Cyber threats are growing more complex every year and businesses need smarter ways to keep their data safe. Most people picture hackers hiding in basements or lone IT staff watching screens all night but the real muscle behind digital defense is surprising. A fully functional Security Operations Center can detect and respond to threats in real time around the clock often stopping attacks before they even start. The kicker is that SOCs do way more than just watch for trouble. Their strategic intelligence is changing the whole game of cybersecurity.
Table of Contents
- What Is Soc And Its Purpose In Cybersecurity?
- The Importance Of Defining Soc In A Business Context
- Key Components Of A Security Operations Center
- How Soc Functions: Processes And Technologies
- Real-World Applications And Challenges Of Soc Implementation
Quick Summary
| Takeaway | Explanation |
|---|---|
| SOC centers enhance cybersecurity resilience | A Security Operations Center centralizes monitoring and incident response to strengthen an organization’s overall security posture. |
| Continuous monitoring is critical | SOCs perform real-time tracking of network traffic and system logs to quickly identify potential security threats. |
| Define clear SOC objectives for success | Establishing specific goals aligns SOC efforts with business aims, ensuring effective risk management and compliance. |
| Invest in skilled personnel and technology | An effective SOC relies on expert analysts and advanced tools to manage and mitigate complex cyber threats. |
| Adopt adaptive security frameworks | Incorporating modern technologies like AI allows SOCs to anticipate threats and respond dynamically to evolving risks. |
What is SOC and Its Purpose in Cybersecurity?
A Security Operations Center (SOC) represents a centralized facility where cybersecurity professionals monitor, detect, analyze, and respond to digital security threats in real time. According to Capitol Technology University, a SOC is a dedicated team responsible for maintaining an organization's ongoing security posture through continuous monitoring and proactive incident management.
The Core Functions of a SOC
The primary mission of a SOC goes beyond simple monitoring. These specialized teams perform critical functions that protect an organization's digital infrastructure:
- Continuous Threat Monitoring: Tracking network traffic, system logs, and user activities to identify potential security incidents
- Incident Response: Quickly investigating and mitigating detected security threats to minimize potential damage
- Vulnerability Management: Identifying and addressing potential weaknesses in the organization's technology ecosystem
Strategic Security Intelligence
SOCs are not just reactive units but strategic intelligence centers. By aggregating data from multiple sources, they transform raw information into actionable security insights. EDUCAUSE highlights that these centers enable organizations to develop sophisticated defense mechanisms against evolving cyber threats.
Organizations can implement SOC capabilities through various models: in-house teams, outsourced services, or hybrid approaches. Each model offers unique advantages depending on the organization's size, complexity, and security requirements.
Below is a table comparing different SOC implementation models mentioned in the article, highlighting their respective advantages to help readers identify which approach best meets their organizational needs.
| SOC Implementation Model | Description | Key Advantages |
|---|---|---|
| In-house | An internal team and facility dedicated solely to the organization | Greater control, tailored security posture |
| Outsourced | Security services provided by an external vendor | Cost savings, access to specialized talent |
| Hybrid | Combines internal resources and external security service providers | Flexibility, scalability, balanced control |
The Importance of Defining SOC in a Business Context
Defining a Security Operations Center (SOC) is not merely a technical exercise but a strategic business imperative that directly impacts an organization's resilience and risk management capabilities. ISACA emphasizes that a well-defined SOC serves as a critical framework for understanding and mitigating cybersecurity risks.
Strategic Alignment and Business Objectives
A precisely defined SOC transforms cybersecurity from a technical function into a strategic business asset.
 Organizations must articulate clear objectives that align with their broader business goals, ensuring that the SOC becomes more than just a monitoring center. Key strategic considerations include:
Organizations must articulate clear objectives that align with their broader business goals, ensuring that the SOC becomes more than just a monitoring center. Key strategic considerations include:
- Risk Management: Proactively identifying and mitigating potential security vulnerabilities
- Compliance Requirements: Ensuring adherence to industry-specific regulatory standards
- Business Continuity: Minimizing potential disruptions from cyber incidents
Operational Effectiveness and Resource Optimization
Clear SOC definition enables organizations to optimize their cybersecurity resources effectively. By establishing precise roles, responsibilities, and operational parameters, businesses can create a more efficient and targeted security approach. This definition helps in:
- Determining appropriate staffing and skill requirements
- Establishing clear escalation and incident response protocols
- Implementing cost-effective security monitoring strategies
Moreover, a well-defined SOC provides transparency and builds stakeholder confidence. Learn more about advanced security questionnaire strategies to enhance your organization's comprehensive security framework and demonstrate a mature, proactive approach to cybersecurity management.
Key Components of a Security Operations Center
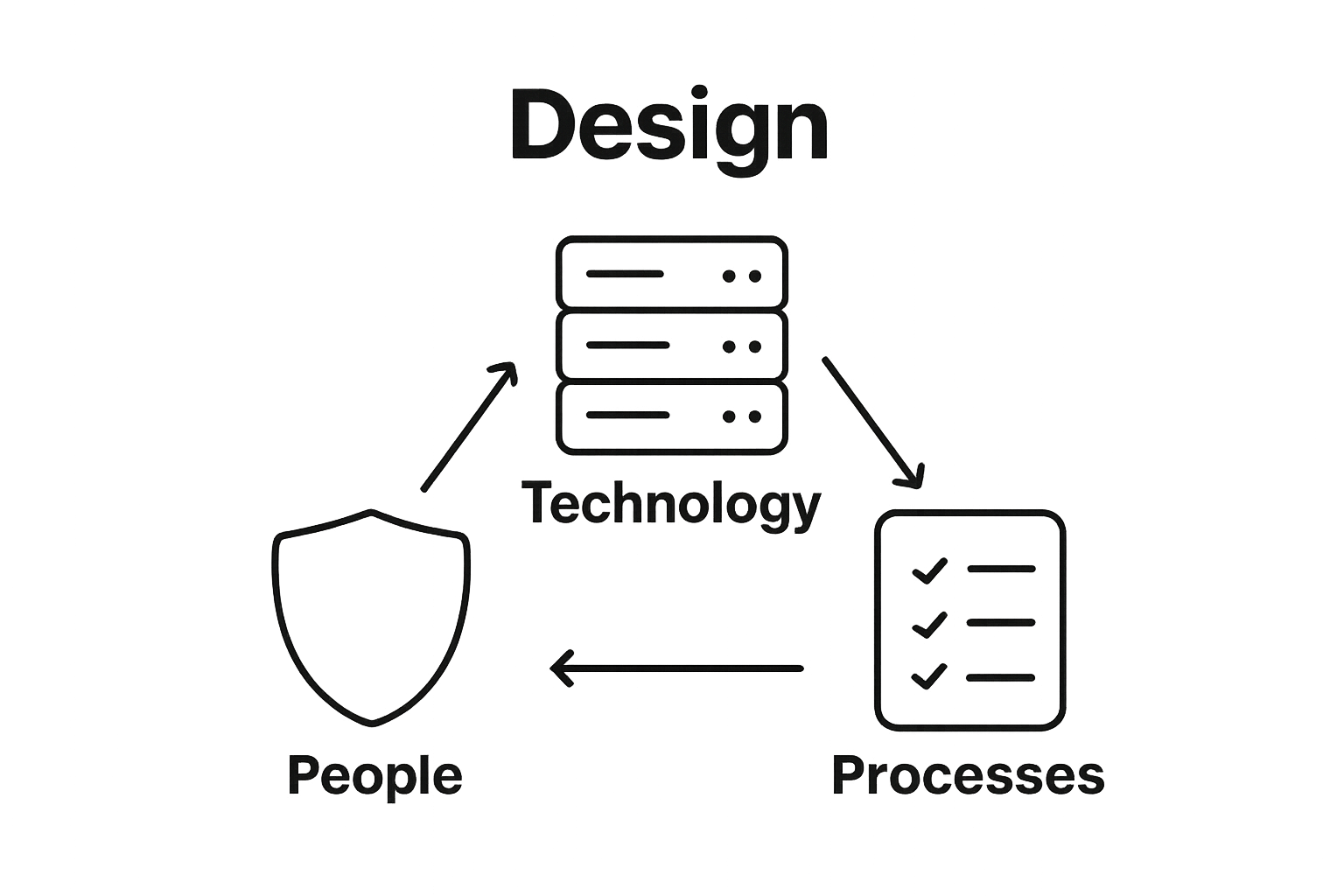
A Security Operations Center (SOC) is a complex ecosystem composed of interconnected elements that work synergistically to protect an organization's digital infrastructure. California Institute of Technology highlights that these components are designed to create a comprehensive and adaptive cybersecurity defense mechanism.
People and Expertise
The human element forms the core of any effective SOC. Skilled professionals with specialized roles drive the center's operational capabilities:
The following table organizes the key human roles within a Security Operations Center (SOC) and summarizes their primary responsibilities to clarify the structure and expertise required for effective SOC operation.
| SOC Role | Primary Responsibility |
|---|---|
| Security Analyst | Monitors network traffic, investigates threats |
| Incident Responder | Develops and executes rapid response strategies |
| Threat Hunter | Proactively searches for hidden vulnerabilities |
| SOC Manager | Oversees SOC operations and strategic planning |
- Security Analysts: Monitoring network traffic and investigating potential threats
- Incident Responders: Developing and executing rapid response strategies
- Threat Hunters: Proactively searching for hidden vulnerabilities
- SOC Managers: Overseeing operations and strategic planning
Technology and Infrastructure
Cutting-edge technological infrastructure enables SOC teams to detect, analyze, and mitigate security risks. Critical technological components include:
- Advanced security information and event management (SIEM) systems
- Intrusion detection and prevention systems
- Threat intelligence platforms
- Endpoint detection and response (EDR) tools
Processes and Protocols
Structured processes ensure systematic and consistent security management.
VIDEO:video_content] Well-defined protocols help organizations respond effectively to emerging threats. [Learn more about advanced security questionnaire strategies to complement your SOC's comprehensive security framework. Key procedural elements include incident response workflows, regular security assessments, and continuous training programs that adapt to evolving cybersecurity landscapes.
How SOC Functions: Processes and Technologies
Security Operations Centers (SOCs) employ a sophisticated approach to cybersecurity that combines advanced technological capabilities with strategic human expertise. Department of Homeland Security emphasizes that SOC functionality revolves around continuous monitoring, rapid detection, and proactive threat management.
Continuous Monitoring and Threat Detection
The core function of a SOC involves comprehensive digital surveillance across an organization's entire technological ecosystem. This process includes:
- Network Traffic Analysis: Examining data flows for suspicious patterns
- Log Management: Collecting and analyzing system logs from multiple sources
- Real-time Threat Intelligence: Aggregating global threat information to identify potential risks
Incident Response and Mitigation Technologies
When potential security threats are identified, SOCs deploy sophisticated response mechanisms designed for swift and precise intervention. Critical technological tools include:
- Security Information and Event Management (SIEM) systems
- Automated threat correlation platforms
- Incident tracking and management software
- Forensic investigation tools
Adaptive Security Frameworks
Modern SOCs go beyond traditional reactive approaches, implementing adaptive security frameworks that anticipate and prevent potential cyber incidents. Learn more about advanced security questionnaire strategies to understand how proactive security measures can transform organizational resilience. These frameworks integrate machine learning, predictive analytics, and continuous risk assessment to create dynamic defense mechanisms that evolve alongside emerging technological challenges.
Real-World Applications and Challenges of SOC Implementation
Security Operations Centers (SOCs) represent critical infrastructure for organizations seeking comprehensive cybersecurity protection. NIST Special Publication emphasizes the complex landscape of implementing robust security monitoring and response capabilities across diverse technological environments.
Industry-Specific SOC Applications
Different sectors leverage SOC implementations to address unique cybersecurity challenges:
- Financial Services: Protecting sensitive transaction data and preventing fraud
- Healthcare: Safeguarding patient information and maintaining regulatory compliance
- Government: Defending critical infrastructure against sophisticated cyber threats
- Technology: Monitoring complex, distributed network architectures
Implementation Challenges and Strategic Considerations
Organizations frequently encounter multifaceted obstacles when establishing SOC capabilities:
- Recruiting and retaining specialized cybersecurity talent
- Managing sophisticated technological integrations
- Balancing comprehensive monitoring with operational efficiency
- Maintaining cost-effectiveness of security investments
Emerging Technologies and Future Readiness
Successful SOC implementation requires continuous adaptation to technological evolution. Modern organizations must embrace flexible frameworks that integrate advanced technologies like artificial intelligence and machine learning. Learn more about advanced security questionnaire strategies to understand how proactive approaches can transform organizational cybersecurity resilience. The future of SOC lies in predictive analytics, automated threat detection, and seamless cross-platform security management.
Transform SOC Insights into Action with Skypher
Many organizations struggle to make their Security Operations Center (SOC) more than just a reactive command post. Without seamless information sharing and real-time collaboration, teams often face delays and miss critical threats. You read how a well-defined SOC requires continuous monitoring, smart automation, and operational clarity. But dealing with endless security questionnaires often slows you down and takes energy away from what matters most: protecting your organization.

Imagine delivering faster security reviews and boosting trust in every stakeholder touchpoint. With Skypher, you maximize your SOC’s efficiency by automating security questionnaires using AI that understands your unique environment. Instantly parse any file type, sync with OneTrust or ServiceNow, and empower every expert on your team to answer even the largest reviews in minutes. Discover how our AI Questionnaire Automation Tool brings accuracy, speed, and scalability to your security operations, so you can turn SOC recommendations into action and win more business opportunities now. Ready to reduce your review time and prove your security maturity? Visit Skypher to start redefining your cyber resilience.
Frequently Asked Questions
What is a Security Operations Center (SOC)?
A Security Operations Center (SOC) is a centralized facility where cybersecurity professionals monitor, detect, analyze, and respond to digital security threats in real time to maintain an organization’s security posture.
What are the main functions of a SOC?
The main functions of a SOC include continuous threat monitoring, incident response to mitigate detected threats, and vulnerability management to address weaknesses in an organization’s technology infrastructure.
How does a SOC contribute to an organization’s risk management?
A SOC helps in risk management by proactively identifying and mitigating potential security vulnerabilities, ensuring compliance with regulatory standards, and supporting business continuity by minimizing disruptions from cyber incidents.
What technologies are essential for an effective SOC?
Essential technologies for an effective SOC include advanced Security Information and Event Management (SIEM) systems, intrusion detection and prevention systems, threat intelligence platforms, and endpoint detection and response (EDR) tools.
Recommended
- Understanding SOC 2 AICPA: Your Guide to Compliance
- Smart Security Knowledge Base - Saasy - Webflow HTML Website Template
- The different formats & mistakes made when writing or answering security questionnaires
- The ever growing number of security questionnaires and what you and your company can do to face it
