Navigating the world of data security can feel intimidating, but understanding SOC 2 compliance is essential for any organization. In fact, more than 80 percent of businesses in tech and finance are prioritizing SOC 2 certification due to rising regulatory demands and customer expectations. But here’s the twist—achieving compliance is about much more than just checking boxes on a list. It's a chance to elevate your organization's security posture and build deeper trust with your clients. This isn't just about rules; it's about redefining how you manage and protect critical information in today's digital landscape.
Table of Contents
- Defining Soc 2 And Its Requirements
- The Trust Services Criteria Explained
- Meeting Soc 2 Requirements
- Getting Started With Soc 2 Compliance
Quick Summary
| Takeaway | Explanation |
|---|---|
| SOC 2 is critical for data protection | SOC 2 compliance is essential for organizations, especially in technology, healthcare, and finance, to demonstrate their commitment to secure data management and gain customer trust. |
| Five Trust Services Criteria guide compliance | Organizations must understand the five Trust Services Criteria—Security, Availability, Processing Integrity, Confidentiality, and Privacy—to effectively tailor their SOC 2 compliance efforts. |
| Robust documentation is essential | Producing key documents like the Management Assertion, System Description, and Control Matrix is necessary for demonstrating compliance effectiveness during audits. |
| Continuous improvement is vital | Successful SOC 2 compliance is not a one-time task; organizations must adopt a culture of ongoing risk assessment, policy updates, and security control evaluation to maintain compliance and enhance security practices. |
| Strategic approach to compliance is beneficial | Viewing SOC 2 requirements as opportunities for improvement rather than burdens can turn compliance into a competitive advantage, enhancing operational excellence and customer trust. |
Defining SOC 2 and Its Requirements
In the complex landscape of cybersecurity and data protection, SOC 2 stands as a critical framework for organizations seeking to demonstrate their commitment to secure and responsible data management. Unlike generic security certifications, SOC 2 provides a comprehensive approach to evaluating an organization's internal controls and operational processes.
What Exactly is SOC 2?
SOC 2 (Service Organization Control 2) is a rigorous compliance standard developed by the American Institute of Certified Public Accountants (AICPA) that focuses on how companies manage customer data. Sprinto explains that it is specifically designed to assess an organization's information systems and ensure they are structured to protect the confidentiality, processing integrity, and privacy of customer information.
The framework is unique because it is not a one-size-fits-all certification. Organizations can tailor their SOC 2 compliance to their specific operational needs by selecting from five Trust Service Criteria: Security (mandatory), Availability, Confidentiality, Processing Integrity, and Privacy. This flexibility allows businesses across different industries to demonstrate their commitment to data protection in a manner most relevant to their operational context.
The Core Requirements of SOC 2
Achieving SOC 2 compliance is a comprehensive process that requires organizations to provide extensive documentation and implement robust security controls. Secureframe highlights that the compliance process involves several critical components:
- Management Assertion: A formal statement from organizational leadership confirming the effectiveness of internal controls
- System Description: A detailed document outlining the organization's systems, processes, and security infrastructure
- Control Matrix: A comprehensive framework demonstrating how specific controls meet AICPA's stringent requirements
The compliance journey isn't just about documentation—it's about creating a genuine culture of security. Bitsight emphasizes that successful SOC 2 compliance involves continuous improvement through:
- Conducting thorough gap analysis of existing security measures
- Developing and implementing comprehensive security policies
- Establishing robust vendor risk management protocols
- Ensuring ongoing alignment with Trust Service Criteria
While the process might seem daunting, SOC 2 compliance is more than a checkbox exercise. It represents an organization's commitment to protecting sensitive data, maintaining customer trust, and demonstrating professional-grade security practices in an increasingly digital world.
For businesses operating in technology, cloud services, healthcare, finance, and other data-sensitive sectors, SOC 2 is not just recommended—it has become an essential standard that signals reliability, transparency, and a proactive approach to cybersecurity.
The Trust Services Criteria Explained
In the intricate world of information security and data protection, the Trust Services Criteria (TSC) serve as a comprehensive framework that enables organizations to establish, implement, and validate robust control mechanisms. These criteria provide a structured approach to assessing an organization's capacity to protect sensitive information and maintain operational excellence.
Understanding the Five Trust Services Criteria
CBH Insights explains that the Trust Services Criteria encompass five distinct categories, each addressing a critical aspect of organizational security and operational integrity. While organizations have the flexibility to select which criteria are most relevant to their operations, the Security criterion remains mandatory for all SOC 2 audits.
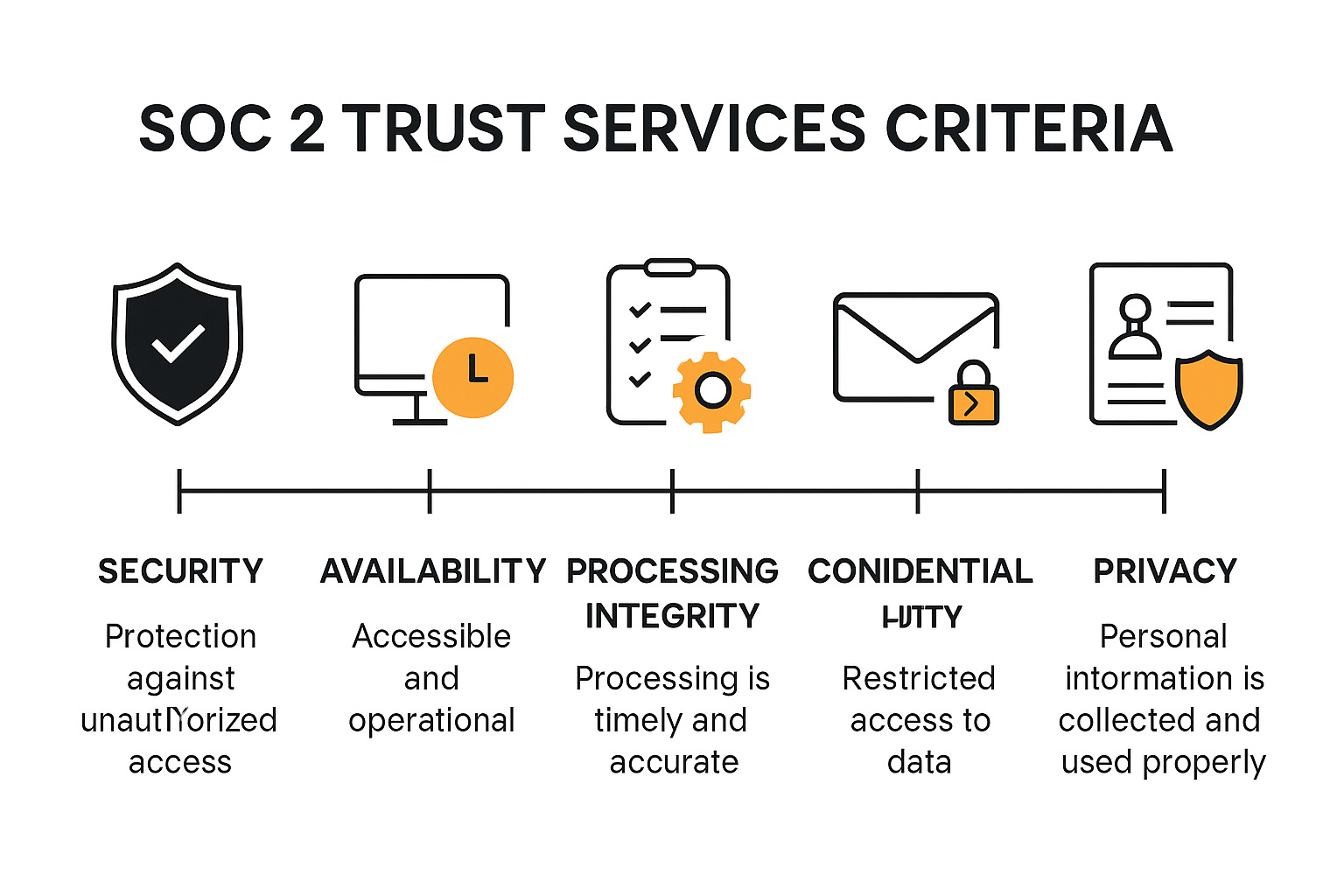 The five Trust Services Criteria include:
The five Trust Services Criteria include:
- Security: The foundational criterion that protects against unauthorized access and system vulnerabilities
- Availability: Ensures systems and services are accessible and operational as committed
- Processing Integrity: Validates that system processing is complete, accurate, and timely
- Confidentiality: Restricts access and use of confidential information
- Privacy: Safeguards personal information collection, use, retention, and disclosure
Deep Dive into Security and Operational Controls
Secureframe highlights that each criterion is designed to address specific organizational challenges. The Security criterion, being the most comprehensive, requires organizations to implement multi-layered controls that protect information systems against potential threats.
Key components of the Security criterion include:
- Risk Assessment: Systematically identifying and evaluating potential security risks
- Access Control: Implementing robust mechanisms to manage user authentication and authorization
- System Operations: Maintaining consistent and secure system performance
- Change Management: Establishing protocols for managing system modifications and updates
Beyond Security, the other criteria play crucial roles in comprehensive organizational governance. Availability ensures that systems meet predefined operational commitments, Processing Integrity guarantees data accuracy and completeness, Confidentiality protects sensitive information from unauthorized disclosure, and Privacy manages personal data in compliance with regulatory standards.
The beauty of the Trust Services Criteria lies in their adaptability. Organizations can customize their approach, selecting the most relevant criteria that align with their specific industry requirements, operational model, and risk profile. This flexibility allows businesses across various sectors—from technology and healthcare to finance and cloud services—to demonstrate their commitment to robust information security and operational excellence.
 Ultimately, the Trust Services Criteria represent more than a compliance checklist. They embody a holistic approach to information protection, encouraging organizations to develop a culture of continuous improvement, risk management, and strategic security planning.
Ultimately, the Trust Services Criteria represent more than a compliance checklist. They embody a holistic approach to information protection, encouraging organizations to develop a culture of continuous improvement, risk management, and strategic security planning.
Meeting SOC 2 Requirements
Navigating the complex landscape of SOC 2 compliance requires a strategic, comprehensive approach that goes beyond mere technical implementations. Organizations must develop a holistic framework that demonstrates their commitment to robust security practices, data protection, and continuous improvement.
Establishing a Robust Compliance Strategy
Sprinto emphasizes that meeting SOC 2 requirements begins with a comprehensive risk assessment tailored to your organization's unique operational environment. This means conducting an in-depth analysis of your current systems, identifying potential vulnerabilities, and developing targeted strategies to address these specific risks.
The compliance journey involves several critical steps:
- Comprehensive Risk Assessment: Thoroughly evaluate your organization's existing security infrastructure
- Gap Analysis: Identify discrepancies between current controls and SOC 2 requirements
- Control Implementation: Develop and deploy robust security mechanisms
- Continuous Monitoring: Establish ongoing evaluation and improvement processes
Critical Documentation and Compliance Evidence
Secureframe highlights the importance of creating three pivotal documents that form the core of your SOC 2 compliance effort:
- Management Assertion: A formal statement from leadership attesting to the effectiveness of internal controls
- System Description: A detailed narrative explaining the organization's systems, processes, and security infrastructure
- Control Matrix: A comprehensive framework demonstrating how specific controls meet AICPA's rigorous standards
These documents are not static artifacts but living frameworks that must evolve with your organization's changing risk landscape. Bitsight recommends a dynamic approach that includes:
- Regular policy updates
- Ongoing risk assessment
- Vendor risk management protocols
- Continuous control effectiveness monitoring
Successful SOC 2 compliance transcends a mere checklist—it represents a fundamental commitment to protecting customer data, maintaining operational integrity, and building trust. For technology companies, cloud service providers, financial institutions, and other data-sensitive organizations, this framework is not just a certification but a critical differentiator in a competitive marketplace.
The most successful organizations view SOC 2 requirements as an opportunity for strategic improvement rather than a compliance burden. By embracing a proactive, holistic approach to security and data protection, businesses can transform SOC 2 compliance from a regulatory requirement into a powerful competitive advantage that demonstrates their dedication to customer trust and operational excellence.
Getting Started With SOC 2 Compliance
Embarking on the SOC 2 compliance journey can seem daunting, but with a structured approach and strategic planning, organizations can navigate this complex process effectively. The path to compliance requires careful preparation, commitment, and a systematic methodology that transforms security requirements into actionable strategies.
Initial Preparation and Assessment
Sprinto recommends beginning the SOC 2 compliance process with a clear, methodical approach. The first critical step involves defining your specific compliance objectives and determining which type of SOC 2 report—Type 1 or Type 2—best suits your organization's needs.Key initial preparation steps include:
- Define Compliance Objectives: Clarify your organization's specific security and compliance goals
- Select Report Type: Choose between Type 1 (point-in-time assessment) and Type 2 (continuous performance evaluation)
- Conduct Internal Risk Assessment: Thoroughly evaluate your current security infrastructure
- Perform Gap Analysis: Identify areas requiring improvement before formal audit
Developing a Comprehensive Compliance Framework
Bitsight emphasizes the importance of a comprehensive readiness assessment that goes beyond surface-level compliance. This involves a deep evaluation of your organization's security posture against the Trust Service Criteria, with a particular focus on identifying and addressing potential control gaps.
Critical elements of building a robust compliance framework include:
- Policy Development: Create comprehensive security policies that align with SOC 2 requirements
- Control Implementation: Establish and document security controls across all relevant domains
- Documentation Preparation: Develop detailed documentation demonstrating control effectiveness
- Continuous Improvement: Create mechanisms for ongoing security enhancement
Navigating the Audit Process
Secureframe highlights the critical documentation required for a successful SOC 2 audit. Organizations must prepare three essential documents that will be scrutinized during the compliance assessment:
- Management Assertion: A formal statement from leadership about control effectiveness
- System Description: A comprehensive narrative explaining organizational systems and security processes
- Control Matrix: A detailed framework demonstrating how specific controls meet AICPA standards
Successful SOC 2 compliance is not a one-time achievement but an ongoing commitment to security excellence. Organizations must view this process as a continuous journey of improvement, regularly updating their security practices, reassessing risks, and demonstrating a proactive approach to protecting sensitive information.
For technology companies, cloud service providers, and organizations handling sensitive data, SOC 2 compliance is more than a checkbox—it's a strategic differentiator that builds customer trust, demonstrates operational maturity, and provides a competitive edge in an increasingly security-conscious marketplace.
Frequently Asked Questions
What is SOC 2 compliance?
SOC 2 compliance is a standard developed by the American Institute of Certified Public Accountants (AICPA) that evaluates how companies manage customer data based on stringent security criteria. It aims to ensure that organizations protect sensitive information and maintain customer trust.
What are the Trust Services Criteria in SOC 2?
The Trust Services Criteria in SOC 2 consist of five categories: Security (mandatory), Availability, Processing Integrity, Confidentiality, and Privacy. Organizations must meet the Security criterion and can choose the other criteria relevant to their operations.
How can my organization achieve SOC 2 compliance?
To achieve SOC 2 compliance, your organization should conduct a comprehensive risk assessment, implement robust security controls, create essential documentation (such as Management Assertion and Control Matrix), and undergo an audit process to validate adherence to SOC 2 requirements.
What is the difference between a Type 1 and Type 2 SOC 2 report?
A Type 1 SOC 2 report evaluates the effectiveness of your systems at a specific point in time, whereas a Type 2 report assesses the effectiveness of the systems over a defined period, typically six months to a year. Type 2 reports provide a deeper insight into ongoing compliance.
Elevate Your SOC 2 Compliance Journey with Skypher
Navigating the complexities of SOC 2 compliance doesn’t just involve rigorous documentation and stringent controls—it’s also about efficiency and accuracy. As you strive to meet the Trust Services Criteria while building trust with your clients, let Skypher's powerful AI Questionnaire Automation Tool become your trusted ally. Our platform is designed to streamline and automate the response process for security questionnaires, allowing organizations like yours to tackle compliance challenges head-on.

Imagine completing security reviews significantly faster and with higher accuracy, all while enhancing team collaboration and communication. With Skypher, you gain access to:
- Real-time collaboration features
- Seamless API integrations with over 40 third-party risk management platforms
- A customizable Trust Center tailored to your specific needs
Don't let the challenge of SOC 2 compliance become a burden. Act now to transform how your organization manages security and compliance. Experience the Skypher advantage today by visiting skypher.co—because meeting compliance should empower you, not weigh you down.
