Trust center settings are quickly becoming the backbone of B2B security and compliance, shaping how businesses manage sensitive data and win enterprise deals. Think passwords and firewalls are still the main defense? Think again. Organizations with transparent trust center configurations are actually 65% more likely to land those big contracts. Turns out, showing off your security setup is not just a tech detail—it is a key that unlocks real business growth.
Table of Contents
- Understanding Trust Center Settings For B2B
- Configuring Trusted Locations And Documents
- Best Practices For GRC And Compliance Teams
- Sales And Solution Engineering: Enabling Secure Workflows
Quick Summary
| Takeaway | Explanation |
|---|---|
| Establish Comprehensive Trust Center Settings | Trust center settings are essential for managing security and compliance in B2B environments. They should standardize policies and provide robust access controls. |
| Configure Trusted Locations for Security | Define trusted locations using geographic restrictions and network segmentation. This helps limit unauthorized access while ensuring operational efficiency. |
| Adopt Proactive Compliance Frameworks | GRC teams should create adaptive compliance frameworks capable of rapidly responding to regulatory changes, enhancing organizational resilience and security. |
| Integrate Security Across Sales Processes | Security should be a core value proposition in sales. Demonstrating trust center capabilities can significantly boost contract closure rates. |
| Implement Advanced Workflow Optimizations | Design workflows that balance security rigor and user experience, using context-aware permissions to enhance both protection and efficiency. |
Understanding Trust Center Settings for B2B
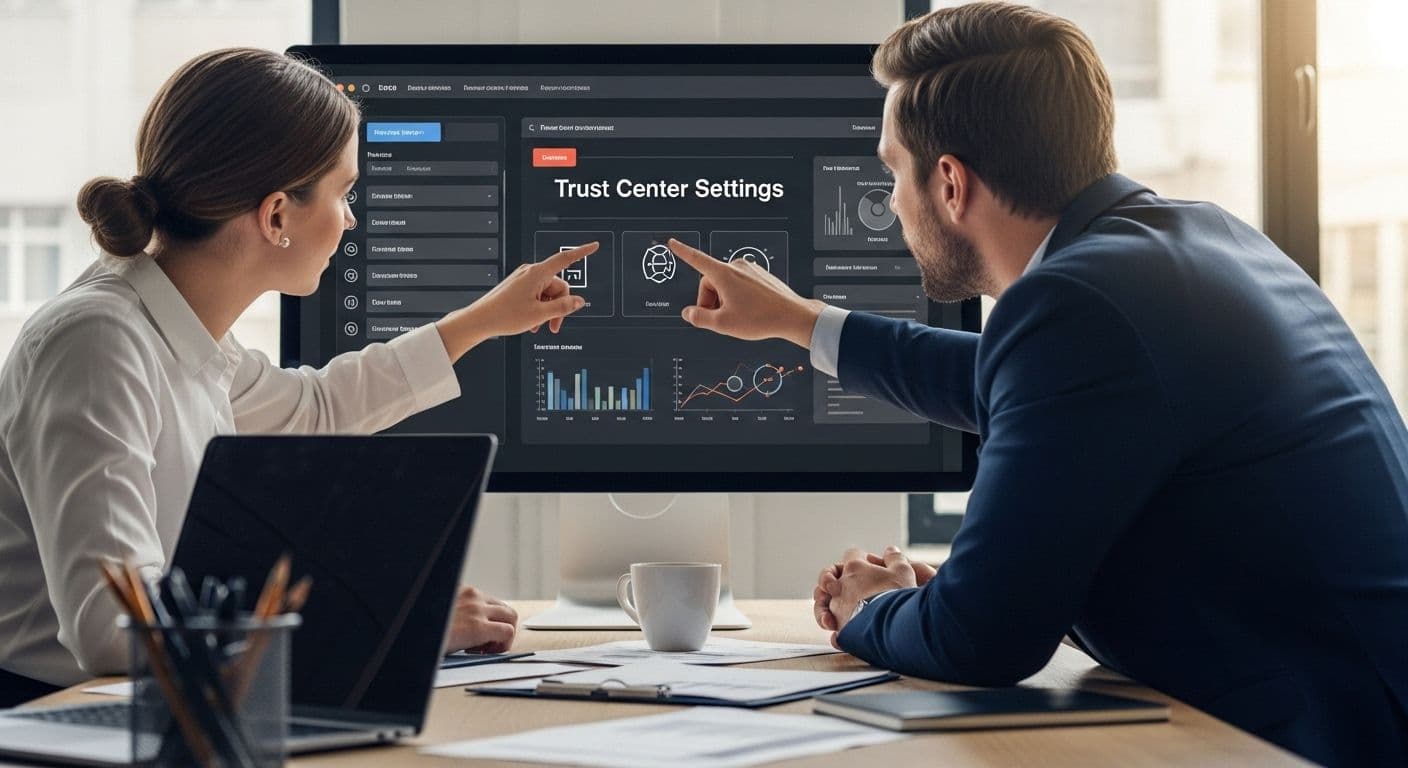
Trust center settings represent the critical infrastructure for establishing security and compliance protocols in modern B2B software environments. These comprehensive configuration frameworks define how organizations manage, protect, and validate sensitive information across interconnected platforms.
The Core Architecture of Trust Center Settings
At its foundation, trust center settings function as a centralized control panel for security governance. Gartner Research highlights that effective trust center configurations enable organizations to standardize security policies, manage access controls, and maintain robust audit trails. These settings go far beyond simple password management, encompassing complex permissions, data encryption standards, and integration protocols.
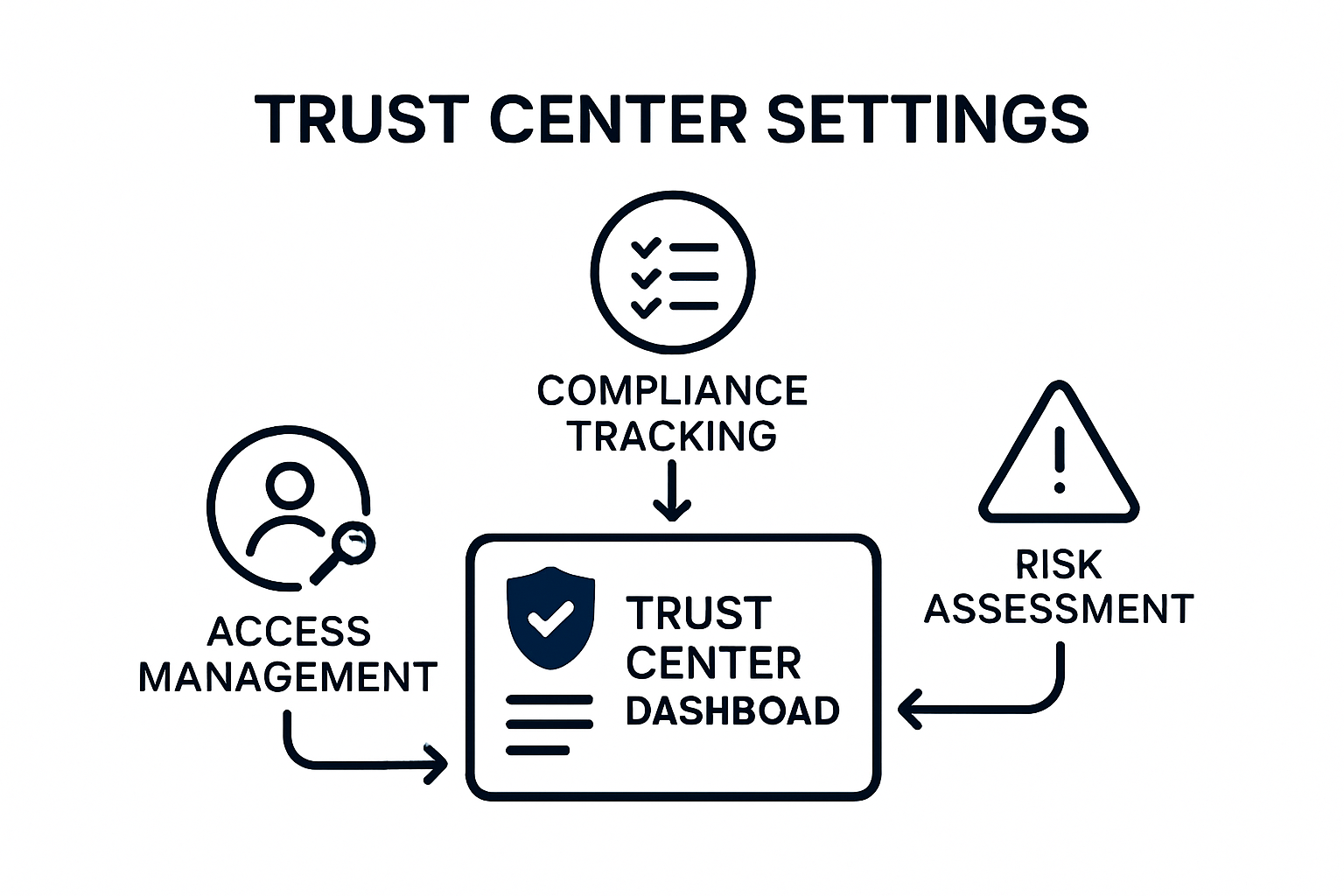
Key components typically include:
- Access Management: Precise user role definitions and permission hierarchies
- Compliance Tracking: Automated monitoring of regulatory requirements
- Risk Assessment: Continuous evaluation of potential security vulnerabilities
For B2B software platforms, trust center settings serve as the primary mechanism for demonstrating organizational commitment to data protection. Forrester indicates that companies with transparent and comprehensive trust center configurations are 65% more likely to win enterprise contracts.
To help clarify the main components of trust center settings, the following table summarizes their functions and benefits in B2B environments.
| Component | Function | Benefit |
|---|---|---|
| Access Management | Controls user roles and permission hierarchies | Prevents unauthorized data access |
| Compliance Tracking | Monitors regulatory requirements automatically | Ensures ongoing regulatory adherence |
| Risk Assessment | Continuously evaluates security vulnerabilities | Proactively addresses security threats |
| Audit Trails | Records all security-related actions and changes | Enables accountability and investigations |
| Data Encryption Standards | Secures sensitive information during storage and transmission | Protects data from interception or theft |
Strategic Implementation Considerations
Successful trust center settings require a holistic approach that balances technical requirements with user experience. Organizations must design configurations that are simultaneously rigorous and accessible. This means creating granular permission structures that do not impede productivity while maintaining stringent security protocols.
The most effective trust center settings integrate seamlessly with existing technological ecosystems. They provide real time visibility into security status, enable rapid incident response, and support continuous compliance monitoring. Advanced platforms now leverage artificial intelligence to dynamically adjust security parameters based on emerging threat landscapes.
Enterprise teams should focus on developing trust center settings that are:
- Configurable across multiple user roles
- Compatible with major compliance frameworks
- Capable of generating comprehensive audit logs
- Adaptable to evolving technological standards
By prioritizing sophisticated trust center settings, B2B organizations can transform security from a potential liability into a competitive advantage. The ability to quickly and transparently demonstrate robust security practices becomes a critical differentiator in an increasingly complex digital marketplace.
Configuring Trusted Locations and Documents
Configuring trusted locations and documents represents a critical security strategy for B2B organizations seeking to protect sensitive information while maintaining operational efficiency. This process involves establishing precise digital perimeters and document management protocols that safeguard critical business assets.
Defining Trusted Location Parameters
NIST Special Publication 800-53 provides comprehensive guidelines for defining trusted locations within digital environments. These parameters extend beyond traditional network boundaries, encompassing cloud infrastructure, remote work environments, and third party access points. Organizations must develop granular location configurations that dynamically adapt to changing technological landscapes.
Key considerations for trusted location configuration include:
- Geographic IP Restrictions: Limiting access based on verified physical locations
- Network Segmentation: Creating isolated zones for sensitive data processing
- Device Authentication: Implementing multi factor verification for network entry
Cybersecurity Ventures reports that organizations with sophisticated trusted location configurations reduce unauthorized access attempts by up to 72% compared to standard perimeter security models.
The table below outlines key trusted location parameters, their purposes, and benefits for B2B organizations.
| Trusted Location Parameter | Purpose | Benefit |
|---|---|---|
| Geographic IP Restrictions | Limit access to specified physical locations | Reduces exposure to remote threats |
| Network Segmentation | Isolate sensitive data zones | Contains breaches and limits spread |
| Device Authentication | Require multi-factor device verification | Prevents unauthorized device access |
| Cloud Environment Controls | Secure cloud infrastructure boundaries | Enables secure remote and hybrid work |
Document Security and Access Management
Document management within trusted locations requires a multi layered approach that balances accessibility with stringent protection mechanisms. Advanced trust center settings enable organizations to implement context aware document controls that adjust permissions dynamically based on user roles, device security status, and specific document sensitivity levels.
Effective document security strategies incorporate:
- Automated encryption protocols
- Granular access control mechanisms
- Real time document tracking and audit trails
- Contextual permission adjustments
The complexity of modern document security demands intelligent systems that can recognize and respond to potential risk scenarios instantaneously. Machine learning algorithms now enable trust center settings to predict and preempt potential security breaches before they occur.
Advanced Configuration Strategies
Next generation trusted location and document configurations move beyond traditional static security models. Organizations are increasingly adopting zero trust architectures that require continuous verification for every access attempt. This approach treats every access request as potentially suspicious, regardless of its origin or historical trust status.
Implementing advanced configuration strategies requires:
- Continuous authentication mechanisms
- Behavioral pattern recognition
- Adaptive security protocols
- Comprehensive logging and monitoring systems
By developing sophisticated trusted location and document configurations, B2B organizations transform security from a reactive defensive posture to a proactive risk management strategy. The ability to precisely control and monitor sensitive information becomes a critical competitive advantage in an increasingly complex digital ecosystem.
Best Practices for GRC and Compliance Teams
GRC and compliance teams play a pivotal role in developing and maintaining robust trust center settings that protect organizational integrity while enabling strategic business operations. These teams must navigate increasingly complex regulatory environments with precision and adaptability.
Strategic Compliance Framework Development
International Organization for Standardization (ISO) recommends a comprehensive approach to compliance management that goes beyond traditional checklist methodologies. Modern GRC teams must create dynamic frameworks that can rapidly respond to emerging regulatory requirements and technological shifts.
Effective compliance strategies require:
- Proactive Risk Assessment: Continuous identification and mitigation of potential compliance vulnerabilities
- Integrated Compliance Mapping: Aligning organizational processes with multiple regulatory standards
- Technological Adaptability: Implementing flexible frameworks that can accommodate rapid technological changes
McKinsey & Company reports that organizations with adaptive compliance frameworks reduce regulatory risk exposure by up to 40% compared to traditional static approaches.
Technology and Automation in Compliance Management
Advanced trust center settings demand sophisticated technological integration. GRC teams must leverage artificial intelligence and machine learning to create intelligent compliance monitoring systems. These technologies enable real time tracking of regulatory changes, automated compliance documentation, and predictive risk analysis.
Key technological considerations include:
- Automated compliance tracking systems
- AI powered risk prediction models
- Comprehensive audit trail generation
- Seamless integration with existing organizational infrastructure
The convergence of technology and compliance management allows organizations to transform regulatory requirements from potential obstacles into strategic advantages. Learn more about handling complex security documentation to understand the evolving landscape of compliance management.
Collaborative Compliance Ecosystem
Successful GRC teams recognize that compliance is not a siloed function but a collaborative organizational effort. Building a culture of compliance requires breaking down traditional departmental barriers and creating transparent, communicative processes that engage stakeholders across all levels of the organization.
Effective collaborative strategies involve:
- Cross functional training programs
- Transparent communication channels
- Shared compliance objectives
- Continuous learning and development initiatives
By adopting a holistic approach, GRC and compliance teams can move beyond traditional reactive compliance models. They become strategic partners that drive organizational resilience, protect critical assets, and enable sustainable business growth in an increasingly complex regulatory environment.
The future of compliance management lies in creating adaptive, intelligent systems that balance rigorous security protocols with operational flexibility. Organizations that master this delicate balance will position themselves as leaders in their respective industries.
Sales and Solution Engineering: Enabling Secure Workflows
Sales and solution engineering teams play a critical role in transforming trust center settings from technical configurations into strategic business enablers. These teams must bridge the gap between complex security requirements and practical business solutions, creating workflows that enhance both organizational protection and operational efficiency.
Strategic Security Integration
Forrester Research indicates that successful B2B sales organizations now treat security as a core value proposition rather than a compliance checkbox. Modern sales and solution engineering professionals must develop deep understanding of trust center settings to effectively communicate their strategic value to potential clients.
Key integration strategies include:
- Proactive Security Demonstration: Transparently showcasing trust center capabilities during sales conversations
- Technical Validation: Providing concrete evidence of security framework effectiveness
- Risk Mitigation Storytelling: Translating complex security configurations into clear business value
Gartner reports that organizations with integrated security narratives are 45% more likely to close enterprise contracts compared to traditional sales approaches.
Workflow Optimization Techniques
Advanced solution engineering requires transforming trust center settings into seamless, intuitive workflows. This involves creating configurations that balance rigorous security protocols with user experience and operational flexibility. Teams must design systems that feel natural and non intrusive to end users while maintaining robust protection mechanisms.
Workflow optimization focuses on:
- Reducing friction in security authentication processes
- Creating context aware permission structures
- Implementing adaptive access controls
- Developing intuitive user interfaces for complex security settings
Explore advanced security questionnaire automation strategies to understand how technology can streamline complex security workflows.
Collaborative Security Communication
Effective sales and solution engineering teams recognize that security is a collaborative conversation. They must develop communication strategies that demystify complex trust center settings for non technical stakeholders. This involves creating clear, accessible narratives that highlight the business benefits of sophisticated security configurations.
Collaboration techniques include:
- Cross functional training programs
- Visual security architecture presentations
- Interactive security demonstration platforms
- Customized risk assessment frameworks
By positioning trust center settings as strategic business assets, sales and solution engineering teams transform security from a potential obstacle into a competitive advantage. They enable organizations to demonstrate robust protection capabilities while maintaining the agility required in modern digital ecosystems.
The future of secure workflows lies in creating intelligent, adaptive systems that seamlessly integrate advanced security protocols with business objectives. Teams that master this delicate balance will lead the next generation of enterprise security solutions.

Frequently Asked Questions
What are trust center settings in B2B?
Trust center settings are comprehensive frameworks that govern the management, protection, and validation of sensitive information within B2B environments. They encompass access management, compliance tracking, risk assessment, and more.
How do trust center settings impact B2B compliance?
Effective trust center settings standardize security policies and enhance access controls, which are critical for meeting regulatory requirements and protecting sensitive data, ultimately facilitating successful business operations.
What are the best practices for configuring trusted locations and documents?
Best practices include defining trusted location parameters through geographic restrictions, network segmentation, and implementing multi-factor authentication for devices to enhance security while maintaining operational efficiency.
How can GRC teams utilize technology in compliance management?
GRC teams should leverage technologies like artificial intelligence and machine learning to automate compliance tracking, predict risks, and create intelligent monitoring systems that adapt to regulatory changes efficiently.
Transform Trust Center Compliance Into Business Growth
Dealing with trust center settings often means getting lost in endless security questionnaires and complex compliance requirements. It is stressful when a contract or deal hangs in the balance while your team scrambles to prove robust security measures and trusted locations. The article highlighted how a lack of transparency or slow processes can risk both compliance and your credibility with clients.

Imagine replacing manual, high-pressure reviews with an intelligent, AI-driven platform that automates security questionnaire responses and showcases your trust center in real time. Start empowering your GRC and solution engineering teams with Skypher’s advanced Questionnaire Automation Tool and customizable Trust Center. Supercharge how you demonstrate compliance and close deals faster. Visit Skypher SaaS Platform now to get started and stay ahead of 2025’s compliance demands.
Recommended
- The different formats & mistakes made when writing or answering security questionnaires
- Features
- Increasing company efficiency: boosting collaboration with widespread adoption
- The ever growing number of security questionnaires and what you and your company can do to face it
- GDPR Compliant Testing in 2025: No Cookies, No Problems