Type 2 SOC 2 compliance is quickly becoming a make-or-break factor for companies that handle sensitive data. Here is something that surprises most leaders: Type 2 SOC 2 demands security controls to work in real life for at least six months—no quick fixes or check-the-box shortcuts allowed. And what really turns heads is that this isn’t just another paperwork drill. The process forces companies to actually strengthen operations and win deeper trust from clients in a world where one security slip can cost it all.
Table of Contents
- Understanding Type 2 Soc 2 Compliance
- Key Differences Between Type 1 and Type 2 Soc 2
- Steps to Achieve Type 2 Soc 2 in 2025
- Benefits of Type 2 Soc 2 for Your Business
Quick Summary
| Takeaway | Explanation |
|---|---|
| Type 2 SOC 2 shows ongoing security effectiveness | Unlike Type 1, Type 2 assesses controls over a minimum six-month period, verifying their operational performance rather than just design. |
| Achieving Type 2 SOC 2 requires thorough preparation | Companies must evaluate their current security infrastructure and address identified gaps, developing robust policies and procedures for compliance. |
| Type 2 SOC 2 enhances stakeholder trust | Independent validation through regular assessments builds confidence among clients and partners, showcasing a company’s commitment to security. |
| Compliance leads to operational improvements | The process fosters ongoing evaluation, encouraging organizations to consistently enhance their security practices and risk management processes. |
| Type 2 SOC 2 supports regulatory alignment | Achieving this compliance helps organizations meet complex security requirements, which is crucial for maintaining industry standards and gaining market advantages. |
Understanding Type 2 SOC 2 Compliance
Type 2 SOC 2 compliance represents a critical framework for organizations seeking to demonstrate robust security controls and build trust with stakeholders. Unlike its Type 1 counterpart, a Type 2 SOC 2 assessment provides a comprehensive evaluation of an organization's security practices over an extended period.
The Foundational Principles of Type 2 SOC 2
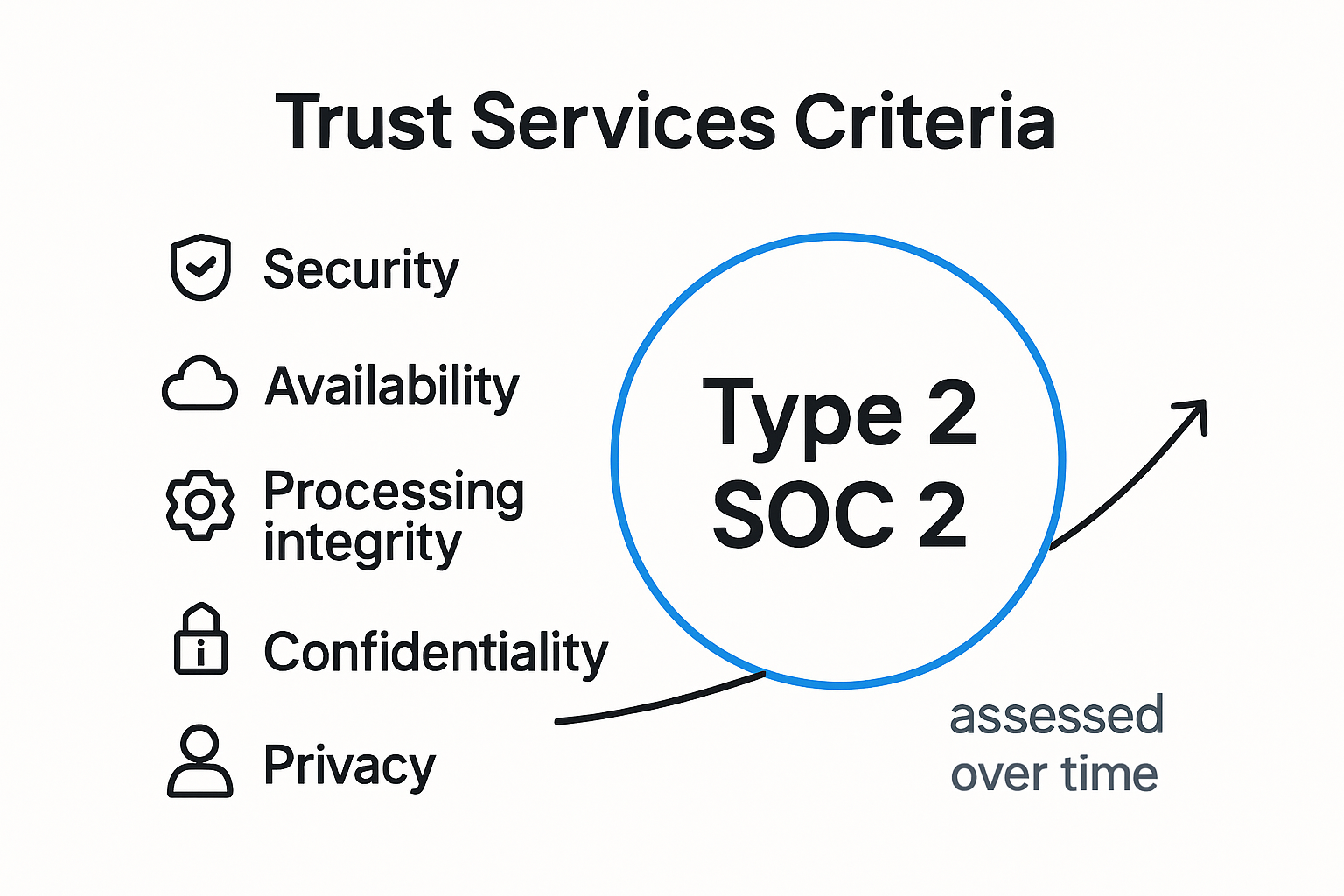
At its core, Type 2 SOC 2 compliance is about proving consistent and effective security controls. Research from the American Institute of CPAs (AICPA) reveals that this compliance framework focuses on five key trust service criteria: security, availability, processing integrity, confidentiality, and privacy.
The assessment goes beyond a snapshot evaluation. While Type 1 reports examine the design of security controls at a specific point in time, Type 2 SOC 2 reports track the actual operational effectiveness of these controls over a minimum six month period. This approach provides a more dynamic and realistic view of an organization's security posture.
Why Type 2 SOC 2 Matters for Modern Organizations
Cybersecurity research indicates that organizations are increasingly adopting Type 2 SOC 2 compliance as a critical mechanism for demonstrating security readiness. The comprehensive nature of these assessments offers several key advantages:
- Comprehensive Verification: Goes beyond surface level checks to validate ongoing security practices
- Stakeholder Confidence: Provides external validation of security controls to clients and partners
- Regulatory Alignment: Helps organizations meet complex regulatory and contractual security requirements
The assessment process involves an independent third party auditor who thoroughly examines an organization's security controls. This external validation ensures an unbiased and professional evaluation of the organization's security practices.
Key elements examined during a Type 2 SOC 2 audit include access controls, data protection mechanisms, incident response protocols, and the consistent implementation of security policies. The auditor will test these controls multiple times throughout the assessment period to confirm their reliability and effectiveness.
For technology companies and service providers, achieving Type 2 SOC 2 compliance is not just a checkbox exercise. It represents a commitment to maintaining high standards of security and demonstrating ongoing diligence in protecting sensitive information. The rigorous nature of the assessment means that organizations must continuously monitor, update, and improve their security practices.
Companies pursuing Type 2 SOC 2 compliance should expect a comprehensive review that requires significant preparation, documentation, and potentially substantial changes to existing security infrastructure. The investment, however, can yield significant benefits in terms of customer trust, competitive differentiation, and risk management.
Key Differences Between Type 1 and Type 2 SOC 2
Understanding the nuanced differences between SOC 2 Type 1 and Type 2 reports is crucial for organizations seeking comprehensive security assessments. While both reports evaluate an organization's security controls, they offer distinctly different levels of insight and assurance.
Temporal Scope and Assessment Depth
According to Schellman, the primary distinguishing factor between Type 1 and Type 2 reports lies in their temporal assessment approach. A Type 1 report provides a snapshot evaluation of control design at a specific point in time, whereas a Type 2 report offers a more extensive examination of control effectiveness over a sustained period.
Research from AuditBoard highlights that while both reports adhere to the same Trust Services Criteria, the depth of analysis varies significantly. Type 1 reports essentially validate the theoretical framework of security controls, while Type 2 reports demonstrate the practical, real-world implementation and consistent performance of these controls.
Comprehensive Evaluation and Stakeholder Confidence
Wikipedia's technical documentation reveals that Type 1 reports typically span a brief assessment period, focusing on control design documentation and theoretical compliance. In contrast, Type 2 reports involve a more rigorous examination, usually extending 9 to 12 months, which provides stakeholders with a more comprehensive understanding of an organization's security practices.
Key differences between Type 1 and Type 2 SOC 2 reports include:
- Assessment Duration: Type 1 is a point-in-time evaluation, while Type 2 covers an extended period
- Depth of Validation: Type 1 verifies control design, Type 2 confirms operational effectiveness
- Stakeholder Trust: Type 2 reports generally provide higher confidence due to sustained performance evidence
For technology companies and service providers, the choice between Type 1 and Type 2 reports depends on specific organizational needs, client requirements, and the desired level of security assurance. Type 1 reports can be valuable for initial compliance demonstrations, but Type 2 reports offer a more robust and credible security validation.
The extended observation period in Type 2 reports allows auditors to test controls multiple times, ensuring consistent performance and identifying potential vulnerabilities that might not be apparent in a single snapshot assessment. This continuous monitoring approach provides a more dynamic and realistic representation of an organization's security posture.
Business leaders and security professionals should carefully consider their compliance strategy, recognizing that while Type 1 reports offer a preliminary assessment, Type 2 reports deliver a more comprehensive and trustworthy validation of security controls. The additional time and resources invested in a Type 2 assessment can yield significant returns in terms of stakeholder confidence and risk management.
Here is a table summarizing the key differences between Type 1 and Type 2 SOC 2 reports for quick reference:
| Feature | Type 1 SOC 2 | Type 2 SOC 2 |
|---|---|---|
| Assessment Duration | Point-in-time (single date) | Extended period (min. 6+ months) |
| Focus | Control design only | Operational effectiveness |
| Depth of Evaluation | Theoretical framework | Real-world implementation/testing |
| Stakeholder Confidence | Lower | Higher |
| Use Case | Initial compliance | Ongoing, robust validation |
Steps to Achieve Type 2 SOC 2 in 2025
Achieving Type 2 SOC 2 compliance requires a strategic and systematic approach. As organizations prepare for 2025, understanding the critical steps to successful certification becomes increasingly important for maintaining robust security practices and building stakeholder trust.
Comprehensive Preparation and Initial Assessment
According to Sikich, the first crucial step in achieving Type 2 SOC 2 compliance involves defining the precise audit scope and conducting a thorough readiness assessment. This initial phase requires organizations to carefully evaluate their existing security infrastructure and identify potential gaps that need addressing.
Research from TrustNet recommends developing a formal security program that comprehensively addresses the five Trust Services Criteria: security, availability, processing integrity, confidentiality, and privacy. This involves creating detailed policies and procedures that demonstrate a systematic approach to managing and protecting sensitive information.
Implementation of Robust Security Controls

Key steps for implementing effective security controls include:
- Access Management: Develop strict access control mechanisms with multi-factor authentication
- Risk Assessment: Conduct regular and comprehensive risk evaluations
- Documentation: Maintain detailed records of security policies and control implementations
- Incident Response: Create and test a robust incident response and management plan
FreeCodeCamp's compliance guide emphasizes the importance of continuous system monitoring and proactive security management. Organizations must establish ongoing processes that consistently validate and improve their security controls.
The implementation phase requires significant investment in both technological infrastructure and organizational processes. This means deploying advanced security tools, implementing comprehensive monitoring systems, and ensuring that all team members understand and adhere to established security protocols.
Organizations should prepare for a minimum six-month assessment period, during which independent auditors will thoroughly examine the effectiveness of implemented controls. This requires maintaining meticulous documentation, demonstrating consistent application of security practices, and being prepared to provide evidence of ongoing compliance.
Technology leaders and security professionals must approach Type 2 SOC 2 compliance as more than a one-time certification. It represents an ongoing commitment to maintaining the highest standards of security and data protection. Regular internal audits, continuous improvement of security practices, and staying updated with emerging cybersecurity trends are essential for long-term success.
By following a structured approach and maintaining a proactive stance towards security, organizations can not only achieve Type 2 SOC 2 compliance but also build a robust security framework that instills confidence among clients, partners, and stakeholders.
To help visualize the key steps for achieving Type 2 SOC 2 compliance, here's a table summarizing the main actions organizations should take during the process:
| Step | Description |
|---|---|
| Define Audit Scope | Specify boundaries, systems, and processes in scope |
| Conduct Readiness Assessment | Evaluate current security posture and identify gaps |
| Develop Security Program | Create policies for all five Trust Service Criteria |
| Implement Security Controls | Deploy controls for access, risk, and incident mgmt. |
| Collect Documentation | Maintain detailed records of policies and procedures |
| Monitor & Test Controls | Ongoing validation through audits and assessments |
| Undergo Third-Party Audit | Engage independent auditor for operational review |
Benefits of Type 2 SOC 2 for Your Business
Type 2 SOC 2 compliance offers far-reaching advantages that extend well beyond basic security validation. For modern businesses navigating increasingly complex technological landscapes, these reports represent strategic investments in organizational credibility and operational excellence.
Strategic Business Value and Trust Enhancement
Research from CBH Consulting reveals that SOC 2 reports provide substantial organizational value by creating actionable security insights and enabling operational efficiency. The comprehensive nature of Type 2 SOC 2 assessments allows businesses to demonstrate a proactive approach to security management.
According to AuditPeak, the report builds critical stakeholder trust through enhanced transparency and systematic security validation. This trust becomes a significant competitive differentiator in markets where data protection is paramount.
Comprehensive Operational and Market Benefits
NEDigital's compliance research highlights multiple strategic advantages of SOC 2 compliance:
- Enhanced Customer Confidence: Demonstrates commitment to robust security practices
- Operational Improvements: Identifies and addresses potential security vulnerabilities
- Regulatory Alignment: Helps meet complex compliance requirements
- Competitive Differentiation: Provides a clear market advantage
Type 2 SOC 2 reports go beyond mere documentation. They represent a comprehensive evaluation of an organization's security ecosystem, offering deep insights into operational processes, risk management strategies, and control effectiveness.
For technology companies and service providers, these reports serve multiple critical functions. They not only validate existing security infrastructure but also provide a roadmap for continuous improvement. The extended assessment period allows auditors to observe and validate control performance over time, offering a more nuanced understanding of an organization's security posture.
Businesses can leverage Type 2 SOC 2 reports to streamline vendor risk management, accelerate sales cycles, and reduce the frequency of individual security questionnaires. By presenting a standardized, third-party validated security assessment, companies can significantly reduce due diligence time and demonstrate their commitment to maintaining high security standards.
Moreover, the process of achieving and maintaining Type 2 SOC 2 compliance drives internal cultural shifts. It encourages organizations to develop more rigorous security practices, foster a culture of continuous improvement, and align technological infrastructure with strategic business objectives.
The investment in Type 2 SOC 2 compliance yields returns that extend far beyond immediate security validation. It positions businesses as responsible, forward-thinking organizations committed to protecting stakeholder interests and maintaining the highest standards of operational excellence.
Frequently Asked Questions
What is Type 2 SOC 2 compliance?
Type 2 SOC 2 compliance is a framework designed to assess an organization's security controls over a minimum of six months, focusing on their operational effectiveness rather than just their design.
How does Type 2 SOC 2 differ from Type 1 SOC 2?
Type 2 SOC 2 provides an ongoing evaluation of security controls over time, while Type 1 SOC 2 provides a snapshot assessment of control design at a specific point in time. Type 2 reports validate the practicality of control effectiveness.
Why is Type 2 SOC 2 important for organizations?
Type 2 SOC 2 is vital as it enhances stakeholder trust, demonstrates ongoing security effectiveness, and aligns with regulatory requirements. Achieving this compliance can provide a competitive advantage in the market.
What are the steps to achieve Type 2 SOC 2 compliance?
To achieve Type 2 SOC 2 compliance, organizations should define their audit scope, conduct a readiness assessment, develop a security program, implement robust security controls, gather documentation, continuously monitor and test these controls, and undergo an independent third-party audit.
Make Type 2 SOC 2 Your Security Differentiator With Skypher
Having a strong Type 2 SOC 2 report is not enough if your team gets stuck every time a new security questionnaire lands in your inbox. The article shows just how demanding Type 2 SOC 2 is—solid controls, continual monitoring, and tough audits. The next hurdle is translating all this hard compliance work into quick responses for clients and partners. Wasted hours and scattered answers during security reviews can ruin the trust and operational confidence you have built.

Let Skypher close this gap for you. Automate and speed up your security questionnaire workflow using our AI Questionnaire Automation Tool. Share your completed Type 2 SOC 2 evidence instantly through a fully customizable Trust Center and see how our SaaS platform cuts response times and boosts accuracy, even with complex requirements. Visit https://skypher.co to start transforming your compliance proofs into a business advantage. Get started now to stop losing momentum just when trust matters most.
