SOC certification is quickly becoming a make or break factor for companies dealing with sensitive data and internal controls. Yet, even as demand surges, 62 percent of small to medium businesses struggle with SOC 2 requirements directly due to resource constraints. Most assume that only big corporations need to care about these standards, but smaller teams face the most pressure from clients and regulators. Here is why the path to SOC certification in 2025 holds more surprises—and bigger advantages—than most organizations realize.
Table of Contents
- Understanding Soc Certification And Its Types
- Key Steps To Achieve Soc Certification
- Common Challenges And How To Overcome Them
- Soc Certification Benefits For Your Business
Quick Summary
| Takeaway | Explanation |
|---|---|
| Understanding SOC Certification Types is Essential | Organizations should be aware of the three primary SOC report categories—SOC 1, SOC 2, and SOC 3—to select the certification that aligns with their operational needs and industry expectations. |
| Strategic Steps are Necessary for Certification | Achieving SOC certification requires clear scoping, conducting a comprehensive gap analysis, and thorough audit preparation to ensure compliance with security standards. |
| Prepare for Common Challenges | Organizations face resource constraints, cybersecurity alert overload, and expanding attack surfaces during the certification process. Strategic planning and investing in automation can help navigate these challenges. |
| Certification Offers Significant Business Benefits | Beyond compliance, SOC certification enhances customer trust, mitigates risks, and enables strategic business improvements, thus transforming security into a competitive advantage. |
| Continuous Improvement is Key | SOC certification is an ongoing commitment, necessitating organizations to continuously monitor and adapt their controls to meet evolving security demands. |
Understanding SOC Certification and Its Types
SOC certification represents a critical framework for organizations to demonstrate their commitment to robust security and operational controls. These standardized assessments provide comprehensive insights into an organization's internal systems, processes, and risk management strategies.
The Core Types of SOC Certification
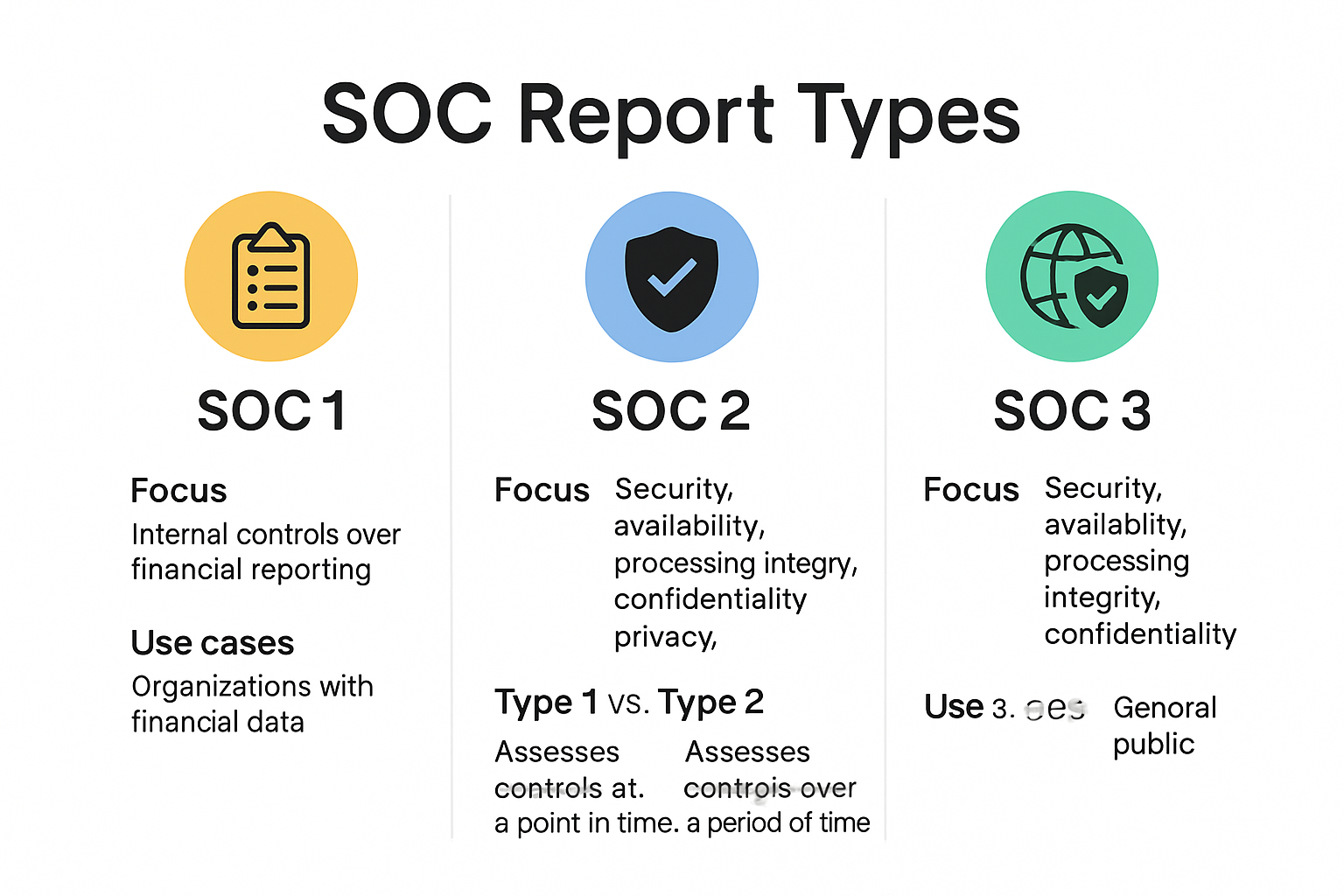
Understanding the distinct SOC certification types is crucial for businesses seeking to validate their operational integrity. The American Institute of CPAs (AICPA) has developed three primary SOC report categories, each serving unique organizational needs:
-
SOC 1: Specifically focused on financial reporting controls. This certification ensures that organizations maintain accurate and reliable financial systems and processes. Companies in finance, banking, and accounting frequently pursue SOC 1 certification to demonstrate their fiscal accountability.
-
SOC 2: The most comprehensive and widely adopted certification for technology and cloud service providers. According to Sprinto, SOC 2 evaluates five critical trust service criteria: security, availability, processing integrity, confidentiality, and privacy.
-
SOC 3: A generalized version of SOC 2 that provides a high-level overview of an organization's controls, suitable for public distribution and marketing purposes.
SOC 2 Report Variations: Type 1 vs Type 2
Within the SOC 2 framework, two distinct report types offer different levels of assurance. Sprinto's comprehensive guide explains these variations:
-
SOC 2 Type 1: Evaluates the design of an organization's controls at a specific point in time. This snapshot assessment examines whether the planned controls are appropriately structured to meet security and operational objectives.
-
SOC 2 Type 2: Provides a more rigorous evaluation by assessing the operational effectiveness of controls over a defined period, typically 12 months. As StrongDM notes, this report offers deeper insights into how consistently an organization maintains its security protocols.
For international organizations, it is worth noting that while SOC 2 is primarily used in North America, many businesses complement it with ISO/IEC 27001, a globally recognized information security management system certification.
The choice between different SOC certifications depends on several factors: industry requirements, organizational goals, customer expectations, and specific regulatory landscapes. Technology companies, cloud service providers, and financial institutions often find SOC 2 Type 2 most comprehensive for demonstrating their security and operational capabilities.
By pursuing SOC certification, organizations signal their commitment to transparency, risk management, and maintaining high standards of internal control. The certification process involves detailed audits conducted by independent certified public accountants who meticulously review an organization's systems, policies, and procedures.
Whether you are a startup looking to build trust or an established enterprise seeking to validate your operational excellence, understanding SOC certification types provides a strategic pathway to enhanced credibility and client confidence.
Key Steps to Achieve SOC Certification
Achieving SOC certification requires a strategic and systematic approach that demands careful planning, rigorous assessment, and consistent commitment to security standards. Organizations must navigate a complex process that transforms their internal controls and demonstrates operational excellence.
Defining the Certification Scope
The initial phase of SOC certification involves precise scoping and preparation. CertPro's comprehensive guide highlights the critical importance of determining the exact boundaries of your certification effort. This crucial step includes:
- Service Selection: Identifying which specific services or products will be included in the SOC audit
- Trust Service Criteria (TSCs): Selecting the relevant security principles that align with your organization's operational model
- Certification Type: Deciding between SOC 2 Type 1 or Type 2 based on organizational maturity and compliance requirements
According to Sprinto, the entire certification process typically spans 1 to 2 months, depending on the organization's size and complexity.
Comprehensive Gap Analysis and Control Implementation
After establishing the scope, organizations must conduct a thorough gap analysis of their existing cybersecurity infrastructure. This diagnostic process involves:
- Mapping current security practices against SOC 2 requirements
- Identifying potential vulnerabilities and control weaknesses
- Developing a detailed remediation plan to address identified gaps
CertPro's research emphasizes that many organizations overlook critical administrative and technological security measures during this phase. Key focus areas include:
- Documenting security policies and procedures
- Implementing robust access control mechanisms
- Establishing comprehensive incident response protocols
- Creating detailed employee security training programs
- Developing vendor management and risk assessment frameworks
Audit Preparation and External Attestation
The final stage involves preparing for the external audit and working with an independent certified public accountant. This phase requires:
- Compiling all necessary documentation
- Conducting internal readiness assessments
- Preparing evidence demonstrating control effectiveness
- Engaging with an accredited SOC auditor

The auditor will thoroughly examine your organization's controls, assessing their design and operational effectiveness. They will produce a detailed report highlighting strengths, potential improvements, and overall compliance with SOC standards.
Successful SOC certification is not a one-time achievement but an ongoing commitment to maintaining robust security practices. Organizations must continuously monitor, update, and improve their control environments to sustain their certification and adapt to evolving technological landscapes.
By following these structured steps and maintaining a proactive approach to security, businesses can successfully navigate the SOC certification process, ultimately building trust with clients, partners, and stakeholders.
Common Challenges and How to Overcome Them
SOC certification presents a complex journey fraught with potential obstacles that can derail even the most well-intentioned organizations. Understanding these challenges and developing strategic approaches to address them is crucial for successful certification.
Resource Constraints and Compliance Complexity
CGCompliance research reveals that 62% of small to medium enterprises struggle with SOC 2 requirements due to significant resource limitations. Organizations typically allocate approximately 15% of their IT budget toward achieving and maintaining compliance, which can strain already tight operational budgets.
To overcome these resource challenges, businesses can:
- Prioritize incremental improvements
- Leverage automation tools
- Consider phased implementation strategies
- Invest in targeted training programs
- Utilize external consulting services for efficient guidance
Cybersecurity Alert Overload and Threat Management
Splunk's State of Security report highlights a critical challenge: 46% of security leaders spend more time in maintenance mode, configuring and troubleshooting tools rather than strategically investigating threats. Additionally, 59% report being overwhelmed by the sheer volume of security alerts.
Effective strategies to manage this complexity include:
- Implementing advanced threat detection algorithms
- Developing clear incident response protocols
- Creating hierarchical alert prioritization systems
- Investing in artificial intelligence and machine learning tools
- Establishing dedicated security operations teams
Expanding Attack Surfaces and Evolving Threat Landscapes
Check Point Software's 2025 Security Report documents a startling 44% year-over-year increase in cyberattacks. Modern organizations face increasingly complex attack surfaces spanning on-premises infrastructure, multi-cloud deployments, SaaS platforms, and IoT devices.
To effectively mitigate these expanding risks, organizations should:
- Develop comprehensive, adaptive security frameworks
- Conduct regular vulnerability assessments
- Implement continuous monitoring systems
- Create cross-functional security awareness programs
- Maintain flexible, scalable security architectures
Successful SOC certification requires more than technical compliance. It demands a holistic approach that integrates technological solutions, strategic planning, and organizational culture. By anticipating challenges, investing in robust systems, and maintaining a proactive security mindset, businesses can transform potential obstacles into opportunities for enhanced operational resilience.
Remember that SOC certification is not a destination but an ongoing journey of continuous improvement and adaptation in an ever-evolving digital security landscape.
SOC Certification Benefits for Your Business
SOC certification transcends mere compliance requirements, offering strategic advantages that can fundamentally transform an organization's operational effectiveness, market positioning, and risk management capabilities. Understanding these multifaceted benefits helps businesses recognize the profound value of investing in comprehensive security standards.
Enhanced Customer Trust and Competitive Positioning
BeMo Pro research reveals that organizations with mature security programs experience 53% fewer security incidents and save an average of $2.9 million annually. Linford & Co emphasizes that a SOC report provides a critical competitive advantage by showcasing the effectiveness of an organization's operational and control environment.
Specific trust-building benefits include:
- Demonstrating commitment to rigorous security standards
- Providing transparent evidence of robust internal controls
- Differentiating from competitors lacking similar certifications
- Accelerating sales cycles through immediate credibility
- Reducing customer acquisition friction
Risk Mitigation and Operational Resilience
RSI Security's analysis highlights that SOC certification systematically minimizes organizational risks through comprehensive control assessments. By implementing stringent security protocols, businesses can:
- Proactively identify and address potential vulnerabilities
- Develop structured incident response mechanisms
- Create standardized security governance frameworks
- Establish consistent monitoring and reporting processes
- Reduce potential financial and reputational damages from security breaches
Strategic Business Enablement
Beyond immediate security benefits, SOC certification acts as a strategic business enablement tool. The certification process compels organizations to:
- Streamline internal processes and documentation
- Improve cross-departmental communication
- Develop more sophisticated technological infrastructures
- Create scalable security management approaches
- Build a culture of continuous improvement and accountability
The comprehensive nature of SOC certification means businesses are not just checking a compliance box but fundamentally enhancing their operational maturity. This holistic approach transforms security from a cost center into a strategic business asset.
By viewing SOC certification as an investment rather than an expense, organizations can unlock significant long-term value. The certification serves as a powerful signal to customers, partners, and stakeholders that your business takes security seriously and maintains world-class operational standards.
Ultimately, SOC certification represents more than technical compliance. It is a strategic declaration of your organization's commitment to excellence, transparency, and proactive risk management in an increasingly complex digital landscape.
Frequently Asked Questions
What is SOC certification?
SOC certification is a framework that organizations use to demonstrate their commitment to strong security and operational controls. It involves standardized audits that assess how well an organization's internal systems, processes, and risk management strategies comply with established security criteria.
What are the types of SOC certification?
There are three main types of SOC certification: SOC 1, SOC 2, and SOC 3. SOC 1 focuses on financial reporting controls, SOC 2 assesses security and operational measures for technology providers, and SOC 3 offers a high-level overview suitable for public distribution.
What is the difference between SOC 2 Type 1 and Type 2 reports?
SOC 2 Type 1 evaluates the design of controls at a specific point in time, while SOC 2 Type 2 assesses the operational effectiveness of these controls over a defined period, typically 12 months, providing a deeper analysis of ongoing security measures.
Why is SOC certification important for small to medium businesses?
SOC certification is crucial for small to medium businesses as it helps build customer trust, demonstrates compliance with security standards, and enhances competitiveness. It can also mitigate risks and improve operational resilience, especially when handling sensitive data.
Ready to Make SOC Certification in 2025 Easier Than Ever?
If navigating complex SOC 2 requirements and handling endless security questionnaires feels overwhelming, you are not alone. As this guide highlights, resource constraints and compliance bottlenecks can stall even the most ambitious teams. Imagine reclaiming hours from tedious questionnaire reviews and turning a pain point into a competitive advantage.

Take control and speed up your security compliance journey with Skypher's AI-driven Questionnaire Automation Tool. Experience fast, accurate responses to security reviews, seamless team collaboration, and stronger customer trust. Don’t let manual processes slow down your path to certification or your sales pipeline. Visit Skypher.co now to see how leading tech and finance teams are transforming compliance challenges into business wins. Get started today and turn compliance complexity into confidence and growth.
