Rising customer expectations make proving robust cybersecurity more challenging for growing tech and finance companies. Delays in answering third-party security questionnaires can stall business, while inconsistent controls expose organizations to risk and lost trust. This article breaks down SOC 2 Type Reports, the industry-backed way to validate and communicate your security posture across the five Trust Services Criteria, giving officers practical insight for faster compliance and smoother audit cycles.
Table of Contents
- SOC 2 Type Reports Explained For SaaS
- Trust Services Criteria And Framework
- SOC 2 Type I Vs. Type II Differences
- Compliance Steps For Risk Officers
- Common Pitfalls And Alternatives
Key Takeaways
| Point | Details |
|---|---|
| Importance of SOC 2 Reports | SOC 2 Type Reports are essential for SaaS organizations to validate their cybersecurity and data protection measures, enhancing customer trust and regulatory compliance. |
| Types of SOC 2 Reports | Understanding the differences between SOC 2 Type I and Type II is crucial, as Type I provides a snapshot while Type II assesses sustained operational effectiveness over time. |
| Trust Services Criteria | The five Trust Services Criteria—Security, Availability, Processing Integrity, Confidentiality, and Privacy—are foundational for evaluating organizational information systems and controls. |
| Proactive Compliance Management | Risk officers should adopt a strategic and holistic approach to SOC 2 compliance, focusing on documentation, control effectiveness, and continuous monitoring to avoid common pitfalls. |
SOC 2 Type Reports Explained for SaaS
SaaS organizations increasingly rely on SOC 2 Type Reports to demonstrate their commitment to robust cybersecurity and data protection standards. These comprehensive audit documents provide a critical mechanism for proving operational security to potential customers and partners.
SOC 2 reports evaluate an organization's internal controls across five key Trust Services Criteria:
- Security
- Availability
- Processing Integrity
- Confidentiality
- Privacy
There are two primary types of SOC 2 reports: Type 1 and Type 2. SOC 2 cybersecurity audit framework distinguishes between these critical evaluation methods. A Type 1 report assesses control design at a specific point in time, providing a snapshot of an organization's security infrastructure. In contrast, a Type 2 report delivers a more comprehensive evaluation by examining operational effectiveness over an extended period, typically 6-12 months.
Why SOC 2 Reports Matter for SaaS
For SaaS providers, SOC 2 reports serve multiple strategic purposes:
- Validate security infrastructure
- Demonstrate regulatory compliance
- Build customer trust
- Accelerate sales cycles
- Identify potential security improvements
SOC 2 documentation enables SaaS companies to prove their security commitment and operational excellence to potential clients.
Key Components of a SOC 2 Report
Typical SOC 2 reports include several critical sections:
- Auditor's independent opinion
- Management's assertion of control effectiveness
- Detailed system description
- Comprehensive control evaluation
Pro tip: Work closely with experienced auditors who understand your specific SaaS infrastructure to maximize the value and accuracy of your SOC 2 report.
Trust Services Criteria and Framework
The Trust Services Criteria represent a comprehensive framework established by the American Institute of Certified Public Accountants (AICPA) to evaluate organizational information systems and data protection mechanisms. SOC 2 control framework provides organizations with a flexible approach to assessing critical operational controls.
The framework encompasses five fundamental Trust Services Criteria that organizations must evaluate:
- Security: Protection against unauthorized system access
- Availability: Ensuring system accessibility for authorized users
- Processing Integrity: Guaranteeing accurate, timely, and authorized data processing
- Confidentiality: Restricting information access to authorized parties
- Privacy: Managing personal information collection, use, retention, and disclosure
Each criterion represents a crucial aspect of organizational information management, allowing businesses to demonstrate their commitment to robust cybersecurity and data protection standards. The framework is intentionally designed to be adaptable, enabling evaluation at entity-wide, unit, or functional levels.

Key Characteristics of the Trust Services Framework
The AICPA's Trust Services Criteria offer several significant advantages for organizations:
- Provides a standardized evaluation methodology
- Supports customization based on specific organizational risks
- Aligns with international regulatory standards
- Offers comprehensive assessment of information system controls
- Facilitates transparent communication of security practices
The Trust Services Criteria enable organizations to demonstrate their commitment to comprehensive information security and operational excellence.
Implementing the Trust Services Criteria
Successful implementation requires a strategic approach that involves:
- Conducting thorough internal assessments
- Identifying potential control gaps
- Developing targeted improvement strategies
- Engaging qualified independent auditors
- Maintaining continuous monitoring and improvement
Pro tip: Regularly review and update your Trust Services Criteria implementation to ensure ongoing alignment with evolving cybersecurity threats and organizational changes.
SOC 2 Type I vs. Type II Differences
Understanding the nuanced differences between SOC 2 Type I and SOC 2 Type II reports is critical for organizations seeking comprehensive security assurance. SOC II Type 1 reporting standards provide distinct approaches to evaluating an organization's information security controls.
Key differences between SOC 2 Type I and Type II reports include:
-
Timeframe of Assessment
- Type I: Snapshot evaluation at a specific point in time
- Type II: Comprehensive review over 6-12 months
-
Depth of Evaluation
- Type I: Focuses on control design and initial implementation
- Type II: Examines operational effectiveness and sustained performance
-
Audit Scope
- Type I: Theoretical assessment of control mechanisms
- Type II: Practical validation of control execution
The primary distinction lies in the temporal and substantive nature of the assessment. A Type I report provides an initial validation of an organization's security control design, essentially offering a theoretical blueprint of the company's security infrastructure.
Here is a comparison of SOC 2 Type I and Type II reports to clarify their strategic relevance:
| Attribute | SOC 2 Type I | SOC 2 Type II |
|---|---|---|
| Assessment Frequency | One-time snapshot | Ongoing, annual cycle |
| Assurance Level | Initial confidence | Full operational test |
| Audit Cost | Generally lower | Higher due to duration |
| Use Case | Early-stage trust | Mature security proof |
Comparative Analysis of SOC 2 Report Types
Organizations typically progress through SOC 2 reporting in a strategic manner:
- Initial Type I report establishes baseline security controls
- Subsequent Type II report demonstrates sustained control effectiveness
- Ongoing Type II reports validate continuous improvement
- Regular updates maintain compliance and stakeholder confidence
- Iterative process refines security management strategies
SOC 2 Type II reports represent the gold standard for demonstrating comprehensive security commitment and operational excellence.
Practical Implications for Organizations
The choice between Type I and Type II reports depends on several critical factors:
- Organizational maturity
- Stakeholder requirements
- Industry regulatory expectations
- Complexity of security infrastructure
- Customer trust considerations
Pro tip: Consider initiating with a Type I report and strategically transitioning to Type II to demonstrate progressive security management and build stakeholder confidence.
Compliance Steps for Risk Officers
Risk officers play a pivotal role in navigating the complex landscape of SOC 2 compliance, requiring a strategic and methodical approach to security assessments. Security compliance checklist provides critical guidance for implementing comprehensive risk management strategies.
Successful SOC 2 compliance requires risk officers to focus on several key strategic domains:
-
Comprehensive Risk Assessment
- Identify potential security vulnerabilities
- Evaluate existing control mechanisms
- Quantify potential operational risks
-
Control Design and Implementation
- Develop robust security policies
- Establish clear operational procedures
- Create measurable control objectives
-
Documentation and Evidence Management
- Maintain detailed security documentation
- Collect continuous operational evidence
- Prepare comprehensive audit trails
Effective compliance management demands a proactive and systematic approach that goes beyond simple checklist completion. Risk officers must develop a holistic understanding of their organization's security ecosystem, integrating technical controls with strategic governance frameworks.
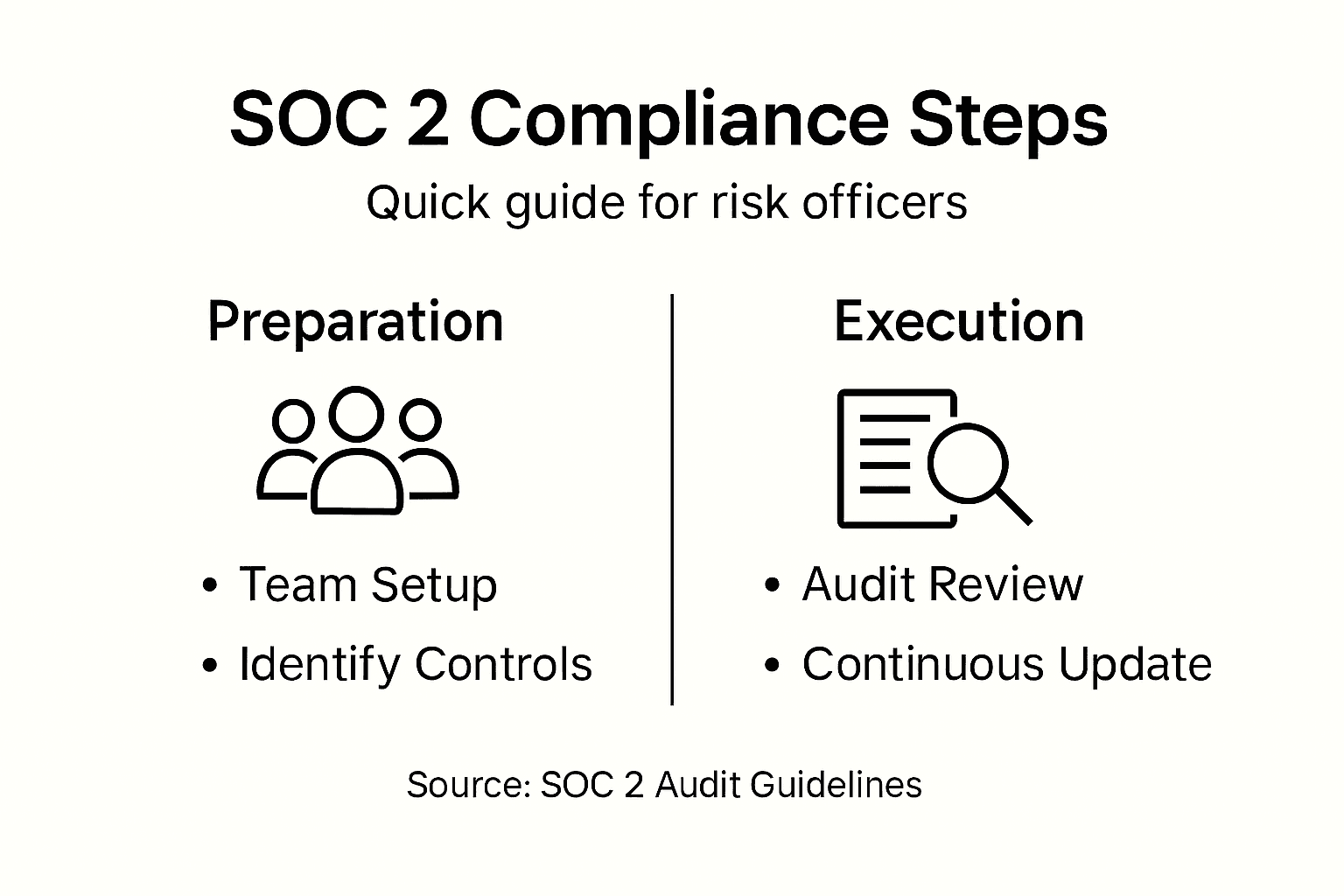
Strategic Compliance Implementation Steps
Risk officers should follow a structured approach to SOC 2 compliance:
- Conduct initial organizational risk assessment
- Map existing security controls against Trust Services Criteria
- Identify and remediate control gaps
- Develop comprehensive security documentation
- Implement continuous monitoring mechanisms
- Prepare for independent third-party audit
- Establish ongoing improvement protocols
Successful SOC 2 compliance transforms security from a procedural requirement into a strategic organizational advantage.
Key Considerations for Effective Compliance
Critical factors that risk officers must prioritize include:
- Alignment with organizational strategic objectives
- Scalability of security control frameworks
- Adaptability to evolving threat landscapes
- Integration of compliance across multiple business units
- Maintaining cost-effective implementation strategies
Pro tip: Develop a cross-functional compliance team that includes representatives from IT, legal, and operations to ensure comprehensive and integrated security management.
Common Pitfalls and Alternatives
Navigating SOC 2 compliance requires strategic awareness of potential challenges that can derail even the most well-intentioned security efforts. Common SOC 2 compliance challenges reveal critical areas where organizations frequently encounter obstacles in their security assessment journey.
Organizations typically encounter several significant SOC 2 compliance pitfalls:
-
Documentation Challenges
- Insufficient or outdated documentation
- Generic policies not tailored to organizational risks
- Lack of comprehensive evidence tracking
-
Operational Weaknesses
- Inadequate staff training
- Poor access control mechanisms
- Undefined compliance scope
-
Strategic Implementation Gaps
- Misalignment with organizational objectives
- Ineffective continuous monitoring
- Reactive instead of proactive compliance approach
Understanding these common pitfalls enables organizations to develop more robust and strategic compliance frameworks that transcend mere checkbox exercises. Successful SOC 2 compliance demands a holistic approach that integrates technical controls with organizational culture and strategic objectives.
Alternative Compliance Frameworks
When SOC 2 presents significant challenges, organizations can consider alternative compliance frameworks:
This table provides an overview of leading compliance frameworks and when they are most suitable:
| Framework | Industry Focus | Ideal For |
|---|---|---|
| SOC 2 | SaaS, Tech, Cloud | U.S.-based tech companies |
| ISO 27001 | All industries | Global and multinational firms |
| HITRUST | Healthcare, Pharma | U.S. healthcare providers |
| PCI DSS | Payment Processing | Businesses handling card data |
| NIST CSF | General, Government | Risk-based security programs |
- ISO 27001 - International information security standard
- HITRUST - Healthcare-focused comprehensive security framework
- NIST Cybersecurity Framework - Flexible risk management approach
- PCI DSS - Payment card industry data security standard
- GDPR - European data protection regulation
Selecting the right compliance framework requires careful evaluation of organizational needs, industry requirements, and strategic objectives.
Mitigation Strategies for Common Challenges
Effective SOC 2 compliance requires proactive strategies:
- Automate documentation processes
- Implement continuous training programs
- Develop clear, organization-specific policies
- Establish robust access control mechanisms
- Create cross-functional compliance teams
Pro tip: Conduct periodic internal audits and gap analyses to identify and address potential compliance weaknesses before external assessments.
Accelerate Your SOC 2 Compliance and Cut Security Response Time
SOC 2 Type Reports highlight the importance of strong internal controls and continuous monitoring but managing security questionnaires can delay certification and extend sales cycles. If you want to reduce the time spent on SOC 2 assessments and demonstrate operational excellence faster, Skypher's AI Questionnaire Automation Tool is designed exactly for your needs. It automates the completion of complex security reviews with unparalleled speed and accuracy, letting your team focus on what matters most—strengthening controls and building customer trust.

Discover how to streamline your SOC 2 compliance process and accelerate your security response times with Skypher's platform. Benefit from integrations with over 40 third-party risk management systems, real-time collaboration features, and a customizable Trust Center to showcase your security posture effortlessly. Take control of your cybersecurity narrative now and visit Skypher to transform SOC 2 complexities into competitive advantage.
Frequently Asked Questions
What is a SOC 2 Type Report?
A SOC 2 Type Report is an audit report that evaluates an organization's internal controls related to security, availability, processing integrity, confidentiality, and privacy. It serves to demonstrate compliance with industry standards and build trust with customers.
What is the difference between SOC 2 Type I and Type II reports?
SOC 2 Type I reports assess the design of controls at a specific point in time, while SOC 2 Type II reports evaluate the operational effectiveness of those controls over a longer period, typically 6-12 months.
Why are SOC 2 reports important for SaaS companies?
SOC 2 reports are crucial for SaaS companies as they validate security infrastructures, demonstrate regulatory compliance, build customer trust, and help identify areas for security improvements, ultimately facilitating sales.
How can organizations prepare for a SOC 2 audit?
Organizations can prepare for a SOC 2 audit by conducting thorough internal assessments, identifying potential control gaps, developing targeted improvement strategies, and engaging qualified independent auditors.