Every business that handles sensitive customer data faces new challenges in 2025. Now pause for a moment. Eighty three percent of organizations have had security issues with their vendors in just the past three years. That figure is jarring, but here’s the real twist. For most companies, achieving a SOC 2 Type 2 report is no longer just about ticking a box for compliance. It has become a powerful statement of trust that clients demand and competitors envy, setting apart companies who are ready for the future of digital accountability.
Table of Contents
- What Is A SOC 2 Type 2 Report?
- Key Requirements And Trust Principles
- Why Businesses Need SOC 2 Type 2 In 2025
- How To Prepare For A Successful SOC 2 Type 2 Audit
Quick Summary
| Takeaway | Explanation |
|---|---|
| SOC 2 Type 2 Reports are Essential for Businesses in 2025 | Organizations recognize that SOC 2 Type 2 compliance is critical for maintaining customer trust and a competitive advantage amidst rising cybersecurity threats. |
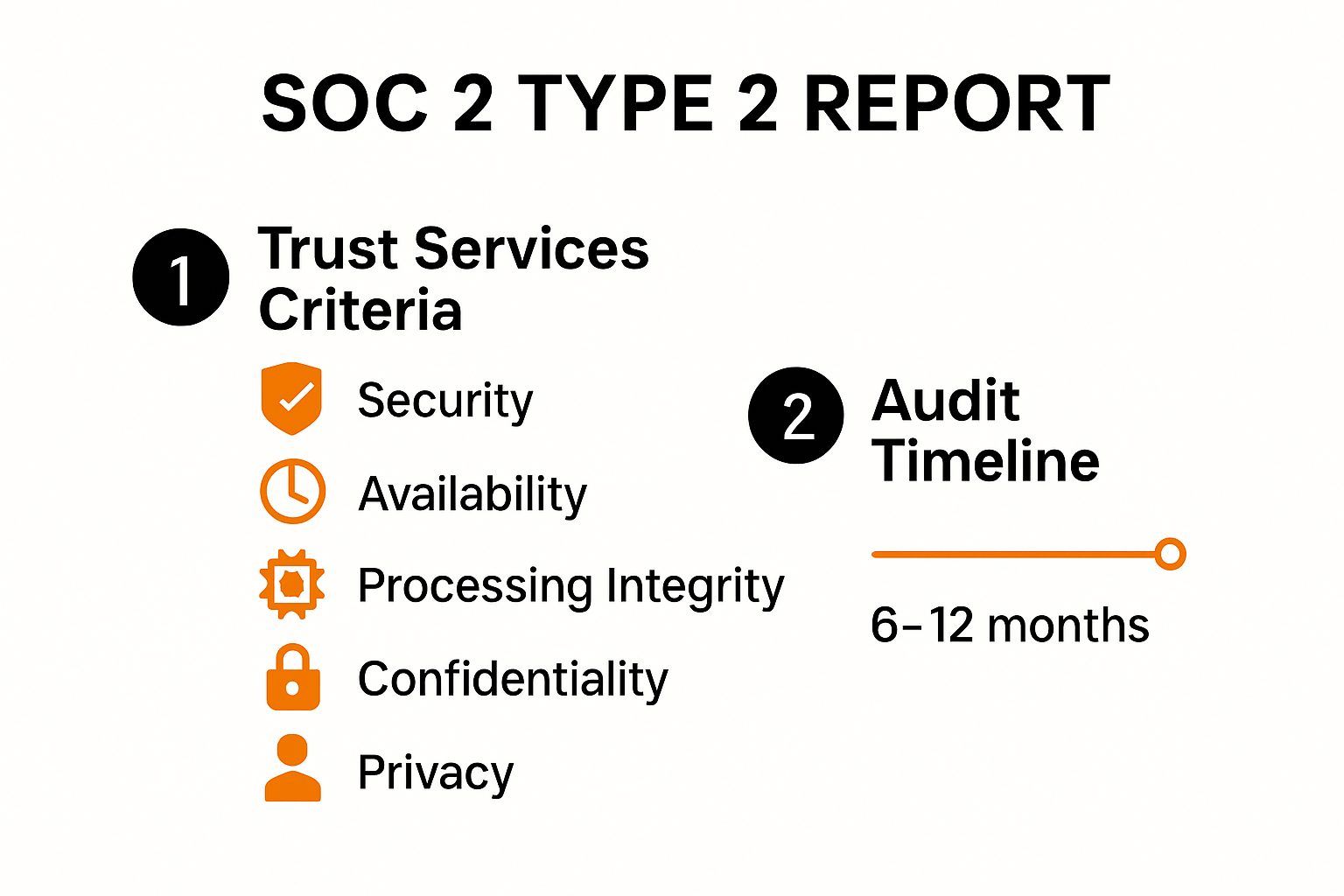
| Five Trust Services Criteria are Fundamental | The five criteria—security, availability, processing integrity, confidentiality, and privacy—provide a structured framework for evaluating security practices. Security is the only mandatory criterion. |
| Preparation is Key for Successful Audits | Conducting a readiness assessment and developing comprehensive documentation and policies are crucial steps in preparing for a SOC 2 Type 2 audit. |
| Continuous Monitoring Enhances Security | Organizations must implement systems for ongoing monitoring and improvement of security controls, ensuring a proactive approach to data protection. |
| Strategic Asset for Differentiation | Achieving SOC 2 Type 2 compliance not only reduces breach risks but also acts as a strategic differentiator that builds client confidence and enhances credibility. |
What Is a SOC 2 Type 2 Report?
A SOC 2 Type 2 report represents a comprehensive security assessment that provides organizations with critical insights into their information security controls and practices. Unlike standard compliance documents, this report goes beyond surface level checks to deliver a deep examination of how a company protects customer data and maintains robust security protocols.
Understanding the Core Components
At its foundation, a SOC 2 Type 2 report evaluates an organization's systems and controls based on five key trust services criteria: security, availability, processing integrity, confidentiality, and privacy. Linford & Co explains that this report is not a one time snapshot but a detailed assessment of controls operating effectively over a specified time period.
The audit process typically spans three to six months, during which independent auditors conduct a thorough examination. According to Sprinto, auditors meticulously test both the design and operational effectiveness of internal controls. This means they are not just checking if controls exist on paper but verifying that these controls function consistently and as intended in real world scenarios.
Why SOC 2 Type 2 Matters for Businesses
For technology companies and service providers, a SOC 2 Type 2 report serves as a critical trust signal to potential clients and partners. It demonstrates a commitment to rigorous security practices and provides tangible evidence of an organization's ability to protect sensitive information.
Key aspects that make SOC 2 Type 2 reports valuable include:
- Comprehensive Security Assessment: Provides a holistic view of an organization's security posture
- Third Party Validation: Independent verification from certified auditors
- Detailed Control Effectiveness: Proves that security measures work consistently over time
Businesses across industries recognize that in an era of increasing cybersecurity threats, a SOC 2 Type 2 report is more than a compliance document. It is a strategic asset that can differentiate an organization in competitive markets, build customer confidence, and demonstrate a proactive approach to data protection and risk management.
Understanding the nuances of a SOC 2 Type 2 report requires recognizing it as a dynamic, in depth assessment of an organization's commitment to maintaining the highest standards of security and operational excellence.
Key Requirements and Trust Principles
A SOC 2 Type 2 report centers on five critical Trust Services Criteria that form the foundation of comprehensive security assessments. These principles provide a structured framework for evaluating an organization's commitment to protecting and managing sensitive information.The Five Trust Services Criteria
Sprinto highlights that while all five principles are important, Security stands as the only mandatory criterion for organizations seeking SOC 2 compliance. The comprehensive framework includes:
- Security: The core principle covering access controls, network and application protection, and data encryption
- Availability: Ensuring systems and data remain accessible and operational
- Processing Integrity: Guaranteeing system processing is complete, accurate, and timely
- Confidentiality: Protecting sensitive information from unauthorized disclosure
- Privacy: Managing personal information collection, use, retention, and disposal
Secureframe explains that the Security principle encompasses over 30 specific criteria, making it the most rigorous and comprehensive of the five principles. Organizations must demonstrate robust mechanisms to protect against unauthorized access, implement strong authentication protocols, and maintain comprehensive security controls.
Implementing Trust Principles in Practice

The Availability principle requires special attention. According to Secureframe, organizations must develop and test comprehensive data backup and recovery procedures. This ensures that critical systems remain operational and data can be recovered quickly in the event of technical failures, natural disasters, or potential security breaches.
Each trust principle demands a specific set of controls and documentation. Businesses must not only implement these controls but also demonstrate their consistent effectiveness over time. This means creating detailed policies, maintaining rigorous documentation, and conducting regular internal assessments to ensure ongoing compliance.
Key considerations for successful implementation include:
- Comprehensive Documentation: Detailed policies and procedures for each trust principle
- Consistent Control Monitoring: Regular internal audits and assessments
- Proactive Risk Management: Identifying and addressing potential security vulnerabilities
Organizations must recognize that SOC 2 Trust Principles are not a one time checklist but an ongoing commitment to maintaining the highest standards of information security and operational excellence. The principles provide a flexible yet comprehensive framework that adapts to the unique needs of different businesses while ensuring a robust approach to protecting sensitive information.
Why Businesses Need SOC 2 Type 2 in 2025
In the rapidly evolving digital ecosystem of 2025, SOC 2 Type 2 compliance has transformed from an optional credential to a critical business imperative. Organizations across industries are recognizing that robust security practices are no longer just a technical requirement but a fundamental business strategy for maintaining customer trust and competitive advantage.
The Rising Stakes of Data Security
CertPro reveals a stark reality: 83% of organizations have experienced security problems with their vendors in the last three years. This statistic underscores the urgent need for comprehensive security assessments like SOC 2 Type 2 reports. Businesses can no longer afford to treat security as an afterthought or a checkbox exercise.
In 2025, data breaches are not just technical failures but potentially existential threats to an organization's reputation and financial stability. SOC 2 Type 2 compliance provides a structured framework for demonstrating a proactive and systematic approach to protecting sensitive information. By establishing well defined policies and controls, businesses create a robust defense against evolving cybersecurity threats.
Competitive Advantage and Client Trust
Beyond risk mitigation, SOC 2 Type 2 compliance offers significant strategic benefits. CertPro highlights that achieving this certification provides a competitive advantage by reducing breach risks and supporting scalable security practices. In an era where customers are increasingly sophisticated about data protection, a SOC 2 Type 2 report becomes a powerful differentiator.
Key advantages include:
- Enhanced Credibility: Tangible proof of robust security practices
- Risk Reduction: Systematic approach to identifying and mitigating potential vulnerabilities
- Scalable Security Framework: Adaptable controls that grow with your business
For technology companies, service providers, and organizations handling sensitive data, SOC 2 Type 2 compliance is no longer optional. It represents a commitment to transparency, security, and professional excellence. Potential clients and partners view this certification as a critical indicator of an organization's maturity and reliability.
Future Proofing Business Operations
The dynamic nature of cybersecurity demands continuous adaptation. SOC 2 Type 2 reports are not static documents but living frameworks that encourage ongoing security improvements. By establishing comprehensive policies and demonstrating consistent control effectiveness, businesses position themselves to navigate the complex and ever changing digital threat landscape.
As technological complexity increases and regulatory requirements become more stringent, SOC 2 Type 2 compliance provides a strategic roadmap for maintaining robust security practices. It signals to stakeholders that an organization is not just reactive but proactively committed to protecting data and maintaining the highest standards of operational integrity.
How to Prepare for a Successful SOC 2 Type 2 Audit
Preparing for a SOC 2 Type 2 audit requires meticulous planning, strategic preparation, and a comprehensive approach to demonstrating an organization's commitment to robust security practices. Success hinges on thorough documentation, proactive control implementation, and a deep understanding of the audit process.
Initial Readiness Assessment
CertPro recommends conducting a comprehensive readiness assessment as the critical first step in SOC 2 Type 2 audit preparation. This internal evaluation helps organizations identify and remediate potential control gaps before the external audit begins. The assessment serves as a diagnostic tool, allowing businesses to strengthen their security infrastructure and ensure alignment with trust service criteria.
Sprinto emphasizes the importance of clearly defining the audit's scope by selecting relevant trust service categories. Organizations must carefully consider which principles most accurately represent their business needs: security, availability, processing integrity, confidentiality, or privacy. This strategic selection determines the focus and depth of the audit preparation process.
Developing Comprehensive Documentation and Policies
Successful SOC 2 Type 2 audit preparation demands robust administrative guidelines and standard operating procedures. Sprinto highlights the critical importance of developing detailed documentation that covers:
- Staff Training Protocols: Comprehensive security awareness programs
- Incident Response Procedures: Clear guidelines for managing potential security events
- Risk Assessment Frameworks: Systematic approaches to identifying and mitigating potential vulnerabilities
- Disaster Recovery Plans: Detailed strategies for maintaining operational continuity
Documentation should be more than a static set of rules. It must demonstrate a living, adaptive approach to security that shows how an organization consistently implements and monitors its control mechanisms. Auditors will scrutinize not just the existence of policies but their practical application and effectiveness.
Implementing Continuous Monitoring and Improvement
A successful SOC 2 Type 2 audit preparation strategy goes beyond initial documentation. Organizations must establish continuous monitoring systems that track and validate the ongoing effectiveness of their security controls. This involves:
- Regular internal audits
- Consistent control testing
- Prompt addressing of identified vulnerabilities
- Maintenance of comprehensive evidence trails
The audit process is not a destination but a journey of continuous improvement. Businesses must cultivate a culture of security that embeds rigorous practices into every aspect of their operational framework. By treating SOC 2 Type 2 compliance as an ongoing commitment rather than a one time achievement, organizations can build resilient, trustworthy security infrastructures that adapt to evolving technological challenges.
Preparing for a SOC 2 Type 2 audit requires significant investment in time, resources, and organizational commitment. However, the benefits far outweigh the challenges. A successful audit demonstrates an organization's dedication to protecting sensitive information, building client trust, and maintaining the highest standards of operational excellence.
Frequently Asked Questions
What is a SOC 2 Type 2 report?
A SOC 2 Type 2 report is a comprehensive assessment of an organization's security controls and practices, focusing on their effectiveness over a specified period. It evaluates the security, availability, processing integrity, confidentiality, and privacy of customer data.
Why do businesses need a SOC 2 Type 2 report in 2025?
In 2025, SOC 2 Type 2 compliance is crucial for businesses as it helps build customer trust, enhances credibility, and provides a competitive advantage in an increasingly cybersecurity-conscious market.
What are the five Trust Services Criteria in a SOC 2 Type 2 report?
The five Trust Services Criteria are security, availability, processing integrity, confidentiality, and privacy. Only the security criterion is mandatory for SOC 2 compliance, but all five are important for a comprehensive security evaluation.
How can a business prepare for a SOC 2 Type 2 audit?
To prepare for a SOC 2 Type 2 audit, businesses should conduct an initial readiness assessment, develop detailed documentation and policies, and implement continuous monitoring of their security controls. This proactive approach helps identify and address potential vulnerabilities before the audit.
Transform SOC 2 Type 2 Readiness Into Rapid Wins With Automation
The pressure to achieve and maintain SOC 2 Type 2 compliance is real. Businesses struggle with constant back-and-forth on security questionnaires and face mounting demands to prove their trustworthiness. The stakes are especially high when just one missed question can disrupt your sales cycle or shake client confidence. Whether you're dealing with endless reviews, time-consuming documentation, or the need to show consistent control effectiveness, relying on slow manual processes puts your team at a real disadvantage.

Imagine harnessing automation that turns security reviews into a competitive edge. With Skypher, you get an AI-powered questionnaire automation tool that adapts to your workflow, slashes response times, and brings real-time collaboration across your teams—all while supporting your quest for SOC 2 Type 2 excellence. Empower your organization to respond faster, prove your compliance with ease, and show clients your unwavering commitment to security. Stop letting manual processes stall your growth. Discover more about Skypher's automation platform and take the first step to transform your security operations today.
