SOC Type 1 and SOC Type 2 reports shape how companies prove their security and stay compliant. Nearly every industry uses these audits to build trust and keep up with rising risks. Yet while SOC Type 2 covers control effectiveness over 6 to 12 months, most people overlook how much more influence these reports have beyond the checklist. The real value is not just in passing an audit but in making risk management a living part of business strategy.
Table of Contents
- Defining Soc Type 1 And Soc Type 2: Core Concepts
- The Importance Of Soc Reports In Risk Management
- Key Differences Between Soc Type 1 And Soc Type 2
- Real-World Applications Of Soc Type 1 Vs 2
- How Soc Type 1 And Soc Type 2 Impact Business Operations
Quick Summary
| Takeaway | Explanation |
|---|---|
| Understand SOC Report Types | SOC Type 1 provides a snapshot, while SOC Type 2 offers a comprehensive evaluation over time. |
| Choose Based on Need | The choice between SOC Type 1 and SOC Type 2 depends on compliance requirements and stakeholder assurance needs. |
| Build Stakeholder Confidence | SOC reports enhance trust by showing rigorous assessments of internal controls and security practices. |
| Proactively Manage Risks | Utilizing SOC reports helps organizations identify vulnerabilities and implement effective risk management strategies. |
| Demonstrate Operational Excellence | Organizations with robust control frameworks are better positioned for sustainable operational success and stakeholder credibility. |
Defining SOC Type 1 and SOC Type 2: Core Concepts
Service Organization Control (SOC) reports represent critical compliance and security assessment frameworks used by organizations to validate their internal control mechanisms and risk management processes. These standardized audits, developed by the American Institute of Certified Public Accountants (AICPA), provide comprehensive evaluations of an organization's operational controls and information security practices.
Understanding SOC Reports
SOC reports are designed to offer independent verification of an organization's control environment, focusing on specific aspects of financial reporting, operational effectiveness, and data protection. While multiple SOC report types exist, SOC Type 1 and SOC Type 2 are the most commonly utilized frameworks for demonstrating organizational security and compliance.
Key characteristics of SOC reports include:
- Conducted by independent certified public accountants
- Provide detailed assessments of control mechanisms
- Offer transparent insights into organizational risk management
- Help build trust with stakeholders and potential clients
Fundamental Differences Between SOC Type 1 and SOC Type 2
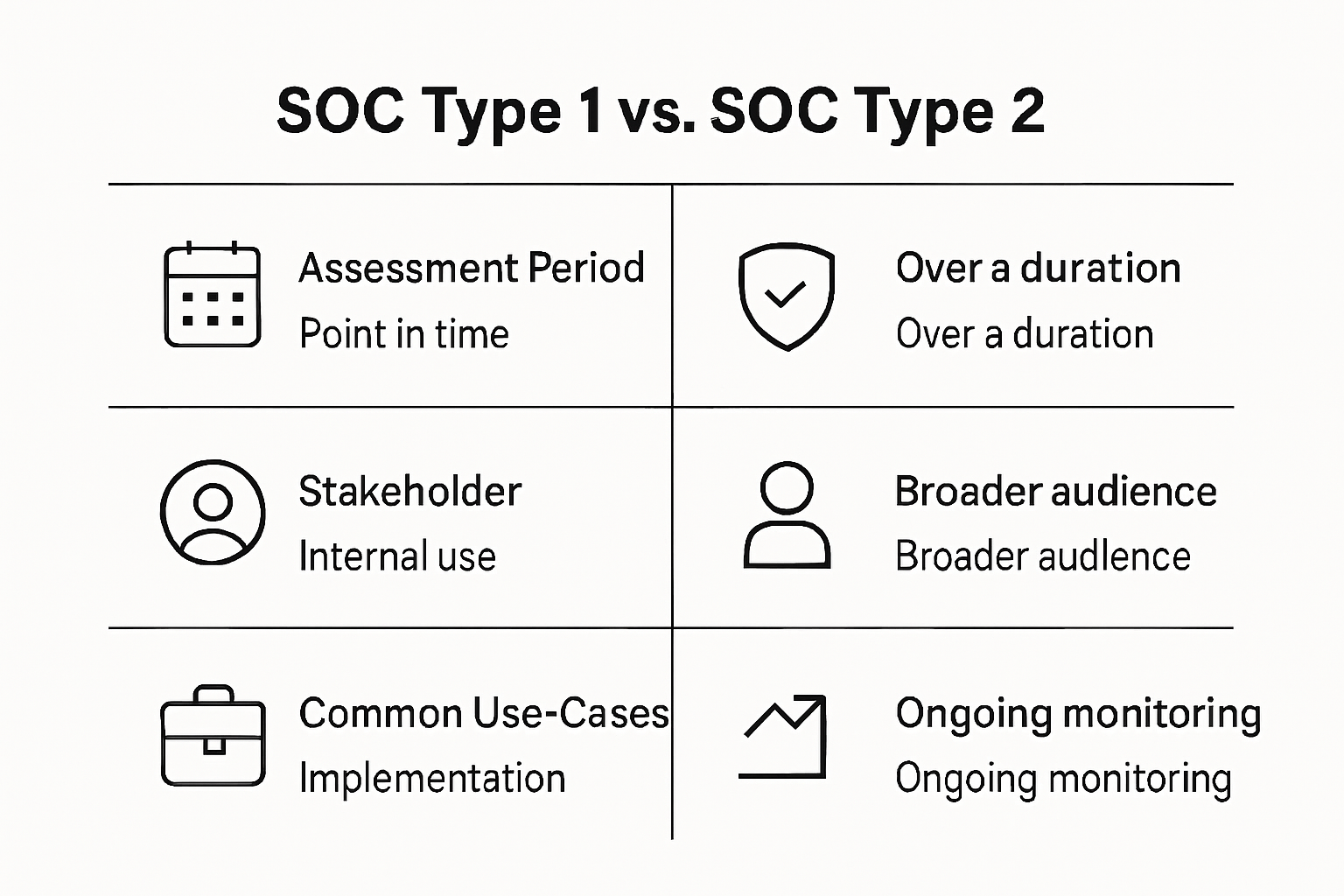
The primary distinction between SOC Type 1 and SOC Type 2 lies in their scope, depth, and assessment methodology. SOC Type 1 reports focus on a snapshot of an organization's control design at a specific point in time, while SOC Type 2 reports provide a more comprehensive evaluation of both control design and operational effectiveness over an extended period.
In SOC Type 1 assessments, auditors examine the design of internal controls at a specific moment, verifying whether these controls are appropriately structured to meet predefined security and operational standards. SOC Type 2 reports, conversely, involve a more rigorous examination that includes testing the actual implementation and effectiveness of these controls over typically a 6 to 12 month period.
The selection between SOC Type 1 and SOC Type 2 depends on an organization's specific compliance requirements, industry standards, and the depth of assurance needed by stakeholders to demonstrate robust security and operational practices.
The Importance of SOC Reports in Risk Management
Risk management represents a critical strategic function for organizations seeking to protect their operational integrity, financial stability, and reputation. SOC reports provide a comprehensive mechanism for evaluating and communicating an organization's internal control mechanisms, enabling stakeholders to assess potential vulnerabilities and understand the effectiveness of risk mitigation strategies.
Strategic Risk Assessment Framework
SOC reports function as powerful diagnostic tools that offer deep insights into an organization's control environment. By providing independent and objective evaluations, these reports help businesses identify potential weaknesses, validate existing control structures, and demonstrate commitment to robust security practices.
Key strategic benefits of SOC reports include:
- Systematic identification of potential operational risks
- Independent verification of internal control mechanisms
- Enhanced transparency for stakeholders and potential business partners
- Proactive approach to managing organizational vulnerabilities
Building Stakeholder Confidence
In an increasingly complex business landscape, stakeholders demand transparent and verifiable evidence of an organization's risk management capabilities. Research from Gartner indicates that organizations with comprehensive risk assessment frameworks are 60% more likely to prevent significant operational disruptions.
SOC reports serve multiple critical functions in building stakeholder confidence. They provide a standardized assessment that goes beyond surface level evaluations, offering detailed insights into an organization's control design, operational effectiveness, and commitment to maintaining high security standards.
For vendors, service providers, and technology companies, SOC reports become essential credentials that demonstrate professional credibility. These reports signal to potential clients and partners that an organization has undergone rigorous, independent assessment and maintains a structured approach to managing technological and operational risks.
Ultimately, SOC reports transform risk management from a theoretical concept into a measurable, actionable framework that enables organizations to systematically identify, assess, and mitigate potential vulnerabilities across their operational ecosystem.
Key Differences Between SOC Type 1 and SOC Type 2
While SOC Type 1 and SOC Type 2 reports share a common goal of providing assurance about an organization's internal controls, they differ significantly in scope, depth, and purpose. Understanding these nuanced differences is crucial for organizations seeking to demonstrate their commitment to robust security and operational practices.
Scope and Assessment Methodology
The fundamental distinction between SOC Type 1 and SOC Type 2 lies in their approach to evaluating organizational controls. SOC Type 1 reports offer a point-in-time snapshot of an organization's control design, while SOC Type 2 reports provide a comprehensive assessment of both control design and operational effectiveness over an extended period.
To clearly illustrate the differences between SOC Type 1 and SOC Type 2, the table below compares their key characteristics based on information detailed in the article.
| Aspect | SOC Type 1 | SOC Type 2 |
|---|---|---|
| Assessment Scope | Design of controls at a specific point in time | Design and effectiveness of controls over time |
| Evaluation Period | Specific date (snapshot) | 6-12 months (ongoing period) |
| Depth of Review | Verifies documentation and control design | Tests implementation and operational effectiveness |
| Use Case | Initial vendor assessments, quick validation | Long-term assurance, client and regulatory needs |
| Stakeholder Assurance Level | Moderate | High |
| Reporting Detail | Single point-in-time assessment | Comprehensive, includes actual performance data |
| Typical Users | Startups, new service providers | Established providers, high-compliance industries |
Key comparative aspects include:
- Timeframe of Assessment
- Depth of Control Evaluation
- Stakeholder Reporting Requirements
- Compliance and Validation Objectives
Technical and Operational Implications
Research from the AICPA reveals that SOC Type 1 reports primarily focus on the design of internal controls at a specific moment. Auditors examine whether the organization's control mechanisms are appropriately structured to meet predefined security and operational standards. In contrast, SOC Type 2 reports involve a more rigorous examination that includes:
- Detailed testing of control implementation
- Verification of operational effectiveness
- Comprehensive analysis over 6 to 12 months
- In-depth review of actual control performance
SOC Type 2 reports provide a more dynamic and comprehensive view of an organization's control environment. They demonstrate not just how controls are designed, but how effectively they are implemented and maintained over time. This approach offers stakeholders a more robust and credible assessment of an organization's risk management capabilities.
For technology companies, service providers, and organizations handling sensitive data, the choice between SOC Type 1 and SOC Type 2 depends on specific compliance requirements, industry standards, and the level of assurance needed by stakeholders. While SOC Type 1 reports can be valuable for initial assessments, SOC Type 2 reports offer a more comprehensive and trustworthy validation of an organization's operational and security practices.
Real-World Applications of SOC Type 1 vs 2
In the complex landscape of cybersecurity and compliance, SOC Type 1 and SOC Type 2 reports serve critical roles across various industries, helping organizations demonstrate their commitment to robust internal controls and risk management strategies. Understanding their practical applications provides insights into how businesses leverage these compliance frameworks to build trust and validate their operational integrity.
Industry-Specific Compliance Scenarios
Different sectors utilize SOC reports strategically to address unique regulatory and operational challenges. Financial services, cloud computing providers, and healthcare technology companies frequently rely on these assessments to validate their control environments and reassure stakeholders about their security practices.
Key industries benefiting from SOC reports include:
The following table summarizes the key industries mentioned in the article and highlights how each commonly utilizes SOC reports for compliance and stakeholder assurance.
| Industry/Sector | Common Usage of SOC Reports |
|---|---|
| Financial Technology | Validate control environments, reassure partners |
| Cloud Service Providers | Demonstrate data protection and operational security |
| Healthcare Information Systems | Ensure compliance with data protection regulations, build trust |
| Payment Processing | Meet regulatory standards, prove secure transaction handling |
| Managed Service Providers | Show operational reliability and security to clients |
| Technology Startups | Establish initial credibility with stakeholders |
- Financial technology platforms
- Cloud service providers
- Healthcare information systems
- Payment processing organizations
- Managed service providers
Practical Implementation Strategies
Research from Deloitte highlights that organizations typically choose between SOC Type 1 and SOC Type 2 based on specific business requirements and stakeholder expectations. SOC Type 1 reports offer a quick snapshot suitable for initial vendor assessments, while SOC Type 2 reports provide comprehensive evidence of long-term control effectiveness.
For instance, a cloud storage provider might use a SOC Type 2 report to demonstrate continuous data protection mechanisms, showing potential clients how security controls are consistently maintained over time. Conversely, a financial technology startup might initially pursue a SOC Type 1 report to quickly establish credibility with potential investors and partners.
The selection between SOC Type 1 and SOC Type 2 depends on multiple factors, including regulatory requirements, client expectations, and the organization's maturity in implementing comprehensive security frameworks. While SOC Type 1 reports provide an initial validation, SOC Type 2 reports offer a more in-depth and credible assessment of an organization's operational resilience and commitment to maintaining high security standards.
How SOC Type 1 and SOC Type 2 Impact Business Operations
SOC reports play a transformative role in shaping organizational strategies, operational frameworks, and stakeholder confidence. By providing comprehensive insights into internal control mechanisms, these assessments enable businesses to systematically identify, address, and mitigate potential operational risks and vulnerabilities.
Operational Risk Management
Business continuity and risk mitigation are critical considerations for modern organizations. SOC Type 1 and SOC Type 2 reports serve as powerful diagnostic tools that help leadership teams understand their operational landscape, identify potential weaknesses, and develop targeted strategies for improvement.
Key operational impact areas include:

- Identification of systemic control vulnerabilities
- Enhanced internal process transparency
- Improved decision making through comprehensive risk assessment
- Streamlined compliance management
- Proactive risk mitigation strategies
Strategic Business Transformation
Research from McKinsey indicates that organizations with robust control frameworks are 40% more likely to achieve sustainable operational excellence. SOC Type 2 reports, in particular, provide a dynamic view of an organization's control effectiveness over time, enabling leadership to:
- Track incremental improvements in control mechanisms
- Demonstrate consistent operational discipline
- Build credibility with stakeholders
- Validate long-term strategic investments in risk management
Beyond compliance, SOC reports fundamentally transform how businesses approach operational risk. They shift organizational perspective from reactive problem-solving to proactive risk management, creating a culture of continuous improvement and strategic resilience. For technology companies, service providers, and enterprises handling sensitive data, these reports are not just compliance documents but strategic assets that communicate operational maturity and commitment to excellence.
Bridge the Gap Between SOC Reporting and Real Security Progress
Struggling to keep up with the demands of SOC Type 1 and Type 2 audits? This article made it clear that precise reporting, effective risk management, and continuous assurance are crucial. Yet for many teams, responding to security questionnaires and demonstrating compliance means hours lost to manual tasks, slow communication, and missed business opportunities.

Skypher delivers exactly what you need to turn SOC best practices into business wins. Accelerate your next audit win by automating your security questionnaire responses with our AI-Powered Questionnaire Automation Tool. Reduce time spent on vendor requests while impressing stakeholders with transparent controls. See how our customizable Trust Center and integrations with 40+ risk management platforms can help you show your SOC compliance story faster. Visit Skypher today and get ahead of the next questionnaire. Act now to empower your team and secure more business opportunities.
Frequently Asked Questions
What is the main difference between SOC Type 1 and SOC Type 2 reports?
The main difference between SOC Type 1 and SOC Type 2 reports lies in their scope and assessment methodology. SOC Type 1 provides a point-in-time evaluation of an organization's control design, while SOC Type 2 offers a comprehensive assessment of both control design and effectiveness over an extended period, typically 6 to 12 months.
When should an organization choose SOC Type 1 over SOC Type 2?
Organizations might choose SOC Type 1 when they need a quick evaluation of their control environment for initial vendor assessments or to establish credibility with stakeholders. It's suitable for situations where a comprehensive assessment of operational effectiveness is not yet required.
How do SOC Type 1 and Type 2 reports impact stakeholder confidence?
Both SOC Type 1 and SOC Type 2 reports enhance stakeholder confidence by providing independent verification of an organization's internal control mechanisms. However, SOC Type 2 reports offer deeper insights into operational effectiveness, thereby providing a stronger assurance of ongoing security practices, which can further build trust among stakeholders.
What industries typically utilize SOC Type 1 and SOC Type 2 reports?
Industries such as financial services, cloud computing, healthcare technology, and payment processing commonly utilize SOC Type 1 and SOC Type 2 reports to validate their control environments and reassure stakeholders about their security and compliance practices.
