Displaying the SOC 2 Type 2 logo is now a make-or-break signal for companies seeking client trust. Here’s the kicker. You can only show that sought-after logo for 12 months after your certification date or risk legal trouble. Most brands overlook this detail, but strict rules around the logo’s use are the real story. Get this right and you stand out as a verified security leader. Get it wrong and you could lose your credibility overnight.
Table of Contents
- What The Soc 2 Type 2 Logo Means For Your Business
- Official Guidelines For Displaying The Soc 2 Type 2 Logo
- Best Practices To Promote Your Soc 2 Type 2 Achievement
- Common Mistakes To Avoid With The Soc 2 Type 2 Logo
Quick Summary
| Takeaway | Explanation |
|---|---|
| Verified Security Practices | The SOC 2 Type 2 logo signifies that an organization's security controls have been independently validated by an auditor, enhancing trust with clients and partners. |
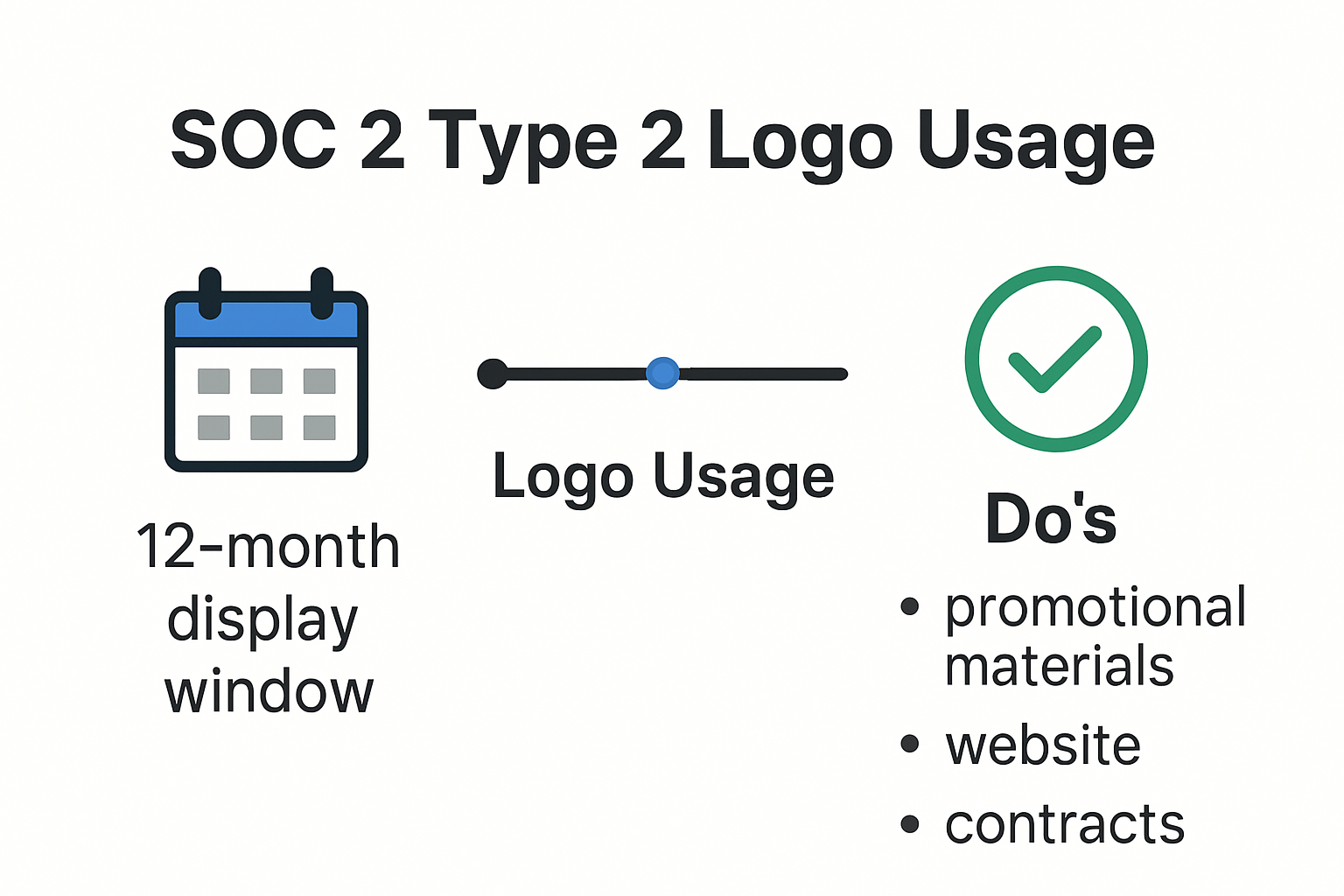
| Compliance with Usage Guidelines | Organizations must adhere to strict guidelines, including displaying the logo only within 12 months of certification and using approved versions without modifications. |
| Strategic Promotion of Certification | Properly promoting the SOC 2 Type 2 achievement through digital channels and marketing can significantly improve an organization's reputation and client trust. |
| Avoid Common Logo Missteps | Organizations should avoid misrepresenting SOC 2 certification by using precise language and ensuring proper logo usage to maintain credibility and avoid legal issues. |
What the SOC 2 Type 2 Logo Means for Your Business
The SOC 2 Type 2 logo represents more than just a visual badge of compliance. It is a powerful symbol of your organization's commitment to robust security practices and data protection standards. When displayed correctly, this logo communicates critical assurances to potential clients, partners, and stakeholders about your company's information security management.
The Strategic Significance of the SOC 2 Type 2 Logo
Understanding the SOC 2 Type 2 logo goes beyond mere graphic design. According to AICPA guidelines, organizations that complete a SOC 2 Type 2 examination can display the official service organization logo for 12 months following their report date. This logo serves as a tangible demonstration of your rigorous security controls and systematic approach to protecting sensitive information.
The logo tells potential clients several key things about your organization:
- Verified Security Practices: Your security controls have been thoroughly tested and validated by an independent auditor.
- Ongoing Commitment: You maintain consistent security standards over an extended observation period.
- Third Party Validation: An objective professional has reviewed and confirmed your security protocols.
Proper Usage and Compliance Considerations
The Journal of Accountancy highlights that the AICPA has specific approved logos for service organizations completing SOC engagements. Improper use can lead to potential legal and reputational risks.
When implementing the SOC 2 Type 2 logo, consider these key guidelines:
- Only display the logo during the 12-month period after your report
- Use the exact approved version from your auditing firm
- Maintain the logo's original proportions and color scheme
- Place the logo in contexts that clearly communicate your security achievements
Businesses across technology, finance, and service sectors view the SOC 2 Type 2 logo as a mark of trustworthiness. It signals that your organization has not just claimed security standards but has proven them through comprehensive, independent assessment. The logo transforms abstract security concepts into a visible, credible symbol of your commitment to protecting client data and maintaining rigorous operational standards.
Beyond marketing, the SOC 2 Type 2 logo can be a competitive differentiator. In an era where data breaches and cybersecurity threats are constant concerns, this logo provides immediate visual reassurance to potential clients and partners about your organization's mature, professional approach to information security.
Official Guidelines for Displaying the SOC 2 Type 2 Logo

Displaying the SOC 2 Type 2 logo requires precision and adherence to strict professional standards. Organizations must navigate a complex set of guidelines to ensure proper representation and maintain the logo's credibility and legal integrity.
Logo Compliance and Verification Requirements
Professional bodies have established comprehensive rules for SOC 2 Type 2 logo usage. AICPA official guidelines mandate specific protocols for organizations seeking to display their certification mark. These guidelines are designed to protect the integrity of the certification process and prevent misrepresentation.
Key verification steps include:
- Authentic Documentation: Maintain a current SOC 2 Type 2 report from a recognized independent auditor.
- Timeframe Restrictions: The logo can only be displayed for 12 months following the report date.
- Original Format Preservation: Use the logo exactly as provided by the certifying organization without modifications.
To help understand the main guidelines for SOC 2 Type 2 logo compliance and verification, see the table below:
| Requirement | Description |
|---|---|
| Authentic Documentation | Maintain a current SOC 2 Type 2 report from a recognized independent auditor |
| Timeframe Restriction | Display the logo only within 12 months after the report date |
| Original Format Preservation | Use the logo as provided with no modifications (other than allowed resizing) |
| Approved Version Only | Utilize the exact approved logo version from your auditor |
| Proper Placement | Place logo in contextually relevant, honest locations (e.g., website, marketing collateral) |
Placement and Contextual Considerations
Cybersecurity experts from Gartner recommend strategic logo placement that provides maximum visibility while maintaining professional context. The logo should be positioned where it naturally communicates your organization's commitment to security standards.
Recommended placement locations include:
- Company website homepage
- Security or compliance dedicated web pages
- Marketing collateral
- Corporate email signatures
- Proposal and contract documents
When incorporating the SOC 2 Type 2 logo, organizations must ensure:
- Clear visibility without appearing boastful
- Contextual relevance to security and compliance messaging
- Consistent sizing and proportional representation
- Alignment with overall brand aesthetic
Legal and Ethical Implications
International compliance research emphasizes that unauthorized or incorrect logo usage can result in significant legal consequences. Misrepresentation might lead to:
- Potential decertification
- Legal disputes with certifying bodies
- Reputational damage
- Loss of client trust
Professional organizations strongly advise consulting with your specific SOC 2 auditor to confirm exact logo usage requirements. Each certification may have nuanced guidelines that require careful interpretation and implementation.
Ultimately, the SOC 2 Type 2 logo is more than a decorative element. It represents a rigorous commitment to maintaining exceptional security standards. Proper display demonstrates transparency, professionalism, and a genuine dedication to protecting sensitive organizational and client information.
Best Practices to Promote Your SOC 2 Type 2 Achievement
Achieving SOC 2 Type 2 certification is a significant milestone that demonstrates your organization's commitment to robust security practices. However, simply obtaining the certification is not enough. Strategic promotion of this achievement can significantly enhance your company's reputation and build trust with potential clients and partners.
Strategic Digital Visibility
AICPA guidelines recommend a comprehensive approach to showcasing your SOC 2 Type 2 achievement. Digital platforms offer multiple opportunities to highlight your certification.
Key digital promotion strategies include:
- Website Prominence: Place the SOC 2 Type 2 logo on your homepage or dedicated security page
- Social Media Announcements: Share your achievement across professional networks
- Email Marketing: Include certification details in newsletter communications
- Case Studies: Develop detailed content explaining your security journey
Leveraging Marketing and Sales Opportunities
UpGuard security experts emphasize the importance of integrating SOC 2 Type 2 certification into your broader marketing narrative. This certification is not just a technical achievement but a powerful differentiator in competitive markets.
Effective promotional approaches:
- Include certification details in sales presentations
- Highlight security credentials in proposal documents
- Create comparison materials showing your advanced security posture
- Develop targeted content explaining the significance of SOC 2 Type 2
Compliance and Communication Best Practices
ISO compliance research suggests a nuanced approach to communicating your SOC 2 Type 2 achievement. Transparency and accuracy are crucial when promoting your certification.
Critical communication guidelines:
- Hyperlink the SOC 2 logo to www.aicpa.org/soc4so
- Do not modify the logo beyond approved resizing
- Provide context about what the certification means
- Avoid overstating the scope of your security capabilities
- Update promotional materials within the 12-month certification window
Below is a summary table of key promotion strategies and communication best practices for maximizing the impact of your SOC 2 Type 2 certification:
| Strategy | Description |
|---|---|
| Website Prominence | Display logo on homepage or security/compliance pages |
| Social Media Announcements | Share achievement on professional platforms and networks |
| Email Marketing | Incorporate certification in newsletters and email signatures |
| Sales & Marketing Collateral | Include details in proposals, presentations, and comparison materials |
| Case Studies | Publish detailed accounts of your security journey and audit process |
| Logo Hyperlink | Link logo to www.aicpa.org/soc4so |
| Guideline Compliance | Only use approved logo versions, within 12-month window, with no changes |
Your SOC 2 Type 2 certification represents more than a technical accomplishment. It is a testament to your organization's dedication to maintaining the highest standards of data protection and operational security. By thoughtfully and strategically promoting this achievement, you demonstrate transparency, build client confidence, and differentiate your organization in an increasingly security-conscious marketplace.
Common Mistakes to Avoid with the SOC 2 Type 2 Logo
Navigating the complexities of SOC 2 Type 2 logo usage requires careful attention to detail. Many organizations inadvertently compromise their compliance and professional reputation by making critical errors in logo representation and communication.
Terminology and Communication Missteps
Barra Advisory experts highlight that precise language is crucial when discussing SOC 2 achievements. One of the most common mistakes is incorrectly claiming certification.
Terminology errors to avoid:
- Incorrect Certification Claims: Never state you are "SOC 2 certified"
- Precise Wording: Use "completed a SOC 2 Type 2 examination"
- Avoid Overstating Scope: Do not imply the examination covers all possible security controls
- Be Specific: Clearly communicate the specific trust services criteria examined
Logo Usage and Representation Violations
UpGuard security professionals emphasize strict guidelines for logo deployment. Improper logo usage can result in significant professional consequences.
Critical logo misuse scenarios include:
- Modifying the logo beyond approved resizing
- Failing to hyperlink to www.aicpa.org/soc4so
- Using an outdated or expired logo version
- Displaying the logo outside the 12-month valid period
- Placing the logo in contexts that misrepresent its meaning
Below is a checklist of common mistakes to avoid to ensure proper and compliant SOC 2 Type 2 logo usage:
| Potential Mistake | Avoidance Checklist |
|---|---|
| State "SOC 2 certified" | Use "completed SOC 2 Type 2 exam" |
| Modify logo beyond resizing | Only use approved resizing |
| Use outdated/expired logo | Verify current 12-month period |
| Omit logo hyperlink to AICPA | Always hyperlink to aicpa.org/soc4so |
| Overstate certification scope | Clearly define examination covered |
| Place logo in misleading contexts | Ensure truthful representation |
| Fail to use approved logo version | Obtain from auditing organization |
Authorization and Compliance Pitfalls
Compliance research from AICPA indicates that unauthorized logo use can lead to serious repercussions. Organizations must obtain explicit permission before displaying the SOC 2 Type 2 logo.
Key authorization requirements:
- Submit official logo registration forms
- Maintain current documentation of your SOC 2 examination
- Regularly verify your logo usage meets current guidelines
- Consult with your independent auditor about specific usage restrictions
The SOC 2 Type 2 logo represents a sophisticated commitment to security standards. Treating it as a mere marketing graphic undermines its profound significance. Each interaction with the logo is an opportunity to demonstrate your organization's professionalism, attention to detail, and genuine commitment to maintaining rigorous security protocols.
By understanding and meticulously following logo usage guidelines, you transform a simple graphic into a powerful statement of your organization's dedication to protecting sensitive information and maintaining the highest professional standards.
Frequently Asked Questions
What does the SOC 2 Type 2 logo signify?
The SOC 2 Type 2 logo indicates that an organization’s security controls have been independently validated by an auditor, showcasing their commitment to maintaining robust data protection standards.
How long can I use the SOC 2 Type 2 logo after certification?
Organizations can only display the SOC 2 Type 2 logo for 12 months following the certification date as per AICPA guidelines.
Are there specific guidelines for using the SOC 2 Type 2 logo?
Yes, organizations must adhere to strict guidelines, including using the approved logo version without modifications and placing it in relevant contexts that clearly communicate security achievements.
What are common mistakes to avoid when using the SOC 2 Type 2 logo?
Common mistakes include misrepresenting the certification status, modifying the logo, using outdated logos, and not hyperlinking it to the official AICPA site.
Take Your SOC 2 Type 2 Gains Beyond the Logo—Earn Even Greater Trust
You have invested time and resources to use the SOC 2 Type 2 logo correctly. Yet, the pressure does not end there. Clients are not just looking for a badge. They need proof that your security practices run deep throughout your team, every day. The biggest challenge organizations face is quickly showing clients they know their controls and can answer complex security questionnaires without risking mistakes, reputational damage, or wasted hours. If you are struggling to handle endless security reviews or if delays around accurate answers keep slowing your sales cycle, that pain stops here.

Skypher answers the call for real security credibility and operational efficiency. Our AI-driven Questionnaire Automation Tool lets you respond to security questionnaires in minutes instead of days. You can centralize compliance proof, energize collaboration, and keep your brand’s trust at the forefront even after your 12-month SOC 2 showcase period ends. Don’t let outdated manual processes hold your team back. Visit Skypher today and see how our solutions help you increase trust, win deals faster, and make every security review an opportunity to stand out.
