SOC 2 compliance is making big waves in how companies prove they care about data protection. Over trillions of dollars are at risk every year from global cybercrime according to recent research. Most people expect the biggest hurdle is just passing a security test, but the real story lies in what that security badge truly means for your trust and business growth.
Table of Contents
- Defining Soc 2 Type 1 And Type 2: What They Are
- The Importance Of Soc 2 Type 1 And Type 2 For Businesses
- How Soc 2 Type 1 And Type 2 Assess Controls And Risks
- Key Differences Between Soc 2 Type 1 And Type 2 Reports
- Real-World Applications And Benefits Of Soc 2 Assessments
Quick Summary
| Takeaway | Explanation |
|---|---|
| Understanding SOC 2 Types 1 and 2 is crucial | SOC 2 Type 1 offers a snapshot of control design, while Type 2 evaluates ongoing effectiveness over time. |
| SOC 2 compliance builds customer trust | Achieving SOC 2 certification demonstrates commitment to data security, enhancing credibility in the eyes of clients. |
| SOC 2 audits offer strategic business advantages | These assessments improve competitive positioning, identify risks, and foster confidence from partners and vendors. |
| Type 1 is a preliminary evaluation | It assesses design and implementation of controls, providing a snapshot rather than a comprehensive review. |
| Type 2 audits assess sustained practices | They evaluate control effectiveness over 6-12 months, ensuring robust operational security measures are in place. |
Defining SOC 2 Type 1 and Type 2: What They Are
SOC 2 compliance represents a critical framework for organizations demonstrating their commitment to data security and privacy. These audit reports, developed by the American Institute of Certified Public Accountants (AICPA), evaluate how companies manage customer data according to specific trust service principles. Learn more about SOC 2 AICPA compliance to understand the foundational requirements.
Understanding the Basic Framework
SOC 2 audits assess an organization's systems and processes across five primary trust service criteria: security, availability, processing integrity, confidentiality, and privacy. These audits come in two primary variations: Type 1 and Type 2, each serving distinct purposes in validating an organization's control environment.
Key Differences Between Type 1 and Type 2
The primary distinction between SOC 2 Type 1 and Type 2 lies in their depth and duration of assessment:
-
SOC 2 Type 1: A snapshot evaluation that examines an organization's systems and controls at a specific point in time. This audit focuses on the design and implementation of security controls, providing a preliminary assessment of an organization's compliance readiness.
-
SOC 2 Type 2: A more comprehensive audit that evaluates the operational effectiveness of those controls over a designated period, typically six to twelve months. This report offers a more robust and dynamic view of an organization's ongoing security practices.
Both audit types are crucial for organizations seeking to demonstrate their commitment to protecting sensitive data and maintaining robust security protocols.
To better understand the areas evaluated during SOC 2 audits, the table below summarizes the five trust service criteria and the focus of each criterion within the SOC 2 compliance framework.
| Trust Service Criteria | Focus Area Description |
|---|---|
| Security | Protecting systems against unauthorized access and threats |
| Availability | Ensuring systems are operational and accessible as agreed |
| Processing Integrity | Delivering systems that process data accurately, completely, and timely |
| Confidentiality | Preserving information designated as confidential |
| Privacy | Collecting, using, retaining, and disclosing personal information appropriately |
| Gartner's research highlights that organizations implementing comprehensive SOC 2 compliance frameworks experience significant improvements in their overall security posture and customer trust. |
By understanding the nuances between SOC 2 Type 1 and Type 2, businesses can strategically approach their compliance efforts, ensuring they not only design strong security controls but also consistently implement and maintain them over time.
The Importance of SOC 2 Type 1 and Type 2 for Businesses
In an era where data breaches and cybersecurity threats are increasingly prevalent, SOC 2 Type 1 and Type 2 audits have become essential tools for businesses to demonstrate their commitment to robust security practices. Our comprehensive security questionnaire automation guide provides deeper insights into compliance strategies.
Building Customer Trust and Credibility
Businesses today operate in a landscape where customers are increasingly vigilant about data protection. SOC 2 compliance serves as a powerful testament to an organization's dedication to maintaining stringent security standards. By successfully completing these audits, companies can differentiate themselves from competitors and provide tangible proof of their commitment to protecting sensitive information.
Strategic Business Advantages
The benefits of SOC 2 Type 1 and Type 2 audits extend far beyond mere regulatory compliance. These assessments offer significant strategic advantages for organizations:
-
Enhanced Competitive Positioning: Companies with SOC 2 certification stand out in markets where data security is paramount, particularly in technology, finance, and healthcare sectors.
-
Risk Mitigation: Comprehensive audits help identify potential vulnerabilities in security infrastructure before they can be exploited by malicious actors.
-
Vendor and Partner Confidence: Many organizations require SOC 2 compliance as a prerequisite for business partnerships, making these audits crucial for expanding business opportunities.
Long-Term Organizational Resilience
Cybersecurity Ventures research predicts that global cybercrime damages could reach trillions of dollars annually. SOC 2 audits provide a structured approach to continually assess and improve an organization's security posture. Type 1 audits offer an initial snapshot of control design, while Type 2 audits provide ongoing validation of control effectiveness.
By investing in these comprehensive audit processes, businesses not only protect their digital assets but also demonstrate a proactive approach to cybersecurity that can significantly enhance their reputation and operational credibility.

How SOC 2 Type 1 and Type 2 Assess Controls and Risks
Effective risk assessment and control validation are fundamental to maintaining robust cybersecurity frameworks. SOC 2 Type 1 and Type 2 audits provide organizations with structured methodologies to comprehensively evaluate their security infrastructure. Learn about security questionnaire best practices to complement these assessment strategies.
Detailed Control Assessment Mechanisms
SOC 2 audits meticulously examine an organization's control environment across five critical trust service principles: security, availability, processing integrity, confidentiality, and privacy. These assessments go beyond surface level evaluations, diving deep into the architectural and operational aspects of an organization's security mechanisms.
Risk Identification and Mitigation Strategies
The audit process involves a comprehensive evaluation of potential vulnerabilities and risks within an organization's systems. Key aspects of this risk assessment include:
-
Technical Control Evaluation: Detailed analysis of security configurations, access management protocols, and system architecture
-
Operational Process Review: Examination of how security policies are implemented and maintained in real world scenarios
-
Documentation and Evidence Validation: Rigorous verification of security documentation, incident response plans, and control implementation records
NIST's cybersecurity framework emphasizes the importance of continuous monitoring and assessment, which aligns perfectly with the SOC 2 audit approach. Type 1 audits provide an initial snapshot of control design, while Type 2 audits offer a more dynamic view by assessing the operational effectiveness of these controls over an extended period.
By systematically identifying potential security gaps and providing actionable insights, SOC 2 Type 1 and Type 2 audits enable organizations to develop proactive risk management strategies that protect sensitive data and maintain operational resilience.
Key Differences Between SOC 2 Type 1 and Type 2 Reports
Navigating the nuanced landscape of SOC 2 compliance requires understanding the distinct characteristics of Type 1 and Type 2 reports. These audit reports serve different purposes and provide varying levels of insight into an organization's security controls. Learn more about security assessment strategies to enhance your compliance approach.
Temporal and Depth Variations
The fundamental distinction between SOC 2 Type 1 and Type 2 reports lies in their scope of assessment and duration of evaluation.
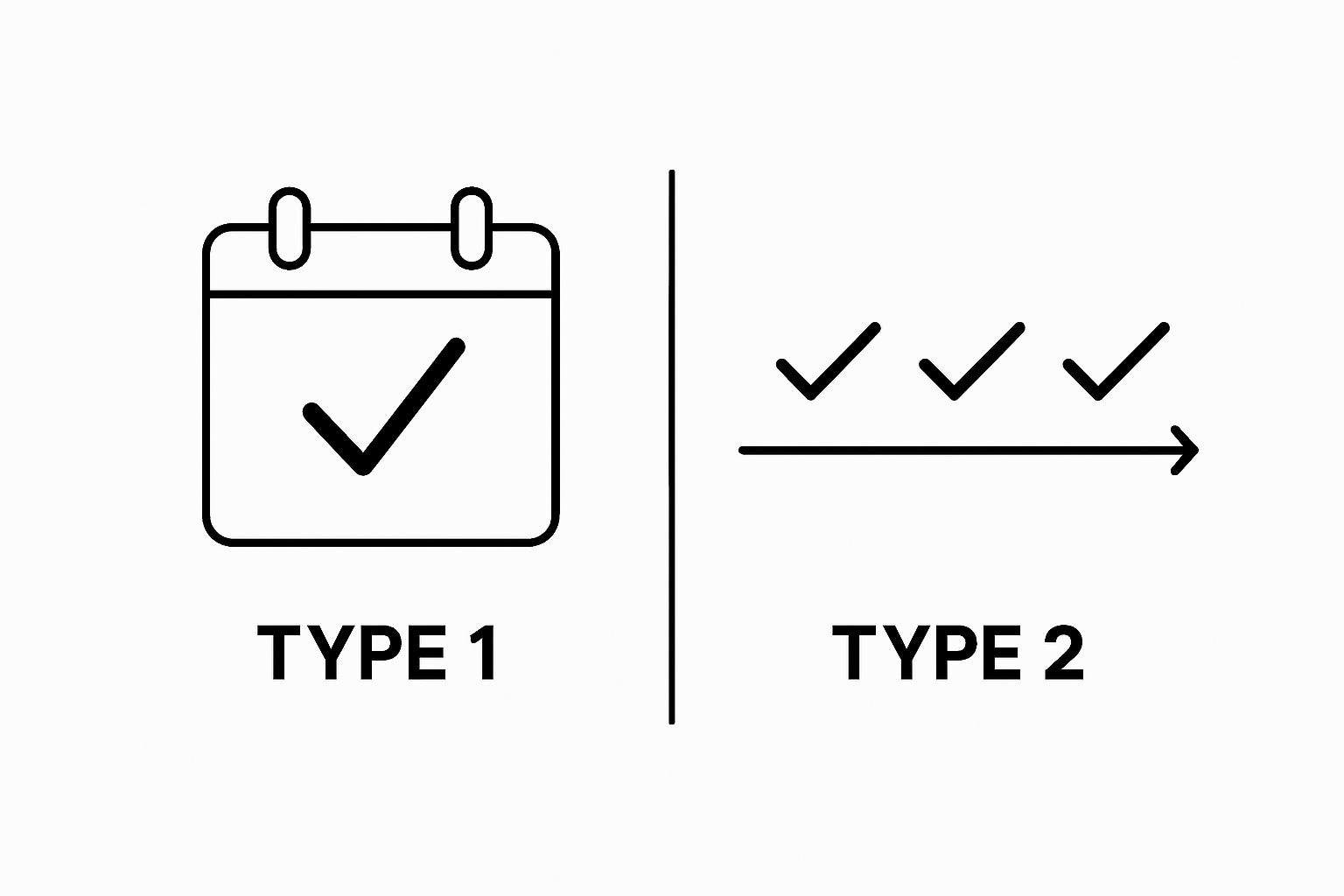 Type 1 reports capture a snapshot of an organization's control design at a specific moment, while Type 2 reports offer a more comprehensive view by assessing the operational effectiveness of these controls over an extended period.
Type 1 reports capture a snapshot of an organization's control design at a specific moment, while Type 2 reports offer a more comprehensive view by assessing the operational effectiveness of these controls over an extended period.
Comprehensive Comparative Analysis
Key differences between SOC 2 Type 1 and Type 2 reports include:
-
Time Frame of Assessment:
- Type 1: Point-in-time evaluation (typically one day)
- Type 2: Continuous assessment over 6-12 months
-
Depth of Evaluation:
- Type 1: Focuses on design and documentation of controls
- Type 2: Examines actual implementation and operational effectiveness of controls
-
Credibility and Stakeholder Confidence:
- Type 1: Preliminary indication of control readiness
- Type 2: More robust proof of sustained security practices
Deloitte's cybersecurity research underscores the importance of continuous monitoring, which aligns closely with the Type 2 report's comprehensive approach. While Type 1 reports provide an initial assessment of an organization's control design, Type 2 reports offer a more dynamic and credible representation of ongoing security practices.
Understanding these distinctions enables organizations to strategically approach their SOC 2 compliance journey, selecting the most appropriate audit type based on their specific business needs and stakeholder requirements.
To clarify the main distinctions between SOC 2 Type 1 and Type 2 reports, the following table compares their scope, assessment approach, and implications for businesses.
| Feature / Aspect | SOC 2 Type 1 | SOC 2 Type 2 |
|---|---|---|
| Time Frame | Point-in-time (single date) | Over a period (typically 6–12 months) |
| Focus | Design and implementation of controls | Operational effectiveness of controls in practice |
| Depth of Review | Snapshot assessment | Continuous evaluation across timeframe |
| Stakeholder Confidence | Preliminary indication of compliance | Stronger, evidence-based assurance |
| Typical Use Case | Initial certification, readiness check | Ongoing compliance, demonstrating maturity |
| Business Impact | Foundation for trust | Enhanced trust and competitive differentiation |
Real-World Applications and Benefits of SOC 2 Assessments
SOC 2 assessments have become critical tools for organizations seeking to demonstrate robust security practices and build trust with stakeholders. Our comprehensive SIG assessment guide provides additional context for understanding comprehensive security evaluations.
Industry-Specific Implementation Strategies
Different industries leverage SOC 2 assessments uniquely based on their specific operational requirements. Technology companies often use these audits to validate cloud service security, while financial institutions rely on them to demonstrate compliance with stringent data protection regulations. Healthcare organizations utilize SOC 2 reports to ensure patient data privacy and secure information management systems.
Strategic Business Advantages
The practical applications of SOC 2 assessments extend far beyond simple compliance checkboxes. Key strategic benefits include:
-
Competitive Differentiation: Organizations with SOC 2 certification can distinguish themselves in markets where data security is paramount
-
Risk Management: Comprehensive audits help identify and mitigate potential security vulnerabilities before they become critical issues
-
Enhanced Customer Confidence: Demonstrating rigorous security practices builds trust and credibility with clients and partners
NIST's cybersecurity framework emphasizes the importance of continuous monitoring and assessment, which aligns perfectly with the comprehensive nature of SOC 2 audits. By providing a structured approach to evaluating security controls, these assessments enable organizations to proactively manage their cybersecurity risks and maintain a robust defense against potential threats.
Ultimately, SOC 2 assessments serve as powerful tools for organizations to validate their commitment to protecting sensitive data, maintaining operational integrity, and building long-term stakeholder trust in an increasingly complex digital landscape.
Ready to Accelerate Your SOC 2 Journey?
Struggling to keep up with the demands of SOC 2 Type 1 and Type 2 audits? If your organization faces overwhelming security questionnaires, documentation headaches, or the stress of proving robust control practices, you are not alone. The article made it clear that success today means not just designing strong controls, but efficiently demonstrating them over time. Skypher removes the pain from compliance by transforming how teams manage, answer, and organize security reviews with unparalleled speed and accuracy.

Discover how our AI Questionnaire Automation Tool—with rapid uploads, smart integrations, and real-time collaboration—can help you successfully handle even the most complex audit requirements. Visit Skypher’s platform now to see how you can streamline your next SOC 2 assessment, impress partners, and free your team for what matters most. Focus on getting audit-ready with less stress and more confidence, starting today.
Frequently Asked Questions
What is SOC 2 Type 1?
SOC 2 Type 1 is an audit that evaluates an organization’s systems and controls at a specific point in time, focusing on the design and implementation of security controls.
How does SOC 2 Type 2 differ from SOC 2 Type 1?
SOC 2 Type 2 is a comprehensive audit that assesses the operational effectiveness of an organization’s controls over a period of time, typically 6 to 12 months, providing a more thorough evaluation.
Why are SOC 2 audits important for businesses?
SOC 2 audits are crucial for businesses to demonstrate their commitment to data security and privacy, build customer trust, enhance competitive positioning, and mitigate potential risks.
What are the key trust service criteria evaluated in SOC 2 audits?
The key trust service criteria evaluated in SOC 2 audits include security, availability, processing integrity, confidentiality, and privacy.
