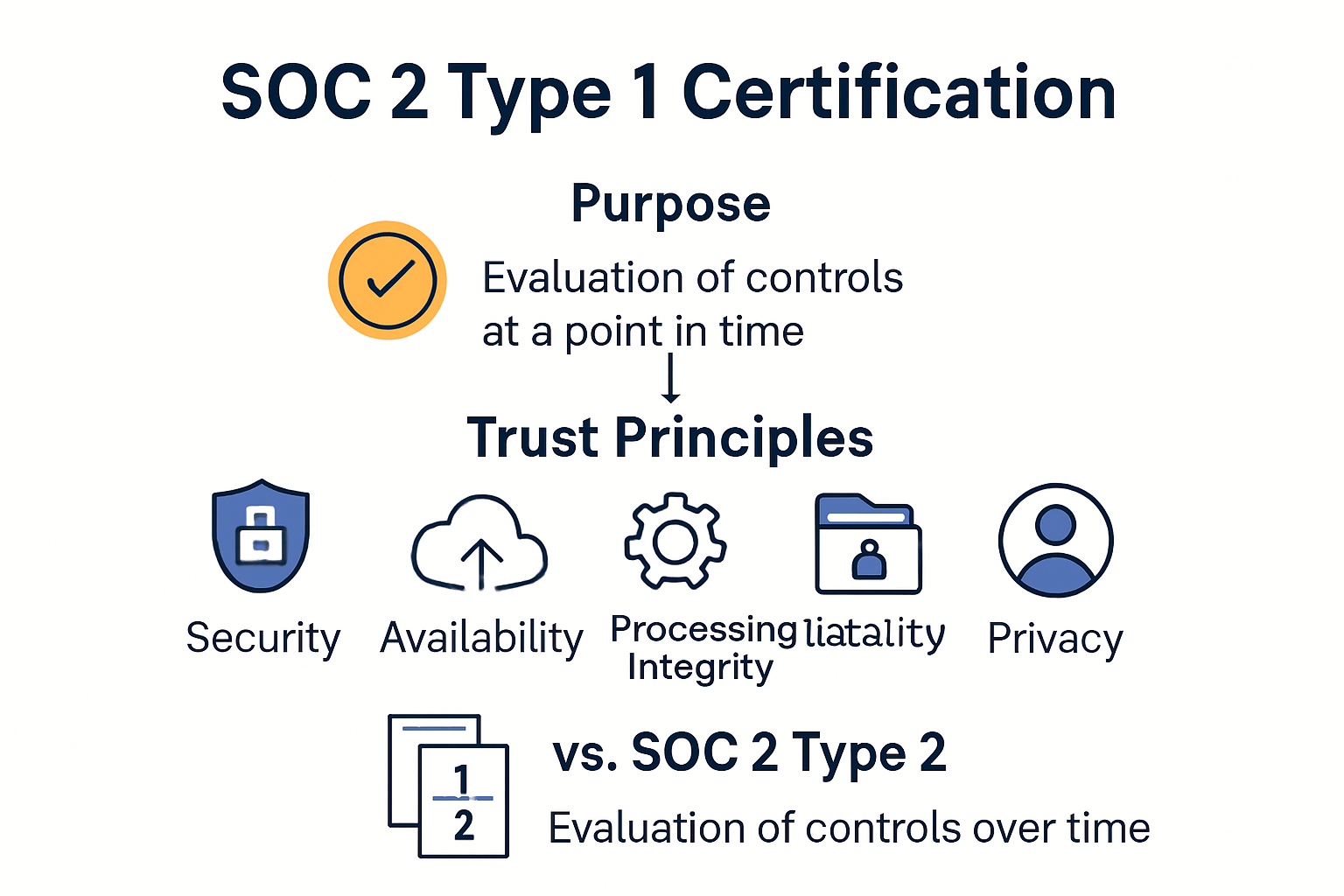
SOC 2 Type 1 is an attestation report that evaluates whether an organization's internal controls are suitably designed to meet the relevant Trust Service Criteria (TSC) at a specific point in time. Unlike its counterpart, SOC 2 Type 2, which assesses the operating effectiveness of controls over a period, Type 1 provides a snapshot assessment at a particular date.
The certification process involves an independent audit conducted by a CPA firm. During this audit, the auditor reviews evidence such as documents, conducts interviews, and examines procedures before issuing an opinion on control design in the report. This thorough examination ensures that the organization's security measures align with the AICPA's Trust Service Criteria.
According to Scytale, the auditor specifically focuses on whether the controls are properly designed to meet the selected trust principles. These principles typically include security, availability, processing integrity, confidentiality, and privacy.
The SOC 2 Type 1 Certification Process
Obtaining a SOC 2 Type 1 certification follows a structured process that organizations must navigate carefully. The journey begins with a readiness assessment to identify gaps in existing controls. Next comes remediation, where organizations implement necessary changes to address these gaps.
The formal audit phase follows, conducted by an AICPA-accredited auditor who examines the design of controls against the selected trust criteria. After completing the audit, the auditor issues a report detailing their findings and opinion on the design effectiveness of the organization's controls.
The entire certification process typically takes between 1.5 to 3.5 months, combining both preparation—implementing and documenting required controls—and the formal audit phase, as noted by Easy Audit.
Benefits and Limitations of SOC 2 Type 1
SOC 2 Type 1 certification offers several advantages for organizations. First, it provides a quicker path to compliance compared to Type 2, making it an excellent starting point for companies beginning their compliance journey. It also demonstrates to customers and partners that an organization has designed appropriate security controls, potentially opening doors to new business opportunities.
However, SOC 2 Type 1 has limitations that organizations should recognize. Since it only examines controls at a specific point in time, it doesn't verify whether these controls work effectively over time. This point-in-time assessment means that while controls may be well-designed, there's no guarantee they're consistently followed or effective in practice.
Many organizations view SOC 2 Type 1 as a stepping stone toward the more comprehensive SOC 2 Type 2 certification. Type 1 helps establish the foundation by ensuring controls are properly designed before moving on to evaluate their operating effectiveness over time.
As StrongDM points out, SOC 2 reports are based on criteria established by the American Institute of Certified Public Accountants (AICPA) and are designed specifically for service organizations. The Type 1 variation focuses solely on the design of controls at a particular date, not their operational effectiveness.
Understanding the scope and limitations of SOC 2 Type 1 certification helps organizations make informed decisions about their compliance strategy. Whether used as an initial compliance step or as part of a broader security program, SOC 2 Type 1 plays a valuable role in establishing trust with stakeholders and demonstrating commitment to security best practices.
SOC 2 Type 1 Certification Process
Navigating the SOC 2 Type 1 certification process requires careful planning, thorough preparation, and attention to detail. Organizations seeking this certification must follow specific steps to demonstrate that their security controls are properly designed. Let's explore the journey to achieving SOC 2 Type 1 compliance.
Preparation and Scoping
The certification journey begins with defining the audit scope. According to Easy Audit, this crucial first step involves identifying critical services and data, assessing your organization's risk appetite, and utilizing the Trust Services Criteria framework to guide your efforts. Proper scoping ensures that the certification process remains focused and manageable.
Organizations must decide which trust principles apply to their business operations. The five trust principles include security, availability, processing integrity, confidentiality, and privacy. While the security principle (also known as the Common Criteria) is mandatory, organizations can choose which additional principles to include based on their business needs and customer requirements.
After determining the scope, conducting a readiness assessment helps identify gaps in existing controls. This gap analysis serves as a roadmap for remediation efforts, highlighting areas that need attention before the formal audit begins. Many organizations work with compliance consultants during this phase to ensure they're on the right track.
With a clear understanding of what needs improvement, organizations can develop and implement policies, procedures, and controls that align with the selected trust principles. This implementation phase may involve updating existing documentation, creating new policies, configuring systems, and training staff on new procedures.
Documentation Requirements
Documentation forms the backbone of SOC 2 Type 1 certification. Secureframe notes that organizations must prepare three key documents for the certification:
-
A management assertion - A formal statement from management confirming that the system description is accurate and that controls are suitably designed to meet the applicable trust criteria.
-
A system description - A comprehensive document detailing the organization's system, including its components, boundaries, and the services provided. This document helps auditors understand the scope of the assessment.
-
A controls matrix - A detailed listing of all controls implemented to address the selected trust criteria, including control objectives, control descriptions, and how each control maps to the relevant trust criteria.
These documents must be meticulously prepared and reviewed for accuracy, as they form the foundation for the auditor's assessment. Organizations should maintain clear, concise documentation that accurately reflects their security practices.
The Audit and Reporting Phase

Once preparation is complete, the formal audit begins. The audit is conducted by a licensed CPA firm with experience in SOC 2 assessments. During this phase, auditors review the prepared documentation, conduct interviews with key personnel, and examine evidence that controls are properly designed.
Unlike the SOC 2 Type 2 audit, which observes operations over a six-month period, the Type 1 audit assesses controls at a specific point in time. As StrongDM explains, a Type 1 report evaluates whether security processes are properly designed at that particular moment, without tracking their effectiveness over time.
After completing their assessment, auditors prepare a formal report that includes their findings and opinion on the design effectiveness of the organization's controls. This report typically includes:
- The auditor's opinion
- Management's assertion
- The system description
- Information about the applicable trust criteria
- Details about the controls in place and their design
If the auditors identify deficiencies during their assessment, these will be noted in the report along with management's response and remediation plans. However, minor deficiencies don't necessarily prevent certification—what matters is how the organization addresses these issues.
Once the report is finalized, organizations can share it with stakeholders, including customers, partners, and regulators, to demonstrate their commitment to security and compliance. Many organizations use this report as a stepping stone toward SOC 2 Type 2 certification, which provides a more comprehensive assessment of control effectiveness over time.
The entire SOC 2 Type 1 certification process, from preparation to final report, typically takes several months to complete. However, the investment of time and resources pays dividends in terms of improved security posture, enhanced customer trust, and competitive advantage in the marketplace.
Implementing Key Compliance Controls
Establishing robust compliance controls is fundamental to achieving SOC 2 Type 1 certification. These controls form the foundation of your security posture and demonstrate to auditors that your organization has designed appropriate safeguards for protecting sensitive information. Let's explore the essential controls you need to implement and strategies for ensuring they meet SOC 2 requirements.
Understanding the Trust Services Criteria Framework
SOC 2 controls are structured around the Trust Services Criteria (TSC) established by the AICPA. According to Sprinto, these controls fall into five main categories that align with the trust principles:
-
Control Environment - This category covers the organization's commitment to integrity and ethical values, board independence, organizational structure, and assignment of authority and responsibility. These foundational controls set the tone for the entire compliance program.
-
Monitoring and Control Activities - These controls involve ongoing evaluation processes that ensure security measures remain effective. They include regular assessments, internal audits, and mechanisms for addressing deficiencies.
-
Logical and Physical Access Controls - This critical category encompasses user authentication, data encryption, access management, and physical security measures that prevent unauthorized access to systems and facilities.
-
System and Operations Controls - These controls focus on detecting and mitigating threats, managing vulnerabilities, and ensuring business continuity. They include incident response procedures, system monitoring, and disaster recovery planning.
-
Change Management Controls - These controls govern how modifications to systems, applications, and infrastructure are implemented to prevent unauthorized or untested changes that could compromise security.
Implementing controls across these categories requires a systematic approach that considers your organization's unique risk profile and operational context. The goal is to create a cohesive security framework that addresses all applicable trust principles while remaining practical for daily operations.
Implementing a Systematic Control Framework
The implementation process begins with a thorough gap analysis to identify where your current security measures fall short of SOC 2 requirements. This assessment should evaluate existing policies, procedures, and technical controls against the specific criteria for your chosen trust principles.
Once gaps are identified, develop a remediation plan that prioritizes critical controls based on risk level and implementation complexity. CertPro explains that this remediation phase is crucial, as it involves implementing necessary security procedures according to trust principles, addressing control gaps, and conducting post-remediation tests to ensure comprehensive compliance before the formal audit.
Documentation plays a vital role in implementing controls. Each control should be clearly documented with:
- A detailed description of the control objective
- Specific implementation procedures
- Roles and responsibilities for maintaining the control
- Methods for testing and validating the control's design
- Evidence requirements for demonstrating compliance
Technical controls often require configuration changes to systems, applications, and networks. These might include implementing multi-factor authentication, encryption for data at rest and in transit, access control lists, network segmentation, and logging mechanisms. When implementing these controls, ensure they're configured according to industry best practices and documented thoroughly for auditor review.
Testing and Validating Control Effectiveness
Before entering the formal audit, thoroughly test your implemented controls to validate their design effectiveness. For SOC 2 Type 1, the focus is on whether controls are properly designed rather than their operating effectiveness over time. Nevertheless, preliminary testing helps identify design flaws that could result in audit findings.
Control validation should include:
- Review of policy and procedure documentation to ensure clarity and completeness
- Walkthrough testing to verify that controls are implemented as designed
- Evidence collection to confirm that controls can be properly documented
- Stakeholder interviews to verify understanding and awareness of controls
As Fraxtional notes, while SOC 2 Type 1 reviews control design at a specific point in time, it's still important to ensure controls are functioning properly. This preliminary validation prepares the organization for a potential future Type 2 audit, which examines both design and operational effectiveness over an extended period.
Addressing any identified deficiencies before the audit demonstrates proactive risk management and can significantly improve audit outcomes. Remember that perfect security isn't the goal—reasonable security appropriate to your organization's risk profile is the standard for SOC 2 compliance.
Implementing key compliance controls requires coordination across multiple departments, including IT, security, human resources, and operations. By taking a collaborative approach and maintaining clear communication about control requirements, organizations can create a robust security framework that not only satisfies SOC 2 Type 1 certification requirements but also provides genuine protection for sensitive information.
Boosting Security and Trust
Beyond achieving compliance, SOC 2 Type 1 certification delivers substantial benefits by strengthening your organization's security posture and building trust with stakeholders. This certification serves as more than just a checkbox—it becomes a powerful business asset that can drive growth and competitive advantage.
Building Customer Confidence
In today's digital landscape, customers are increasingly concerned about how their data is handled and protected. SOC 2 Type 1 certification provides tangible evidence of your commitment to information security, which directly translates to increased customer confidence. According to Scytale, this certification demonstrates to customers and prospects that your organization has suitable security control designs in place and takes information security seriously, helping build trust with clients and stakeholders.
This enhanced trust can significantly impact your business relationships. A customer satisfaction survey by Deloitte found that 85% of clients consider SOC 2 compliance a key factor when choosing a service provider, as cited by CG Compliance. This data highlights the growing importance of security certifications in client decision-making processes.
When prospective clients evaluate potential service providers, they often include security requirements in their vendor assessment questionnaires. Having SOC 2 Type 1 certification allows you to respond confidently to these inquiries, sometimes even eliminating the need for lengthy security questionnaires altogether. This streamlined process reduces friction in the sales cycle and accelerates deal closures.
Gaining Competitive Advantage
SOC 2 Type 1 certification can provide a significant competitive edge, especially in crowded markets where service offerings may be similar. When potential clients are choosing between providers with comparable services, security credentials often become the differentiating factor.
This competitive advantage translates directly to business performance. According to a study cited by Gartner and referenced by CG Compliance, businesses with SOC 2 compliance experience a 30% faster sales cycle. This acceleration provides a significant advantage in markets where data security is paramount, allowing certified organizations to close deals more quickly than non-certified competitors.
Many enterprise clients and government agencies explicitly require SOC 2 certification in their contract requirements. Without this certification, organizations may be excluded from bidding on certain contracts or participating in specific markets altogether. By obtaining SOC 2 Type 1 certification, you open doors to new business opportunities that would otherwise remain closed.
Strengthening Internal Security Practices
The process of preparing for SOC 2 Type 1 certification naturally strengthens your organization's security posture by formalizing and enhancing existing controls. Even organizations with strong security practices benefit from the structured approach required by SOC 2, which helps identify and address overlooked vulnerabilities or process gaps.
The certification process promotes a security-first culture throughout the organization. When teams understand that security is a priority backed by formal certification requirements, they're more likely to incorporate security considerations into their daily activities. This cultural shift can prevent security incidents more effectively than technical controls alone.
Regular security reviews become part of normal operations rather than exceptional events. This proactive approach to security management helps organizations stay ahead of emerging threats rather than reacting to incidents after they occur. The formal documentation required for SOC 2 certification also ensures continuity of security practices even as personnel changes occur.
Additionally, the improvements made during the certification process often yield operational benefits beyond security. Many organizations find that the systematic examination of their processes leads to efficiency improvements, better documentation, and clearer roles and responsibilities. These operational enhancements can reduce errors, improve service delivery, and ultimately contribute to better customer experiences.
By investing in SOC 2 Type 1 certification, organizations don't just satisfy a compliance requirement—they create a foundation for sustainable business growth built on security and trust. The certification serves as visible evidence of your commitment to protecting sensitive information, which resonates strongly with security-conscious clients in today's threat-laden digital landscape.
Frequently Asked Questions
What is SOC 2 Type 1 certification?
SOC 2 Type 1 certification is an attestation that evaluates whether an organization's internal controls are suitably designed to meet the Trust Services Criteria (TSC) at a specific point in time. It provides a snapshot assessment of controls rather than an evaluation of their operational effectiveness over a longer period.
How long does the SOC 2 Type 1 certification process take?
The SOC 2 Type 1 certification process typically takes between 1.5 to 3.5 months. This timeframe includes both preparation—implementing and documenting required controls—and the formal audit phase conducted by an accredited CPA firm.
What are the key steps in the SOC 2 Type 1 certification process?
The key steps include preparation and scoping of the audit, conducting a readiness assessment to identify gaps, preparing essential documentation (such as a management assertion and controls matrix), and undergoing the formal audit by a licensed CPA firm to evaluate control design effectiveness.
What are the benefits of obtaining SOC 2 Type 1 certification?
SOC 2 Type 1 certification enhances customer trust by demonstrating a commitment to data security. It provides a faster path to compliance, opens up new business opportunities, serves as a stepping stone to SOC 2 Type 2 certification, and strengthens internal security practices, contributing to an improved security posture.
Elevate Your Security Certification Journey with Skypher
Achieving your SOC 2 Type 1 certification is just the beginning of establishing trust with your stakeholders—but how do you handle the complexities of security questionnaires efficiently? Just like preparing for your SOC 2 Type 1 audit requires detailed attention and robust documentation, effectively managing security assessments is critical for delivering confidence to clients and partners.
With Skypher’s AI-driven Questionnaire Automation Tool, streamline your response process to security questionnaires and meet compliance with ease. Our platform supports various formats, integrates with over 40 third-party risk management platforms, and promotes real-time collaboration, making it effortless for your team to enhance security practices as you progress from SOC 2 Type 1 to SOC 2 Type 2 certification.

Ready to boost your efficiency and build unshakeable trust? Don’t let security questionnaires slow you down! Experience how Skypher can dramatically speed up your compliance process and elevate your security posture today. Visit https://skypher.co to learn more and start your journey toward excellence in security compliance!
