Cyber attacks are growing every year and organizations are now facing threats that can show up anywhere in their systems. Get this. A single data breach costs US companies an average of $9.48 million. Most people think you can just add more firewalls or passwords to keep hackers out. That approach fails because the real edge comes from tools like Google SIEM which watch everything at once and spot attacks before they become disasters.
Table of Contents
- What Is Google Siem And Its Role In Cybersecurity?
- Why Google Siem Matters For Modern Organizations
- How Google Siem Works: Core Components And Processes
- Key Concepts Behind Google Siem: Threat Detection And Response
- Real-World Applications Of Google Siem In Risk Management
Quick Summary
| Takeaway | Explanation |
|---|---|
| Google SIEM centralizes security logs | It aggregates event logs from various sources, providing a complete view of the security landscape. |
| Real-time monitoring enhances threat detection | Continuous tracking allows for the swift identification of security anomalies and potential breaches. |
| Cloud-based architecture offers scalability | Google SIEM adapts to organizational growth, ensuring security management evolves with changing needs. |
| Machine learning drives intelligent analytics | Advanced algorithms help predict and identify threats, improving incident response capabilities. |
| Supports compliance and risk management | The platform provides actionable insights for maintaining regulatory compliance and managing cybersecurity risks effectively. |
What is Google SIEM and Its Role in Cybersecurity?
Google SIEM represents a comprehensive cloud-based security solution designed to help organizations monitor, detect, and respond to potential cybersecurity threats across their digital infrastructure. By integrating advanced analytics, machine learning, and real-time monitoring capabilities, Google SIEM transforms how businesses approach information security management.
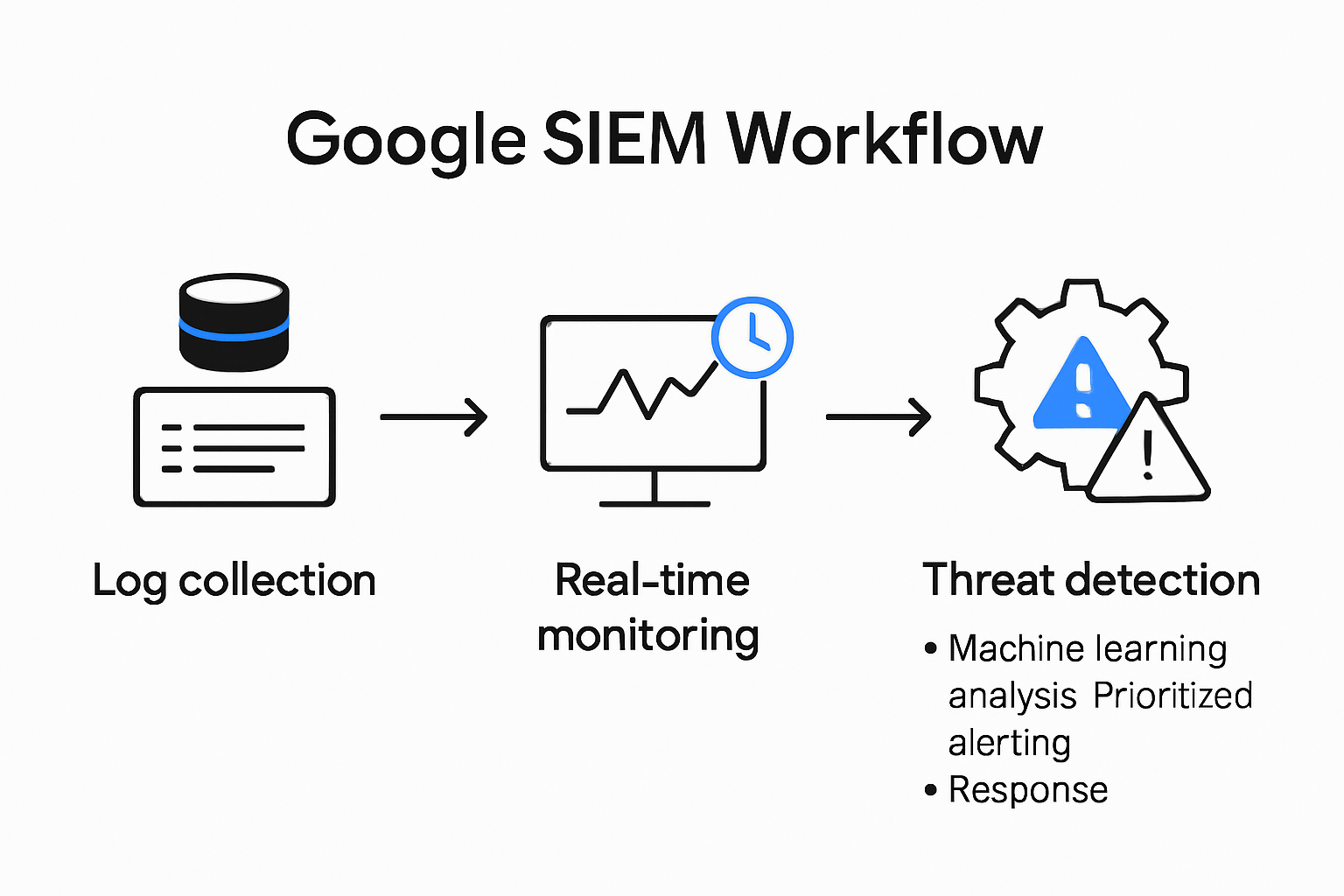
Understanding the Core Components
At its fundamental level, Google SIEM combines multiple critical security functions into a unified platform. These functions include log management, threat detection, incident response, and comprehensive security analytics. The system collects and aggregates data from various sources such as network devices, servers, applications, and cloud environments, creating a holistic view of an organization's security landscape.
To help clarify the core components and their roles in Google SIEM, the following table organizes each major feature alongside its description and purpose.
| Component | Description | Purpose |
|---|---|---|
| Log Aggregation | Collects security event logs from multiple sources | Centralizes data for unified security monitoring |
| Real-time Monitoring | Continuously tracks system activities and anomalies | Enables swift identification of potential threats |
| Advanced Threat Detection | Uses machine learning algorithms for threat identification | Detects and analyzes security incidents intelligently |
| Incident Response | Provides actionable guidance for responding to threats | Minimizes impact and supports quick mitigation |
| Security Analytics | Analyzes aggregated data to spot patterns and risks | Delivers insights for proactive cybersecurity |
Key components of Google SIEM include:
- Log Aggregation: Centralized collection of security event logs from multiple sources
- Real-time Monitoring: Continuous tracking of system activities and potential security anomalies
- Advanced Threat Detection: Intelligent identification of potential security incidents using machine learning algorithms
The Strategic Importance of SIEM
According to NIST, SIEM systems play a crucial role in modern cybersecurity strategies by providing comprehensive visibility and rapid incident response capabilities. Google SIEM goes beyond traditional security monitoring by leveraging cloud-native architectures and sophisticated analytics to identify potential threats before they can cause significant damage.
By integrating advanced correlation techniques and predictive analysis, Google SIEM enables security teams to:
- Quickly identify and investigate potential security breaches
- Reduce mean time to detect and respond to incidents
- Maintain compliance with various regulatory requirements
- Gain actionable insights into an organization's security posture
The cloud-based nature of Google SIEM offers additional advantages, including scalability, flexibility, and continuous updates that ensure organizations remain protected against emerging cyber threats. This approach represents a significant evolution from traditional on-premises security monitoring tools, providing more dynamic and intelligent security management.
Why Google SIEM Matters for Modern Organizations
Modern organizations face increasingly complex cybersecurity challenges that demand sophisticated, intelligent monitoring and response capabilities. Google SIEM emerges as a critical solution for businesses seeking comprehensive security management that goes beyond traditional defensive approaches.
Evolving Threat Landscape
The digital ecosystem has transformed dramatically, with cyber threats becoming more sophisticated and persistent. Organizations now encounter complex attack vectors ranging from ransomware and advanced persistent threats to insider risks and cloud-based vulnerabilities. IEEE Computer Society emphasizes that modern SIEM systems are no longer optional but essential for maintaining robust cybersecurity infrastructure.
Key characteristics that make Google SIEM crucial include:
- Rapid threat detection across complex digital environments
- Intelligent correlation of security events from multiple sources
- Proactive risk identification using machine learning algorithms
- Comprehensive visibility into organizational security posture
Strategic Security Intelligence
Google SIEM transcends traditional security monitoring by providing strategic intelligence that empowers security teams. By aggregating and analyzing vast amounts of security data in real-time, organizations can transform raw information into actionable insights. This approach enables predictive threat management, allowing businesses to anticipate and mitigate potential security risks before they escalate.
The platform's cloud-native architecture offers significant advantages, including:
- Scalable security infrastructure that adapts to organizational growth
- Continuous updates reflecting the latest threat intelligence
- Reduced infrastructure complexity and maintenance overhead
- Enhanced compliance reporting and audit capabilities
Moreover, Google SIEM supports organizations in understanding complex security questionnaire requirements, enabling more comprehensive risk management strategies. By providing a holistic view of an organization's security landscape, businesses can make informed decisions, optimize their security investments, and maintain a robust defense against emerging cyber threats.
How Google SIEM Works: Core Components and Processes
Google SIEM operates through a sophisticated architecture that combines advanced data collection, intelligent processing, and real-time threat analysis. By leveraging cloud-native technologies and machine learning algorithms, the platform creates a dynamic security monitoring ecosystem that adapts to evolving cybersecurity challenges.
Data Collection and Aggregation
The foundation of Google SIEM lies in its comprehensive data collection mechanism. The system seamlessly integrates logs and telemetry data from multiple sources, including network devices, cloud services, applications, and endpoint systems. According to CISA, this centralized approach enables organizations to develop a holistic view of their security landscape.
The table below summarizes Google SIEM's key strategies for data collection and threat detection, helping readers understand each step in the process and its significance.
| Stage | Strategy/Technique | Significance |
|---|---|---|
| Data Collection | Automated log ingestion, real-time streaming | Ensures all security-relevant data is captured |
| Data Normalization | Standardized log formatting | Supports consistent and accurate analysis |
| Secure Data Transmission | Encrypted data channels | Protects sensitive information in transit |
| Threat Detection | Machine learning, behavioral analysis, pattern recognition | Identifies anomalies and potential incidents |
| Incident Response Recommendation | Automated response guidance | Enables rapid mitigation of detected threats |
Key data collection strategies include:
- Automated log ingestion from diverse technological environments
- Real-time data streaming capabilities
- Standardized log normalization to ensure consistent analysis
- Secure data transmission using encrypted channels
Intelligent Threat Detection and Analysis
Once data is collected, Google SIEM employs advanced machine learning algorithms to transform raw information into actionable security intelligence. The platform continuously analyzes patterns, identifies anomalies, and correlates events across different systems to detect potential security threats.
The threat detection process involves:
- Behavioral analysis of user and system activities
- Predictive threat modeling using historical data
- Automated threat scoring and prioritization
- Generation of detailed incident response recommendations
By helping organizations navigate complex security questionnaire requirements, Google SIEM provides a comprehensive approach to cybersecurity management. The platform's intelligent design ensures that security teams can quickly identify, investigate, and mitigate potential risks, transforming reactive security practices into proactive defense strategies.
Key Concepts Behind Google SIEM: Threat Detection and Response
Threat detection and response represent the cornerstone of modern cybersecurity strategies, with Google SIEM providing advanced capabilities that transform how organizations protect their digital assets. By integrating sophisticated analytical techniques and real-time monitoring, the platform enables proactive security management that goes beyond traditional defensive approaches.
Threat Detection Methodologies
Google SIEM employs multiple sophisticated methodologies to identify potential security threats across complex digital environments. According to NIST, effective threat detection requires a comprehensive approach that combines multiple analytical techniques and contextual understanding.
Key threat detection strategies include:
- Behavioral anomaly detection using machine learning algorithms
- Correlation of events across multiple system logs
- Pattern recognition for identifying potential malicious activities
- Contextual analysis of user and system interactions
Incident Response Framework
The incident response capabilities of Google SIEM are designed to provide security teams with actionable intelligence and rapid mitigation strategies. The platform transforms threat detection into a structured, methodical process that enables organizations to respond quickly and effectively to potential security incidents.
Critical components of the incident response framework involve:

- Automated threat prioritization and risk scoring
- Detailed forensic analysis and evidence collection
- Streamlined communication and escalation protocols
- Comprehensive reporting and compliance documentation
Moreover, our advanced security features demonstrate how Google SIEM empowers organizations to move beyond reactive security measures. By providing intelligent, context-aware threat detection and response capabilities, the platform enables security teams to anticipate, identify, and neutralize potential risks before they can cause significant damage to organizational infrastructure.
Real-World Applications of Google SIEM in Risk Management
Google SIEM transforms risk management from a reactive process to a proactive, intelligence-driven strategy. By providing comprehensive visibility and advanced analytical capabilities, organizations can systematically identify, assess, and mitigate potential cybersecurity risks across complex technological landscapes.
Enterprise Security Governance
In enterprise environments, Google SIEM serves as a critical tool for comprehensive security governance. The platform enables organizations to establish robust risk management frameworks that transcend traditional security monitoring. By integrating data from multiple sources, businesses can develop a holistic understanding of their technological ecosystem and potential vulnerabilities.
Key enterprise risk management applications include:
- Continuous compliance monitoring across regulatory frameworks
- Comprehensive asset and vulnerability tracking
- Real-time identification of potential security gaps
- Detailed audit trail generation for regulatory reporting
Incident Prediction and Mitigation
Google SIEM's advanced machine learning algorithms enable organizations to transition from reactive incident response to predictive risk management. The platform analyzes historical data, identifies emerging patterns, and generates actionable insights that help security teams anticipate and prevent potential security breaches before they occur.
Risk mitigation strategies encompass:
- Predictive threat modeling based on behavioral analytics
- Automated risk scoring and prioritization
- Contextual threat intelligence integration
- Proactive vulnerability remediation recommendations
Moreover, navigating the complex landscape of security questionnaires becomes significantly more manageable with Google SIEM's comprehensive risk management capabilities. By providing a centralized platform for security assessment and monitoring, organizations can streamline their risk evaluation processes, enhance their security posture, and demonstrate robust compliance to stakeholders and regulatory bodies.
Bridge the Gap Between Advanced Security Monitoring and Seamless Risk Assessment
You have seen how Google SIEM modernizes threat detection and response, giving organizations real-time visibility and control across their security landscape. However, understanding and acting on complex security intelligence is only part of the challenge. Many teams still struggle to efficiently complete and demonstrate their compliance through detailed security questionnaires, especially when every minute counts in sales and due diligence cycles.

With Skypher, you can turn your SIEM insights into action by automating security questionnaire responses. Our AI-powered Questionnaire Automation Tool instantly connects your security posture with customer and partner requirements. Use real-time collaboration, integrate with leading risk platforms, and build trust faster with a customizable Trust Center. Reduce delays, limit manual effort, and improve accuracy when every response matters most. Start now at skypher.co and experience a smarter way to protect your growth.
Frequently Asked Questions
What is Google SIEM?
Google SIEM is a cloud-based security solution that helps organizations monitor, detect, and respond to cybersecurity threats using advanced analytics and real-time monitoring capabilities.
How does Google SIEM enhance threat detection?
Google SIEM employs machine learning algorithms and intelligent correlation techniques to identify potential security incidents by analyzing patterns and anomalies within collected data.
What are the key components of Google SIEM?
The key components of Google SIEM include log aggregation, real-time monitoring, advanced threat detection, and incident response, providing a holistic view of an organization's security landscape.
How does Google SIEM support compliance and risk management?
Google SIEM helps organizations maintain compliance by providing continuous monitoring across regulatory frameworks, detailed audit trails, and actionable insights for risk mitigation, improving overall security governance.
