Over 60 percent of American businesses now rely on third-party vendors to expand their SaaS capabilities. As digital demands rise, the role of external providers becomes more vital and complex. Choosing the right partners means navigating risks, compliance, and integration hurdles. This guide unpacks who these vendors are, why they matter, and how organizations can maximize benefits while protecting security and performance.
Table of Contents
- Defining Third-Party Vendors In SaaS
- Common Types Of Third-Party Vendors
- How Vendor Relationships Function In Organizations
- Key Risks And Integration Challenges
- Compliance, Due Diligence, And Mitigation
Key Takeaways
| Point | Details |
|---|---|
| Third-Party Vendors Are Essential | They provide specialized software and services that enhance the functionality of SaaS platforms without being embedded within an organization. |
| Comprehensive Vendor Selection Is Critical | Conduct thorough assessments of technological capabilities, security standards, and alignment with business objectives before onboarding vendors. |
| Effective Vendor Management Enhances Value | Establish clear management policies to ensure continuous performance evaluation, compliance, and alignment with strategic goals. |
| Implement Risk Mitigation Strategies | Use multi-tiered frameworks for screening, monitoring, and assessing vendors to identify and address potential vulnerabilities proactively. |
Defining Third-Party Vendors in SaaS
In the complex ecosystem of Software as a Service (SaaS), third-party vendors represent crucial external entities that provide software services or products independent of the primary service provider and end-user. Third-party sources are fundamentally independent suppliers operating within the broader technology transaction landscape, delivering specialized solutions that augment or complement core business technologies.
These vendors typically offer specialized software, integrations, support services, or complementary technological capabilities that extend the functionality of primary SaaS platforms. Unlike internal teams or direct service providers, third-party vendors maintain organizational independence, bringing unique expertise, technological solutions, and potential innovation to the SaaS environment. Their role involves providing targeted services that fill specific technological gaps or enhance existing software infrastructure without being directly embedded within an organization's primary operational structure.
Understanding third-party vendors requires recognizing their multifaceted nature. They can range from small specialized software providers to large technology consulting firms offering complex integration services. Key characteristics include operational independence, contractual relationships defined by service level agreements, and the ability to provide targeted technological solutions that address specific business requirements. Successful integration of third-party vendors demands rigorous evaluation of their technological capabilities, security protocols, compliance standards, and alignment with organizational objectives.
Pro Tip: Vendor Selection Strategy: Before onboarding any third-party vendor, conduct a comprehensive risk assessment that evaluates their technological capabilities, security practices, financial stability, and potential impact on your existing SaaS ecosystem.
Common Types of Third-Party Vendors
In the intricate landscape of SaaS environments, several distinct categories of third-party vendors play critical roles in expanding and enhancing technological capabilities. Independent software vendors (ISVs) represent a primary category, specializing in developing and selling targeted software applications designed to integrate seamlessly with existing platforms, providing specialized functionalities that address unique business requirements.
Another significant category encompasses Data as a Service (DaaS) providers, who offer cloud-based tools for sophisticated data management and analysis. These vendors supply advanced data-related services that enable organizations to leverage complex data insights without substantial infrastructure investments. DaaS vendors typically provide comprehensive solutions including data integration, real-time analytics, predictive modeling, and scalable data processing capabilities that can be directly embedded into existing SaaS ecosystems.
Beyond ISVs and DaaS providers, other notable third-party vendor types include cloud infrastructure providers, cybersecurity specialists, compliance and regulatory technology firms, integration platform vendors, and specialized consulting services. Each category brings unique technological expertise, helping organizations enhance their digital capabilities, streamline operations, mitigate risks, and drive strategic technological innovation. These vendors operate across diverse domains, offering targeted solutions that address specific technological challenges and support organizational growth strategies.
The following table summarizes major third-party vendor types in SaaS and their contributions:
| Vendor Type | Main Contribution | Typical Business Impact |
|---|---|---|
| Independent Software Vendor | Custom application add-ons and plugins | Enhanced platform functionality |
| Data as a Service Provider | Managed data analytics and integration | Improved data-driven decision making |
| Cloud Infrastructure Vendor | Scalable hosting and computing power | Increased system reliability |
| Cybersecurity Specialist | Security monitoring and threat defense | Reduced risk of breaches |
| Compliance Technology Firm | Automated compliance and reporting | Stronger regulatory adherence |
| Consulting Service Provider | Strategic IT guidance and integration | Enhanced implementation effectiveness |
Pro Tip: Vendor Classification Strategy: Develop a comprehensive vendor taxonomy that categorizes third-party providers based on their technological capabilities, integration potential, and strategic alignment with your organization's core objectives.
How Vendor Relationships Function in Organizations
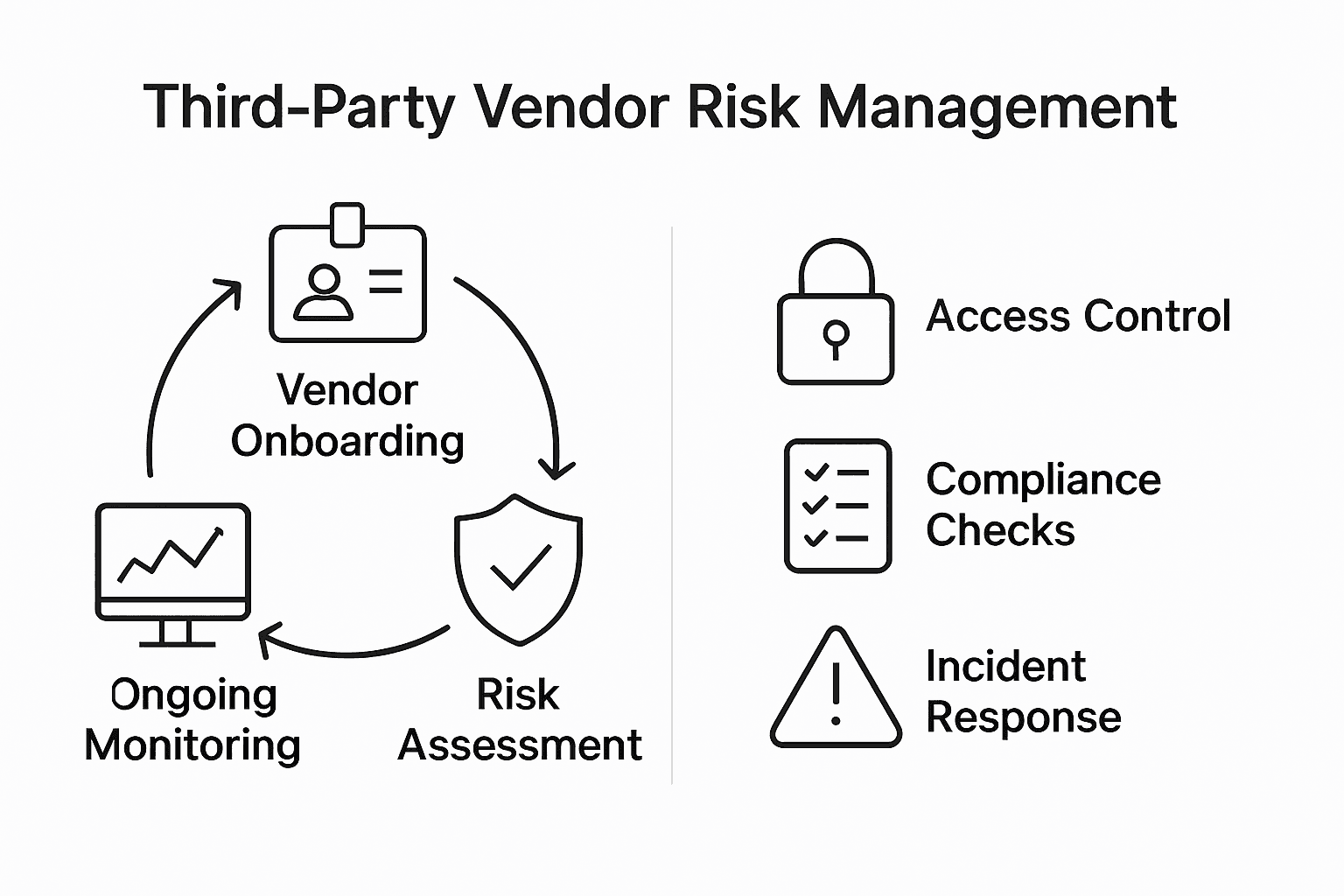
Third-party management represents a complex organizational process that involves strategically overseeing and managing relationships with external entities providing critical goods, services, and technological support. These relationships extend far beyond simple transactional interactions, requiring comprehensive assessment, continuous monitoring, and proactive risk mitigation strategies that ensure vendors deliver consistent value while maintaining organizational security and compliance standards.
The fundamental framework of vendor relationships is built upon rigorous vendor management policies that establish clear expectations, performance metrics, and governance protocols. Institutional vendor management policies typically outline specific standards for engagement, emphasizing the protection of organizational data, systems, reputation, and financial stability. These policies create structured approaches for vendor selection, onboarding, performance evaluation, and potential contract termination, ensuring that each external relationship aligns with the organization's strategic objectives and risk management frameworks.

Successful vendor relationships are characterized by transparent communication, well-defined service level agreements (SLAs), regular performance reviews, and robust risk assessment mechanisms. Organizations must develop comprehensive due diligence processes that evaluate potential vendors across multiple dimensions, including technological capabilities, financial stability, cybersecurity practices, regulatory compliance, and cultural alignment. This holistic approach enables organizations to build resilient, adaptive vendor ecosystems that can respond effectively to changing technological landscapes and emerging business challenges.
Pro Tip: Vendor Relationship Optimization: Implement a dynamic vendor scorecard system that tracks performance metrics, risk indicators, and strategic alignment, enabling continuous improvement and data-driven decision-making in vendor management.
Key Risks and Integration Challenges
Third-party vendor risks encompass a complex landscape of potential vulnerabilities that organizations must strategically navigate in modern SaaS environments. These risks span multiple critical dimensions, including information security, regulatory compliance, operational stability, financial integrity, and organizational reputation. Each interaction with an external vendor introduces potential breach points that can compromise an organization's core technological infrastructure and strategic objectives.
The multifaceted nature of vendor risks requires comprehensive assessment strategies that go beyond traditional evaluation frameworks. Cybersecurity integration challenges represent a significant concern, with vendors potentially introducing complex technical vulnerabilities that can undermine existing security architectures. Blockchain-enhanced risk management frameworks are emerging as innovative solutions to enhance transparency and traceability in vendor interactions, providing more robust mechanisms for identifying and mitigating potential security threats through immutable transaction records and advanced verification protocols.
Organizations must develop sophisticated risk assessment methodologies that evaluate vendors across multiple critical dimensions. Key evaluation criteria should include technological capabilities, data protection practices, regulatory compliance standards, financial stability, incident response preparedness, and cultural compatibility. This holistic approach enables businesses to construct resilient vendor ecosystems that can adapt to evolving technological landscapes while maintaining stringent security and performance standards. Advanced risk management techniques now incorporate predictive analytics, continuous monitoring systems, and dynamic risk scoring models to provide real-time insights into vendor performance and potential vulnerabilities.
Here is a comparison of common vendor risk management strategies and their unique strengths:
| Strategy | Key Focus | Business Value |
|---|---|---|
| Initial Screening | Background and reputation | Avoid unreliable vendors |
| Continuous Monitoring | Ongoing performance | Early detection of issues |
| Predictive Analytics | Risk forecasting | Proactive incident prevention |
| Due Diligence Questionnaires | Security and compliance | Identifies hidden vulnerabilities |
| Blockchain Traceability | Transparent tracking | Verifiable vendor interactions |
Pro Tip: Risk Assessment Protocol: Implement a multi-tiered vendor risk assessment framework that includes initial screening, comprehensive due diligence, ongoing monitoring, and periodic reevaluation to ensure continuous alignment with organizational security standards.
Compliance, Due Diligence, and Mitigation
Comprehensive vendor compliance demands a strategic approach that integrates rigorous due diligence questionnaire methodologies with advanced risk assessment frameworks. Organizations must develop systematic processes that thoroughly evaluate potential third-party vendors across multiple critical dimensions, including technological capabilities, security protocols, regulatory adherence, financial stability, and operational reliability. This holistic evaluation approach enables businesses to identify potential vulnerabilities and establish robust safeguards before initiating vendor relationships.
Compliance frameworks represent the foundational infrastructure for managing third-party vendor risks in modern technological ecosystems. SOC 2 compliance standards provide critical guidelines for assessing vendor security practices, data protection mechanisms, and operational controls. These comprehensive standards require vendors to demonstrate rigorous information management protocols, ensuring that data privacy, confidentiality, and integrity remain paramount throughout vendor interactions. Successful compliance management involves continuous monitoring, periodic reassessments, and dynamic risk scoring mechanisms that adapt to evolving technological landscapes.
Effective vendor risk mitigation strategies incorporate multi-layered approaches that combine proactive screening, comprehensive contractual protections, ongoing performance evaluations, and advanced technological monitoring systems. Organizations should implement detailed vendor assessment protocols that include initial background checks, in-depth security audits, financial stability reviews, and continuous performance tracking. These strategies enable businesses to establish resilient vendor ecosystems that can quickly identify and address potential risks, maintain operational continuity, and protect critical organizational assets from potential technological vulnerabilities.
Pro Tip: Compliance Documentation Strategy: Develop a standardized vendor risk assessment template that systematically captures critical compliance metrics, enabling consistent and comprehensive evaluation across all potential third-party technology partners.
Strengthen Your Third-Party Vendor Risk Management with Skypher
Managing third-party vendor risks is a crucial challenge for organizations in today’s SaaS environments. As the article highlights, vulnerabilities from external vendors can put your data security, compliance, and operational stability at risk. Skypher helps you overcome these challenges by automating and streamlining your security questionnaire process, enabling faster, more accurate responses to critical vendor assessments and due diligence requirements.

Experience AI-powered efficiency with Skypher’s Questionnaire Automation Tool that integrates seamlessly with over 40 third-party risk management platforms. With real-time collaboration features and customizable Trust Centers, Skypher empowers your teams to handle complex vendor evaluations while maintaining stringent security standards. Don’t let third-party risks slow down your business operations. Visit Skypher to learn how you can enhance your vendor compliance strategy and accelerate your security reviews today. Explore more about our API Integrations with TPRM Platforms and discover why tech and finance leaders trust Skypher for managing third-party risk with confidence.
Frequently Asked Questions
What are third-party vendor risks in SaaS environments?
Third-party vendor risks refer to the potential vulnerabilities and challenges organizations face when relying on external vendors for software services, such as cybersecurity threats, compliance issues, and operational stability concerns that may impact the organization's technological infrastructure and strategic objectives.
How can organizations assess third-party vendors’ security protocols?
Organizations can assess third-party vendors' security protocols by conducting thorough due diligence, which may include evaluating their cybersecurity practices, compliance with standards like SOC 2, and examining their incident response preparedness and financial stability.
What are some common types of third-party vendors in SaaS?
Common types of third-party vendors in SaaS include Independent Software Vendors (ISVs), Data as a Service (DaaS) providers, cloud infrastructure providers, cybersecurity specialists, compliance technology firms, and consulting service providers, each offering unique technological capabilities and support.
How can organizations mitigate risks associated with vendor relationships?
Organizations can mitigate risks associated with vendor relationships by implementing comprehensive vendor management policies, conducting continuous monitoring, utilizing predictive analytics for risk forecasting, and establishing multi-layered compliance frameworks to ensure ongoing adherence to security and operational standards.
