Managing third party vendors is not just a side task for companies anymore. Third party breaches now account for 30 percent of all data security incidents, a 15 percent jump from previous years. That might sound like a technical issue, something for IT to sort out. Yet the real twist is this. The weakest link in your cybersecurity might not even be inside your company at all, but sitting in a vendor’s office halfway across the country.
Table of Contents
- Why Third Party Vendors Management Matters
- Key Steps In Effective Vendor Management
- Managing Risks And Ensuring Compliance
- Best Practices For Strong Vendor Relationships
Quick Summary
| Takeaway | Explanation |
|---|---|
| Proactive Vendor Management | Companies must view vendor management as a proactive business enabler, focusing on continuous monitoring, adaptive risk assessment, and integrating advanced technologies to mitigate risks effectively. |
| Establish a Risk Assessment Framework | Implement a comprehensive vendor risk assessment framework, categorizing vendors by risk levels and ensuring thorough due diligence and continuous monitoring tailored to their specific risk. |
| Foster Strong Relationships | Building and maintaining collaborative vendor relationships is crucial; establish clear communication, shared objectives, and mutual accountability to enhance operational resilience and strategic advantage. |
Why Third Party Vendors Management Matters
In the rapidly evolving digital ecosystem, third party vendors management has transformed from a peripheral business function to a critical strategic imperative. Organizations today face unprecedented challenges in maintaining secure and efficient external vendor relationships that directly impact operational resilience, financial performance, and cybersecurity posture.
The Rising Stakes of Vendor Risk
The landscape of third party vendor interactions has become exponentially more complex. Recent data reveals a stark reality: third-party breaches now account for 30% of all data security incidents, representing a significant 15% increase from previous years. This trend underscores the urgent need for comprehensive vendor management strategies that go beyond traditional compliance checkboxes.
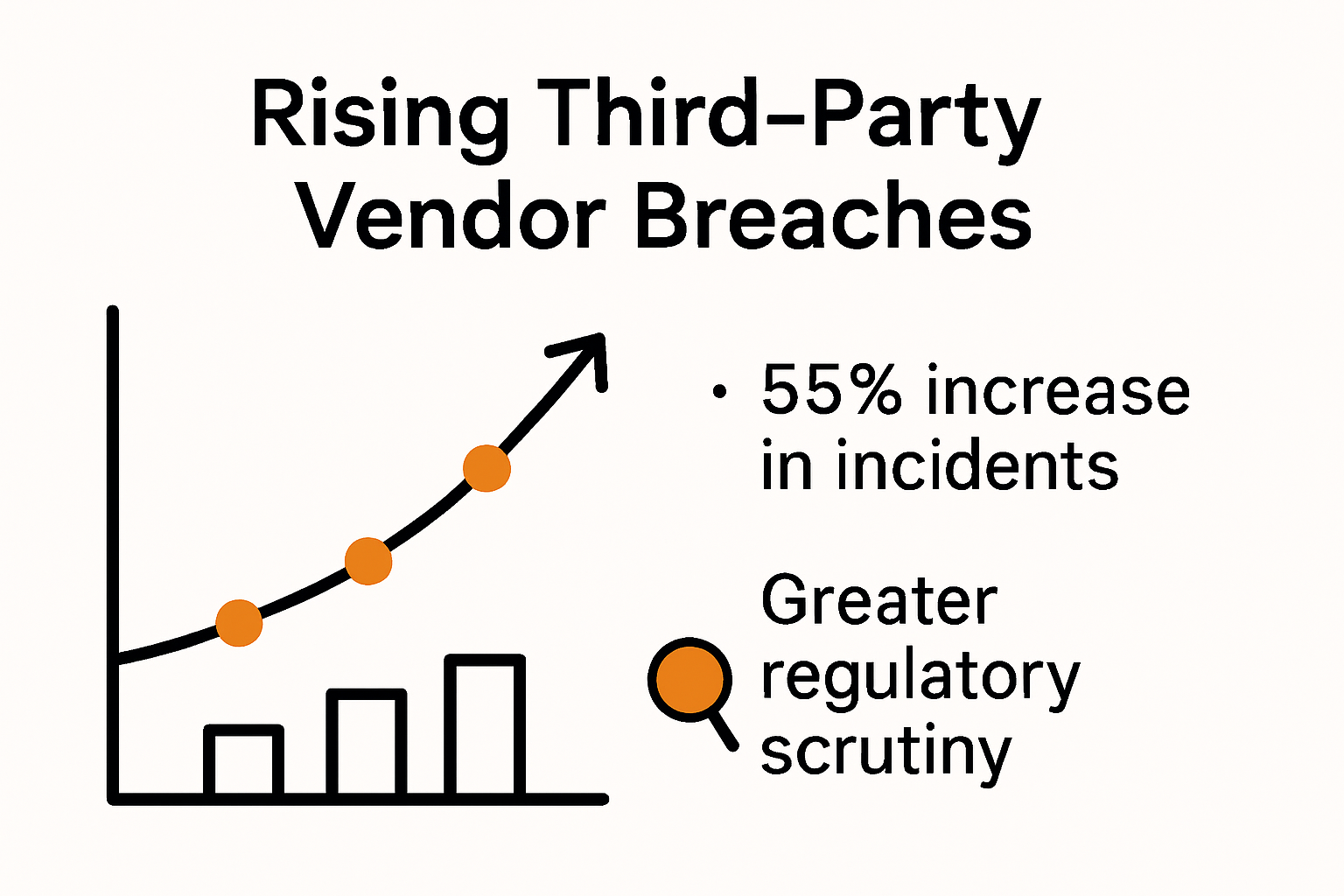
U.S. regulatory bodies have intensified their focus on vendor oversight. Examiners are now closely scrutinizing how organizations assess, monitor, and manage third-party relationships, recognizing the profound potential for systemic risk. The regulatory landscape demands more than superficial risk assessments. Companies must develop robust, dynamic frameworks that provide real-time visibility into vendor performance, security protocols, and potential vulnerabilities.
Financial and Operational Implications
Beyond cybersecurity, third party vendors management directly impacts an organization's bottom line and operational continuity. The high-profile Change Healthcare cyberattack in 2023 demonstrated how a single vendor vulnerability could disrupt entire healthcare ecosystems, causing millions in lost revenue and compromising patient data.
Effective vendor management is no longer a defensive strategy but a proactive business enabler. Organizations that implement sophisticated vendor risk management approaches can:
- Reduce Financial Exposure: Minimize potential losses from vendor-related incidents
- Enhance Operational Efficiency: Streamline vendor interactions and performance monitoring
- Protect Organizational Reputation: Mitigate risks before they escalate into public incidents
The most successful companies view third party vendors management as a strategic function. It requires continuous monitoring, adaptive risk assessment, and a holistic approach that integrates technological solutions, comprehensive due diligence, and agile governance frameworks.
As digital interdependence continues to grow, organizations must recognize that their vendor ecosystem is not peripheral but central to their operational DNA. Those who invest in sophisticated, intelligent vendor management strategies will not just survive but thrive in an increasingly complex business environment.
Key Steps in Effective Vendor Management
Effective third party vendors management requires a strategic, comprehensive approach that goes beyond traditional checklist-based evaluations. Organizations must develop a robust framework that encompasses thorough vendor selection, continuous monitoring, and adaptive risk management strategies.
Establishing a Comprehensive Vendor Risk Assessment Framework
The foundation of successful vendor management lies in creating a systematic approach to vendor evaluation and categorization. Implementing a tiered vendor management approach allows organizations to allocate resources and controls proportionate to each vendor's risk level. This methodology involves:
- Initial Risk Categorization: Classify vendors into high, medium, and low-risk tiers based on their access to sensitive data, critical systems, and potential business impact
- Comprehensive Due Diligence: Conduct in-depth assessments that go beyond surface-level security checks
- Continuous Monitoring: Develop a dynamic evaluation process that adapts to changing vendor landscapes
Technology-Driven Vendor Oversight
Modern vendor management demands sophisticated technological solutions. Leveraging advanced technologies enables organizations to implement continuous monitoring, automated alerts, and data analytics that provide real-time insights. This approach transforms vendor management from a reactive to a proactive discipline.
Key technological strategies include:
- Implementing automated risk assessment tools
- Creating real-time monitoring dashboards
- Developing integrated communication platforms
- Utilizing AI-powered risk prediction models

Establishing a Centralized Vendor Management Program
Creating a centralized vendor risk management program ensures consistent oversight and effective risk mitigation across the entire vendor ecosystem. This approach requires:
- Developing clear governance structures
- Creating standardized vendor evaluation protocols
- Implementing comprehensive reporting mechanisms
- Establishing clear escalation procedures for identified risks
Successful vendor management is not a one-time event but a continuous process of assessment, communication, and adaptation. Organizations must view their vendor relationships as dynamic partnerships that require ongoing attention and strategic alignment.
The most effective vendor management programs integrate multiple disciplines. They combine legal compliance, cybersecurity expertise, operational insights, and strategic thinking. By treating vendor management as a critical business function rather than a peripheral activity, organizations can transform potential risks into strategic opportunities for growth and innovation.
Managing Risks and Ensuring Compliance
Navigating the complex terrain of third party vendors management requires a strategic approach to risk mitigation and compliance that goes far beyond traditional checklist methodologies. Organizations must develop sophisticated frameworks that proactively identify, assess, and mitigate potential risks while maintaining rigorous compliance standards.
Comprehensive Due Diligence and Initial Risk Assessment
Conducting thorough due diligence before onboarding vendors is the critical first line of defense in managing third-party risks. This process extends well beyond surface-level evaluations and demands a multifaceted approach to vendor screening. Organizations must meticulously examine:
- Operational Resilience: Assess the vendor's ability to maintain consistent service delivery
- Cybersecurity Protocols: Evaluate comprehensive security measures and incident response capabilities
- Financial Stability: Analyze financial health and long-term sustainability
- Compliance Certifications: Verify adherence to industry-specific regulatory requirements
Implementing a Risk-Tiered Monitoring Strategy
A strategic tiered vendor management approach allows organizations to allocate resources efficiently and apply proportionate risk controls. This methodology involves categorizing vendors into distinct risk levels and developing targeted monitoring strategies:
- High-Risk Vendors: Require most intensive monitoring and frequent comprehensive assessments
- Medium-Risk Vendors: Need periodic detailed reviews and continuous background checks
- Low-Risk Vendors: Subjected to standard annual evaluations and periodic lightweight monitoring
Continuous Compliance and Real-Time Risk Management
Ongoing monitoring and regular compliance reviews are fundamental to maintaining robust vendor risk management. Modern organizations must embrace dynamic, technology-driven approaches that enable:
- Automated compliance tracking systems
- Real-time risk assessment tools
- Periodic comprehensive audits
- Immediate notification mechanisms for potential compliance breaches
Successful risk management transcends mere compliance. It represents a proactive strategy of anticipating potential vulnerabilities, understanding complex interdependencies, and creating adaptive frameworks that can respond quickly to emerging threats.
The most effective organizations view vendor risk management as a continuous, intelligence-driven process. They recognize that compliance is not a static destination but a dynamic journey requiring constant vigilance, technological innovation, and strategic thinking. By integrating advanced risk assessment methodologies, leveraging cutting-edge technologies, and maintaining a holistic view of vendor ecosystems, companies can transform potential risks into strategic opportunities for enhanced operational resilience.
Best Practices for Strong Vendor Relationships
Building and maintaining robust vendor relationships is a strategic imperative that goes far beyond transactional interactions. Successful organizations recognize that effective third party vendors management requires a collaborative, transparent, and mutually beneficial approach.
Establishing Clear Communication and Expectations
Conducting thorough due diligence before engaging with a vendor creates a solid foundation for strong relationships. This process involves more than just initial screening. Organizations must develop comprehensive communication frameworks that:
- Define Clear Performance Metrics: Establish measurable, transparent expectations
- Create Open Dialogue Channels: Develop mechanisms for ongoing communication
- Align Strategic Objectives: Ensure vendor goals complement organizational priorities
- Implement Regular Performance Reviews: Conduct structured evaluations that provide constructive feedback
Developing a Collaborative Risk Management Approach
A tiered vendor management approach enables organizations to create targeted engagement strategies that strengthen relationships while maintaining robust risk controls. This methodology involves:
- Customizing interaction protocols based on vendor risk levels
- Creating collaborative risk mitigation strategies
- Developing joint contingency planning
- Establishing mutual accountability frameworks
Fostering Long-Term Partnership Strategies
Implementing a centralized vendor risk management program supports the development of strategic, long-term vendor relationships. Successful organizations approach vendor relationships as dynamic partnerships that require:
- Continuous knowledge sharing
- Mutual investment in technological and operational improvements
- Transparent risk and opportunity discussions
- Adaptive collaboration mechanisms
The most sophisticated organizations view vendor relationships as strategic assets rather than mere transactional connections. They invest time and resources in understanding vendor capabilities, aligning mutual objectives, and creating ecosystems of shared value and innovation.
Effective vendor relationship management requires a delicate balance between rigorous risk management and collaborative engagement. It demands emotional intelligence, strategic thinking, and a commitment to mutual growth. By treating vendors as strategic partners and creating frameworks of trust, transparency, and shared objectives, organizations can transform potential vendor risks into sources of competitive advantage and organizational resilience.
Frequently Asked Questions
What are third party vendors, and why is their management important?
Third party vendors are external providers that supply goods or services to an organization. Their management is crucial because breaches related to these vendors account for 30% of all data security incidents, making effective oversight vital for the security and operational resilience of a business.
How can organizations assess vendor risk effectively?
Organizations can assess vendor risk by establishing a comprehensive vendor risk assessment framework that includes categorizing vendors by risk levels, conducting thorough due diligence, and implementing continuous monitoring tailored to each vendor's specific risk profile.
What are the best practices for building strong relationships with vendors?
Best practices include establishing clear communication and expectations, developing a collaborative risk management approach, and fostering long-term partnership strategies that emphasize transparency, shared objectives, and mutual accountability.
What role does technology play in vendor management?
Technology drives modern vendor management by enabling continuous monitoring, automated risk assessments, and real-time data analytics. This helps organizations proactively identify and mitigate risks associated with their vendor relationships.
Ready to Reinvent Vendor Risk Management?
Are you struggling to keep up with the rising pressure around third party vendor risk, constant security questionnaires, and the never-ending compliance requirements highlighted in this article? The reality is, inefficient vendor management not only opens the door to costly data breaches but also puts your team under daily stress and slows down critical business partnerships. Imagine taking control and transforming vulnerability into your competitive advantage.

Achieve faster, more accurate responses to vendor security assessments by teaming up with Skypher. Our AI-driven platform streamlines every step of your security questionnaire process, boosts real-time collaboration, and helps you demonstrate trust and transparency to every partner. Turn those hours of frustration into productive wins with Skypher today. Visit Skypher's homepage to see how you can automate your vendor risk workflows and power smarter decisions for 2025 and beyond.
