Over 40% of new compliance officers mistakenly treat SOC 2 Type 1 reports as equivalent to Type 2 in assurance value, creating dangerous audit readiness gaps. This confusion leads to wasted resources, failed audits, and erosion of stakeholder trust. Understanding the fundamental differences between these report types is critical for medium and large tech and finance organizations navigating customer expectations and regulatory pressures. This guide clarifies SOC 2 Type 1 versus Type 2 to sharpen your audit strategy and strengthen your compliance posture.
Table of Contents
- Understanding SOC 2: Basics And Importance
- Core Differences Between SOC 2 Type 1 And Type 2
- Misconceptions About SOC 2 Type 1 And Type 2
- Selecting The Right SOC 2 Type For Your Organization
- Preparing For SOC 2 Audits: Best Practices And Real World Lessons
- Operational And Business Implications Of SOC 2 Report Types
- Summary And Next Steps For Compliance Leaders
- Streamline Your SOC 2 Compliance With Skypher Solutions
Key Takeaways
| Point | Details |
|---|---|
| Type 1 snapshots design | Evaluates control design at a single point in time without operational testing. |
| Type 2 tests operations | Requires evidence collection over 4 to 6 months to validate sustained control effectiveness. |
| Assurance levels differ | Type 1 offers limited design assurance while Type 2 delivers operational confidence. |
| Decision depends on maturity | Choose Type 1 for early benchmarking and Type 2 for customer contracts and ongoing risk management. |
| Misunderstanding causes failures | Assuming Type 1 readiness equals Type 2 preparedness leads to audit failures and resource waste. |
Understanding SOC 2: Basics and Importance
SOC 2 is an auditing framework developed by the American Institute of CPAs that evaluates service organizations against Trust Services Criteria. These criteria cover security, availability, processing integrity, confidentiality, and privacy. SOC 2 compliance is driven by regulatory and customer expectations in tech and finance sectors, making it essential for organizations handling sensitive customer data.
Service organizations in technology and finance face mounting pressure from both regulators and customers to demonstrate robust data protection. A SOC 2 report provides third party validation that your controls meet industry standards. Without this verification, you risk losing contracts, failing audits, and damaging your reputation.
Compliance officers and security leaders play pivotal roles in SOC 2 audits. You must coordinate cross functional teams, maintain documentation, and ensure controls operate effectively. Understanding SOC reports helps you navigate audit requirements and set realistic timelines.
Key responsibilities for compliance teams include:
- Mapping organizational controls to Trust Services Criteria
- Collecting and organizing evidence for auditor review
- Coordinating with IT, legal, and operations teams
- Monitoring control performance and remediating gaps
- Communicating audit status to executives and stakeholders
Core Differences Between SOC 2 Type 1 and Type 2
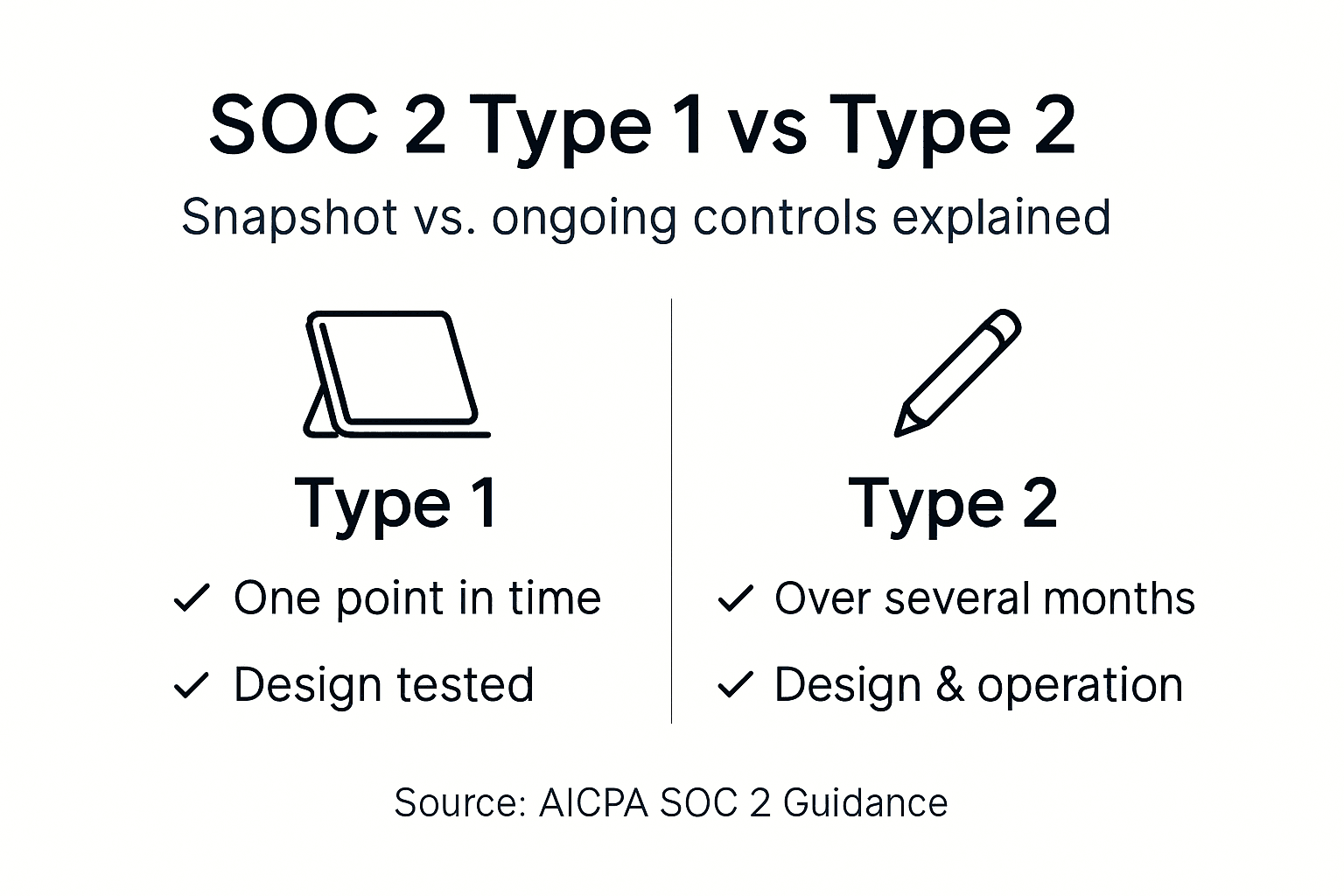
SOC 2 Type 1 and Type 2 reports differ fundamentally in scope, timeframe, and the level of assurance they provide. Type 1 evaluates whether your controls are suitably designed to meet Trust Services Criteria at a specific point in time. Auditors review documentation, interview staff, and assess design logic, but they do not test whether controls actually work in practice.
SOC 2 Type 1 assesses controls at a point in time, whereas Type 2 tests operational effectiveness over a 6 plus month period. Type 2 requires you to demonstrate that controls operated effectively throughout the audit period. Auditors collect evidence samples, review logs, and validate that controls consistently performed as designed.
| Aspect | Type 1 | Type 2 |
|---|---|---|
| Audit Scope | Control design only | Design plus operational effectiveness |
| Timeframe | Single point in time | 4 to 6 months minimum |
| Evidence Required | Policies and documentation | Logs, tickets, evidence samples over time |
| Assurance Level | Limited design assurance | Sustained operational assurance |
| Audit Duration | 4 to 8 weeks | 4 to 6 months |
Resource requirements differ dramatically between the two audit types. Type 1 audits require less preparation time and fewer staff hours, making them suitable for organizations in early compliance stages. Type 2 audits demand continuous monitoring, extensive evidence collection, and sustained control performance across months.
Pro Tip: Use a successful Type 1 audit as a readiness benchmark before committing to Type 2. This phased approach helps identify control gaps early, reducing the risk of Type 2 audit failures and wasted resources.
For detailed guidance, review the SOC 2 Type 1 report details and SOC 2 Type 2 report guide to understand what auditors will scrutinize.
Misconceptions About SOC 2 Type 1 and Type 2
Many compliance officers believe that passing a Type 1 audit automatically prepares them for Type 2 success. This misconception stems from underestimating the operational testing rigor required for Type 2 reports. Type 1 audits do not guarantee readiness for Type 2 audits despite common belief, as design validation differs sharply from proving sustained effectiveness.
Nearly 35% of organizations fail their first Type 2 audit attempt due to inadequate evidence collection and monitoring gaps discovered during operational testing.
Another widespread misunderstanding is that Type 1 and Type 2 provide equivalent assurance to customers and partners. Customers increasingly demand Type 2 reports because they demonstrate ongoing commitment to security, not just theoretical control design. Relying solely on Type 1 reports can cost you contracts and damage trust.
Common misconceptions include:
- Type 1 proves controls work effectively in daily operations
- Type 2 is just a longer version of Type 1 with no additional value
- Passing Type 1 means you are ready for Type 2 immediately
- Type 1 satisfies all regulatory and customer compliance requirements
- You can skip continuous monitoring if you have strong control designs
These misunderstandings lead to audit failures, compliance gaps, and wasted resources. Organizations that assume Type 1 readiness translates directly to Type 2 success often discover critical evidence gaps months into the audit period. For clarity on SOC 2 misconception corrections, review the distinctions carefully before committing resources.
Selecting the Right SOC 2 Type for Your Organization
Choosing between SOC 2 Type 1 and Type 2 depends on your organizational maturity, customer expectations, risk tolerance, and available resources. Type 1 audits work best when you need a quick baseline assessment of control design or want to identify gaps before pursuing full operational validation.
Type 1 is best suited for:
- Organizations new to SOC 2 seeking initial benchmarking
- Early stage companies without established operational history
- Internal assessments to identify control design weaknesses
- Situations where customer contracts do not mandate Type 2
Type 2 becomes necessary when customers, partners, or regulators require proof of sustained control effectiveness. Most enterprise customers in tech and finance now demand Type 2 reports as a condition of doing business. If your sales team faces repeated Type 2 requests, delaying the audit risks lost revenue and market credibility.
Type 2 is required for:
- Customer contracts explicitly demanding operational assurance
- Regulatory environments requiring continuous control validation
- Organizations with mature security programs ready for extended testing
- Situations where stakeholder trust depends on proven reliability
Resource and cost considerations matter significantly. Type 1 audits typically cost 40% to 60% less than Type 2 and require fewer staff hours. However, Type 2 delivers far greater business value by opening doors to enterprise customers and reducing long term compliance risk.
Pro Tip: Adopt a phased approach by completing Type 1 first, remediating identified gaps, and then transitioning to Type 2 after six months of continuous monitoring. This strategy optimizes audit efficiency and reduces failure risk. For preparation steps, consult the SOC 2 compliance checklist.
Preparing for SOC 2 Audits: Best Practices and Real World Lessons
Successful SOC 2 preparation requires meticulous documentation, continuous monitoring, and proactive gap remediation. For Type 1 audits, focus on creating clear control descriptions, policy documents, and design evidence that demonstrate how controls meet Trust Services Criteria. Auditors will review these materials to assess design suitability.
Type 2 preparation extends far beyond documentation. Continuous monitoring and documentation readiness are critical for successful SOC 2 Type 2 audits, as auditors require evidence samples proving controls operated effectively throughout the audit period. This means implementing logging, ticketing, and evidence collection systems months before the audit begins.
Key preparation steps include:
- Mapping all controls to specific Trust Services Criteria subcategories
- Establishing automated logging and monitoring for critical security controls
- Creating a centralized evidence repository accessible to auditors
- Conducting internal control testing to identify and fix gaps early
- Training staff on evidence collection and audit response procedures
Common pitfalls include waiting until the audit starts to collect evidence, assuming Type 1 readiness equals Type 2 preparedness, and neglecting continuous monitoring between audits. Organizations that fail to maintain consistent control performance throughout the audit period often face findings or qualified opinions.
Pro Tip: Adopting automated tools mitigates common audit readiness failures by streamlining evidence collection and reducing manual errors. Automation ensures you capture control performance data consistently, making auditor requests easier to fulfill. Learn more about cybersecurity best practices to strengthen your overall posture.
For tactical guidance, review SOC 2 audit preparation tips that cover evidence organization, auditor communication, and timeline management.
Operational and Business Implications of SOC 2 Report Types
SOC 2 report types carry significant operational and business consequences beyond audit completion. Type 2 reports substantially improve customer confidence by proving that your security controls work reliably over time, not just on paper. Type 2 reports significantly increase client trust and reduce long term risk compared to Type 1, making them a competitive advantage in enterprise sales.
Cost benefit analysis reveals that while Type 2 audits require greater upfront investment, they deliver stronger ROI through increased contract wins and reduced security incidents. Organizations with Type 2 reports close enterprise deals 30% faster on average and face fewer customer security questionnaires.
| Factor | Type 1 Impact | Type 2 Impact |
|---|---|---|
| Customer Trust | Moderate baseline confidence | High sustained confidence |
| Contract Success | Limited enterprise appeal | Strong enterprise appeal |
| Audit Cost | Lower upfront investment | Higher but justified by ROI |
| Internal Security | Design baseline established | Operational rigor enforced |
| Resource Allocation | Minimal ongoing commitment | Continuous monitoring required |
Type 2 audits also strengthen your internal security posture by enforcing continuous monitoring and accountability. Teams become more disciplined about logging, incident response, and change management when they know auditors will review evidence samples. This cultural shift reduces risk and improves operational resilience.
For deeper insights into business impact, explore SOC 2 Type 2 business impact and SOC 2 compliance cost considerations to inform your investment decisions.
Summary and Next Steps for Compliance Leaders
SOC 2 Type 1 and Type 2 reports serve distinct purposes and deliver different levels of assurance. Type 1 validates control design at a point in time, making it suitable for early benchmarking. Type 2 tests operational effectiveness over months, providing the sustained assurance that enterprise customers and regulators demand. Understanding these distinctions helps you allocate resources wisely and avoid costly audit failures.
Use this checklist to guide your SOC 2 decision and preparation:
- Assess organizational maturity and control readiness
- Review customer contracts to identify Type 2 requirements
- Establish continuous monitoring and evidence collection systems
- Conduct internal control testing to identify gaps early
- Engage auditors early to clarify expectations and timelines
- Leverage automation tools to streamline evidence management
Compliance officers and security leaders should prioritize building a culture of continuous monitoring and documentation discipline. These practices not only support SOC 2 success but also strengthen overall security posture and operational resilience. For comprehensive preparation guidance, refer to the SOC 2 compliance checklist.
Streamline Your SOC 2 Compliance with Skypher Solutions
Managing SOC 2 audit preparation and security questionnaires can overwhelm even experienced compliance teams. Skypher streamlines these processes through AI security questionnaire automation tools that complete 200 questions in under a minute.

Our platform integrates with over 40 third party risk management portals, enabling real time collaboration and evidence management. Explore best practices for automating security questionnaires and learn how to optimize your security questionnaire automation process for maximum efficiency.
Frequently Asked Questions
How long does a SOC 2 Type 2 audit typically take?
Type 2 audits usually span four to six months due to operational effectiveness testing over time. Duration depends on organizational size, control complexity, and auditor availability.
Can a SOC 2 Type 1 report satisfy all customer compliance demands?
Type 1 reports offer limited assurance and usually are not enough for ongoing customer requirements. Many customers and regulators expect the sustained assurance shown only by Type 2 reports.
What are best practices for preparing documentation for SOC 2 audits?
Maintain clear, updated documents reflecting control design and operation. Implement continuous monitoring to collect evidence routinely. Use automated tools to reduce errors and streamline audit readiness.
