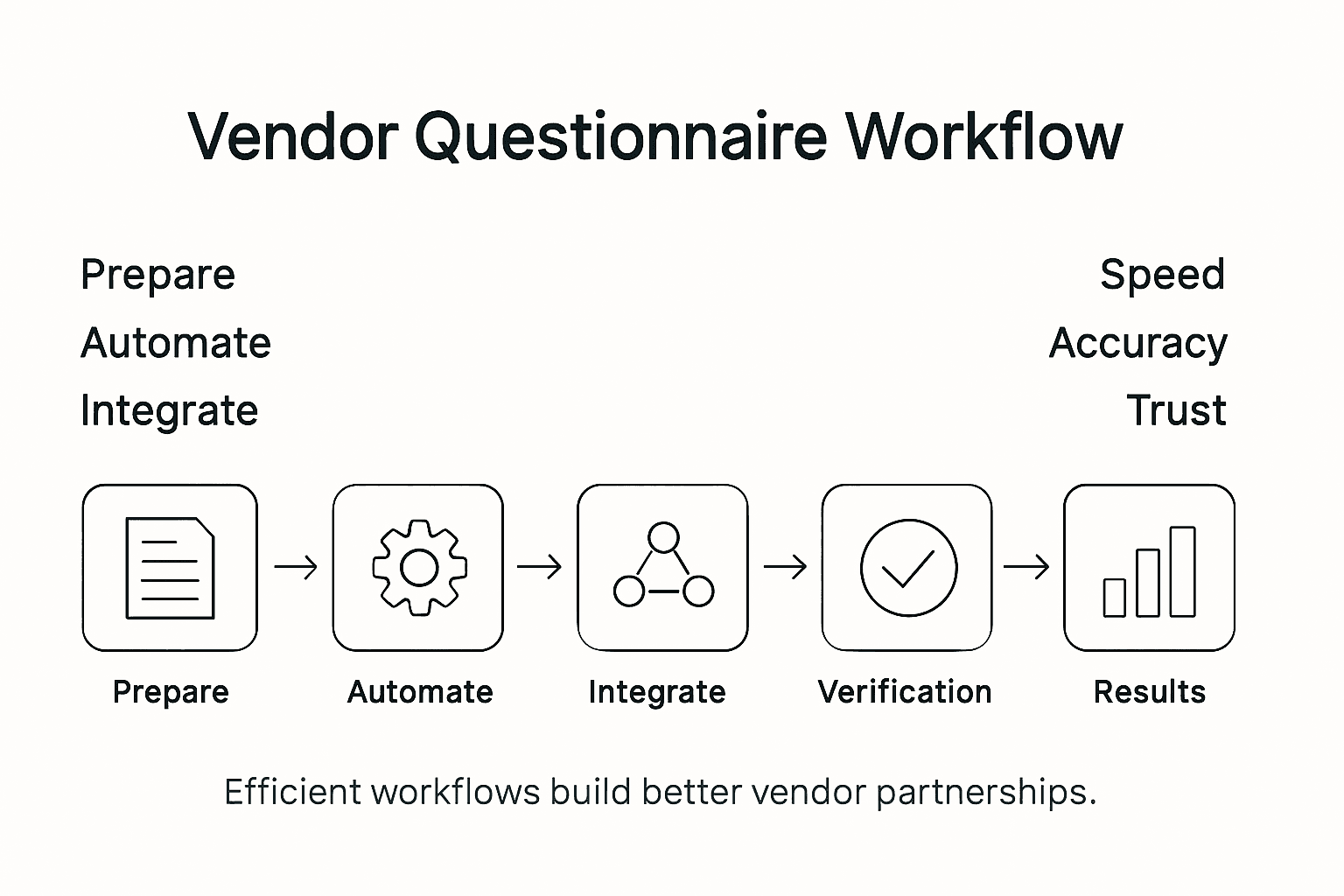
A recent study reveals that over 60 percent of American organizations struggle to answer client security questionnaires quickly and accurately. This challenge exposes many international and European firms to delays, compliance risks, and lost business opportunities. Security compliance officers need a smarter way to manage these growing demands. In the following guidance, discover practical strategies that bring clarity, speed, and confidence to every vendor security assessment while building greater trust among global clients.
Table of Contents
- Step 1: Prepare Key Security Requirements And Templates
- Step 2: Upload And Parse Questionnaires Using Automation Tools
- Step 3: Integrate With Platforms For Data Collection And Collaboration
- Step 4: Verify Responses With Ai-Powered Quality Checks
- Step 5: Share Results And Establish Vendor Trust Efficiently
Quick Summary
| Key Point | Explanation |
|---|---|
| 1. Develop Comprehensive Templates | Create structured vendor security questionnaires that cover essential security domains for effective risk assessment. |
| 2. Automate Data Processing | Utilize automation tools to streamline questionnaire uploads and data extraction, ensuring higher accuracy and efficiency. |
| 3. Integrate for Effective Communication | Use platforms that support secure data sharing and collaboration, enabling smoother vendor engagement and risk management. |
| 4. Employ AI for Accurate Verification | Implement AI technologies to perform intelligent checks on vendor responses, enhancing response reliability and reducing manual workload. |
| 5. Clearly Share Assessment Results | Communicate findings effectively, focusing on transparency and constructive feedback to foster improvement and vendor trust. |
Step 1: Prepare key security requirements and templates
Preparing robust vendor security questionnaire templates requires strategic planning and comprehensive understanding of your organization's risk landscape. The goal is to design a flexible yet thorough assessment framework that enables rapid yet precise evaluation of potential vendor security risks.
Start by referencing established security assessment frameworks like the International Association of Privacy Professionals vendor privacy checklist to build a structured approach. Your template should include essential categories such as data protection practices, regulatory compliance, access controls, incident response capabilities, and third party risk management protocols. Develop targeted questions that dig deeper than surface level responses requiring vendors to provide specific evidence and documentation supporting their security claims.
Each section of your questionnaire should map directly to specific security domains such as infrastructure protection, application security, data privacy, and business continuity. Break down complex requirements into clear measurable components that allow for objective scoring and comparative analysis across different vendor profiles. Incorporate scoring mechanisms that help quantify and rank vendor security maturity levels effectively.
Pro tip: Create a dynamic template with weighted scoring that automatically highlights high risk areas and provides actionable insights during vendor security assessments.
Step 2: Upload and parse questionnaires using automation tools
Transforming your vendor security assessment workflow requires strategic implementation of automation technologies that can intelligently handle document uploads and data extraction. The objective is to streamline the entire questionnaire processing cycle with minimal manual intervention and maximum accuracy.
Leverage advanced automation platforms that support comprehensive questionnaire data parsing across multiple document formats. These tools can intelligently recognize complex form structures, extract relevant security information, and automatically map responses to standardized evaluation frameworks. Look for solutions that offer intelligent form recognition capabilities machine learning algorithms and natural language processing technologies that can parse unstructured questionnaire data with high precision.

Integrate your automation tools with existing risk management systems to create a seamless workflow. Advanced platforms should support multiple input methods including direct file uploads drag and drop interfaces and API integrations. Ensure your chosen solution can handle various questionnaire formats PDF Word Excel and can automatically validate data entries detect potential inconsistencies and generate preliminary risk scoring based on vendor responses.
Pro tip: Configure your automation tool with predefined validation rules and scoring algorithms to automatically flag high risk responses and streamline initial vendor security assessment processes.
Step 3: Integrate with platforms for data collection and collaboration
Successfully managing vendor security assessments requires sophisticated integration strategies that enable seamless data sharing and collaborative workflows across multiple organizational platforms. Your primary objective is to create a robust ecosystem that supports secure information exchange and real-time collaboration.
Explore cross sector data sharing platforms that facilitate advanced interoperability and secure information management. These platforms enable organizations to implement federated data collection approaches that support dynamic vendor questionnaire processing while maintaining strict security protocols. Modern integration strategies should focus on establishing technical standards that allow smooth data synchronization between different risk management systems document repositories and collaborative environments.
Implement comprehensive integration frameworks that support multiple communication channels API connections and standardized data exchange protocols. Your platform should enable secure document sharing granular access controls and real-time collaboration features that allow multiple stakeholders to review validate and annotate vendor security questionnaires simultaneously. Look for solutions that provide end to end encryption multi factor authentication and detailed audit trails to ensure complete transparency and compliance throughout the assessment process.
Pro tip: Select integration platforms with robust API capabilities and flexible data mapping features to minimize manual data transfer and reduce potential security vulnerabilities during vendor assessment workflows.
Step 4: Verify responses with AI-powered quality checks
Verifying vendor security questionnaire responses requires sophisticated AI-powered techniques that go beyond traditional manual review methods. The primary goal is to implement intelligent validation mechanisms that can rapidly assess response accuracy reliability and potential risk indicators.
Utilize advanced AI test and evaluation frameworks that enable comprehensive response analysis through natural language processing and machine learning algorithms. These intelligent systems can automatically detect inconsistencies compare responses against established security benchmarks and flag potential areas of concern that might require deeper human investigation. By implementing AI driven quality checks you can dramatically reduce the time spent on manual review while simultaneously improving the overall accuracy of your vendor risk assessment process.
Deploy multilayered verification strategies that combine AI pattern recognition with contextual understanding and cross referencing capabilities. Modern AI tools can analyze response syntax semantic meaning and contextual relevance providing nuanced insights that traditional checklist approaches might miss. Focus on solutions that offer granular scoring mechanisms real time risk profiling and the ability to learn from historical assessment data to continuously improve verification accuracy.
Pro tip: Configure your AI verification tool to generate detailed confidence scores for each response enabling quick identification of high risk or potentially incomplete vendor submissions.
The table below contrasts Manual vs. Automated Vendor Security Assessments:
| Feature | Manual Review | Automated & AI-driven |
|---|---|---|
| Processing Time | Slow, labor-intensive | Fast, high throughput |
| Error Risk | Higher, human mistakes | Lower, consistent output |
| Scalability | Limited by staff | Easily scalable |
| Reporting | Basic summaries | Dynamic, actionable insights |
| Risk Detection | Prone to oversight | Enhanced by AI analytics |
Step 5: Share results and establish vendor trust efficiently
Successfully communicating vendor security assessment outcomes requires a strategic approach that prioritizes transparency clarity and constructive dialogue. Your goal is to transform potentially sensitive findings into collaborative opportunities for mutual improvement and risk mitigation.
Leverage standardized vendor security communication protocols that provide structured frameworks for presenting assessment results. These approaches should include comprehensive executive summaries detailed risk breakdowns and actionable recommendations that help vendors understand their current security posture. By offering clear comparative metrics and specific guidance you demonstrate a commitment to partnership rather than simply pointing out vulnerabilities.
Create a nuanced communication strategy that balances transparency with professional support. Present findings in a manner that highlights both strengths and potential improvement areas while offering constructive pathways for remediation. Use visual representations like risk heat maps segmented scoring charts and trend analysis graphics to make complex security assessments more digestible. Establish regular follow up mechanisms that allow vendors to ask questions provide clarifications and demonstrate progressive improvements in their security practices.
Pro tip: Design vendor result communication templates that include specific action items scoring context and clear next steps to transform assessment findings into a collaborative risk reduction journey.
Here is a summary of critical vendor security assessment steps and their main benefits:
| Step | Main Objective | Key Benefit |
|---|---|---|
| Prepare Requirements | Structure assessments | Ensures comprehensive coverage |
| Automate Parsing | Speed processing | Reduces manual errors |
| Platform Integration | Enable collaboration | Improves data consistency |
| AI-Powered Checks | Verify accuracy | Increases review precision |
| Share Results | Build trust | Supports vendor improvements |
Accelerate Your Vendor Security Assessments with Skypher
Navigating the complexities of vendor security questionnaires can be time consuming and prone to error. The article highlights key challenges such as preparing detailed security requirements, parsing diverse questionnaire formats, integrating multiple platforms for collaboration, and verifying responses with AI powered checks. Many organizations face slow manual processes, scattered data, and difficulty building vendor trust efficiently.
Skypher’s AI Questionnaire Automation Tool directly addresses these pain points by enabling you to upload any document format and parse hundreds of questions in under one minute with unparalleled accuracy. Its deep integration capabilities with over 30 third party risk management platforms including OneTrust and ServiceNow ensure seamless data flow while collaborative features support real time team efforts for verification and communication. Plus, Skypher’s Custom Trust Center transforms how you present security results to vendors fostering transparency and stronger partnerships.
Are you ready to streamline vendor security assessments and accelerate risk management workflows today

Discover how Skypher can automate your entire questionnaire process and reduce manual workload immediately at Skypher’s official site. Explore our AI driven platform and integrations for a smarter security review experience at Skypher. Start transforming your vendor security process now and build trust faster with Skypher.
Frequently Asked Questions
How can I prepare effective vendor security questionnaires?
To prepare effective vendor security questionnaires, start by referencing established frameworks and including key categories like data protection practices and regulatory compliance. Focus on developing targeted questions that require specific evidence to ensure comprehensive coverage and clarity in vendor responses.
What automation tools can help with parsing vendor questionnaires?
Automation tools designed for data parsing can greatly enhance your efficiency by extracting relevant information from various document formats. Look for tools that offer intelligent form recognition and can handle PDF, Word, and Excel files to streamline your vendor security assessment workflow.
How can I ensure accurate verification of vendor responses?
To ensure accurate verification of vendor responses, implement AI-powered quality checks that analyze response consistency and reliability. Utilize advanced algorithms to detect potential red flags, increasing the accuracy of your security assessment while reducing manual review time.
What integration strategies are effective for vendor security assessments?
Effective integration strategies involve establishing seamless data sharing and collaboration between risk management systems and document repositories. Prioritize solutions that support multiple communication channels and offer granular access controls to enhance security and streamline workflows.
How do I communicate assessment results to vendors?
Communicate assessment results clearly by providing structured frameworks that include comprehensive summaries and risk breakdowns. Use visual aids like risk heat maps to present complex information in a digestible format, and create follow-up mechanisms for collaborative dialogue and improvement.