SOC compliance sets the gold standard for data protection, and more companies are chasing it every year. Some might think these audits are just paperwork, but one fact stands out: SOC 2 reports have become the top priority for technology and cloud providers who handle sensitive data every single day. The real surprise is that SOC compliance is not just about passing an audit. It is transforming how organizations build credibility, protect their reputation, and win over customers who demand security above all else.
Table of Contents
- What Is Soc Compliance?
- The Importance Of Being Soc Compliant
- How Soc Compliance Works In Practice
- Key Concepts Behind Soc Compliance
- Real-World Applications Of Soc Compliance
Quick Summary
| Takeaway | Explanation |
|---|---|
| SOC compliance ensures data security | It demonstrates a commitment to protecting sensitive customer information through rigorous standards and audits. |
| Different SOC reports serve unique purposes | SOC 1, SOC 2, and SOC 3 reports evaluate financial controls, data security, and provide overviews, respectively. |
| SOC compliance builds organizational credibility | Achieving compliance establishes trust and transparency with clients and stakeholders, verifying your organization's commitment to security. |
| Continuous improvement is essential for SOC compliance | Organizations must regularly update their security frameworks to adapt to emerging threats and maintain compliance. |
| Vendor management relies on SOC compliance | Companies increasingly demand SOC reports from partners to assess their security capabilities and mitigate risks. |
What is SOC Compliance?
SOC compliance represents a critical framework for organizations to demonstrate their commitment to data security, privacy, and operational integrity. At its core, SOC (Service Organization Control) compliance is a rigorous set of standards developed by the American Institute of Certified Public Accountants (AICPA) that evaluates how companies manage and protect customer data.
Understanding SOC Compliance Framework
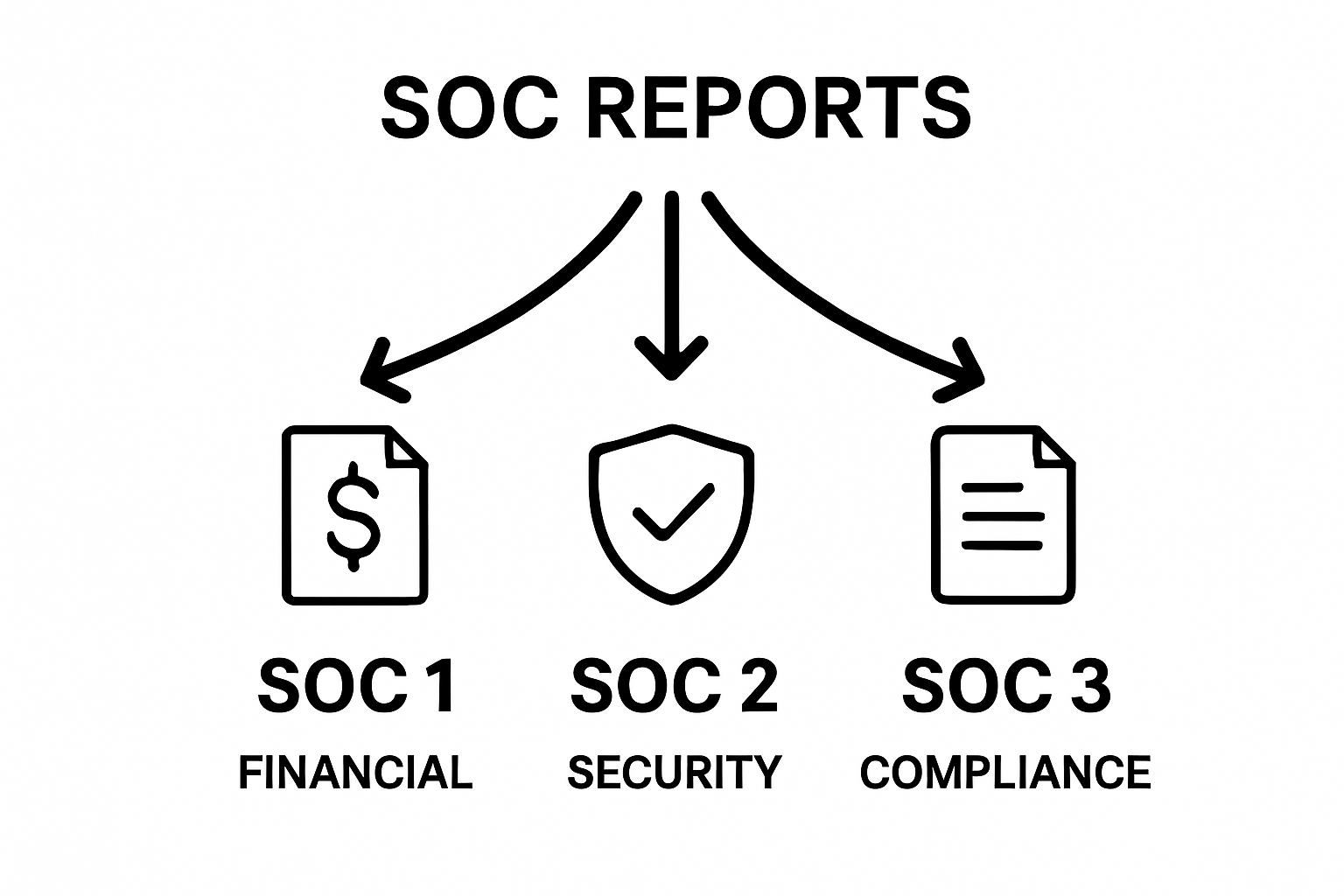
The SOC compliance framework encompasses multiple types of reports designed to assess different aspects of an organization's operational controls. According to AICPA standards, there are three primary SOC report types:
- SOC 1: Focuses on financial reporting controls
- SOC 2: Evaluates security, availability, processing integrity, confidentiality, and privacy controls
- SOC 3: Provides a general overview of an organization's security controls
Each report type serves a unique purpose in helping organizations validate their internal processes and provide transparency to stakeholders.
To help clarify the differences between SOC report types, the table below summarizes each type's focus and intended audience.
| SOC Report Type | Main Focus | Intended Audience |
|---|---|---|
| SOC 1 | Financial reporting controls | User entities and auditors |
| SOC 2 | Security, availability, processing integrity, confidentiality, and privacy controls | Business partners and clients |
| SOC 3 | General overview of security controls | Public and prospective clients |
 SOC 2 reports, in particular, have become increasingly important in the technology and cloud services sectors, where data protection is paramount.
SOC 2 reports, in particular, have become increasingly important in the technology and cloud services sectors, where data protection is paramount.
Why SOC Compliance Matters
SOC compliance is not just a checkbox exercise but a comprehensive approach to risk management. For businesses operating in sensitive industries like finance, healthcare, and technology, demonstrating robust security controls is essential. By undergoing SOC compliance audits, organizations prove their commitment to:
- Protecting sensitive customer and client information
- Implementing robust cybersecurity measures
- Maintaining transparent and reliable operational processes
- Meeting industry-specific regulatory requirements
An independent third-party auditor conducts these assessments, providing an objective evaluation of an organization's control environment. The audit process involves detailed documentation review, interviews with key personnel, and thorough testing of implemented controls.
For technology companies and service providers, SOC compliance serves as a critical differentiator in a competitive market. It signals to potential clients that the organization takes data protection seriously and has implemented rigorous safeguards to prevent security breaches and maintain operational excellence.
The Importance of Being SOC Compliant
In an increasingly digital landscape, SOC compliance has transformed from a optional business practice to a critical requirement for organizations seeking to establish trust, protect sensitive information, and demonstrate operational excellence. According to cybersecurity experts, compliance is no longer just about meeting regulatory standards but about creating a comprehensive security framework that safeguards an organization's most valuable assets.
Building Organizational Credibility
SOC compliance serves as a powerful mechanism for organizations to establish credibility and transparency with clients, partners, and stakeholders. When a company undergoes rigorous SOC audits and receives certification, it sends a clear message about its commitment to:
- Maintaining robust security protocols
- Protecting sensitive customer data
- Implementing comprehensive risk management strategies
- Demonstrating operational integrity
These certifications act as a seal of approval, signaling to potential clients that the organization has undergone independent verification of its internal controls and security practices.
Risk Mitigation and Strategic Advantage
Beyond regulatory compliance, SOC certification provides significant strategic advantages. Companies that invest in comprehensive compliance frameworks can:
- Reduce potential financial losses from data breaches
- Minimize legal and reputational risks
- Differentiate themselves in competitive markets
- Streamline vendor and partnership negotiations
Moreover, the process of achieving SOC compliance forces organizations to critically evaluate and strengthen their internal systems. This continuous improvement approach helps identify potential vulnerabilities before they can be exploited by malicious actors.
In sectors like technology, finance, and healthcare, where data privacy and security are paramount, SOC compliance is not just a recommended practice but an essential component of responsible business operations. The comprehensive audit process ensures that organizations maintain high standards of control, providing peace of mind for both the business and its stakeholders.
How SOC Compliance Works in Practice
Achieving SOC compliance is a systematic and comprehensive process that requires organizations to demonstrate robust control mechanisms and commitment to data security. According to enterprise security frameworks, the practical implementation of SOC compliance involves strategic planning, meticulous documentation, and continuous monitoring.
Preparation and Initial Assessment
The SOC compliance journey begins with a thorough internal evaluation of existing systems and processes. Organizations must conduct a comprehensive risk assessment that identifies potential vulnerabilities and gaps in their current control environment. This initial phase involves:
- Mapping existing security protocols
- Identifying potential risk areas
- Documenting current operational procedures
- Establishing baseline security standards
Companies typically engage internal teams or external consultants to perform a comprehensive gap analysis, which provides a roadmap for achieving full compliance.
The Audit and Certification Process
Once an organization has prepared its internal systems, it undergoes a rigorous audit conducted by an independent certified public accountant. The audit process involves multiple critical steps:
- Detailed documentation review
- Interviews with key personnel
- Technical and procedural control testing
- Verification of security implementation
- Comprehensive reporting of findings
Auditors evaluate the effectiveness of an organization's controls, looking beyond mere technical configurations to understand the holistic approach to risk management and data protection.
Continuous Improvement and Maintenance
SOC compliance is not a one-time achievement but an ongoing commitment. Organizations must continuously update their security frameworks, adapt to emerging threats, and demonstrate consistent adherence to established standards. This requires regular internal audits, periodic reassessments, and a proactive approach to identifying and mitigating potential security risks.
By treating SOC compliance as a dynamic process of continuous improvement, organizations can create resilient security infrastructures that protect sensitive data and maintain stakeholder trust.
The table below provides an at-a-glance overview of the key steps involved in the SOC compliance process, from preparation through ongoing maintenance.
| SOC Compliance Phase | Description |
|---|---|
| Preparation and Assessment | Internal risk assessment, gap analysis, and documentation of current controls |
| Audit and Certification | Independent audit, interviews, control testing, and reporting conducted by a certified public accountant |
| Continuous Improvement | Regular updates, internal audits, reassessments, and adaptation to emerging threats |
Key Concepts Behind SOC Compliance
SOC compliance represents a sophisticated framework of principles and practices designed to ensure organizations maintain rigorous standards of data protection and operational integrity. According to cybersecurity governance frameworks, understanding the foundational concepts is crucial for implementing effective security controls.
Trust and Control Principles
At the heart of SOC compliance are fundamental trust and control principles that guide organizations in protecting sensitive information. These principles encompass several critical dimensions:
- Establishing clear accountability mechanisms
- Creating transparent operational processes
- Implementing robust risk management strategies
- Developing comprehensive security governance
Trust principles require organizations to demonstrate a consistent and verifiable approach to managing and protecting stakeholder information, moving beyond mere technical implementations to holistic organizational commitment.
Comprehensive Risk Management Framework
SOC compliance introduces a structured approach to understanding and mitigating organizational risks. Key risk management elements include:
- Systematic identification of potential vulnerabilities
- Quantitative and qualitative risk assessment techniques
- Development of mitigation strategies
- Continuous monitoring and adaptation of control mechanisms
This framework enables organizations to proactively address potential security challenges, transforming risk management from a reactive to a predictive discipline.
Organizational Governance and Accountability
Successful SOC compliance transcends technical controls, embedding accountability and governance at every organizational level. It requires leadership commitment, employee training, and a culture of security awareness. Organizations must develop clear policies, assign specific responsibilities, and create mechanisms for ongoing evaluation and improvement.
By integrating these key concepts, organizations can develop a robust, dynamic approach to information security that not only meets compliance requirements but also builds genuine trust with stakeholders.

Real-World Applications of SOC Compliance
SOC compliance has evolved from a theoretical framework to a practical necessity across multiple industries, providing organizations with a structured approach to managing cybersecurity risks and demonstrating operational excellence. According to enterprise security research, real-world applications of SOC compliance extend far beyond simple regulatory checkboxes.
Cloud Service and Technology Sectors
In the rapidly expanding digital ecosystem, cloud service providers and technology companies rely heavily on SOC compliance to build customer trust and differentiate themselves in competitive markets. Critical applications include:
- Validating data center security protocols
- Demonstrating robust infrastructure management
- Ensuring consistent performance and availability standards
- Protecting sensitive customer information
Technology organizations use SOC 2 reports specifically to showcase their commitment to comprehensive security practices, which has become a crucial decision-making factor for potential clients evaluating service providers.
Financial and Healthcare Environments
Highly regulated industries like finance and healthcare leverage SOC compliance as a critical risk management tool. Practical implementations involve:
- Protecting patient and financial records
- Establishing strict access control mechanisms
- Implementing comprehensive data privacy frameworks
- Creating audit trails for regulatory compliance
These sectors recognize that SOC compliance provides a standardized methodology for demonstrating adherence to complex regulatory requirements while maintaining the highest levels of data protection and operational integrity.
Vendor Risk Management
Modern businesses increasingly use SOC compliance as a key criteria in vendor selection and management processes. Organizations demand SOC reports from potential partners to:
- Assess third-party security capabilities
- Identify potential operational vulnerabilities
- Ensure alignment with internal security standards
- Mitigate potential supply chain risks
By requiring SOC compliance documentation, companies can make more informed decisions about their business relationships, reducing potential security and operational risks before they manifest.
Simplify SOC Compliance and Supercharge Your Security Questionnaire Process
Struggling to keep up with the demands of SOC compliance and the constant stream of security questionnaires? As highlighted in the article, maintaining operational excellence and protecting sensitive data takes more than just preparation—it requires efficient, transparent processes and the ability to demonstrate your commitment to the highest standards at every touchpoint. Manual questionnaire responses can drain your team’s time, risk errors, and delay sales, making the SOC compliance journey even more challenging.

Let Skypher help you take back control. Our platform automates and streamlines security questionnaire responses, transforming a major pain point into an opportunity to build trust with clients and auditors. By leveraging AI-driven automation, real-time collaboration features, and seamless integration with over 40 risk management platforms, you can cut response time, increase accuracy, and focus on strengthening your organization’s compliance framework. Experience how our security questionnaire automation tool accelerates workflows and supports continuous SOC readiness. Explore Skypher now and give your team the compliance advantage they deserve.
Frequently Asked Questions
What is SOC compliance?
SOC compliance refers to a framework established by the American Institute of Certified Public Accountants (AICPA) that evaluates how organizations manage and protect customer data, focusing on security, privacy, and operational integrity.
Why is SOC compliance important for organizations?
SOC compliance is crucial as it demonstrates a company's commitment to protecting sensitive customer information, implementing robust cybersecurity measures, and maintaining trustworthy operational processes. It is essential for businesses in regulated industries such as finance, healthcare, and technology.
What are the different types of SOC reports?
There are three primary types of SOC reports: SOC 1, which focuses on financial reporting controls; SOC 2, which evaluates security and privacy controls; and SOC 3, which provides a general overview of an organization's security controls.
How does the SOC compliance process work?
The SOC compliance process involves a thorough internal evaluation to assess existing security protocols, followed by a rigorous audit conducted by an independent third-party auditor. The process includes documentation reviews, interviewing key personnel, and ongoing maintenance to ensure adherence to security standards.
Recommended
- Smart Security Knowledge Base - Saasy - Webflow HTML Website Template
- The different formats & mistakes made when writing or answering security questionnaires
- Guides - Saasy - Webflow HTML Website Template
- The ever growing number of security questionnaires and what you and your company can do to face it
