SOC 2 Type 3 compliance is quickly becoming the new standard for organizations focused on digital trust. Here is the twist. Companies with continuous security monitoring can reduce security-related financial risk by up to 40 percent. So while most businesses still rely on outdated point-in-time checks, the smartest companies are shifting to a round-the-clock defense that never takes a break.
Table of Contents
- Understanding Soc 2 Type 3 And Its Role
- Soc 2 Type 3 Vs Other Soc Reports
- Benefits Of Soc 2 Type 3 For Your Business
- Steps To Prepare For Soc 2 Type 3 Compliance
Quick Summary
| Takeaway | Explanation |
|---|---|
| Continuous Evaluation | SOC 2 Type 3 focuses on a dynamic and ongoing assessment of security controls, allowing organizations to monitor their security posture in real time rather than relying solely on periodic reports. |
| Strategic Advantage | Implementing SOC 2 Type 3 not only ensures compliance but also enhances stakeholder confidence, demonstrating a proactive commitment to security that can lead to operational improvements and competitive differentiation. |
| Comprehensive Preparation | To prepare for SOC 2 Type 3 compliance, organizations should conduct a thorough initial assessment, develop robust control frameworks, and implement continuous monitoring mechanisms to address potential vulnerabilities effectively. |
Understanding SOC 2 Type 3 and Its Role
Navigating the complex world of cybersecurity compliance requires a nuanced understanding of audit frameworks, and SOC 2 Type 3 represents a critical evolution in security assessment methodologies. While many organizations are familiar with traditional SOC 2 Type 1 and Type 2 reports, SOC 2 Type 3 emerges as a more comprehensive and continuous evaluation approach that provides deeper insights into an organization's security controls and operational practices.
The Unique Characteristics of SOC 2 Type 3
Unlike its predecessors, SOC 2 Type 3 is not a standard designation but rather an advanced assessment methodology that extends beyond periodic snapshots of security controls. AICPA suggests this approach represents a more dynamic and continuous monitoring framework that captures an organization's security posture across an extended period.
The key distinguishing factor of SOC 2 Type 3 is its emphasis on continuous evaluation and real time assessment of security controls. Traditional SOC 2 reports typically provide a point in time or short term view of an organization's security practices. In contrast, SOC 2 Type 3 introduces a more fluid and adaptive approach that tracks security performance over a longer duration, often spanning multiple reporting periods.
Strategic Implications for Modern Organizations
For technology companies and service providers, SOC 2 Type 3 represents more than a compliance checkbox. Cloud Security Alliance indicates that this advanced assessment methodology offers several strategic advantages:
- Continuous Compliance Monitoring: Organizations can track their security controls dynamically, identifying potential vulnerabilities in near real time.
- Enhanced Stakeholder Confidence: Demonstrates a proactive approach to security that goes beyond traditional periodic assessments.
- Comprehensive Risk Management: Provides a more holistic view of an organization's security ecosystem and potential risk factors.
The evolution towards SOC 2 Type 3 reflects the increasing complexity of cybersecurity threats and the need for more sophisticated, ongoing evaluation mechanisms. Unlike static compliance reports, this approach enables organizations to demonstrate a commitment to adaptive and responsive security practices.
Understanding SOC 2 Type 3 requires recognizing it as more than a technical audit. It represents a strategic framework that allows organizations to continuously validate their security controls, build trust with stakeholders, and maintain a robust defense against emerging cyber risks. By embracing this advanced assessment methodology, companies can transform compliance from a periodic obligation into a dynamic, ongoing security optimization process.
As digital ecosystems become increasingly interconnected and threats grow more sophisticated, SOC 2 Type 3 emerges as a critical tool for organizations committed to maintaining the highest standards of security and operational integrity. It signals a shift from reactive security models to proactive, continuously monitored approaches that can adapt to the rapidly changing technological landscape.
SOC 2 Type 3 vs Other SOC Reports
Comparing SOC reports reveals a complex landscape of compliance and security assessment frameworks, each designed to address specific organizational needs and stakeholder requirements. While SOC 2 Type 3 represents an advanced approach to security evaluation, understanding its distinctions from other SOC report types is crucial for organizations seeking comprehensive compliance strategies.
The SOC Report Ecosystem
The SOC reporting framework encompasses multiple report types, each serving unique purposes in the realm of organizational control and security assessment. AICPA outlines the fundamental differences between these reports, highlighting the nuanced approach of each type.
SOC 1 reports focus primarily on financial reporting controls, making them most relevant for organizations with significant financial system impacts. In contrast, SOC 2 reports dive deeper into security, availability, processing integrity, confidentiality, and privacy controls. Secureframe emphasizes that while SOC 1 is typically used by financial auditors and internal control teams, SOC 2 serves a broader range of technology and service organizations.
Comparative Analysis of SOC Report Types
The distinctions between SOC report types become more pronounced when examining their specific characteristics:
- SOC 1 (Type I and II): Focused on financial reporting controls
- SOC 2 (Type I and II): Concentrates on security and operational controls
- SOC 3: Public-facing report with limited control details
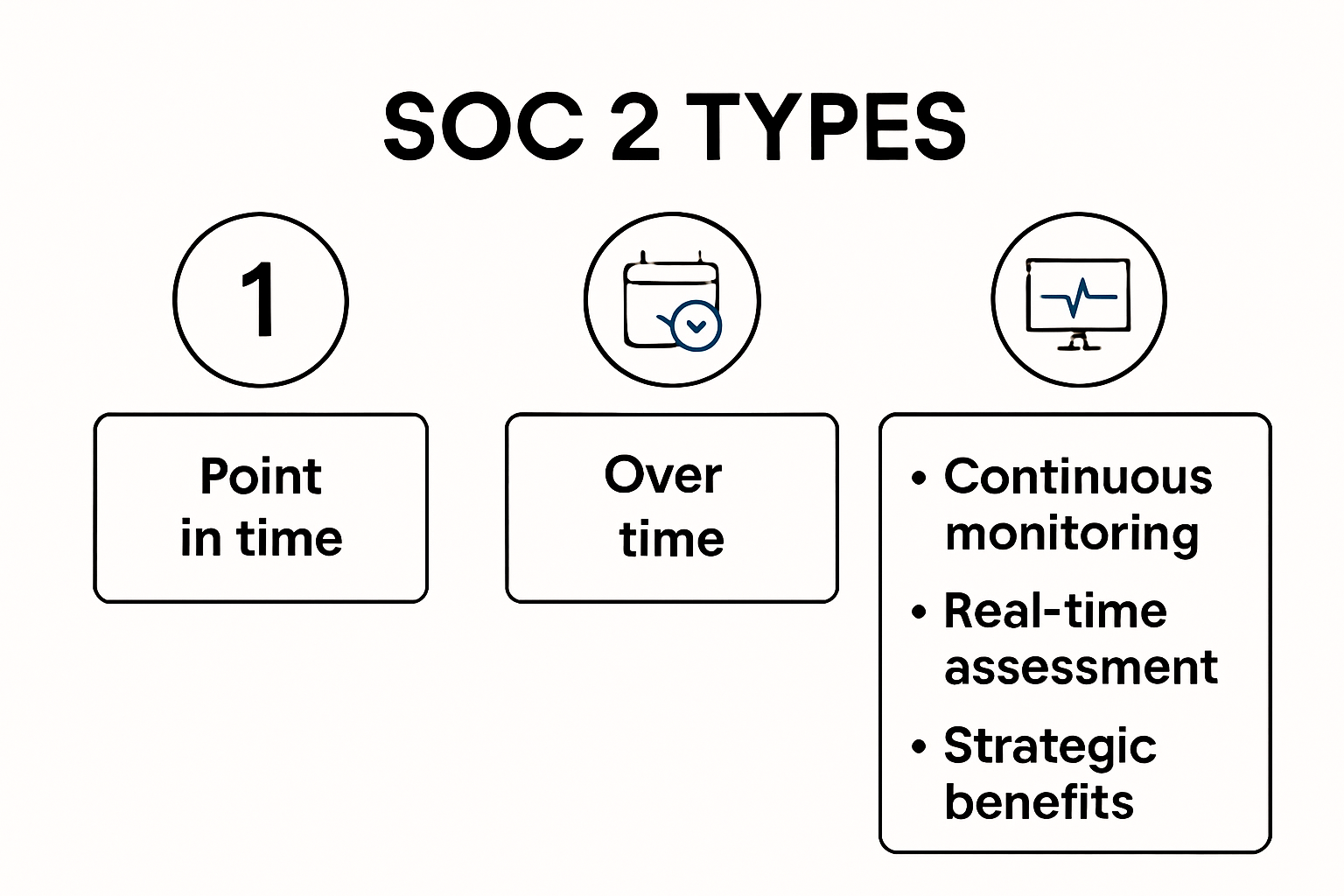
Unlike traditional SOC 2 Type I and Type II reports, SOC 2 Type 3 introduces a more dynamic and continuous assessment approach. ISACA notes that while Type I provides a snapshot of control design at a specific point, and Type II evaluates control effectiveness over a defined period, Type 3 represents a more fluid and ongoing evaluation mechanism.
The most significant differentiator is the temporal aspect. Traditional SOC reports provide periodic assessments, typically covering a 6 or 12-month period. SOC 2 Type 3 breaks this mold by offering a more continuous, real-time approach to security control monitoring. This means organizations can identify and address potential vulnerabilities more quickly and effectively.
From a strategic perspective, the evolution towards more comprehensive reporting reflects the increasingly complex cybersecurity landscape. Cloud Security Alliance suggests that modern organizations require more adaptive and responsive compliance frameworks that can keep pace with rapidly changing technological environments.
For stakeholders and potential clients, the choice between different SOC report types depends on specific needs. Financial auditors might prioritize SOC 1, while technology partners and security-conscious clients increasingly look for the more comprehensive insights provided by advanced SOC 2 reporting methodologies.
Ultimately, SOC 2 Type 3 represents a significant leap forward in compliance reporting. It transforms security assessments from static, point-in-time snapshots to dynamic, continuous monitoring processes that provide real-time insights into an organization's security posture. As cyber threats become more sophisticated, this approach offers organizations a more proactive and comprehensive method of demonstrating their commitment to robust security controls.
To help clarify the differences between the main SOC report types discussed above, the following comparison table summarizes their focus, purpose, and assessment approach.
Here is a comparison table outlining the main characteristics of SOC 1, SOC 2, SOC 3, and the advanced SOC 2 Type 3 approach:
| Report Type | Primary Focus | Intended Audience | Assessment Approach | Detail Level |
|---|---|---|---|---|
| SOC 1 (Type I/II) | Financial Reporting Controls | Financial Auditors, Internal Teams | Point-in-time / Over period | Detailed |
| SOC 2 (Type I) | Security & Operational Controls | Technology, Service Organizations | Point-in-time | Detailed |
| SOC 2 (Type II) | Security & Operational Controls | Technology, Service Organizations | Over a defined period (6-12 months) | Detailed |
| SOC 3 | Security & Operational Controls | General Public, Stakeholders | Over a defined period | Limited (Summary) |
| SOC 2 Type 3 (Advanced) | Continuous Security Monitoring | Technology, Security-Conscious Clients | Dynamic, Ongoing, Real-Time | Highly Detailed |
Benefits of SOC 2 Type 3 for Your Business
While the concept of SOC 2 Type 3 remains technically undefined in standard compliance frameworks, organizations can derive significant strategic advantages from advanced SOC 2 compliance approaches that emphasize continuous monitoring and comprehensive security assessments. The evolving landscape of cybersecurity demands more dynamic and responsive compliance strategies that go beyond traditional point-in-time evaluations.
Building Trust Through Advanced Security Validation
In an era of increasing digital complexity, demonstrating robust security practices becomes paramount for maintaining stakeholder confidence. Compliancy Group reveals that organizations implementing comprehensive security assessments can significantly enhance their credibility among clients, partners, and potential investors.
The continuous monitoring approach analogous to a hypothetical SOC 2 Type 3 enables businesses to:
- Proactively Identify Vulnerabilities: Detect and address potential security risks before they escalate
- Demonstrate Ongoing Commitment: Show continuous investment in security infrastructure
- Provide Real-Time Insights: Offer transparent, up-to-date security performance metrics

Operational and Strategic Advantages
Beyond compliance, advanced security assessment methodologies deliver tangible business benefits. Cloud Security Alliance indicates that organizations adopting comprehensive security frameworks can achieve significant operational improvements.
Key strategic advantages include:
- Enhanced Risk Management: Develop more sophisticated, adaptive risk mitigation strategies
- Improved Internal Controls: Streamline and optimize organizational security processes
- Competitive Differentiation: Position the organization as a security-conscious industry leader
Economic and Competitive Impact
Implementing rigorous, continuous security assessment approaches can translate directly into economic advantages. Cybersecurity Ventures estimates that businesses with robust security frameworks can potentially reduce security-related financial risks by up to 40%.
The economic implications extend beyond direct risk mitigation. Organizations demonstrating advanced security capabilities often experience:
- Faster sales cycles with security-conscious clients
- Reduced insurance premiums
- Lower potential costs associated with data breaches
- Increased investor and stakeholder confidence
While the specific terminology of SOC 2 Type 3 might be fluid, the underlying principle remains consistent: modern businesses require dynamic, responsive, and comprehensive security assessment methodologies. By embracing continuous monitoring and advanced compliance strategies, organizations can transform security from a regulatory obligation into a strategic business asset.
The future of cybersecurity compliance lies not in static reports but in adaptive, real-time frameworks that provide meaningful insights and demonstrate an organization's commitment to protecting critical digital assets. As technological landscapes evolve, so too must our approaches to security validation and risk management.
Steps to Prepare for SOC 2 Type 3 Compliance
Navigating the complex landscape of security compliance requires a strategic and comprehensive approach. While the specific terminology of SOC 2 Type 3 remains technically undefined, organizations can adopt advanced preparation strategies to ensure robust security assessment and validation. The goal is to develop a proactive framework that demonstrates ongoing commitment to security and operational excellence.
Initial Assessment and Scoping
The foundation of a successful compliance journey begins with a thorough initial assessment. Schellman & Company recommends a comprehensive approach that involves multiple critical steps:
- Define Organizational Boundaries: Clearly identify the systems, processes, and services that will be included in the compliance assessment
- Select Relevant Trust Services Criteria: Determine which security parameters are most critical for your organization
- Conduct Preliminary Gap Analysis: Identify existing strengths and potential vulnerabilities in current security infrastructure
This initial phase requires cross-functional collaboration, bringing together IT, security, legal, and operations teams to create a holistic view of the organization's security landscape.
Developing Robust Control Frameworks
Hyperproof emphasizes the critical importance of developing comprehensive control frameworks that go beyond basic compliance requirements. The preparation process involves:
- Policy Development: Create detailed, actionable security policies that cover all critical operational areas
- Documentation Management: Establish systematic documentation processes that provide clear evidence of security controls
- Implement Continuous Monitoring Mechanisms: Develop real-time tracking and reporting systems for security performance
The key is to create a dynamic framework that not only meets current compliance standards but also adapts to evolving security challenges. This approach transforms compliance from a static checkpoint to a continuous improvement process.
Practical Implementation and Readiness
Central Eyes suggests a practical approach to implementing compliance readiness that involves several strategic steps:
- Conduct Internal Audits: Perform rigorous self-assessments to identify and address potential compliance gaps
- Training and Awareness: Develop comprehensive security awareness programs for all organizational levels
- Technical Control Validation: Implement and test technical controls that support security objectives
- Vendor and Third-Party Management: Establish robust processes for managing and assessing external security risks
Successful preparation goes beyond merely meeting compliance requirements. It involves creating a security-first culture that embeds robust practices into every aspect of organizational operations.
While the specific designation of SOC 2 Type 3 may be fluid, the underlying principle remains consistent: modern organizations must adopt a proactive, comprehensive approach to security assessment. By focusing on continuous improvement, detailed documentation, and adaptive control frameworks, businesses can transform compliance from a bureaucratic exercise into a strategic advantage.
The journey to comprehensive security compliance is ongoing. It requires commitment, resources, and a willingness to continuously evolve security practices in response to emerging technological and threat landscapes. Organizations that embrace this approach will not only meet compliance standards but will position themselves as leaders in security and operational excellence.
To illustrate the main phases for preparing for SOC 2 Type 3 compliance, here is a process table summarizing the core steps organizations should take:
This table outlines the principal steps and objectives in the SOC 2 Type 3 compliance preparation process:
| Phase | Key Activities | Objectives |
|---|---|---|
| Initial Assessment & Scoping | - Define organizational boundaries | Identify scope & critical services/processes |
| - Select relevant trust services criteria | Set compliance focus areas | |
| - Conduct preliminary gap analysis | Detect strengths & vulnerabilities | |
| Developing Control Frameworks | - Policy development | Establish clear, actionable security policies |
| - Documentation management | Systematically evidence security controls | |
| - Implement continuous monitoring mechanisms | Enable real-time performance tracking | |
| Implementation & Readiness | - Conduct internal audits | Identify/address compliance gaps |
| - Training and awareness | Foster a security-first culture | |
| - Technical control validation | Test/validate control effectiveness | |
| - Vendor and third-party management | Mitigate external security risks |
Frequently Asked Questions
What is SOC 2 Type 3?
SOC 2 Type 3 is an advanced assessment methodology that focuses on continuous evaluation and real-time assessment of an organization's security controls, providing deeper insights into security practices over an extended period.
How does SOC 2 Type 3 differ from SOC 2 Type 1 and Type 2?
While SOC 2 Type 1 provides a snapshot at a specific point in time and Type 2 evaluates effectiveness over a defined period, SOC 2 Type 3 introduces continuous monitoring, offering dynamic insights into security posture.
What are the benefits of SOC 2 Type 3 for my business?
Implementing SOC 2 Type 3 can enhance stakeholder trust, improve operational efficiencies, reduce financial risk by up to 40%, and position your organization as a proactive leader in security practices.
How can my organization prepare for SOC 2 Type 3 compliance?
To prepare, conduct an initial assessment and gap analysis, develop robust control frameworks, implement continuous monitoring mechanisms, and foster a culture of security awareness within your organization.
Take Control of Continuous Security Compliance with Skypher
The shift to SOC 2 Type 3 compliance is about more than just meeting a new standard. It demands dynamic vigilance, continuous control monitoring, and an ability to respond quickly to evolving risks. Manual questionnaire responses slow teams down, introduce errors, and make true real-time compliance nearly impossible. To stay competitive, your organization needs solutions that actually keep pace with the demands of continuous security validation and stakeholder trust.

Imagine replacing tedious reviews and fragmented communication with instant, AI-driven answers that adapt to real-time requirements. Skypher is built for modern organizations that are ready to demonstrate their proactive security posture—every day, not just during audits. Whether you're preparing for advanced assessments or simply want to accelerate your sales cycles, our AI Questionnaire Automation Tool and customizable Trust Center help you showcase compliance effortlessly. Don't wait to elevate your security and build lasting trust. Discover how Skypher can future-proof your compliance journey today.