Navigating SOC 2 compliance is no small feat. This certification is a critical asset for organizations handling sensitive customer data, setting the standard for information security and privacy. But here's the kicker: many companies believe compliance is just about meeting requirements and passing audits. The truth is far more compelling. Achieving SOC 2 compliance can elevate your entire organization, transforming security into a core competitive advantage that builds trust and fuels growth.
Table of Contents
- What Are Soc 2 Compliance Requirements?
- Understanding The Soc 2 Trust Services Criteria
- Essential Steps To Achieve Soc 2 Compliance
- Common Challenges In Soc 2 Compliance
- Key Benefits Of Soc 2 Certification
Quick Summary
| Takeaway | Explanation |
|---|---|
| Understand the Five Trust Service Criteria | The SOC 2 compliance framework is guided by Security, Availability, Processing Integrity, Confidentiality, and Privacy criteria, with Security being mandatory for audits. Organizations can prioritize criteria relevant to their specific context. |
| Conduct a Gap Analysis | Performing a thorough gap analysis is essential for identifying existing security controls and potential vulnerabilities, helping organizations create a roadmap for compliance enhancement. |
| Focus on Documentation | Key documentation such as management assertion, system description, and control matrix is vital for demonstrating the organization’s commitment to security and compliance. Continuous monitoring and assessment are also crucial. |
| Emphasize Cultural Change | Successful SOC 2 compliance involves a cultural shift within the organization, requiring security awareness and collaboration across all departments to create a cohesive approach to data protection. |
| Leverage Certification for Competitive Advantage | SOC 2 certification enhances customer trust and provides a strategic advantage in the marketplace by signaling a commitment to robust security practices, which can streamline vendor selection and accelerate sales cycles. |
What are SOC 2 Compliance Requirements?
SOC 2 compliance represents a critical framework for organizations handling sensitive customer data, establishing a comprehensive set of standards that ensure robust information security and privacy practices. At its core, SOC 2 (Service Organization Control 2) is an auditing procedure designed to verify that service providers securely manage data to protect the interests of their organization and clients.
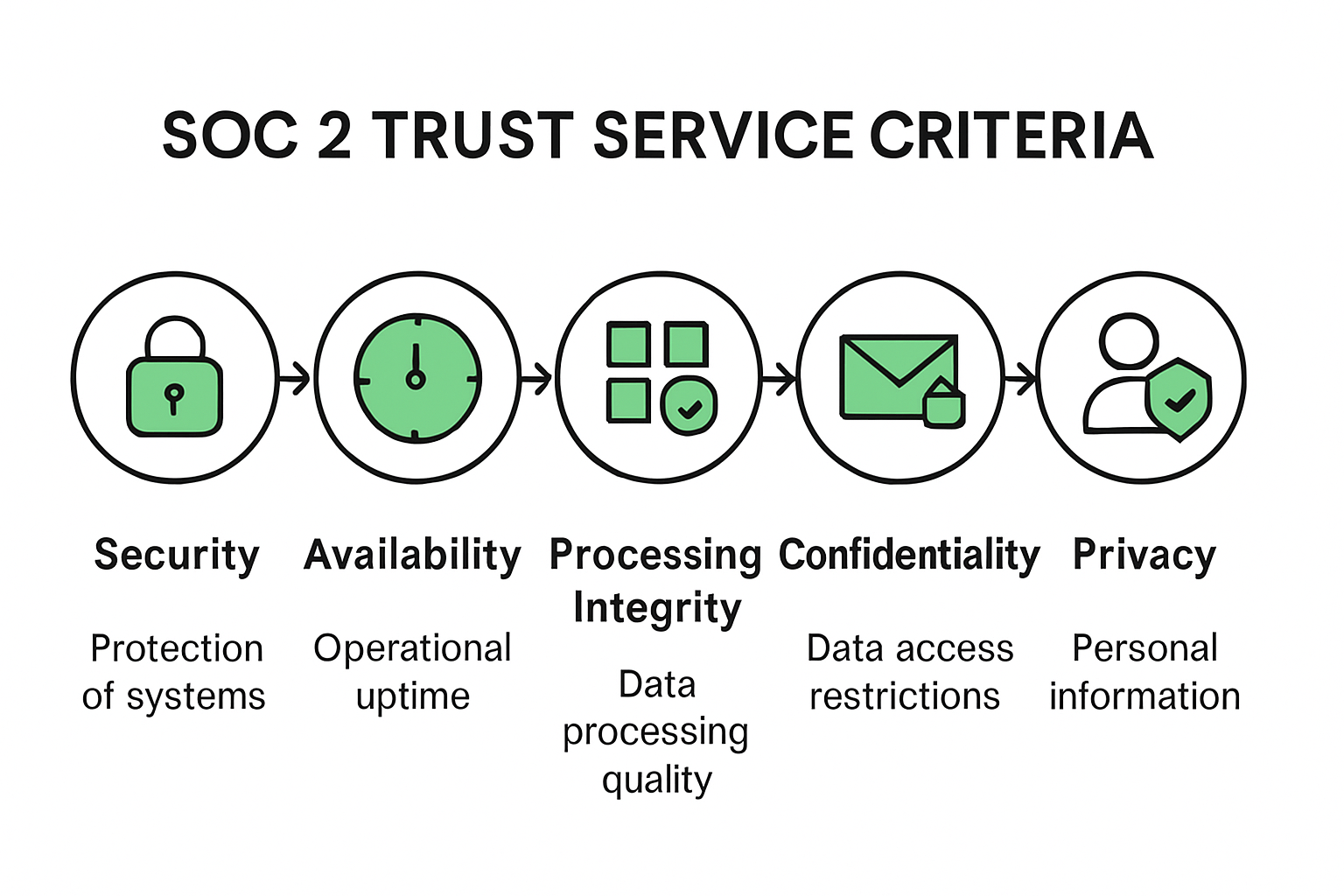
The Five Trust Service Criteria
The SOC 2 compliance requirements revolve around five fundamental Trust Service Criteria (TSC), each addressing a specific dimension of organizational data management. According to Sprinto, these criteria are:
- Security: Protecting systems and data against unauthorized access and potential threats
- Availability: Ensuring systems and services are accessible as agreed upon
- Processing Integrity: Guaranteeing system processing is complete, accurate, and timely
- Confidentiality: Maintaining the confidentiality of information designated as confidential
- Privacy: Managing personal information in accordance with established privacy principles
Organizations are not required to address all five criteria but must demonstrate comprehensive controls for those relevant to their specific operational context. This flexibility allows businesses to tailor their compliance approach to their unique technological ecosystem and industry requirements.
Documentation and Control Implementation
Achieving SOC 2 compliance is more than a checkbox exercise—it demands meticulous documentation and strategic control implementation. Secureframe emphasizes that essential documentation includes a management assertion, a detailed system description, and a comprehensive controls matrix. These documents collectively demonstrate an organization's systematic approach to managing and protecting sensitive information.
The compliance process typically involves several critical steps:
- Conducting a thorough readiness gap analysis
- Developing and implementing robust security policies
- Establishing incident response protocols
- Managing vendor and third-party risks
- Creating ongoing monitoring and assessment mechanisms
As BitSight notes, successful SOC 2 compliance requires organizations to continuously evolve their security practices, ensuring they remain aligned with emerging technological risks and regulatory frameworks.
While the path to SOC 2 compliance might seem complex, it represents a strategic investment in organizational credibility. By demonstrating a commitment to rigorous data protection and privacy standards, businesses can build trust with clients, differentiate themselves in competitive markets, and mitigate potential security vulnerabilities.
Ultimately, SOC 2 compliance is not just about meeting a set of technical requirements—it's about fostering a culture of security, transparency, and responsible data stewardship.
Understanding the SOC 2 Trust Services Criteria
The Trust Services Criteria (TSC) form the foundational framework that guides organizations in establishing comprehensive information security and privacy standards. Developed by the American Institute of Certified Public Accountants (AICPA), these criteria provide a structured approach for evaluating and implementing robust control mechanisms across various operational domains.
The Five Core Trust Services Criteria
Secureframe highlights that while organizations have flexibility in applying these criteria, the Security criteria is mandatory for every SOC 2 audit. The five Trust Services Criteria include:
- Security: The cornerstone criterion that addresses protection against unauthorized access and potential security threats.
- Availability: Ensuring systems and services remain accessible and operational as committed.
- Processing Integrity: Guaranteeing that system processing is accurate, timely, and complete.
- Confidentiality: Maintaining the confidentiality of sensitive information designated as restricted.
- Privacy: Managing personal information in accordance with established privacy principles
Detailed Breakdown of Security Criteria
The Security criterion, considered the most critical, is particularly complex and comprehensive. According to CBH Consulting, the Security criteria encompasses nine critical components:
- Control Environment (CC1): Establishing organizational structure and leadership commitment to security
- Information and Communication (CC2): Ensuring effective communication of security policies and expectations
- Risk Assessment (CC3): Identifying and analyzing potential security risks
- Monitoring Activities (CC4): Implementing continuous assessment and evaluation mechanisms
- Control Activities (CC5): Developing specific control procedures to mitigate identified risks
- Logical and Physical Access Controls (CC6): Managing system and physical access to prevent unauthorized entry
- System Operations (CC7): Maintaining consistent and secure system operations
- Change Management (CC8): Controlling and documenting system changes
- Risk Mitigation (CC9): Implementing strategies to address and minimize potential security risks
Strategically, organizations should not approach these criteria as a one-size-fits-all checklist. Expert guidance suggests focusing on the criteria most relevant to their specific operational context and those that will deliver the most significant impact.
The nuanced nature of these criteria means that compliance imparts not about achieving perfect protection, but demonstrating a systematic, risk-aware approach to information management. Organizations must show they have carefully considered potential vulnerabilities, implemented thoughtful controls, and maintained a proactive stance toward emerging security challenges.
 Ultimately, the Trust Services Criteria represent more than a technical compliance exercise. They embody a comprehensive philosophy of responsible data stewardship, emphasizing transparency, continuous improvement, and a commitment to protecting the most valuable asset in the digital age: information.
Ultimately, the Trust Services Criteria represent more than a technical compliance exercise. They embody a comprehensive philosophy of responsible data stewardship, emphasizing transparency, continuous improvement, and a commitment to protecting the most valuable asset in the digital age: information.

Essential Steps to Achieve SOC 2 Compliance
Achieving SOC 2 compliance is a strategic journey that requires meticulous planning, comprehensive documentation, and a systematic approach to information security. Organizations must navigate a complex landscape of requirements, controls, and assessments to demonstrate their commitment to protecting sensitive data and maintaining robust security practices.
Conducting a Comprehensive Gap Analysis
BitSight emphasizes that the first critical step in achieving SOC 2 compliance is performing a thorough pre-assessment gap analysis. This initial evaluation involves:
- Identifying existing security controls and their effectiveness
- Discovering potential vulnerabilities in current systems
- Comparing current practices against SOC 2 Trust Services Criteria
- Developing a detailed roadmap for addressing identified gaps
The gap analysis serves as a diagnostic tool, providing organizations with a clear understanding of their current security posture and the specific improvements needed to meet SOC 2 requirements. It's not just about finding weaknesses, but creating a strategic plan for comprehensive security enhancement.
Developing Comprehensive Documentation and Policies
Secureframe highlights the critical importance of documentation in the SOC 2 compliance process. Key documentation components include:
- Management Assertion: A formal statement outlining the organization's approach to security and control
- System Description: A detailed overview of the organization's systems, processes, and security mechanisms
- Control Matrix: A comprehensive document detailing specific controls implemented to address Trust Services Criteria
Sprinto notes that management assertion documentation is particularly crucial, as it provides auditors with a clear narrative of the organization's current security practices. This documentation should effectively communicate, "These are our controls, these are our systems, and this is what we are doing right now."
Implementing Robust Controls and Continuous Monitoring
The final stage of SOC 2 compliance involves implementing and maintaining rigorous security controls. This process requires:
- Establishing comprehensive security policies
- Creating incident response protocols
- Implementing access control mechanisms
- Developing vendor risk management procedures
- Setting up continuous monitoring and assessment systems
Successful SOC 2 compliance is not a one-time achievement but an ongoing commitment to security excellence. Organizations must view this process as a continuous journey of improvement, adapting to emerging technological risks and evolving regulatory landscapes.
Beyond meeting technical requirements, SOC 2 compliance represents a strategic investment in organizational credibility. By demonstrating a systematic approach to data protection, businesses can build trust with clients, differentiate themselves in competitive markets, and mitigate potential security vulnerabilities.
Ultimately, the path to SOC 2 compliance is about more than checking boxes—it's about fostering a culture of security, transparency, and responsible data stewardship that permeates every level of the organization.
Common Challenges in SOC 2 Compliance
Navigating SOC 2 compliance is a complex journey fraught with multifaceted challenges that can overwhelm even experienced organizations. The path to achieving and maintaining compliance demands significant strategic planning, resource allocation, and a deep understanding of evolving cybersecurity landscapes.
Resource Constraints And Cost Implications
PwC research reveals that small to medium enterprises face substantial hurdles in SOC 2 compliance, with 62% struggling to comprehend and implement requirements due to limited resources. The financial investment is considerable, typically requiring organizations to dedicate approximately 15% of their IT budget toward implementing and maintaining comprehensive security controls.
Key resource challenges include:
- Hiring specialized cybersecurity personnel
- Developing robust documentation
- Implementing advanced security technologies
- Conducting continuous risk assessments
- Maintaining ongoing compliance monitoring
Technical Complexity And Continuous Adaptation
SOC 2 compliance is not a static achievement but a dynamic, ongoing process. Organizations must continuously evolve their security practices to address emerging technological threats and regulatory changes. This requires:
- Constant monitoring of cybersecurity landscapes
- Regular updating of security controls
- Implementing advanced threat detection mechanisms
- Developing agile response strategies
- Maintaining comprehensive documentation of all changes
The complexity extends beyond initial implementation. Compliance experts emphasize that failure to regularly review and update controls can result in immediate loss of attestation and significant reputational damage.
Organizational Culture And Training Challenges
Successful SOC 2 compliance transcends technical implementation—it requires a fundamental cultural shift within the organization. Challenges in this domain include:
- Creating security awareness across all organizational levels
- Training employees on complex security protocols
- Developing a consistent approach to data protection
- Aligning individual behaviors with organizational security goals
- Overcoming resistance to changing established workflows
Many organizations underestimate the human element in compliance, focusing exclusively on technological solutions while neglecting critical cultural transformation.
Moreover, the interdisciplinary nature of SOC 2 compliance demands collaboration across multiple departments—IT, legal, human resources, and executive leadership must work in concert to develop and maintain robust security frameworks.
Ultimately, SOC 2 compliance represents more than a technical certification. It's a comprehensive commitment to protecting organizational and client data, requiring persistent effort, strategic investment, and an unwavering dedication to security excellence.
By recognizing and proactively addressing these challenges, organizations can transform compliance from a burdensome requirement into a strategic advantage that builds trust, enhances reputation, and demonstrates genuine commitment to data protection.
Key Benefits of SOC 2 Certification
SOC 2 certification represents far more than a mere compliance checkbox—it's a strategic asset that can transform an organization's approach to security, customer trust, and operational excellence. By pursuing this rigorous certification, businesses unlock a multitude of advantages that extend well beyond traditional security frameworks.
Enhanced Customer Trust And Competitive Advantage
Deloitte's Customer Satisfaction Survey reveals that 85% of clients consider SOC 2 compliance a critical factor when selecting service providers. This certification serves as a powerful differentiator in competitive markets, signaling to potential clients a genuine commitment to robust security practices.
Key trust-building benefits include:
- Demonstrating proactive security management
- Streamlining vendor selection processes
- Accelerating sales cycles by reducing security due diligence timelines
- Providing transparent evidence of comprehensive security controls
- Establishing credibility in industries with stringent security requirements
Operational Security And Risk Mitigation
Cybersecurity experts emphasize that SOC 2 compliance compels organizations to implement and document sophisticated security controls. This process results in significant risk reduction and operational improvements:
- Implementing strict access management protocols
- Establishing robust encryption standards
- Creating comprehensive continuous monitoring systems
- Developing structured incident response mechanisms
- Identifying and addressing potential security vulnerabilities proactively
Organizations report remarkable operational efficiency gains, including 30-50% faster incident response times and more effective detection of systemic inefficiencies in critical areas like access provisioning, change management, and disaster recovery planning.
Internal Process Optimization And Organizational Maturity
Beyond external perceptions, SOC 2 certification drives profound internal transformations. The certification process encourages organizations to:
- Develop clear, documented security policies
- Create standardized operational procedures
- Foster a culture of continuous security improvement
- Enhance cross-departmental communication and collaboration
- Implement systematic risk assessment and management frameworks
This holistic approach transforms security from a technical requirement into a strategic organizational capability. By systematically addressing potential weaknesses and establishing robust control mechanisms, businesses develop greater organizational resilience and adaptability.
The true value of SOC 2 certification extends far beyond a simple audit—it represents a comprehensive commitment to excellence, transparency, and responsible technology stewardship. Organizations that genuinely embrace these principles don't just achieve compliance; they establish themselves as industry leaders who prioritize data protection and customer trust.
Ultimately, SOC 2 certification is an investment in an organization's most critical assets: its reputation, its customers' confidence, and its long-term strategic positioning in an increasingly complex digital landscape.
Frequently Asked Questions
What are the SOC 2 compliance requirements?
SOC 2 compliance requirements consist of a set of standards that organizations must follow to ensure the security, availability, processing integrity, confidentiality, and privacy of customer data. The framework is built around five Trust Service Criteria._
Why is SOC 2 compliance important for businesses?
SOC 2 compliance is crucial as it establishes a framework for managing customer data securely and can significantly enhance customer trust. It provides businesses a competitive advantage by demonstrating their commitment to data protection and privacy, which can streamline vendor selection and accelerate sales cycles.
How can organizations achieve SOC 2 compliance?
Organizations can achieve SOC 2 compliance by conducting a comprehensive gap analysis, developing robust documentation policies, and implementing rigorous security controls. Continuous monitoring and adaptability to evolving risks are also essential elements of maintaining compliance._
What are the common challenges in achieving SOC 2 compliance?
Common challenges include resource constraints, technical complexities, and the need for a cultural shift within the organization. These factors can hinder the implementation of security measures and ongoing adherence to SOC 2 standards.
Transform Your SOC 2 Compliance Journey with Skypher
Navigating the complexities of SOC 2 compliance can often feel overwhelming, especially when your organization is struggling with resource constraints and the technical intricacies highlighted in our latest article on SOC 2 compliance requirements for 2025. The extensive documentation and continuous monitoring required can drain your team’s time and energy, preventing you from focusing on strategic goals.
But what if there were a way to simplify this process, boost your operational productivity, and ensure you meet compliance mandates with ease? With Skypher's AI-driven Questionnaire Automation Tool, you can tackle security questionnaires at lightning speed while enhancing accuracy. Our platform supports seamless integration with over 40 third-party risk management systems, enabling real-time collaboration and streamlined communication across your teams. Say goodbye to the hassles of manual documentation and welcome a new era of efficiency—a crucial advantage in achieving your SOC 2 objectives.

Ready to transform your compliance experience? Don’t let the challenges of SOC 2 hold you back any longer. Visit https://skypher.co NOW to learn how our powerful solutions can revolutionize your security processes and elevate customer trust! Act fast to grasp the advantages that SOC 2 compliance can bring to your organization’s credibility and competitive edge.