SOC reports are essential for businesses navigating today's complex regulatory landscape. A staggering 40 percent of organizations that adequately prepare for SOC 2 audits achieve compliance on their first attempt. But here's the surprising truth: most companies underestimate the preparation required. The real challenge lies not in the audit itself but in the culture of compliance that needs to be fostered well before that first review. With the right strategies in place, the SOC audit process can transform from a daunting task into a powerful tool for enhancing security and building client trust.
Table of Contents
- Understanding Soc Reports Audit Basics
- Soc Audit Types And Standards
- Preparing For Soc Reports Audit
- Expert Compliance Tips & Techniques
Quick Summary
| Takeaway | Explanation |
|---|---|
| Clearly Define Scope and Timeline | Establishing a precise scope for what will be audited and a realistic timeline is crucial for a smooth SOC audit process. This includes determining relevant processes, systems, and Trust Services Criteria. |
| Conduct Thorough Risk Assessment and Gap Analysis | Performing a detailed risk assessment helps to identify vulnerabilities and control deficiencies, enabling organizations to implement necessary remediation actions before the audit. |
| Automate Evidence Collection and Monitoring | Utilizing automated tools for evidence gathering and monitoring transforms compliance into an ongoing process, saving time during the audit and enhancing overall security by promptly identifying control failures. |
| Foster a Culture of Compliance | Creating an organizational culture that prioritizes security and compliance through training, accountability, and transparency can greatly enhance the effectiveness of SOC audits. |
| Optimize Audit Scope through Smart Design | Strategically limiting the scope of the audit to relevant areas can reduce complexity and cost, allowing organizations to focus their compliance efforts where they matter most. |
Understanding SOC Reports Audit Basics
SOC (System and Organization Controls) reports have become critical tools in the modern business landscape, particularly for organizations that provide services affecting their clients' financial reporting or handle sensitive data. These specialized audit reports offer assurance about a service organization's controls, but understanding their fundamentals requires clarity on several key aspects.
What Are SOC Reports?
SOC reports are independent audit assessments that evaluate a service organization's controls relevant to security, availability, processing integrity, confidentiality, or privacy. These reports resulted from the American Institute of Certified Public Accountants (AICPA) establishing standards for service auditors to assess the internal controls of service organizations.
The term "SOC" stands for System and Organization Controls, which reflects their purpose of examining how well a company designs and implements controls to mitigate various risks. These reports serve as validation that a service provider maintains appropriate safeguards when handling client data or providing services that impact financial reporting.
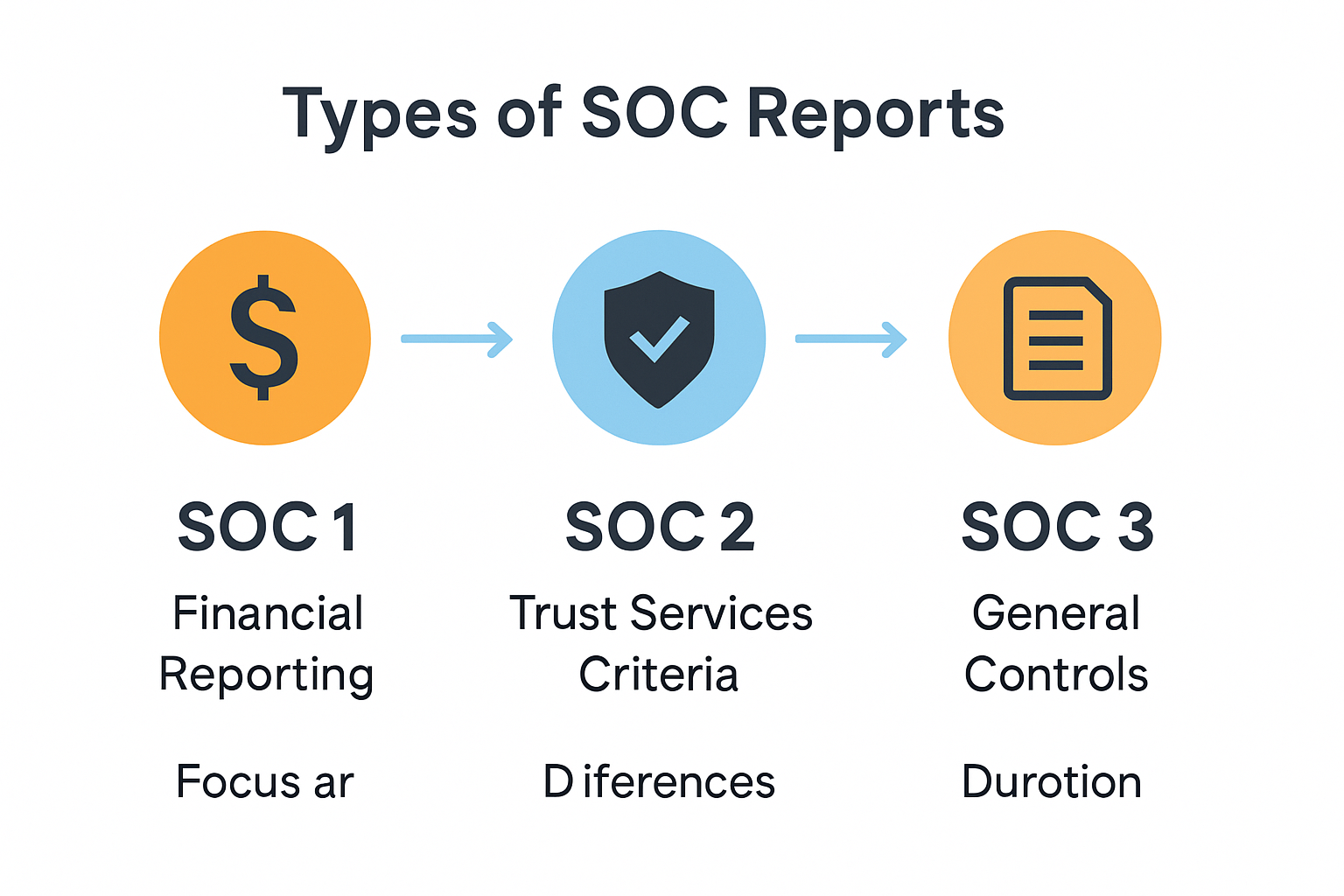
There are three primary types of SOC reports:
- SOC 1 - Focuses on controls relevant to financial reporting
- SOC 2 - Addresses controls relevant to security, availability, processing integrity, confidentiality, and privacy
- SOC 3 - A publicly shareable, condensed version of SOC 2 without sensitive details
The SOC Audit Process
Understanding how SOC audits work helps organizations prepare effectively. SOC reports are generally performed through seven main stages as part of a structured examination process:
- Scoping - Defining what systems, processes, and controls will be included
- Walkthrough and control design - Documenting and understanding existing controls
- Gap assessment - Identifying weaknesses or missing controls
- Remediation - Addressing identified gaps (effort varies based on assessment results)
- Examination/testing - Auditors evaluate evidence of control effectiveness
- Report preparation - Compiling findings and assessments
- Issuance - Delivering the final report
According to SCH Group, the remediation stage effort depends significantly on the gap assessment results, with audit firms typically providing a remediation roadmap to facilitate compliance with the relevant SOC criteria.
Type 1 vs. Type 2 Examinations
Another fundamental distinction in SOC audits is between Type 1 and Type 2 examinations. This classification applies to both SOC 1 and SOC 2 reports but reflects different assessment approaches:
Type 1 reports evaluate the design and implementation of controls at a specific point in time. For example, a SOC 1 Type 1 report reviews the system description and evaluates whether controls are suitably designed as of a specified date, with minimal control testing. These reports focus primarily on management's identification of internal controls relevant to financial reporting, as noted by Warren Averett.
Type 2 reports, by contrast, examine both the design and operating effectiveness of controls over a specified period (usually 6-12 months). This more rigorous assessment provides greater assurance because it demonstrates sustained compliance over time rather than a single snapshot.
The business context for SOC reports extends beyond simple compliance. Section 404 of the Sarbanes-Oxley Act (SOX 404) requires independent auditors to issue an opinion on the effectiveness of internal control over financial reporting. This requirement makes SOC reports critical tools for corporate compliance and internal control evaluation across many industries.
Understanding these SOC audit basics helps organizations approach the process with confidence and clarity. Whether preparing for your first SOC examination or seeking to understand a vendor's SOC report, grasping these fundamentals provides the necessary foundation for making informed business decisions about compliance, risk management, and service provider assessment.
SOC Audit Types and Standards
Navigating the landscape of SOC audit types requires understanding the distinct frameworks designed for different business needs. Each type of SOC report serves specific purposes and follows particular standards established by the American Institute of Certified Public Accountants (AICPA). Let's examine these variations in detail to help you determine which is most relevant for your organization.
SOC 1: Financial Controls Focus
SOC 1 reports concentrate specifically on internal controls over financial reporting (ICFR). These reports are essential for service organizations whose activities might affect their clients' financial statements. For example, payroll processors, loan servicing companies, and data centers handling financial information typically need SOC 1 reports.
SOC 1 reports follow the Statement on Standards for Attestation Engagements (SSAE) No. 18, specifically the AT-C section 320 (formerly SSAE 16). This standard provides guidance for examining and reporting on controls at service organizations relevant to user entities' internal control over financial reporting.
Within the SOC 1 framework, there are two variants:
- SOC 1 Type 1: Evaluates control design appropriateness at a specific point in time
- SOC 1 Type 2: Examines both design appropriateness and operational effectiveness over a period (usually 6-12 months)
While Type 1 reports provide a snapshot assessment, Type 2 reports offer deeper assurance through testing control effectiveness over time. Organizations often start with Type 1 before progressing to the more rigorous Type 2 examination.
SOC 2: Trust Services Focus
Whereas SOC 1 addresses financial reporting controls, SOC 2 reports evaluate controls relevant to security, availability, processing integrity, confidentiality, and privacy. These reports are ideal for technology service providers, cloud computing organizations, and SaaS companies handling sensitive customer data.
The SOC 2 framework is built around the AICPA's Trust Services Criteria (TSC), with five core principles:
- Security: Protection against unauthorized access (mandatory)
- Availability: System availability for operation and use
- Processing Integrity: Complete, accurate, timely, and authorized processing
- Confidentiality: Protection of confidential information
- Privacy: Personal information handling and protection
According to IT Governance, security is the only mandatory category for all SOC 2 reports, while organizations can select which other criteria apply to their services based on relevant risks and client needs.
Like SOC 1, SOC 2 offers both Type 1 and Type 2 variants. SOC 2 audits comprehensively evaluate an organization's controls through several phases, including planning and scoping, fieldwork and testing, and reporting and review. Organizations that engage in regular internal testing report fewer issues during the external audit process, and proper scoping can reduce audit time by up to 20% by focusing efforts on relevant areas, as noted by CG Compliance Group.
SOC 3: Public-Facing Reports
SOC 3 reports represent a simplified, shareable version of SOC 2 reports. While they address the same Trust Services Criteria as SOC 2, they omit sensitive details about control implementation and testing results. This makes SOC 3 reports ideal for marketing purposes, public websites, and general distribution.
The key advantage of SOC 3 reports is their accessibility - organizations can freely share them without confidentiality agreements. They serve as trust badges that demonstrate compliance without revealing security details that could be exploited by malicious actors.
SOC 3 reports offer only a general use report (with no Type 1/Type 2 distinction). They're particularly valuable for organizations that want to publicly demonstrate their commitment to security and compliance without divulging sensitive information.
As data security concerns intensify, SOC 2 Type 2 attestation will become increasingly important for organizations committed to data security and privacy. Data from the Association of Certified Fraud Examiners (ACFE) indicates that organizations adequately preparing for SOC 2 audits experience a 40% higher success rate in achieving compliance on their first attempt.
Understanding these distinct SOC frameworks allows organizations to select the appropriate audit type based on their business model, client requirements, and regulatory needs - ultimately transforming compliance from a necessary burden into a competitive advantage.
Preparing for SOC Reports Audit
Effective preparation for a SOC audit can mean the difference between a smooth process that enhances your business reputation and a stressful experience that identifies numerous gaps. Whether you're pursuing a SOC 1 or SOC 2 report, proactive preparation is essential to position your organization for success. Let's explore key strategies to help you prepare effectively.
Defining Scope and Setting Timeline
The foundation of effective SOC audit preparation begins with clearly defining what will be examined. According to Scrut Automation, clearly defining the audit scope—including specific systems, processes, and Trust Services Criteria—is the foundational first step in preparing for a SOC 2 audit, ensuring the assessment is aligned with the organization's unique risks and objectives.
When establishing your scope, consider:
- Which systems and applications will be included
- Which business processes are relevant to the audit
- Which physical locations need assessment
- For SOC 2, which Trust Services Criteria apply to your business
Beyond scope definition, establishing a realistic timeline is crucial. The early establishment of an audit timeline with agreed-upon milestones and deadlines based on organizational complexity and audit scope facilitates smooth preparation and timely completion of the SOC audit process. Most organizations need 3-6 months to prepare for their first SOC 2 audit, with the actual audit fieldwork typically requiring 4-12 weeks depending on complexity.
Document your scope and timeline clearly, and secure stakeholder agreement before proceeding. This prevents scope creep and helps maintain progress throughout the preparation phase.
Conducting Risk Assessment and Gap Analysis
Once you've defined the scope, conducting a thorough internal risk assessment becomes critical. This process involves identifying and evaluating risks related to the services provided to clients and documenting the controls designed to mitigate those risks.
A comprehensive risk assessment should:
- Identify potential threats and vulnerabilities
- Evaluate the likelihood and potential impact of each risk
- Document existing controls that address identified risks
- Determine residual risk levels after considering control effectiveness
Following the risk assessment, perform a gap analysis to identify areas where controls may be missing or insufficient. This analysis involves comparing your current control environment against SOC requirements to identify deficiencies that need remediation before the audit begins.
Conducting a thorough internal risk assessment to identify, evaluate, and document risks and associated controls is critical for demonstrating compliance during a SOC audit. This assessment demonstrates to auditors that you understand your risk landscape and have implemented appropriate safeguards.
Implementing and Documenting Controls
With gaps identified, the next step is implementing or strengthening controls to address deficiencies. Effective controls should be both well-designed and consistently operated throughout the reporting period. For each control, develop clear documentation that includes:
- Control objective and description
- How the control addresses specific risks
- Who is responsible for performing the control
- How frequently the control is performed
- What evidence demonstrates control performance
Documentation is crucial during a SOC audit. Auditors will request evidence showing that controls operated effectively throughout the assessment period. For Type 2 audits especially, consistent operation over time is essential, so establish processes for generating and retaining evidence of control performance.
Beyond documentation, consider implementing a continuous monitoring program that regularly assesses control effectiveness. This approach helps identify and address issues before the auditor finds them, reducing the likelihood of exceptions in the final report.
Many organizations find that centralizing their control documentation and evidence in a governance, risk, and compliance (GRC) platform streamlines the audit process significantly. These tools provide a single repository for policies, procedures, control descriptions, and supporting evidence, making it easier to manage the audit process and respond quickly to auditor requests.
Preparing for a SOC audit requires significant effort, but this investment pays dividends beyond just receiving a clean report. The process of formalizing and documenting your control environment often leads to operational improvements, better risk management, and enhanced security practices that benefit your organization even beyond compliance requirements.
By following these preparation steps—defining scope, conducting risk assessments, and implementing robust controls with proper documentation—you'll position your organization for a successful SOC audit that validates your commitment to secure, well-controlled service delivery.

Expert Compliance Tips & Techniques
Successful SOC audits don't happen by accident. Organizations that consistently achieve clean SOC reports implement strategic approaches that go beyond basic preparation. These expert techniques can help streamline your compliance efforts while strengthening your overall security posture.
Automate Evidence Collection and Monitoring
One of the most challenging aspects of SOC compliance is collecting and maintaining evidence that demonstrates controls are operating effectively. Leading organizations are increasingly turning to automation to solve this challenge.
Automated evidence collection tools can:
- Capture control evidence on predetermined schedules
- Alert responsible parties when evidence collection is due
- Monitor control effectiveness continuously between audits
- Provide real-time visibility into compliance status
- Reduce the manual effort required for evidence maintenance
Implementing automated tools for continuous control monitoring transforms compliance from a point-in-time scramble into an ongoing, manageable process. This approach not only saves significant time during the audit but also improves your security posture by identifying control failures when they occur rather than months later during the audit.
Automation particularly shines in technical control areas such as access management, system configuration, vulnerability management, and log monitoring. For each of these domains, specialized tools can provide automated evidence collection and verification against your defined requirements.
Foster a Culture of Compliance
Technical controls alone can't ensure successful SOC audits. Organizations with mature compliance programs understand that creating a culture where security and compliance are valued throughout the organization is equally important.
To build this culture, consider these approaches:
- Executive sponsorship: Ensure leadership demonstrates commitment to compliance through both words and actions
- Clear accountability: Assign specific control responsibilities to individuals and teams
- Regular training: Provide role-specific training on security awareness and compliance expectations
- Compliance champions: Identify and empower representatives across departments to advocate for good security practices
- Transparent reporting: Share compliance status and issues openly to drive improvement
Data shows that organizations that adequately prepare for SOC 2 audits—such as by conducting regular internal testing—report fewer issues and have a 40% higher success rate in achieving compliance on the first attempt, according to findings from the Association of Certified Fraud Examiners (ACFE) as reported by CG Compliance Group.
By making compliance part of your organizational DNA rather than a separate initiative, you'll find that maintaining SOC requirements becomes more natural and sustainable over time.
Optimize Scope Through Smart Design
One often-overlooked compliance technique is strategically defining your audit scope. Rather than including everything in your environment, consider carefully what truly needs to be in scope based on what affects your service delivery.
Consider implementing an architecture that segregates in-scope systems from those that don't require compliance. This approach, sometimes called a compliance boundary or scope reduction strategy, can significantly reduce audit complexity and cost.
Common scope optimization techniques include:
- Network segmentation: Isolate in-scope systems from general business systems
- Data flow analysis: Carefully map data flows to identify true scope boundaries
- Cloud service utilization: Leverage compliant cloud services that have their own SOC reports
- Carve-out method: Where appropriate, use the carve-out method for subservice organizations
By properly defining the audit scope and aligning it with relevant Trust Services Criteria, organizations can reduce audit time by up to 20% by focusing efforts on relevant areas, according to CG Compliance Group.
Remember that unnecessary scope expansion not only increases audit costs but also requires maintaining additional controls and evidence. A carefully defined scope focuses your compliance efforts where they matter most.
Implementing these expert techniques requires investment, but the return comes in the form of more efficient audits, fewer exceptions, and a stronger overall security posture. Many organizations find that these approaches actually reduce their total compliance burden by making security and compliance part of their standard operations rather than separate activities.
Finally, consider working with experienced compliance professionals who can provide guidance based on their experience across multiple organizations. Their insights can help you avoid common pitfalls and implement compliance programs that meet both regulatory requirements and your business objectives efficiently.
Frequently Asked Questions
What are SOC reports?
SOC reports are independent audit assessments that evaluate a service organization's controls relevant to security, availability, processing integrity, confidentiality, or privacy. They provide assurance about a service organization's internal controls.
What is the difference between SOC 1, SOC 2, and SOC 3 reports?
SOC 1 focuses on financial reporting controls, SOC 2 evaluates controls relevant to security and privacy, and SOC 3 is a simplified version of SOC 2 that omits sensitive details, making it suitable for public sharing.
How long does it take to prepare for a SOC audit?
Preparation for a SOC audit typically takes 3-6 months, depending on the complexity of the organization and the scope of the audit. The fieldwork for the audit itself usually lasts 4-12 weeks.
What is the difference between SOC Type 1 and Type 2 examinations?
SOC Type 1 reports assess the design and implementation of controls at a specific point in time, while Type 2 reports evaluate both the design and operational effectiveness of those controls over a specified period (usually 6-12 months).
Streamline Your SOC Audit Preparation with Skypher
Navigating the labyrinth of SOC reports and compliance regulations can feel overwhelming, especially with the pressure of maintaining a culture of compliance throughout your organization. Whether you’re facing the complexities of a SOC 2 audit or striving to improve your security posture, the key lies in efficiency and strong documentation. Many organizations struggle with the repetitive and time-consuming process of responding to security questionnaires—but it doesn’t have to be this way!

Imagine transforming your compliance efforts with Skypher’s AI Questionnaire Automation Tool. Our platform automates and accelerates your response process, enabling you to focus on what truly matters—enhancing trust with your clients and increasing operational productivity. By leveraging real-time collaboration features, integrations with over 40 TPRM platforms, and a customizable Trust Center, you can position your business for success in less time. It's not just about passing audits; it’s about cultivating a proactive security culture that stands out in the tech and finance sectors.
Ready to take the first step? Discover how Skypher can redefine your audit journey and get ahead of the compliance curve. Visit https://skypher.co today to explore our solutions and schedule a demo!