SOC II compliance is changing how tech companies handle your data. Over 85% of enterprise buyers now require security certification before signing with a new vendor. That sounds like a number that should slow things down, right? But the real surprise is SOC II actually speeds up sales and builds trust, making it one of the fastest ways for businesses to stand out and win new clients.
Table of Contents
- What Is Soc II Compliance And Its Purpose?
- Why Soc II Compliance Matters For B2B Companies
- Key Principles And Components Of Soc II Compliance
- How Soc II Compliance Works In Practice
- Real-World Impact Of Soc II Compliance On Business Operations
Quick Summary
| Takeaway | Explanation |
|---|---|
| SOC II compliance is essential for data protection | This framework indicates an organization's commitment to safeguarding sensitive customer information through effective security practices. |
| Certification enhances customer trust and sales | SOC II compliance serves as third-party validation, attracting clients and accelerating the sales process in B2B environments. |
| Continuous evaluation is crucial for compliance | Achieving SOC II is an ongoing process that requires regular assessments and improvements to maintain high security standards. |
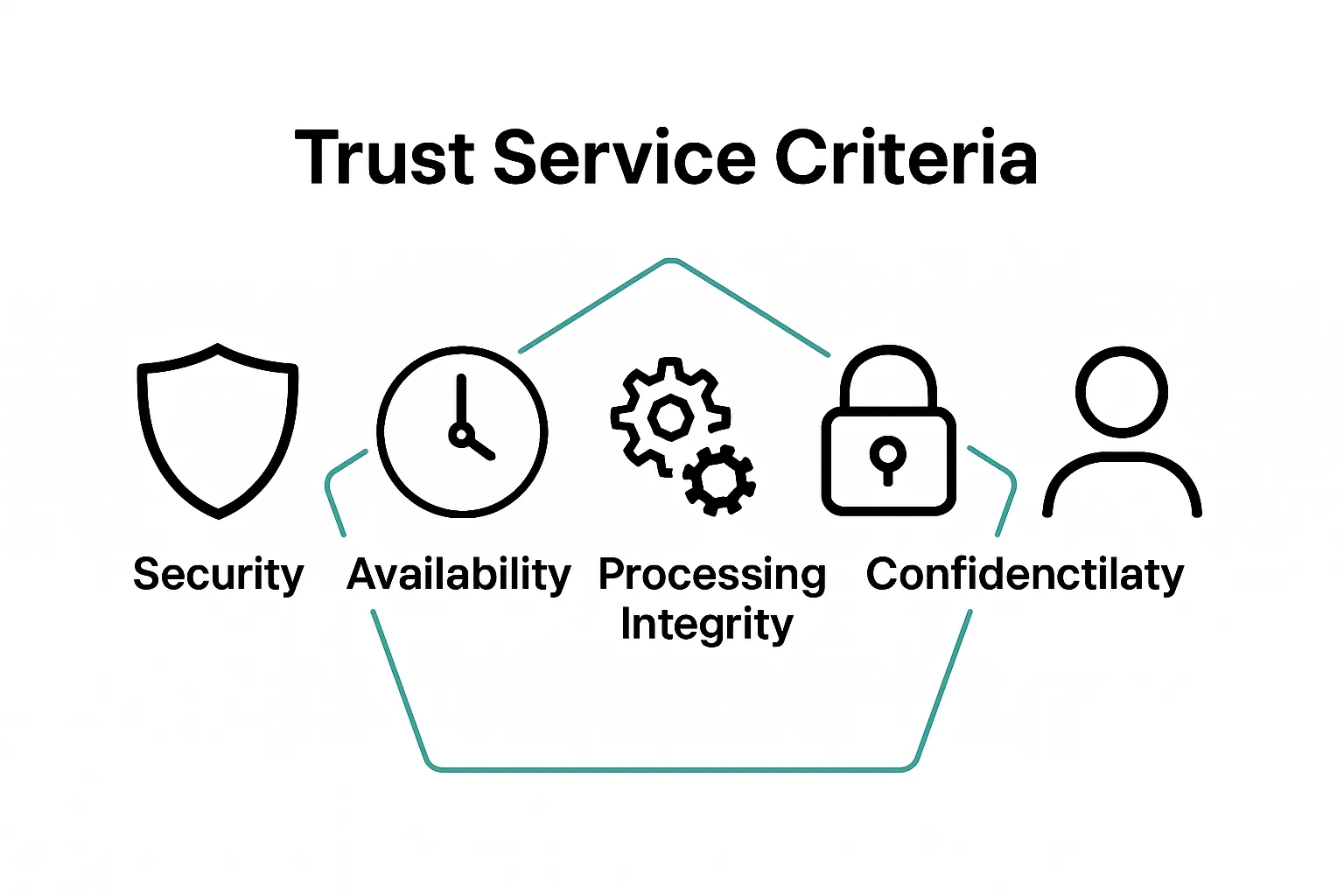
| Five trust service criteria guide SOC II assessments | Organizations are evaluated based on security, availability, processing integrity, confidentiality, and privacy, forming a comprehensive security framework. |
| Type II audit offers deeper insights | This audit evaluates the operational effectiveness of security controls over time, providing a more thorough assessment compared to Type I. |
What is SOC II Compliance and Its Purpose?
SOC II compliance represents a critical framework for organizations managing customer data, particularly in cloud computing and technology services. Developed by the American Institute of Certified Public Accountants (AICPA), SOC II focuses on evaluating how companies protect sensitive information through robust security controls and risk management practices.
Understanding the Core Framework
At its foundation, SOC II compliance is a voluntary audit process that assesses an organization's systems and processes against five key trust service criteria: security, availability, processing integrity, confidentiality, and privacy. Unlike other compliance standards that mandate specific technical implementations, SOC II provides a flexible framework allowing organizations to design controls that align with their unique operational environment.
Learn more about SOC 2 AICPA compliance standards to gain deeper insights into this comprehensive evaluation process.
Why SOC II Matters for Modern Businesses
Businesses across technology, finance, healthcare, and cloud service sectors increasingly recognize SOC II compliance as a critical trust signal for potential customers and partners. The certification demonstrates an organization's commitment to:
- Protecting customer data from unauthorized access
- Maintaining robust security infrastructure
- Implementing consistent risk management protocols
- Ensuring transparent and accountable data handling practices
According to Gartner Research, over 85% of enterprise buyers now require some form of security certification before engaging with a new technology vendor, making SOC II an essential credential in today's competitive marketplace.
By systematically evaluating an organization's control environments, SOC II goes beyond traditional security audits. It provides a comprehensive assessment that builds customer confidence, reduces potential security risks, and establishes a framework for continuous improvement in data protection strategies.
Why SOC II Compliance Matters for B2B Companies
In the competitive landscape of B2B technology and services, SOC II compliance has transformed from an optional credential to a fundamental business requirement. Companies seeking to establish trust, demonstrate security commitment, and differentiate themselves in complex enterprise markets now view SOC II as a critical strategic asset.
Building Customer Trust and Credibility
B2B organizations recognize that potential clients demand robust security assurances before engaging in business relationships. SOC II compliance serves as an independent, third-party validation of an organization's security practices. This certification signals to potential customers that a company has implemented rigorous controls to protect sensitive data, manage risks, and maintain operational integrity.
Learn more about GRC cyber security strategies to understand how comprehensive compliance frameworks enhance organizational resilience.
Competitive Advantage in Enterprise Sales
Enterprise customers are increasingly sophisticated in their vendor selection processes. They conduct thorough due diligence to minimize potential security risks. SOC II compliance provides tangible benefits for B2B companies by:
- Accelerating sales cycles through pre-established trust mechanisms
- Reducing potential security objections during procurement
- Demonstrating a proactive approach to data protection
- Differentiating from competitors lacking similar certifications
According to Cybersecurity Ventures, companies with comprehensive security certifications are 67% more likely to win enterprise contracts compared to non-certified competitors.
Risk Mitigation and Strategic Positioning
Beyond immediate sales advantages, SOC II compliance represents a strategic risk management approach. By systematically evaluating and improving security controls, B2B companies can identify potential vulnerabilities, strengthen their technological infrastructure, and create a culture of continuous security improvement. This proactive stance not only protects against potential breaches but also demonstrates organizational maturity to stakeholders, investors, and potential business partners.
Key Principles and Components of SOC II Compliance
SOC II compliance represents a sophisticated framework that goes far beyond traditional security assessments. It provides a comprehensive approach to evaluating an organization's operational controls and risk management strategies through a nuanced, principle-driven methodology.
The Five Trust Service Criteria
At the heart of SOC II compliance are five critical trust service criteria that form the foundational evaluation framework. These criteria provide a holistic assessment of an organization's ability to protect and manage sensitive information:
The following table summarizes the five Trust Service Criteria at the core of SOC II compliance, providing clear definitions for each principle.
| Trust Service Criteria | Description |
|---|---|
| Security | Protecting system resources against unauthorized access |
| Availability | Ensuring systems are accessible and operational as committed |
| Processing Integrity | Verifying data processing completeness, accuracy, and timeliness |
| Confidentiality | Safeguarding designated confidential information |
| Privacy | Managing personal information collection, use, retention, and disposal |
- Security: Protecting system resources against unauthorized access
- Availability: Ensuring systems are accessible and operational as committed
- Processing Integrity: Verifying data processing completeness, accuracy, and timeliness
- Confidentiality: Safeguarding designated confidential information
- Privacy: Managing personal information collection, use, retention, and disposal
Our guide to SOC 1 compliance offers additional context on how different compliance frameworks intersect and complement each other.
Audit Types and Reporting Structures
SOC II compliance involves two primary audit types that organizations can pursue: Type I and Type II. These audits provide different levels of assurance and depth of evaluation
This table compares the two primary SOC II audit types to help clarify their purpose and scope in the compliance process.
| Audit Type | Evaluation Focus | Timeframe | Depth of Assurance |
|---|---|---|---|
| Type I | Design of control systems | Single point in time | Basic (design effectiveness) |
| Type II | Design and operational effectiveness of controls | 6-12 months | Comprehensive (ongoing effectiveness) |
:
- Type I Audit: Assesses the design of control systems at a specific point in time
- Type II Audit: Evaluates both the design and operational effectiveness of controls over a designated period, typically 6-12 months
According to AICPA standards, the Type II audit provides more comprehensive insights into an organization's long-term security practices and control effectiveness.
Implementation and Ongoing Compliance
Successful SOC II compliance is not a one-time achievement but a continuous process of assessment, improvement, and validation. Organizations must develop robust internal policies, implement rigorous control mechanisms, and maintain meticulous documentation demonstrating their commitment to security and risk management. This ongoing approach ensures that compliance remains dynamic and responsive to evolving technological and regulatory landscapes.
How SOC II Compliance Works in Practice
Implementing SOC II compliance requires a strategic, comprehensive approach that transforms theoretical security frameworks into practical, actionable organizational practices. Organizations must navigate a complex landscape of technical controls, documentation, and continuous improvement to successfully achieve and maintain certification.
Preparation and Initial Assessment
The SOC II compliance journey begins with a thorough internal evaluation of existing security infrastructure and control mechanisms. Organizations conduct comprehensive gap analyses to identify potential weaknesses and areas requiring enhancement. This initial phase involves:
- Mapping current security processes against SOC II trust service criteria
- Identifying potential vulnerabilities in system architecture
- Developing detailed documentation of existing control environments
- Creating remediation strategies for identified gaps
Learn more about GRC framework strategies to understand how comprehensive governance approaches support compliance efforts.
Audit Execution and Validation
Once internal preparations are complete, organizations engage independent certified public accountants (CPAs) to conduct rigorous SOC II audits. These audits typically involve:
- Extensive documentation review
- Interviews with key personnel
- Technical testing of security controls
- Verification of operational effectiveness
- Comprehensive risk assessment processes
According to AICPA guidelines, auditors meticulously evaluate an organization's ability to meet predetermined security and privacy standards, ensuring that control mechanisms are not just documented but consistently and effectively implemented.
Continuous Improvement and Maintenance
SOC II compliance is not a static achievement but a dynamic, ongoing process. Successful organizations view compliance as a continuous improvement cycle, regularly reassessing and enhancing their security practices. This approach involves periodic internal audits, staying current with evolving technological threats, and proactively updating security protocols to address emerging risks and maintain certification integrity.
Real-World Impact of SOC II Compliance on Business Operations
SOC II compliance transcends theoretical security frameworks, delivering tangible transformative impacts on organizational infrastructure, operational processes, and strategic business development. By implementing comprehensive security and privacy controls, companies fundamentally reshape their approach to risk management and technological governance.
Operational Risk Reduction
Beyond theoretical security measures, SOC II compliance provides substantial operational risk mitigation. Organizations implementing robust control mechanisms experience significant improvements in their technological resilience and incident response capabilities. This systematic approach enables businesses to:
- Identify and address potential security vulnerabilities proactively
- Develop more sophisticated risk management protocols
- Create standardized response mechanisms for potential security incidents
- Establish clear accountability and governance structures
Explore comprehensive GRC framework strategies to understand how integrated governance approaches enhance organizational security.

Business Development and Customer Trust
SOC II certification serves as a powerful competitive differentiator in complex enterprise markets. Companies demonstrating rigorous security practices gain significant advantages in customer acquisition and retention. According to Forrester Research, organizations with comprehensive security certifications experience:
- 45% faster sales cycle completion
- Higher customer retention rates
- Increased perceived reliability among enterprise clients
- Enhanced reputation in technology and service sectors
Strategic Technological Transformation
Implementing SOC II compliance drives broader organizational technological transformation. The certification process compels companies to critically evaluate and modernize their technological infrastructure, creating opportunities for systemic improvements beyond mere compliance. This approach encourages continuous innovation, promotes a proactive security culture, and positions organizations to adapt more effectively to evolving technological landscapes and emerging cybersecurity challenges.
Instantly Simplify Your SOC II Compliance Response Process
Are your teams spending countless hours manually answering complex security questionnaires to prove SOC II compliance? You already understand from this article that meeting the five trust service criteria is both essential and time-consuming, especially when every client or partner expects ironclad proof of your controls. These repetitive and costly tasks can stall your business growth, increase risk, and frustrate your staff.

Why let security paperwork slow you down? With Skypher's AI-driven Questionnaire Automation Tool, your organization can automatically generate accurate and fast responses to even the toughest SOC II requests. Our platform seamlessly integrates with over 40 leading security and TPRM systems, supports every file format, and delivers instant answers. Join forward-thinking companies that use Skypher to win new clients, shrink the sales cycle, and give your team more time to focus on core security improvements. Start now and turn compliance from a burden into a competitive edge.
Frequently Asked Questions
What is SOC II compliance?
SOC II compliance is a voluntary audit process that evaluates an organization’s systems and processes concerning five trust service criteria: security, availability, processing integrity, confidentiality, and privacy, primarily focusing on the protection of sensitive customer data.
Why is SOC II compliance important for businesses?
SOC II compliance matters for businesses because it serves as a critical trust signal for potential customers, demonstrating an organization’s commitment to protecting data, maintaining effective security controls, and implementing consistent risk management practices.
What are the key components of SOC II compliance?
The key components of SOC II compliance include the five trust service criteria—security, availability, processing integrity, confidentiality, and privacy—and the audit types known as Type I and Type II, which assess both the design and operational effectiveness of controls.
How does the SOC II compliance process work in practice?
The SOC II compliance process involves an initial internal assessment to identify gaps, followed by an independent audit conducted by certified public accountants. This is complemented by continuous improvement efforts to maintain compliance and adapt to emerging security threats.
