Security attestation is shaping how companies prove they are truly safeguarding their digital assets and data. Over 70 percent of federal organizations now require formal security attestations from software vendors before deployment, according to CISA. Most people see these checks as just another hoop to jump through for compliance. That misses the big picture, because security attestation is quickly becoming the foundation for real trust in today’s digital world—and it is turning cybersecurity from a box-ticking exercise into a powerful business advantage.
Table of Contents
- What Is Security Attestation And Why It Matters?
- Key Concepts In Security Attestation
- How Security Attestation Works: Mechanisms Explained
- Real-World Applications Of Security Attestation
- The Future Of Security Attestation In Compliance And Risk
Quick Summary
| Takeaway | Explanation |
|---|---|
| Security attestation verifies system integrity. | This process involves independent review of security practices to ensure compliance and trustworthiness. |
| Continuous monitoring is vital for ongoing security. | Organizations must track system configurations in real-time to identify vulnerabilities dynamically and adapt strategies accordingly. |
| Cryptographic evidence establishes digital trust. | By generating proof of system states and configurations, organizations can build confidence among stakeholders and regulatory bodies. |
| Automated systems enhance attestation efficiency. | Leveraging AI and automation can streamline verification processes and improve real-time risk assessments significantly. |
| Attestation is essential in regulated industries. | Sectors like healthcare and finance rely on attestation to ensure compliance with strict security protocols and protect sensitive data. |
What is Security Attestation and Why It Matters?
Security attestation represents a critical mechanism for verifying and validating the integrity, security posture, and trustworthiness of digital systems, networks, and infrastructure. At its core, security attestation provides organizations with a systematic approach to confirming that specific security standards, controls, and compliance requirements have been met and maintained.
The Fundamental Purpose of Security Attestation
Security attestation goes beyond simple compliance checking. It serves as a comprehensive process where independent experts or authorized entities review and validate an organization's security practices, technical controls, and risk management strategies. According to NIST, this verification process establishes trust by providing cryptographic evidence about the accurate state of systems and their adherence to predetermined security protocols.
Key Components of Security Attestation
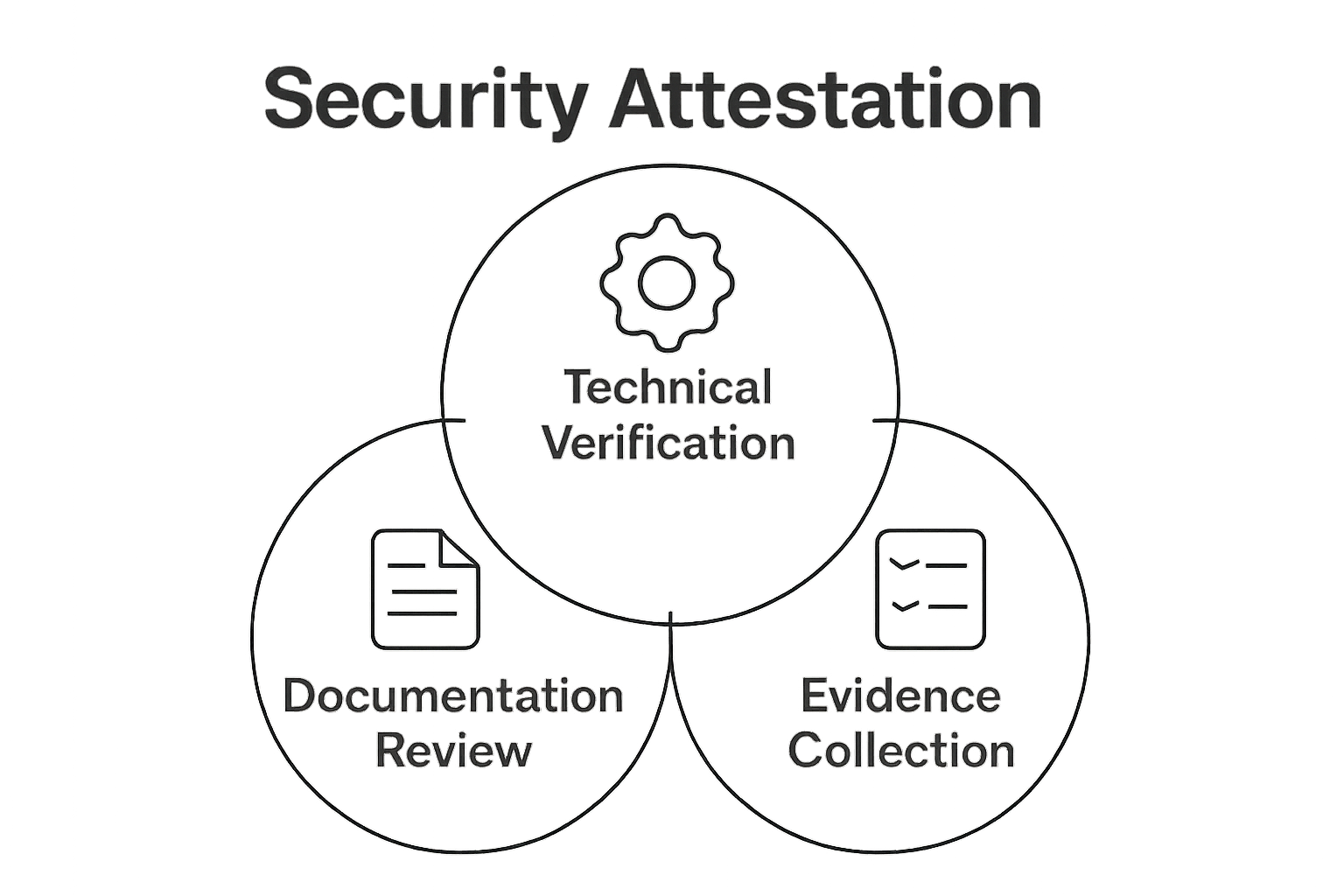
The security attestation process typically involves several critical elements that ensure thorough and credible validation:
- Technical Verification: Detailed examination of system configurations, security controls, and architectural design
- Documentation Review: Comprehensive analysis of security policies, procedural guidelines, and risk management frameworks
- Evidence Collection: Gathering empirical data demonstrating the implementation and effectiveness of security measures
By combining these components, organizations can create a robust mechanism for proving their commitment to maintaining high security standards.
The following table breaks down the three main components of the security attestation process, summarizing their focus and role in validating the integrity of digital systems.
| Component | Focus Area | Role in Security Attestation |
|---|---|---|
| Technical Verification | System configurations and security controls | Ensures proper implementation of security measures |
| Documentation Review | Security policies and risk management documentation | Confirms procedures align with regulations and standards |
| Evidence Collection | Empirical proof and operational security data | Provides verifiable data supporting security claims |
 Security attestation becomes particularly crucial in scenarios involving sensitive data, regulated industries, and environments where trust and transparency are paramount.
Security attestation becomes particularly crucial in scenarios involving sensitive data, regulated industries, and environments where trust and transparency are paramount.
The significance of security attestation extends beyond mere compliance. It represents a proactive approach to cybersecurity that helps organizations identify potential vulnerabilities, demonstrate due diligence, and build confidence among stakeholders, customers, and regulatory bodies. Through systematic evaluation and validation, businesses can transform security from a reactive measure into a strategic organizational capability.
Key Concepts in Security Attestation
Security attestation is built upon several fundamental concepts that enable organizations to establish trust, verify system integrity, and maintain robust cybersecurity frameworks. Understanding these core principles is essential for implementing effective attestation strategies.
Attestation Identity and Trust Establishment
At the heart of security attestation lies the critical process of establishing digital identity and trust. According to IETF standards, this involves creating cryptographic mechanisms that can uniquely identify and validate the integrity of digital systems. The Attestation Identity Key (AIK) serves as a cornerstone in this process, providing a secure method for platforms to prove their authenticity and integrity.
Core Elements of Security Attestation
Security attestation encompasses several key components that work together to create a comprehensive verification mechanism:
- Cryptographic Evidence: Generating verifiable proof of system state and configuration
- Independent Verification: Enabling third-party assessment of security controls
- Continuous Monitoring: Tracking and validating ongoing system integrity
These elements combine to create a dynamic approach to security validation that goes beyond static compliance checks. By implementing robust attestation mechanisms, organizations can develop a proactive strategy for identifying and mitigating potential security risks.
Technological Foundations of Attestation
The technological infrastructure supporting security attestation relies on advanced cryptographic techniques and secure computing principles. This includes sophisticated methods for generating, storing, and validating cryptographic keys that can provide irrefutable evidence of a system's security status. The process involves complex interactions between hardware, software, and cryptographic protocols that ensure the authenticity and integrity of digital environments.
Ultimately, security attestation represents a sophisticated approach to building trust in digital ecosystems. By leveraging advanced cryptographic techniques and comprehensive verification processes, organizations can create resilient security frameworks that adapt to evolving technological challenges and threat landscapes.
How Security Attestation Works: Mechanisms Explained
Security attestation operates through sophisticated mechanisms designed to validate and verify the integrity of digital systems, ensuring comprehensive protection against potential security vulnerabilities. These mechanisms involve complex interactions between technological components that establish trust and authenticate system states.
Cryptographic Validation Process
The core of security attestation relies on cryptographic techniques that generate verifiable evidence about a system's configuration and security status. According to CISA guidelines, this process involves creating cryptographically signed statements that provide authoritative proof of a system's security posture. The validation mechanism typically includes:
- Secure Key Generation: Creating unique cryptographic keys for system identification
- Digital Signature Creation: Generating tamper-evident evidence of system integrity
- Independent Verification: Enabling third-party assessment of security claims
Trusted Execution Environment Mechanisms
Modern security attestation leverages Trusted Execution Environments (TEEs), which create isolated computing spaces that protect critical data and code. These environments use hardware-based security features to ensure that computational processes remain confidential and unaltered. TEEs provide a robust mechanism for:
- Protecting sensitive computational processes
- Preventing unauthorized access to critical system resources
- Generating verifiable evidence of system integrity
Continuous Monitoring and Verification
Security attestation is not a one-time event but a continuous process of monitoring and validation. Organizations implement dynamic mechanisms that continuously track system configurations, detect potential anomalies, and generate real-time attestation reports. This approach transforms security from a static checkpoint into an ongoing, adaptive process that responds to emerging threats and changing technological landscapes.
By integrating advanced cryptographic techniques, hardware-based security mechanisms, and continuous monitoring strategies, security attestation provides organizations with a comprehensive framework for establishing and maintaining digital trust.

Real-World Applications of Security Attestation
Security attestation has evolved from a theoretical concept to a critical operational strategy across multiple industries, providing organizations with robust mechanisms to validate and secure their digital infrastructures. By implementing comprehensive attestation processes, businesses can demonstrate compliance, mitigate risks, and build trust with stakeholders.
Government and Critical Infrastructure Verification
Government agencies have been at the forefront of adopting security attestation mechanisms. According to CISA guidelines, federal organizations now require software producers to provide formal attestations about their secure development practices. This approach ensures that critical systems maintaining national infrastructure meet stringent security standards:
- Software Supply Chain Security: Verifying the integrity of software development processes
- Compliance Documentation: Creating formal records of security control implementations
- Risk Management: Identifying and mitigating potential vulnerabilities before deployment
Enterprise Technology and Cloud Security
In the corporate technology landscape, security attestation has become an essential component of risk management strategies. Organizations leverage attestation processes to validate the security posture of cloud services, third-party vendors, and internal technology ecosystems. These mechanisms provide comprehensive insights into:
- Verifying data protection protocols
- Ensuring regulatory compliance across different jurisdictions
- Maintaining transparency in technology infrastructure
Healthcare and Financial Services Security
Highly regulated industries like healthcare and financial services rely extensively on security attestation to protect sensitive information and maintain strict compliance requirements. By implementing rigorous attestation frameworks, these sectors can:
- Protect patient and financial data
- Demonstrate adherence to industry-specific security regulations
- Create audit trails for regulatory investigations
Security attestation transforms complex security challenges into manageable, verifiable processes.
This table provides an at-a-glance comparison of how security attestation is leveraged across key industries, highlighting each sector's primary attestation applications and objectives.
| Industry | Main Attestation Applications | Primary Objectives |
|---|---|---|
| Government/Critical Infrastructure | Software supply chain, compliance documentation | Maintain national security, ensure secure software deployment |
| Enterprise Technology/Cloud | Data protection, regulatory transparency | Manage risks, build trust with customers and partners |
| Healthcare/Financial Services | Patient and financial data protection | Meet regulatory mandates, protect sensitive information |
| By providing structured mechanisms for validation and continuous monitoring, organizations can build resilient digital environments that adapt to emerging technological threats and regulatory landscapes. |
The Future of Security Attestation in Compliance and Risk
The landscape of security attestation is rapidly transforming, driven by technological advancements, evolving regulatory requirements, and increasingly sophisticated cybersecurity challenges. Organizations are moving beyond traditional compliance frameworks to develop more dynamic, intelligent approaches to security validation and risk management.
Automation and Intelligent Attestation
According to NIST guidance, the future of security attestation will be characterized by increased automation and intelligent monitoring capabilities. This shift represents a fundamental change in how organizations approach security verification:
- Real-Time Verification: Continuous monitoring of system configurations
- Predictive Risk Assessment: Using AI to anticipate potential security vulnerabilities
- Dynamic Compliance Adaptation: Automatically updating security protocols based on emerging threats
Integration of Advanced Technologies
Emerging technologies are reshaping the security attestation landscape, introducing more sophisticated mechanisms for trust establishment and risk mitigation. These advanced approaches will leverage:
- Artificial Intelligence for predictive security modeling
- Blockchain technologies for immutable attestation records
- Machine learning algorithms for complex threat detection
Strategic Compliance Transformation
Security attestation is evolving from a reactive compliance requirement to a strategic business asset. Organizations are recognizing that robust attestation processes provide more than just regulatory adherence they offer competitive advantages by:
- Demonstrating organizational resilience
- Building stakeholder confidence
- Creating transparent risk management frameworks
The future of security attestation represents a paradigm shift from static verification to dynamic, intelligent risk management. By embracing technological innovations and adopting proactive strategies, organizations can transform security attestation from a mandatory checkpoint into a powerful mechanism for building digital trust and organizational resilience.
Turn Security Attestation Into Competitive Advantage With Skypher
Are you struggling to prove your security posture during high-stakes reviews? The growing demands of security attestation often create stress for teams facing strict compliance requirements and constant scrutiny from clients and regulators. You know how important cryptographic evidence, detailed risk management, and continuous monitoring are, yet the manual process of responding to security questionnaires can drain your resources and slow down your business.

Imagine completing detailed security reviews in a fraction of the time, with accuracy and transparency that instantly builds trust. Skypher empowers organizations to automate the response process, leveraging AI for rapid and credible questionnaire completion. Enhance your ability to demonstrate security maturity using real-time collaboration, seamless integrations, and a custom Trust Center designed to streamline every step. If you are ready to move past tedious compliance work and focus on what matters, explore how Skypher's AI Questionnaire Automation Tool can transform your attestation processes. Start now to gain an edge in security validation and prove your commitment to digital trust.
Frequently Asked Questions
What is security attestation?
Security attestation is a process for verifying and validating the integrity and security posture of digital systems. It involves independent experts confirming that specific security standards and compliance requirements are met.
Why is security attestation important for organizations?
Security attestation helps organizations identify vulnerabilities, ensure compliance with regulations, and build trust among stakeholders. It transforms cybersecurity from a reactive measure into a proactive strategy for managing risks.
How does the security attestation process work?
The security attestation process typically involves technical verification, documentation review, and evidence collection. It uses cryptographic techniques to create verifiable proofs of system integrity and security.
What role do Trusted Execution Environments (TEEs) play in security attestation?
TEEs create isolated computing spaces that protect sensitive data and ensure that computational processes remain confidential. They provide a secure foundation for generating evidence of system integrity and preventing unauthorized access.
