Cybersecurity is a major concern for organizations today. With an increasing number of cyber threats, SOC software can provide 24/7 monitoring and immediate threat detection. But here’s the surprising part. Many companies fail to leverage its full potential. Because the real game-changer isn't just monitoring; it's about using advanced technologies like AI to transform how we handle security incidents.
Table of Contents
- What Is Soc Software?
- Key Features Of Soc Software
- Benefits Of Using Soc Software
- Choosing The Right Soc Software
Quick Summary
| Takeaway | Explanation |
|---|---|
| Continuous Monitoring is Essential | SOC software provides 24/7 surveillance of networks, systems, and applications to ensure immediate threat detection and incident response. |
| Leverage Advanced Technologies | Implementing AI and machine learning in SOC software enhances threat detection capabilities, enabling organizations to move from reactive to proactive defense strategies. |
| Automate Routine Tasks | Automation features in SOC software reduce manual workloads for security teams, allowing them to focus on complex strategic tasks. |
| Ensure Comprehensive Visibility | SOC software centralizes security monitoring, offering real-time insights and compliance reporting crucial for organizations in regulated industries. |
| Select SOC Software Based on Needs | Choosing the right SOC software requires assessing organizational size, compliance needs, and current security technology to align with specific operational requirements. |
What is SOC software?
In the rapidly evolving landscape of cybersecurity, SOC software represents a critical technological solution for organizations seeking to protect their digital assets and infrastructure from sophisticated cyber threats. At its core, SOC (Security Operations Center) software is a comprehensive platform designed to centralize, monitor, and manage an organization's security operations in real-time.
Defining SOC Software and Its Core Functions
SOC software is a sophisticated technological ecosystem that integrates multiple security tools, technologies, and processes into a unified system. IBM's cybersecurity research highlights that these platforms enable organizations to continuously monitor, detect, analyze, and respond to potential security incidents across their entire digital infrastructure.
The primary objectives of SOC software include:
- Continuous Monitoring: Providing 24/7 surveillance of an organization's network, systems, and applications
- Threat Detection: Identifying potential security vulnerabilities and active cyber threats in real-time
- Incident Response: Enabling rapid and coordinated actions to mitigate and neutralize security risks
Key Components and Technological Capabilities
Modern SOC software goes beyond traditional security monitoring by incorporating advanced technologies and strategic capabilities. These systems typically integrate several critical components:
- Security Information and Event Management (SIEM): Collects and analyzes log data from various sources
- Threat Intelligence Platforms: Provides up-to-date information about emerging cyber threats
- Automated Incident Response Tools: Enables quick and systematic handling of security events
The sophistication of SOC software lies in its ability to transform raw security data into actionable insights. By leveraging artificial intelligence and machine learning algorithms, these platforms can detect anomalies, predict potential threats, and provide context-rich information that empowers security teams to make informed decisions quickly.
Strategic Importance in Cybersecurity
In today's digital ecosystem, SOC software is not just a technological tool but a strategic asset. Research from cybersecurity experts emphasizes the growing importance of structured data gathering and knowledge sharing in developing next-generation security solutions. Organizations implementing robust SOC software can significantly reduce their vulnerability to cyber attacks, minimize potential financial losses, and maintain regulatory compliance.
The value proposition of SOC software extends beyond mere threat detection. It provides organizations with a proactive approach to cybersecurity, transforming traditional reactive models into intelligent, anticipatory defense mechanisms. By centralizing security operations, these platforms enable security teams to work more efficiently, correlate complex security events, and respond to incidents with unprecedented speed and precision.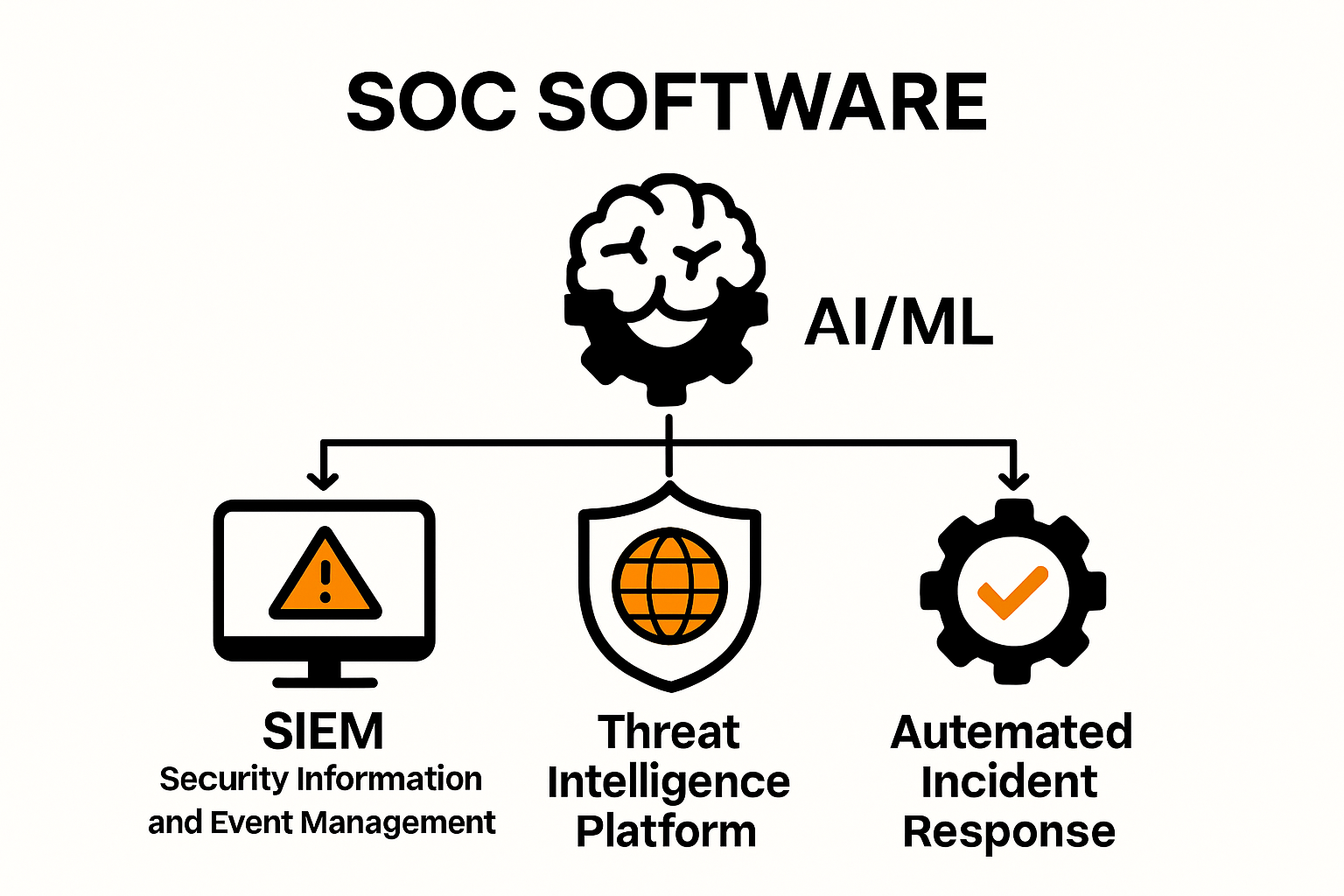
Key features of SOC software
As cyber threats continue to evolve in complexity and sophistication, SOC software has transformed from a simple monitoring tool to a comprehensive, intelligent defense mechanism. The key features of modern SOC software reflect the advanced technological landscape of cybersecurity, enabling organizations to stay ahead of potential security risks.
Advanced Threat Detection and Intelligence
Cybersecurity experts at Cyble emphasize that artificial intelligence and machine learning have become core components of leading SOC software. These advanced technologies enable several critical capabilities:
- Real-time Threat Analytics: Continuous monitoring and instant analysis of potential security incidents
- Predictive Threat Modeling: Using AI to anticipate and prevent potential security breaches
- Anomaly Detection: Identifying unusual network behaviors that might indicate a potential cyber threat
The integration of machine learning algorithms allows SOC software to learn from historical data, continuously improving its threat detection capabilities and reducing false positive rates. This adaptive intelligence transforms how organizations approach cybersecurity, moving from reactive to proactive defense strategies.
Automated Incident Response and Orchestration
 Radiant Security research highlights the critical importance of automation in modern SOC software. Turnkey automation and intelligent orchestration have become fundamental features that distinguish advanced platforms. Key automated capabilities include:
Radiant Security research highlights the critical importance of automation in modern SOC software. Turnkey automation and intelligent orchestration have become fundamental features that distinguish advanced platforms. Key automated capabilities include:
- Autonomous Triage: Automatically categorizing and prioritizing security alerts
- Incident Investigation: AI-driven systems that can quickly gather and analyze relevant context
- Rapid Remediation: Automated response protocols that can neutralize threats without manual intervention
These automation features significantly reduce the workload on security teams, enabling them to focus on complex strategic tasks while the software handles routine monitoring and initial response mechanisms.
Comprehensive Integration and Reporting
Software Analyst research underscores the importance of seamless integration and comprehensive reporting in SOC software. Modern platforms offer robust features that go beyond traditional security monitoring:
- Multi-Source Integration: Ability to collect and correlate data from diverse security tools and systems
- Detailed Compliance Reporting: Generating comprehensive reports for regulatory requirements
- Customizable Dashboard: Providing real-time visibility into an organization's security posture
The ultimate value of SOC software lies in its ability to transform complex security data into actionable insights. By offering intuitive visualization, detailed analytics, and comprehensive reporting, these platforms empower security teams to make informed decisions quickly and effectively.
As cyber threats continue to grow in sophistication, SOC software represents a critical technological shield, combining advanced intelligence, automated response, and strategic insights to protect organizational digital assets.
Benefits of using SOC software
In an increasingly complex digital landscape, SOC software has emerged as a critical tool for organizations seeking robust cybersecurity protection. The benefits of implementing these advanced platforms extend far beyond traditional security measures, offering comprehensive advantages that transform an organization's approach to digital defense.
Enhanced Operational Efficiency
Splunk's State of Security 2025 report reveals compelling insights into the operational benefits of SOC software. Organizations using unified SOC platforms have experienced significant improvements in their security operations:
- Faster Incident Response: 59% of organizations reported accelerated threat mitigation
- Reduced Tool Maintenance: 53% noted decreased administrative overhead
- Streamlined Security Workflows: Centralized management of security processes
By consolidating multiple security tools and automating routine tasks, SOC software dramatically reduces the manual workload on security teams. This efficiency allows cybersecurity professionals to focus on strategic threat analysis and complex security challenges rather than getting bogged down in repetitive monitoring tasks.
Advanced Threat Intelligence and Proactive Defense
Radiant Security research highlights the transformative power of AI and machine learning in SOC software. These technologies enable unprecedented capabilities in threat detection and response:
- Behavioral Analytics: Identifying subtle patterns that indicate potential security risks
- Predictive Threat Modeling: Anticipating potential vulnerabilities before they can be exploited
- Continuous Adaptive Learning: Improving threat detection capabilities over time
The integration of advanced analytics allows organizations to move from a reactive to a proactive security posture. By continuously learning and adapting, SOC software can identify emerging threats that traditional security tools might miss, providing a critical layer of protection in an ever-evolving threat landscape.
Comprehensive Visibility and Compliance
One of the most significant benefits of SOC software is its ability to provide comprehensive visibility across complex digital environments. Cybersecurity experts emphasize that these platforms enable organizations to:
- Centralize Security Monitoring: Create a unified view of an organization's entire security ecosystem
- Ensure Regulatory Compliance: Generate detailed reports and maintain audit trails
- Identify Interconnected Threats: Connect disparate security signals for more holistic threat analysis
This comprehensive approach is particularly crucial for organizations operating in regulated industries or those with complex IT infrastructures. SOC software provides the visibility and documentation needed to demonstrate robust security practices, helping organizations meet stringent compliance requirements while protecting their digital assets.
Ultimately, the benefits of SOC software extend beyond technical capabilities. These platforms represent a strategic investment in an organization's cybersecurity resilience, providing a sophisticated, intelligent approach to protecting digital infrastructure in an increasingly unpredictable threat landscape.
Choosing the right SOC software
Selecting the appropriate SOC software is a critical decision that can significantly impact an organization's cybersecurity strategy. With the rapidly evolving threat landscape and technological advancements, organizations must approach this selection process strategically and comprehensively.
Assessing Organizational Security Requirements
IBM's cybersecurity insights emphasize the importance of thoroughly understanding an organization's unique security needs before selecting SOC software. Key considerations include:
- Organizational Size and Complexity: Matching software capabilities to your infrastructure
- Industry-Specific Compliance Requirements: Ensuring regulatory adherence
- Existing Technology Ecosystem: Compatibility with current security tools
Organizations should conduct a comprehensive security assessment that maps current vulnerabilities, potential threat vectors, and specific operational requirements. This diagnostic approach ensures that the selected SOC software aligns precisely with the organization's security architecture and strategic objectives.
Evaluating Technological Capabilities
Cybersecurity analyst research highlights critical technological features to consider when selecting SOC software:
- Advanced Automation Capabilities: Tools that support comprehensive security orchestration
- AI-Powered Threat Detection: Platforms with machine learning and predictive analytics
- Scalable Architecture: Software that can adapt to growing organizational needs
Modern SOC software should offer more than traditional Security Orchestration, Automation, and Response (SOAR) capabilities. Organizations should prioritize platforms that provide hyperautomation features, enabling seamless integration across multiple security functions and delivering intelligent, context-aware threat management.
Integration and Future-Proofing Considerations
Cyble's cybersecurity trends report underscores the importance of selecting SOC software with robust integration and forward-looking capabilities:
- Multi-Tool Compatibility: Ability to integrate with existing security infrastructure
- Cloud and Hybrid Environment Support: Comprehensive coverage across diverse technological environments
- Continuous Update Mechanisms: Regular feature and threat intelligence updates
The ideal SOC software should not only address current security challenges but also provide flexibility for future technological transformations. Look for platforms that demonstrate a commitment to innovation, offer transparent development roadmaps, and provide comprehensive support ecosystems.
Choosing the right SOC software is more than a technological procurement—it's a strategic investment in an organization's digital resilience. By carefully evaluating technological capabilities, understanding specific organizational needs, and prioritizing adaptable, intelligent solutions, organizations can develop a robust cybersecurity strategy that evolves alongside emerging technological landscapes.
Frequently Asked Questions
What is SOC software?
SOC software, or Security Operations Center software, is a comprehensive platform that centralizes, monitors, and manages an organization’s security operations in real time, helping to detect and respond to potential security threats.
What are the key features of SOC software?
Key features of SOC software include advanced threat detection and intelligence, automated incident response and orchestration, and comprehensive integration and reporting capabilities.
How can SOC software benefit my organization?
Implementing SOC software can enhance operational efficiency, provide advanced threat intelligence for proactive defense, and ensure comprehensive visibility and compliance, ultimately improving your organization's cybersecurity posture.
What should I consider when choosing SOC software?
When selecting SOC software, assess your organization’s security requirements, evaluate technological capabilities, and consider integration and future-proofing to ensure the software can adapt to evolving security needs.
Elevate Your Cybersecurity Strategy with Skypher
In an era where cyber threats are becoming more sophisticated, organizations must enhance their security posture through real-time monitoring and automated incident response. The article on "Top SOC Software Solutions for 2025" emphasizes the importance of leveraging AI technologies to transform how security incidents are handled. But, what about the tedious task of responding to security questionnaires that can often strain your team's resources? This is where Skypher steps in!

Skypher’s AI Questionnaire Automation Tool streamlines the response process for security reviews, enabling your organization to complete these essential tasks faster and with greater accuracy. With features such as real-time collaboration, integration with over 40 third-party risk management platforms, and a customizable Trust Center, Skypher not only enhances operational productivity but also fosters better communication between teams. Don’t let cumbersome security questionnaires slow you down! Visit https://skypher.co and start transforming your approach to security today!
