SOC 2 has quietly become the gold standard for security trust in B2B tech. Big brands are not just adopting it—companies with SOC 2 certification see sales cycle times shrink by up to 30 percent. Outsiders might think it is just another compliance box to tick, but the real shock comes when you realize SOC 2 unlocks cross-team value, pulling together security leaders and sales teams alike in the race for credibility. That level of strategic impact is anything but ordinary.
Table of Contents
- Understanding Soc 2 From Wikipedia Sources
- Soc 2 Trust Principles And Requirements
- Benefits Of Soc 2 For Tech Companies
- How CisOs And Sales Teams Leverage Soc 2
Quick Summary
| Takeaway | Explanation |
|---|---|
| SOC 2 Certification Builds Trust | Achieving SOC 2 certification demonstrates a commitment to data security, reassuring clients about your information protection practices. |
| Core Trust Criteria Matter | Focus on the five core criteria: security, availability, processing integrity, confidentiality, and privacy to enhance your operational controls. |
| SOC 2 Enhances Sales Processes | Companies with SOC 2 certification can accelerate their sales cycles by instilling confidence in potential clients about their security practices. |
| Continuous Improvement is Essential | Committing to ongoing security improvements helps maintain relevance in an evolving digital landscape, safeguarding your organization against new threats. |
| Cross-Functional Collaboration Boosts Value | Engaging multiple teams in the SOC 2 certification process creates unified security strategies and strengthens overall trustworthiness in the organization. |
Understanding SOC 2 From Wikipedia Sources
Security and compliance are critical concerns for modern businesses, and SOC 2 represents a crucial framework for demonstrating organizational commitment to data protection. Wikipedia provides comprehensive insights into this essential audit standard that helps organizations validate their information security practices.
The Origins and Framework of SOC 2
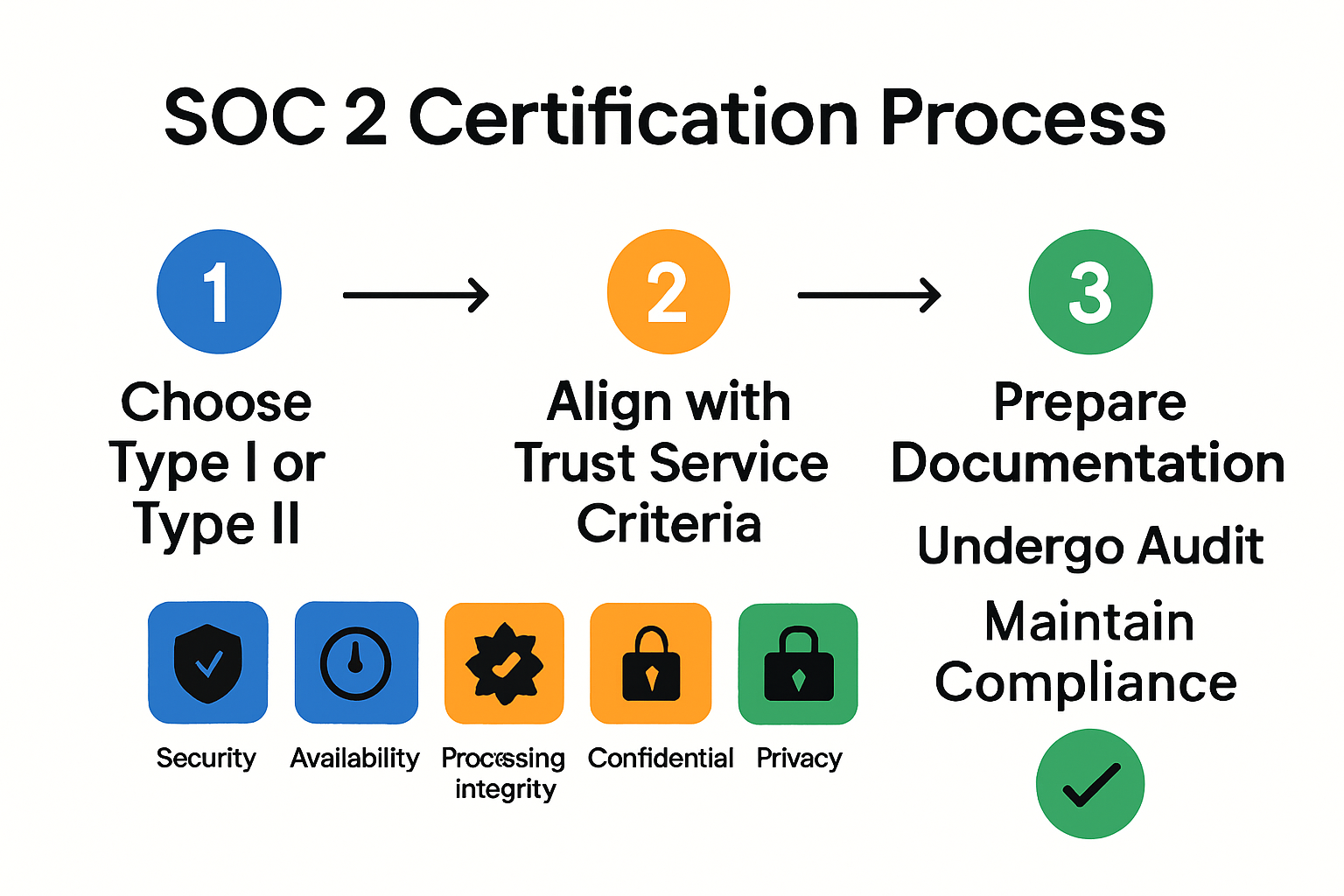
SOC 2 emerged from the American Institute of Certified Public Accountants (AICPA) as a specialized audit report designed to evaluate an organization's security controls and protocols. Unlike financial audits, SOC 2 focuses specifically on non-financial reporting systems. According to AICPA documentation, the framework assesses five core trust service criteria that organizations must demonstrate:
- Security: Protecting system resources against unauthorized access
- Availability: Ensuring systems are accessible and operational as agreed
- Processing Integrity: Maintaining system processing completeness, accuracy, and timeliness
- Confidentiality: Safeguarding confidential information throughout its lifecycle
- Privacy: Managing personal information collection, use, retention, and disclosure
These criteria provide a comprehensive approach to evaluating an organization's control environment, moving beyond traditional compliance checkboxes to create meaningful security assessments.
Key Compliance and Reporting Mechanisms
The SOC 2 report is not a one-size-fits-all certification but a detailed evaluation tailored to each organization's unique operational context. Companies can choose between two primary report types: Type I, which assesses the design of control systems at a specific point in time, and Type II, which examines the operational effectiveness of those controls over a defined period.
To help clarify the differences between SOC 2 Type I and Type II reports, the following table summarizes key aspects of each report type discussed in the article.
| Report Type | Focus | Assessment Period | Description |
|---|---|---|---|
| Type I | Control Design | Single point in time | Evaluates whether controls are suitably designed to meet trust criteria on a specific date. |
| Type II | Control Operating Effectiveness | Defined period (6–12 months) | Examines if controls function effectively over time, providing a more comprehensive overview. |
The Committee of Sponsoring Organizations of the Treadway Commission (COSO) plays a significant role in establishing internal control frameworks that complement SOC 2 standards. Their guidelines help organizations develop robust risk management and internal control strategies that align with SOC 2 requirements.
For B2B technology companies and service providers, SOC 2 compliance has become more than just a credential—it's a critical trust signal. Potential clients and partners view a successful SOC 2 audit as proof of an organization's commitment to maintaining rigorous security standards and protecting sensitive information.
Understanding SOC 2 from Wikipedia sources reveals it is not merely a technical checklist but a comprehensive approach to demonstrating organizational trustworthiness. By systematically evaluating security controls, availability, processing integrity, confidentiality, and privacy, companies can build confidence among stakeholders and differentiate themselves in an increasingly security-conscious marketplace.
SOC 2 Trust Principles and Requirements
The SOC 2 framework stands as a critical benchmark for organizations seeking to demonstrate their commitment to robust information security and privacy practices. Beyond a simple compliance checklist, these trust principles represent a comprehensive approach to protecting organizational and customer data.
Core Trust Service Criteria
SOC 2 is built upon five fundamental trust service criteria that provide a holistic framework for evaluating an organization's control environment. According to the AICPA's official guidance, these principles are not just theoretical constructs but practical mechanisms for ensuring comprehensive security:
-
Security: The foundational criterion addressing protection against unauthorized access. This principle requires organizations to implement robust mechanisms like multi-factor authentication, encryption, and network firewalls to prevent potential security breaches.
-
Availability: Ensures systems and services remain operational and accessible as committed. This involves maintaining infrastructure, implementing disaster recovery plans, and establishing performance monitoring protocols that guarantee consistent service delivery.
-
Processing Integrity: Validates that system processing is complete, accurate, timely, and authorized. Organizations must demonstrate mechanisms to ensure data transactions are processed correctly and without unintended modifications.
-
Confidentiality: Focuses on protecting sensitive information designated as confidential. This requires implementing strict access controls, data encryption, and secure transmission protocols to prevent unauthorized disclosure.
-
Privacy: Addresses the collection, use, retention, and disposal of personal information in alignment with established privacy principles and organizational commitments.
Comprehensive Evaluation Approach
The SOC 2 assessment goes beyond surface-level compliance, diving deep into an organization's control mechanisms. Wikipedia's documentation highlights that auditors conduct thorough examinations of both design and operational effectiveness, ensuring that security controls are not just documented but consistently implemented.
Two primary report types facilitate this comprehensive evaluation:
-
Type I Report: Assesses the design of control systems at a specific point in time, providing a snapshot of an organization's security framework.
-
Type II Report: Examines the operational effectiveness of those controls over a defined period, typically 6-12 months, offering a more dynamic and comprehensive assessment.
For B2B technology companies, these principles transcend mere regulatory compliance. They represent a commitment to building trust with customers, partners, and stakeholders by demonstrating a proactive approach to information security.
The rigorous nature of SOC 2 requirements means that organizations must continuously evolve their security practices. This dynamic approach ensures that trust principles remain relevant in an increasingly complex digital ecosystem, where technological threats and regulatory expectations are constantly changing.
Ultimately, SOC 2 trust principles provide a structured, comprehensive framework that enables organizations to validate their commitment to protecting critical information assets. By systematically addressing security, availability, processing integrity, confidentiality, and privacy, companies can build a robust foundation of trust in an era of increasing digital complexity and heightened security concerns.
Benefits of SOC 2 for Tech Companies
In the competitive landscape of technology services, SOC 2 certification has emerged as a critical differentiator for businesses seeking to establish credibility and trust. Wikipedia's documentation on System and Organization Controls highlights the strategic importance of this comprehensive security framework for tech companies looking to demonstrate their commitment to robust data protection.
Competitive Advantage and Market Differentiation
SOC 2 certification provides tech companies with a significant competitive edge in the marketplace. Unlike generic security claims, this rigorous audit process offers tangible proof of an organization's security capabilities. According to research from Gartner, companies with SOC 2 certification can potentially reduce sales cycle times by up to 30%, as potential clients view the certification as a concrete validation of security practices.
The benefits extend beyond mere compliance. Tech companies can leverage SOC 2 certification to:
Here is a summary table outlining the main internal and external benefits of achieving SOC 2 certification for technology companies, as highlighted in the article.
| Benefit Area | Key Benefit | Example(s) from Article |
|---|---|---|
| External | Competitive Advantage | Reduces sales cycle by up to 30%, builds customer confidence |
| External | Market Differentiation | Overcomes security due diligence, required by enterprise clients |
| Internal | Enhanced Operational Integrity | Develop robust controls and documentation, streamlines sales processes |
| Internal | Improved Risk Management | Identifies/address vulnerabilities, creates repeatable improvement processes |
| Both | Long-Term Strategic Value | Signals commitment to partners, investors, increases acquisition opportunities |
- Build Customer Confidence: Demonstrate a proactive approach to data protection
- Reduce Risk: Identify and address potential security vulnerabilities
- Streamline Sales Processes: Overcome security due diligence more quickly
Enhanced Operational Integrity and Risk Management
Beyond external perceptions, SOC 2 provides substantial internal benefits. The certification process compels organizations to develop more robust internal controls, creating a more secure and efficient operational environment. This systematic approach to security goes far beyond checkbox compliance, our guide on handling security questionnaires can provide additional insights into developing comprehensive security strategies.
The audit process requires tech companies to:
- Implement comprehensive security protocols
- Develop clear documentation of control mechanisms
- Create repeatable processes for ongoing security management
- Establish continuous improvement frameworks
Long-Term Strategic Value
For B2B technology companies, SOC 2 certification is more than a one-time achievement. It represents an ongoing commitment to security and operational excellence. The certification signals to potential clients, investors, and partners that an organization takes data protection seriously and has implemented sophisticated risk management strategies.
Particularly in industries handling sensitive information, SOC 2 has become a critical trust signal. Many enterprise clients now require SOC 2 certification as a prerequisite for doing business, effectively making it a must-have credential for tech companies seeking to work with larger organizations.
The financial implications are significant. Companies with robust SOC 2 certifications often see improved:
- Customer acquisition rates
- Partner trust and collaboration opportunities
- Potential for enterprise-level contracts
- Investor confidence
Ultimately, SOC 2 certification represents a strategic investment in an organization's reputation and operational capabilities. It transforms security from a potential liability into a competitive advantage, positioning tech companies as trustworthy, responsible, and forward-thinking partners in an increasingly complex digital ecosystem.
How CISOs and Sales Teams Leverage SOC 2
In the complex ecosystem of enterprise technology, SOC 2 certification has become a strategic tool for both Chief Information Security Officers (CISOs) and sales teams. This comprehensive framework provides a nuanced approach to demonstrating organizational security capabilities and building customer trust.
Strategic Security Positioning for CISOs
For CISOs, SOC 2 represents more than a compliance checkbox. Research from the Cloud Security Alliance highlights that SOC 2 provides external stakeholders with critical assurance while delivering internal benefits such as enhanced security infrastructure and operational reliability.
Key strategic advantages for CISOs include:
- Comprehensive Risk Assessment: Identifying and addressing potential security vulnerabilities
- Standardized Security Framework: Implementing robust, repeatable security protocols
- Continuous Improvement: Creating mechanisms for ongoing security enhancement
The audit process compels organizations to develop sophisticated internal control mechanisms, transforming security from a reactive function to a proactive strategic initiative. CISOs can use SOC 2 as a roadmap for building more resilient and transparent security architectures.
Sales Acceleration Through Compliance
Sales teams discover that SOC 2 certification becomes a powerful differentiator in competitive markets. Our guide on streamlining security questionnaires illustrates how compliance documentation can significantly accelerate sales cycles.
Specifically, SOC 2 enables sales teams to:
- Rapidly Build Customer Trust: Provide immediate credibility during enterprise sales discussions
- Overcome Security Objections: Demonstrate robust security practices proactively
- Differentiate from Competitors: Position the organization as a security-conscious partner
Cross-Functional Collaboration and Business Value
Academic research published on arXiv emphasizes that successful information security compliance depends on critical socio-organizational factors. These include management commitment, organizational awareness, technological capabilities, and continuous monitoring.
For B2B technology companies, SOC 2 transforms from a technical requirement to a strategic business asset. It bridges the communication gap between technical security teams and business-focused stakeholders, creating a shared language of trust and reliability.
The certification process requires cross-functional collaboration, compelling security, sales, legal, and executive teams to align their objectives. This collaborative approach ensures that security is not an isolated function but an integral part of the organization's value proposition.
Ultimately, SOC 2 serves as a powerful mechanism for CISOs to validate their security strategies and for sales teams to unlock new business opportunities. By demonstrating a holistic commitment to protecting customer data and maintaining rigorous security standards, organizations can differentiate themselves in an increasingly complex and security-conscious marketplace.

Frequently Asked Questions
What is SOC 2 certification?
SOC 2 certification is an auditing process that evaluates an organization's information security practices based on five core trust service criteria: security, availability, processing integrity, confidentiality, and privacy.
Why is SOC 2 important for B2B companies?
SOC 2 is vital for B2B companies as it builds trust with clients and partners by demonstrating a commitment to data security, often resulting in shorter sales cycles and enhanced competitive advantage.
How does SOC 2 differ from SOC 1?
SOC 2 is focused on non-financial reporting systems, assessing controls related to data security and privacy, while SOC 1 concentrates on financial reporting and internal controls related to financial transactions.
What are the benefits of obtaining SOC 2 certification?
The benefits of SOC 2 certification include increased customer confidence, streamlined sales processes, improved risk management, enhanced operational integrity, and long-term strategic value in the marketplace.
Turn SOC 2 Complexity Into Speed and Confidence with Skypher
B2B companies know the pressure of securing SOC 2 compliance and the hassle of endless, manual security questionnaires. Your teams deserve better than getting stuck on repetitive proof of trust. The article highlighted how critical a fast, reliable SOC 2 response is for closing deals quicker and building client trust. But without modern tools, even well-prepared companies struggle to streamline responses and keep sales momentum strong.

Bring new efficiency to your SOC 2 and security questionnaire process with Skypher. Our AI-powered tools automate your answers for every format, integrate painlessly with over 40 risk management platforms, and help your teams collaborate in real time. That means you can impress prospects, shorten proof of concept timelines, and show your clients that your security posture really stands out. See how our AI Questionnaire Automation Tool empowers both CISOs and sales teams. Visit https://skypher.co now and discover how to transform SOC 2 requirements into your competitive advantage today.
Recommended
- The different formats & mistakes made when writing or answering security questionnaires
- Features
- The ever growing number of security questionnaires and what you and your company can do to face it
- How to Manage Business Growth in South Africa: 2025 Guide - Ready Accounting
- Best Business Sustainability Practices for UK Success 2025 - BHA Couriers
