Nearly 60 percent of data breaches stem from failures in basic access controls, revealing just how vulnerable organizations can be without strict security frameworks. Access control is far more than a technical hurdle; it is the foundation that shields sensitive assets from both internal misuse and external threats. By understanding the core principles and models behind access control, readers can better protect valuable information while staying ahead of modern security challenges.
Table of Contents
- Defining Access Control And Core Principles
- Types Of Access Control Systems Compared
- How Access Controls Function In Organizations
- Real-World Use Cases And Industry Examples
- Risks, Compliance, And Implementation Mistakes
Key Takeaways
| Point | Details |
|---|---|
| Access Control Components | Effective access control includes authentication, authorization, and access management to secure resources. |
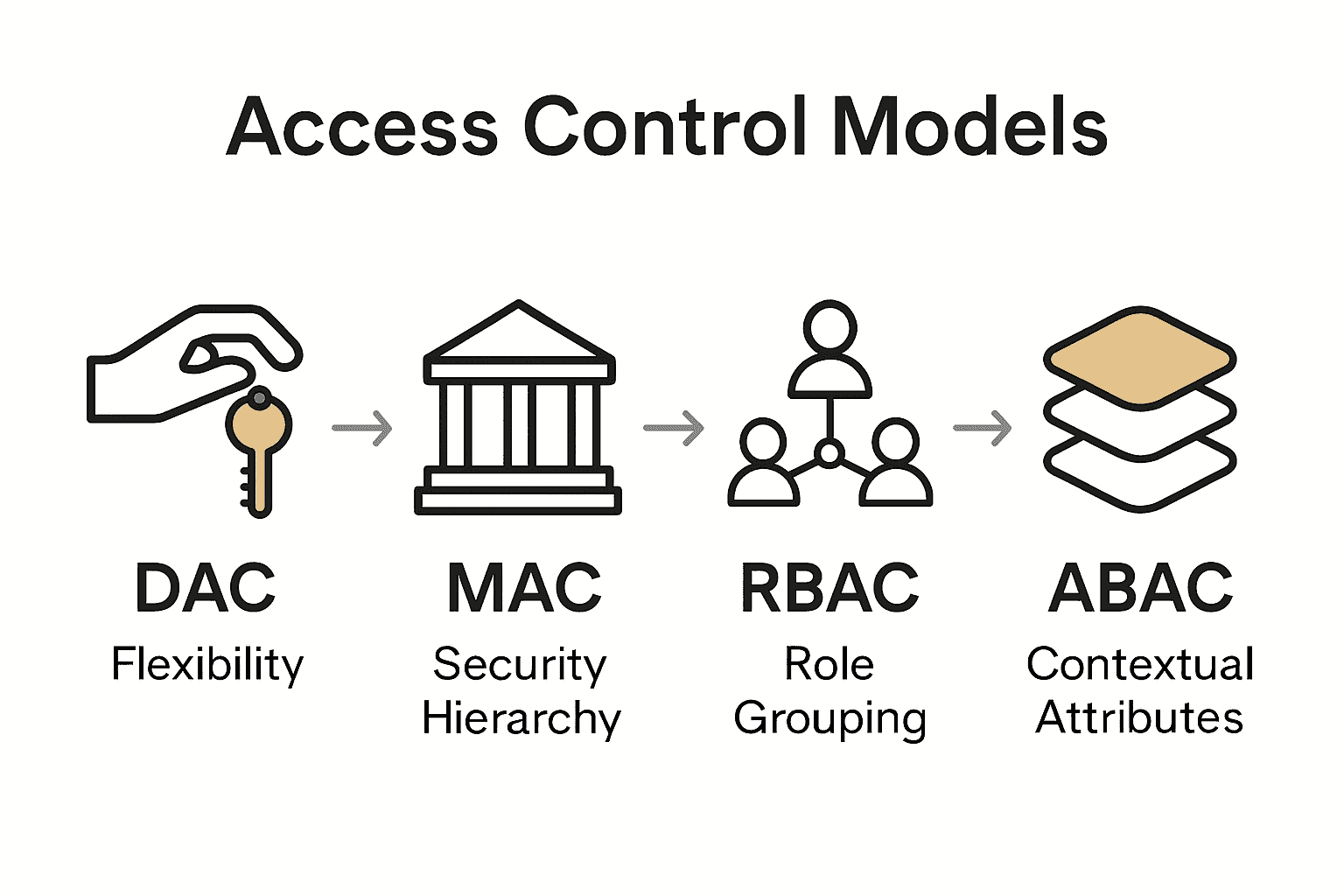
| Access Control Models | Organizations can choose from DAC, MAC, RBAC, and emerging ABAC to align security with operational needs. |
| Implementation Risks | Common pitfalls include inadequate authentication protocols, compliance gaps, and technological vulnerabilities that could compromise security. |
| Technological Advancements | AI and ML are reshaping access control by enhancing threat detection and automating security processes, promoting a proactive security stance. |
Defining Access Control and Core Principles
Access control represents a sophisticated security mechanism designed to selectively manage and restrict resource access based on user identity, permissions, and organizational requirements. Wikipedia defines access control as "the selective restriction of access to a place or resource, allowing only authorized users," which encompasses both physical security measures like locks and guards, and digital information security protocols.
Core Components of Access Control
- Authentication: Verifying user identity through credentials
- Authorization: Determining specific access permissions
- Access Management: Controlling and monitoring resource interactions
Access control models provide structured frameworks for implementing these security principles. According to IRJET, three primary models dominate enterprise security strategies:
- Discretionary Access Control (DAC): Users can share resources at their discretion
- Mandatory Access Control (MAC): Centralized administrative control with strict hierarchical permissions
- Role-Based Access Control (RBAC): Access granted based on organizational job functions
These models enable organizations to create granular, flexible security infrastructures that protect sensitive information while maintaining operational efficiency. By implementing robust access control strategies, businesses can significantly reduce unauthorized data exposure and potential security breaches.

See our guide on GRC framework to understand how access control integrates with broader governance strategies.
Types of Access Control Systems Compared
Access control systems are sophisticated security frameworks that define how organizations manage and restrict resource access. Wikipedia highlights three primary models: Discretionary Access Control (DAC), Mandatory Access Control (MAC), and Role-Based Access Control (RBAC), each offering unique approaches to managing digital security.
Key Access Control Models
- Discretionary Access Control (DAC)
- Resource owners control access permissions
- Maximum flexibility for individual users
- Higher risk of potential security vulnerabilities
- Mandatory Access Control (MAC)
- Centralized, hierarchical permission structure
- Strict security classifications
- Commonly used in government and military systems
- Role-Based Access Control (RBAC)
- Permissions assigned based on organizational roles
- Streamlined permission management
- Reduces complexity in large enterprise environments
According to Journal of Engineering Sciences, emerging models like Attribute-Based Access Control (ABAC) are gaining prominence. ABAC provides unprecedented flexibility by evaluating multiple user, resource, and environmental attributes to make granular access decisions.
The evolution of these access control systems reflects the increasing complexity of modern digital environments, where security must balance robust protection with operational efficiency.
Learn more about our GRC framework guide to understand how these access control strategies integrate with broader security governance.
How Access Controls Function in Organizations
Wikipedia explains that access control in organizations fundamentally operates through two critical mechanisms: authentication and authorization. These interconnected processes ensure that only verified and approved individuals can access specific resources, creating a robust security barrier that protects sensitive organizational information.
Key Functional Components
- Identity Verification: Confirming user credentials
- Permission Mapping: Assigning specific access rights
- Continuous Monitoring: Tracking resource interactions
The authentication process typically involves multiple verification methods:
- Password-Based Authentication
- Biometric Verification
- Multi-Factor Authentication
- Single Sign-On (SSO) Systems
Advanced systems like the Distributed Access Control System (DACS) enable more sophisticated access management. Wikipedia highlights DACS as a lightweight single sign-on mechanism that provides attribute-based access control for web servers, allowing organizations to create flexible yet secure digital environments.
Implementing comprehensive access controls requires a strategic approach that balances security requirements with operational efficiency. Organizations must continuously adapt their access management strategies to address emerging technological challenges and potential security vulnerabilities.
Learn more about our GRC framework guide to understand how access control integrates with broader organizational security strategies.
Real-World Use Cases and Industry Examples
Access control strategies find critical applications across diverse industries, addressing unique security challenges and protecting sensitive information. Wikipedia highlights the Bell-LaPadula model as a prime example, particularly in government and military sectors where data confidentiality is paramount.
Industry-Specific Access Control Applications
- Healthcare
- Patient record protection
- HIPAA compliance enforcement
- Granular access to medical systems
- Financial Services
- Secure transaction monitoring
- Preventing unauthorized account access
- Regulatory compliance tracking
- Government and Military
- Classified information protection
- Strict hierarchical access protocols
- Multi-level security clearance management
Wikipedia introduces an emerging paradigm called Relationship-based Access Control (ReBAC). This innovative approach defines access permissions through intricate relationships between subjects and resources, gaining significant traction in social network and web application environments.
The evolution of access control demonstrates how security mechanisms must continuously adapt to technological advancements and complex organizational ecosystems. Modern systems blend sophisticated authentication techniques with contextual awareness, creating dynamic and responsive security frameworks.
See our guide on GRC framework to explore how access control integrates with comprehensive governance strategies.
Risks, Compliance, and Implementation Mistakes
ArXiv research highlights that traditional access control methods are fraught with significant challenges, including complex third-party interactions, systemic inefficiencies, and critical privacy vulnerabilities. These inherent limitations underscore the need for organizations to develop sophisticated, dynamic access control strategies.
Common Implementation Risks
- Inadequate Authentication Protocols
- Weak password management
- Lack of multi-factor authentication
- Insufficient user verification processes
- Compliance Gaps
- Incomplete regulatory documentation
- Inconsistent access tracking
- Failure to maintain audit trails
- Technological Vulnerabilities
- Outdated security infrastructure
- Limited visibility into access patterns
- Delayed threat response mechanisms
According to Honeywell Buildings, emerging technologies like Artificial Intelligence (AI) and Machine Learning (ML) are revolutionizing access control systems. These advanced technologies can:
- Identify unusual access patterns
- Generate real-time anomaly detection alerts
- Reduce human error in security monitoring
- Provide automated first-level support
Successful access control implementation requires a holistic approach that combines technological innovation, continuous monitoring, and proactive risk management. Organizations must remain agile, regularly updating their strategies to address evolving security landscapes.
Learn more about vendor risk management strategies to complement your access control approach.
Streamline Your Access Control Compliance with Skypher
Access control is essential for protecting sensitive data and maintaining regulatory compliance, but managing security questionnaires can become overwhelming and time-consuming. This article highlights the complexity of implementing robust authentication and authorization mechanisms and the need for precise, efficient access management strategies. If you are responsible for ensuring strong access control while navigating complicated security reviews, the pain of tedious manual processes and delayed responses can hinder your organization’s security posture and slow business growth.
Skypher’s AI Questionnaire Automation Tool is purpose-built to help teams automate and accelerate responses to security questionnaires related to access control and governance. With powerful AI-driven content management, over 30 API integrations including ServiceNow and OneTrust, and real-time collaboration features, Skypher simplifies the process of demonstrating compliance with access control policies. Its customizable Trust Center helps build trust with clients and auditors by centralizing critical security information.

Stop wasting valuable time answering repetitive security questions and reduce errors that can expose your organization to risk. Discover how Skypher can transform your security review process by visiting Skypher today. Explore our AI Questionnaire Automation Tool and learn how we integrate with key third-party risk management platforms to keep your access control compliance on track at scale.
Frequently Asked Questions
What are the core components of access control?
Access control consists of three core components: authentication, authorization, and access management. Authentication verifies user identity, authorization determines specific access permissions, and access management controls and monitors interactions with resources.
What are the main types of access control models?
The main types of access control models are Discretionary Access Control (DAC), Mandatory Access Control (MAC), and Role-Based Access Control (RBAC). Each model has different mechanisms and permissions structures for managing access to resources.
How do authentication and authorization work together in access control?
Authentication and authorization work together in access control by first verifying a user’s identity through authentication. Once verified, authorization then determines what specific resources and permissions the user has access to, creating a secure access environment.
What are some common risks associated with access control implementation?
Common risks in access control implementation include inadequate authentication protocols, compliance gaps, and technological vulnerabilities. Organizations must address these risks with robust strategies to maintain security and compliance.
