Many CISOs are surprised to learn that over 60 percent of medium and large technology firms misunderstand the true purpose of SOC 3 reporting. Getting clarity on the difference between confidential SOC 2 and public-facing SOC 3 documents matters for anyone looking to build trust with American customers or global partners. This article dives into common misconceptions and offers practical insights to help you master SOC 3 assessments and manage questionnaires with greater efficiency.
Table of Contents
- SOC 3 Reports Explained And Common Misconceptions
- Key Features And Structure Of SOC 3 Reports
- SOC 3 Vs SOC 2: Essential Differences
- SOC 3 Audit Process And Requirements For SaaS
- Benefits, Limitations, And Common Challenges
Key Takeaways
| Point | Details |
|---|---|
| SOC 3 Reports Provide Public Assurance | SOC 3 reports communicate an organization's security and privacy controls to the public without revealing sensitive details, promoting trust and transparency. |
| Distinct Roles of SOC 2 and SOC 3 | SOC 3 serves as a high-level overview for public use, while SOC 2 offers detailed technical insights for specific stakeholders, each fulfilling different compliance needs. |
| A Crucial Tool for SaaS Providers | For SaaS organizations, SOC 3 audits help build customer trust and market credibility by showcasing robust security practices without compromising proprietary information. |
| Benefits vs. Limitations | While SOC 3 reports enhance market credibility and public trust, their high-level nature limits technical insights, necessitating careful management of compliance documentation and monitoring. |
SOC 3 Reports Explained and Common Misconceptions
SOC 3 reports represent a strategic compliance mechanism designed to publicly communicate an organization's security and privacy controls without revealing sensitive operational details. Unlike confidential SOC 2 reports, these public-facing documents offer a high-level overview of an organization's commitment to security and trust. Organizations leverage SOC 3 reports as a transparent communication tool to demonstrate their robust security practices to potential customers, partners, and stakeholders.
The core purpose of SOC 3 reports revolves around providing public assurance through a standardized framework established by the American Institute of Certified Public Accountants (AICPA). Organizations use these reports to showcase their security posture across five critical Trust Services Criteria: security, availability, processing integrity, confidentiality, and privacy. These reports differ significantly from SOC 1 and SOC 2 reports, which are typically restricted and intended for specific audiences like auditors and potential business partners.
Common misconceptions about SOC 3 reports often stem from misunderstandings about their purpose and scope. Many professionals mistakenly believe that SOC 3 reports can replace comprehensive SOC 2 assessments, when in reality, they serve complementary but distinct functions. SOC 3 reports are designed for broad public distribution and marketing purposes, providing a simplified, non-confidential snapshot of an organization's control environment. They do not include the detailed testing procedures and specific control descriptions found in SOC 2 reports, making them more accessible but less technically rigorous.
Pro tip: When considering a SOC 3 report, focus on its value as a public trust document that signals your organization's commitment to security without compromising sensitive operational details.
Key Features and Structure of SOC 3 Reports
SOC 3 reports provide a standardized framework for organizations to communicate their security and control practices to a broader audience. These general-use reports offer a concise overview of an organization's control environment that balances transparency with confidentiality. Unlike more detailed compliance documents, SOC 3 reports are designed to be publicly accessible, enabling companies to demonstrate their commitment to robust security practices without revealing sensitive operational details.

The structural composition of a SOC 3 report typically includes several key components that provide a comprehensive yet high-level assessment of an organization's controls. These components include management's formal assertion about control effectiveness, an independent service auditor's opinion, and a description of the system's boundaries and service commitments. The report comprehensively covers critical Trust Services Criteria, focusing on four primary domains: security, availability, confidentiality, and privacy. Each section is carefully crafted to provide meaningful insights while maintaining a level of abstraction that protects the organization's internal methodologies.
One of the most distinctive features of SOC 3 reports is their flexibility and broad applicability across different industries and service types. Organizations can leverage these reports to build public trust by showcasing their adherence to rigorous security standards established by the American Institute of Certified Public Accountants (AICPA). The reports follow a standardized format that allows stakeholders to quickly understand an organization's security posture without requiring deep technical expertise. This accessibility makes SOC 3 reports particularly valuable for marketing, sales, and public communication efforts, enabling companies to differentiate themselves in competitive markets.
Pro tip: When preparing a SOC 3 report, focus on creating a clear, concise narrative that highlights your organization's commitment to security while maintaining the necessary level of confidentiality.
SOC 3 vs SOC 2: Essential Differences
SOC 2 and SOC 3 reports represent two distinct approaches to communicating an organization's security controls, each serving unique purposes in the compliance landscape. Understanding the nuanced differences between SOC Type II reports and SOC 3 reports is crucial for organizations seeking to demonstrate their commitment to robust security practices. While both reports are based on the same Trust Services Criteria established by the American Institute of Certified Public Accountants (AICPA), they differ significantly in audience, detail level, and distribution parameters.
The primary distinction between SOC 2 and SOC 3 reports lies in their intended audience and confidentiality. SOC 2 reports are highly detailed, confidential documents typically shared only with specific stakeholders such as potential business partners, investors, and auditors. These reports include extensive documentation of control testing procedures, specific control descriptions, and comprehensive evidence of security effectiveness. In contrast, SOC 3 reports are designed for public consumption, offering a high-level, non-confidential overview of an organization's security controls that can be freely distributed and used for marketing and public relations purposes.
From a practical standpoint, organizations often utilize both report types as complementary tools in their security communication strategy. SOC 2 reports provide in-depth technical validation for critical stakeholders who require granular insights into security practices, while SOC 3 reports serve as a public-facing document that demonstrates a commitment to security without revealing sensitive operational details. This approach allows companies to balance transparency with the need to protect proprietary information, effectively communicating their security posture to different audiences with varying levels of technical expertise.
Pro tip: Consider developing both SOC 2 and SOC 3 reports as part of a comprehensive security communication strategy, tailoring your approach to different stakeholder needs and compliance requirements.
Here's a concise comparison of SOC 3 and SOC 2 reports for quick reference:
| Aspect | SOC 3 Report | SOC 2 Report |
|---|---|---|
| Audience | General public | Specific stakeholders |
| Detail Level | High-level overview | Detailed technical analysis |
| Distribution | Freely distributable | Restricted access |
| Purpose | Public trust, marketing | Deep compliance validation |
SOC 3 Audit Process and Requirements for SaaS
SOC 3 audits represent a critical compliance mechanism for SaaS providers seeking to demonstrate their security commitment to potential customers and stakeholders. The comprehensive audit process evaluates an organization's controls against stringent AICPA Trust Services Criteria, ensuring that critical security standards are consistently met and maintained. These audits go beyond simple checkbox compliance, requiring SaaS companies to develop robust, documented policies and implement sophisticated operational controls that protect sensitive information and system integrity.
The SOC 3 audit process for SaaS organizations typically follows a structured pathway that begins with extensive preparation and documentation. Companies must first establish comprehensive policies covering five primary domains: security, availability, processing integrity, confidentiality, and privacy. Independent Certified Public Accountants (CPAs) conduct thorough evaluations, examining not just the design of these controls but their actual operational effectiveness. Unlike more restrictive compliance assessments, the SOC 3 audit provides a pathway for organizations to publicly validate their security practices without revealing sensitive internal details.
For SaaS providers, the SOC 3 audit serves as a strategic tool for building market credibility and customer trust. The audit process requires continuous monitoring and improvement of security controls, pushing organizations to maintain high standards of operational excellence. By successfully completing a SOC 3 audit, SaaS companies can differentiate themselves in competitive markets, demonstrating a proactive approach to cybersecurity that goes beyond minimal compliance requirements. The public-facing nature of SOC 3 reports allows companies to showcase their security maturity to potential clients, investors, and partners without compromising proprietary information.
Pro tip: Approach the SOC 3 audit as a continuous improvement process, regularly reviewing and updating your security controls to stay ahead of emerging technological risks and compliance requirements.
Benefits, Limitations, and Common Challenges
SOC 3 reports offer organizations a powerful mechanism for communicating security commitments, but understanding their complete landscape requires careful evaluation. Organizations must navigate the nuanced benefits and potential constraints of these public-facing compliance documents, recognizing that strategic implementation can significantly enhance market credibility while presenting unique operational challenges.
The key benefits of SOC 3 reports are multifaceted, extending beyond simple compliance checkboxes. These reports provide a transparent mechanism for building public trust, offering potential customers and stakeholders a clear window into an organization's security practices. Marketing teams can leverage SOC 3 reports as powerful communication tools, demonstrating security maturity without divulging sensitive technical details. Small and medium-sized technology companies particularly benefit from this approach, as it enables them to compete with larger enterprises by showcasing robust security frameworks in an accessible, non-technical format.
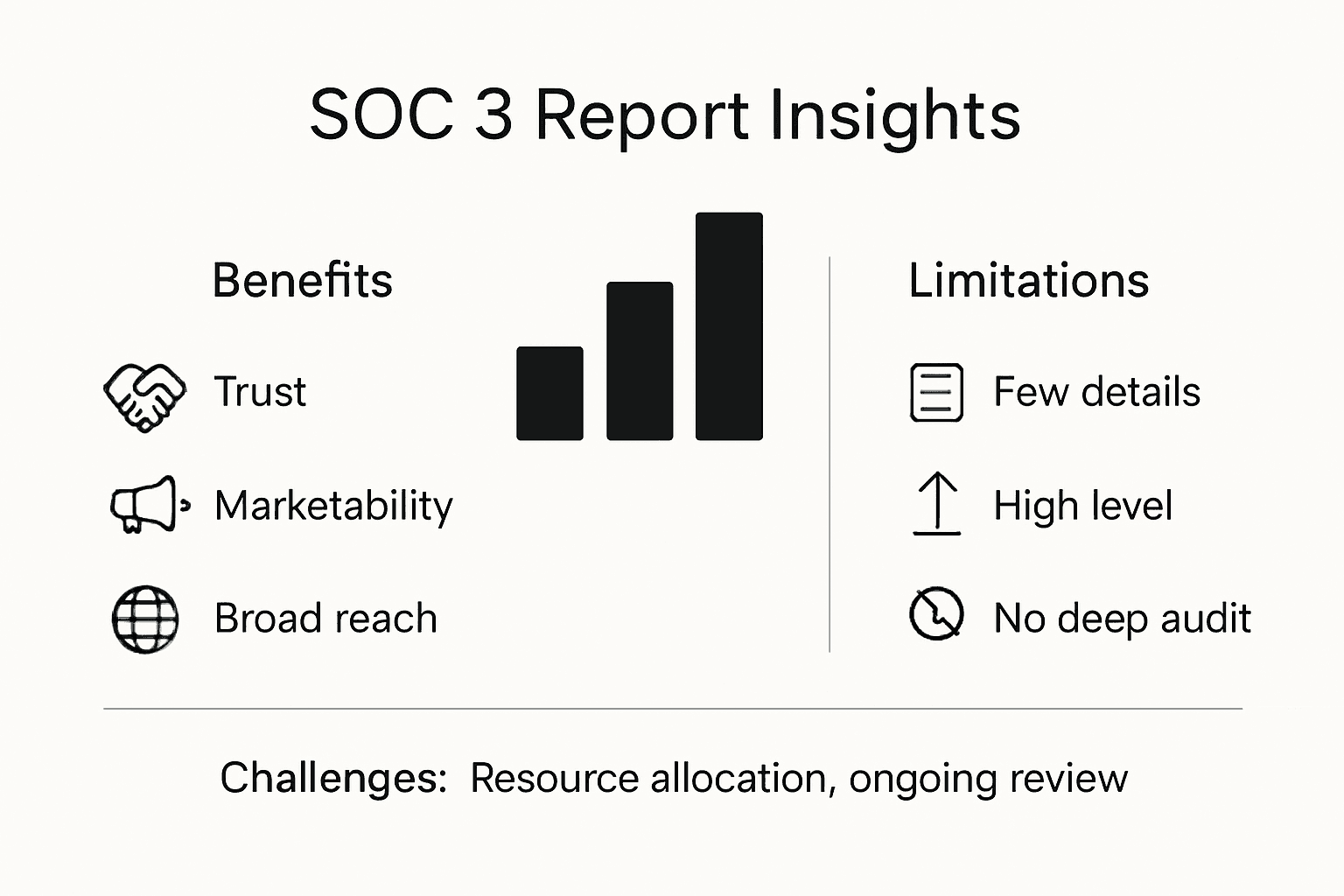
However, SOC 3 reports are not without significant limitations. The high-level nature of these reports means they lack the granular details found in more comprehensive SOC 2 assessments, which can limit their utility for organizations requiring deep technical due diligence. Challenges in maintaining continuous compliance include constantly evolving technological landscapes, complex internal control environments, and the need for ongoing documentation and monitoring. SaaS providers must invest substantial resources in preparing and maintaining the systematic controls necessary to successfully navigate SOC 3 audit processes, balancing operational efficiency with rigorous security standards.
Pro tip: Treat your SOC 3 report preparation as a strategic initiative, allocating dedicated resources to develop and maintain comprehensive security controls that exceed minimal compliance requirements.
Below is a summary of key benefits and challenges associated with SOC 3 reports:
| Benefit | Limitation | Common Challenge |
|---|---|---|
| Builds public trust | Lacks technical details | Maintaining documentation |
| Enhances market credibility | Limited due diligence value | Consistent monitoring |
| Supports marketing efforts | Not suitable for audits | Resource allocation |
Streamline SOC 3 Compliance and Enhance Public Trust with Skypher
Managing the complexities of SOC 3 reports requires a clear, organized approach to documenting and responding to security controls. This article highlights the challenge SaaS companies face in preparing comprehensive yet public-friendly compliance reports that build trust without exposing sensitive details. At the core is the need to efficiently handle detailed questionnaires and maintain continuous security validation while communicating confidently with diverse stakeholders.
Skypher offers a powerful solution tailored for organizations striving to excel in SOC 3 compliance and beyond. Our AI Questionnaire Automation Tool saves you time by completing hundreds of security questions in minutes with unmatched accuracy. Integrated with over 30 enterprise platforms like ServiceNow and OneTrust, and collaboration tools including Slack and MS Teams, Skypher ensures your security teams and sales departments stay aligned and proactive. Our customizable Trust Center helps you showcase your security posture publicly without sacrificing confidentiality, perfectly complementing SOC 3 report objectives.

Take control of your SOC 3 audit preparation today. Visit Skypher to discover how to accelerate your security questionnaire response process and demonstrate public trust effortlessly. Streamline your compliance workflow with automation designed for tech and finance sectors and reduce audit friction through real-time collaboration and powerful API integrations. Start building stronger, transparent relationships with your customers now.
Frequently Asked Questions
What is a SOC 3 report?
A SOC 3 report is a public document that provides a high-level overview of an organization's security and privacy controls, designed to communicate trust without revealing sensitive details.
How does a SOC 3 report differ from a SOC 2 report?
A SOC 3 report is intended for public consumption and offers a simplified summary of security controls, while a SOC 2 report is a detailed, confidential document shared with specific stakeholders for in-depth compliance verification.
Why should my SaaS company consider obtaining a SOC 3 report?
Obtaining a SOC 3 report can enhance your SaaS company’s credibility, help to build public trust, and serve as a marketing tool to demonstrate your commitment to security practices without compromising operational information.
What are the key components included in a SOC 3 report?
A SOC 3 report typically includes management's assertion about control effectiveness, an independent auditor's opinion, and a description of the system's service commitments, covering critical Trust Services Criteria such as security, availability, confidentiality, and privacy.
Recommended
- Understanding the SOC Report: What It Is and Why It Matters
- Understanding SOC 2 AICPA: Your Guide to Compliance
- Complete Guide to SOC Type II Reports
- Understanding SOC II Type 1: What You Need to Know
- Cloud Security and Compliance for Insurers: Navigating 2025 Risks - Digital Insurance Platform | IBSuite Insurance Software | Modern Insurance System