In today's world, information security governance is no longer just an IT issue; it is a cornerstone of strategic management. Organizations that implement effective governance frameworks experience a 53% higher success rate in mitigating digital risks. But consider this: many companies treat security as simply an operational necessity, rather than a vital business strategy. The twist? Failing to engage every employee in security practices can lead to devastating breaches that are primarily caused by human error. This dynamic shift towards understanding security as a shared responsibility is key to safeguarding sensitive data and enhancing organizational resilience.
Table of Contents
- Why Information Security Governance Matters
- Key Principles Of Security Governance
- Implementing A Security Governance Program
- Choosing The Right Governance Framework
Quick Summary
| Takeaway | Explanation |
|---|---|
| Align Security with Business Goals | Information security governance integrates technological protection with broader business objectives, ensuring security investments align with strategic priorities for effective risk management. |
| Cultural Embedding is Essential | Creating a security-aware culture is fundamental; organizations should provide comprehensive training and clear policies to instill security consciousness at all levels. |
| Establish Clear Accountability | Defined roles and responsibilities are crucial; organizations must implement transparent accountability structures to ensure security is embedded in every strategic decision. |
| Adopt a Comprehensive Risk Management Framework | Implementing a dynamic risk management framework is necessary to identify, assess, and mitigate risks, adapting to evolving threats and technological changes. |
| Continuous Improvement is Key | Security governance should not be static; regular assessments, feedback mechanisms, and ongoing training are essential for adapting to new challenges and enhancing security measures. |
Why Information Security Governance Matters
In an era of increasing digital complexity and persistent cyber threats, information security governance has transformed from a technical checkbox to a critical strategic imperative for organizations worldwide. This framework isn't just about implementing security tools—it's about creating a comprehensive approach that aligns technological protection with broader business objectives.
Protecting Organizational Assets in a High-Stakes Digital Landscape
Modern organizations face an unprecedented landscape of digital risks. Cybercriminals are becoming more sophisticated, targeting not just large corporations but businesses of all sizes. Research from IBM reveals that the average cost of a data breach in 2022 reached $4.35 million, underscoring the immense financial implications of inadequate information security governance.
Information security governance provides a structured framework that goes beyond traditional IT security measures. It establishes clear accountability, defines strategic priorities, and ensures that security isn't an isolated function but an integrated aspect of organizational strategy. By centralizing security leadership and decision-making, companies can:
- Align Security Investments with Business Goals
- Create Transparent Accountability Structures
- Implement Proactive Risk Management Strategies
Regulatory Compliance and Strategic Risk Management
Compliance is no longer optional in today's regulatory environment. Information security governance helps organizations navigate complex regulatory landscapes like GDPR, HIPAA, and PCI DSS. NIST Special Publication 800-53 emphasizes that effective governance isn't just about technical controls but about creating comprehensive risk management processes.
By establishing clear governance frameworks, organizations can:
- Demonstrate due diligence to regulators
- Reduce potential legal and financial liabilities
- Build trust with customers and stakeholders
The Human Element of Information Security
Technology alone cannot solve security challenges. Gartner research consistently highlights that 95% of cybersecurity failures are attributed to human error. Information security governance addresses this critical human factor by:
- Developing comprehensive security awareness training
- Creating clear organizational policies
- Establishing a culture of security consciousness
Effective governance transforms security from a purely technical domain into a shared organizational responsibility. It empowers employees at all levels to understand their role in protecting sensitive information, creating a holistic defense mechanism that extends far beyond firewalls and encryption.
In essence, information security governance is not a luxury—it's a fundamental necessity for any organization seeking to thrive in an increasingly interconnected and threat-laden digital ecosystem. By adopting a strategic, comprehensive approach to information security, businesses can protect their most valuable assets while maintaining the agility and innovation needed to compete in today's dynamic marketplace.

Key Principles of Security Governance
Information security governance represents a strategic framework that transcends traditional technical controls, embedding security consciousness into an organization's core operational DNA. By establishing clear principles, organizations can transform security from a reactive measure to a proactive, integrated business strategy.
Strategic Alignment and Leadership Commitment
Effective security governance begins with unwavering leadership commitment. McKinsey research indicates that organizations with strong executive involvement in cybersecurity are 53% more likely to effectively manage digital risks. This principle demands that board members and senior executives:
- Actively Participate in Security Strategy Development
- Allocate Sufficient Resources for Comprehensive Security Initiatives
- Establish Clear Accountability Across Organizational Levels
Leadership must view information security not an IT problem, but as a critical business risk management discipline. This means moving beyond technical compliance to creating a holistic approach that integrates security considerations into strategic planning, resource allocation, and organizational culture.
Comprehensive Risk Management Framework
A robust security governance model requires a systematic approach to identifying, assessing, and mitigating information security risks. NIST Special Publication 800-39 provides a comprehensive framework for managing information security risks that emphasizes:
- Continuous Risk Assessment
- Multi-Level Risk Management Approach
- Integration of Risk Management into Organizational Processes
Organizations must develop a dynamic risk management framework that adapts to evolving technological landscapes and emerging threat vectors. This involves creating flexible policies that can quickly respond to new challenges while maintaining consistent security standards.
Cultural Embedding and Organizational Awareness
Technology alone cannot ensure comprehensive security. Gartner's research emphasizes that building a security-aware culture is fundamental to effective governance. This principle involves:
- Comprehensive Security Training Programs
- Regular Communication of Security Policies
- Creating Incentive Structures that Reward Security-Conscious Behavior
Successful information security governance transforms security from a compliance requirement to a shared organizational responsibility. It requires creating an environment where every employee understands their role in protecting sensitive information, regardless of their position or technical expertise.
By implementing these key principles, organizations can develop a mature, adaptive information security governance model that protects critical assets, manages risks effectively, and supports strategic business objectives. The goal is not just to prevent security incidents but to create a resilient, security-conscious organizational ecosystem that can dynamically respond to an ever-changing digital threat landscape.
Implementing a Security Governance Program
Implementing a robust security governance program is a complex, strategic process that requires meticulous planning, organizational commitment, and a comprehensive approach to integrating security into every aspect of business operations. Successful implementation goes beyond technical solutions, demanding a holistic transformation of organizational culture and operational practices.
Developing A Comprehensive Security Framework
NIST Special Publication 800-37 provides a critical roadmap for developing an integrated risk management framework. Organizations must create a structured approach that includes:
- Comprehensive Risk Assessment Methodologies
- Clear Policy Documentation
- Scalable Implementation Strategies
The framework should be flexible enough to adapt to changing technological landscapes while maintaining consistent security standards. This involves creating a living document that evolves with the organization's strategic objectives and emerging threat landscapes. Gartner research suggests that organizations with adaptive security frameworks are 40% more effective in mitigating potential security risks.
Establishing Organizational Roles And Responsibilities
Effective security governance requires crystal-clear accountability and well-defined roles. ISACA's governance guidelines recommend creating a structured approach to role definition that includes:
- Identifying key stakeholders across departments
- Defining specific security responsibilities for each organizational level
- Creating a centralized oversight mechanism
This typically involves establishing critical positions such as a Chief Information Security Officer (CISO) who reports directly to executive leadership. The goal is to create a transparent chain of accountability that ensures security considerations are integrated into every strategic decision.
Continuous Monitoring And Improvement
Implementation is not a one-time event but an ongoing process of evaluation and refinement. ISO/IEC 27001 emphasizes the importance of continuous improvement in information security governance. Organizations must:
- Implement robust monitoring systems
- Conduct regular security audits
- Create feedback loops for continuous improvement
- Develop incident response and recovery protocols
This approach transforms security governance from a static compliance exercise into a dynamic, adaptive process. Regular assessments help organizations identify potential vulnerabilities, measure the effectiveness of existing controls, and proactively address emerging security challenges.
Successful implementation of a security governance program requires more than just technical solutions. It demands a fundamental shift in organizational thinking—treating information security as a strategic business imperative rather than a technical afterthought. By creating a comprehensive, adaptable framework that aligns security objectives with broader business goals, organizations can build a resilient defense against an increasingly complex digital threat landscape.
The ultimate measure of success is not just preventing security incidents, but creating an organizational culture where security is viewed as a shared responsibility and a critical component of strategic decision-making.
Choosing the Right Governance Framework
Selecting an appropriate information security governance framework is a critical strategic decision that can significantly impact an organization's ability to manage digital risks effectively. The right framework serves as a comprehensive blueprint for aligning security objectives with broader business goals, transforming information security from a technical necessity to a strategic business enabler.
Evaluating Leading Governance Frameworks
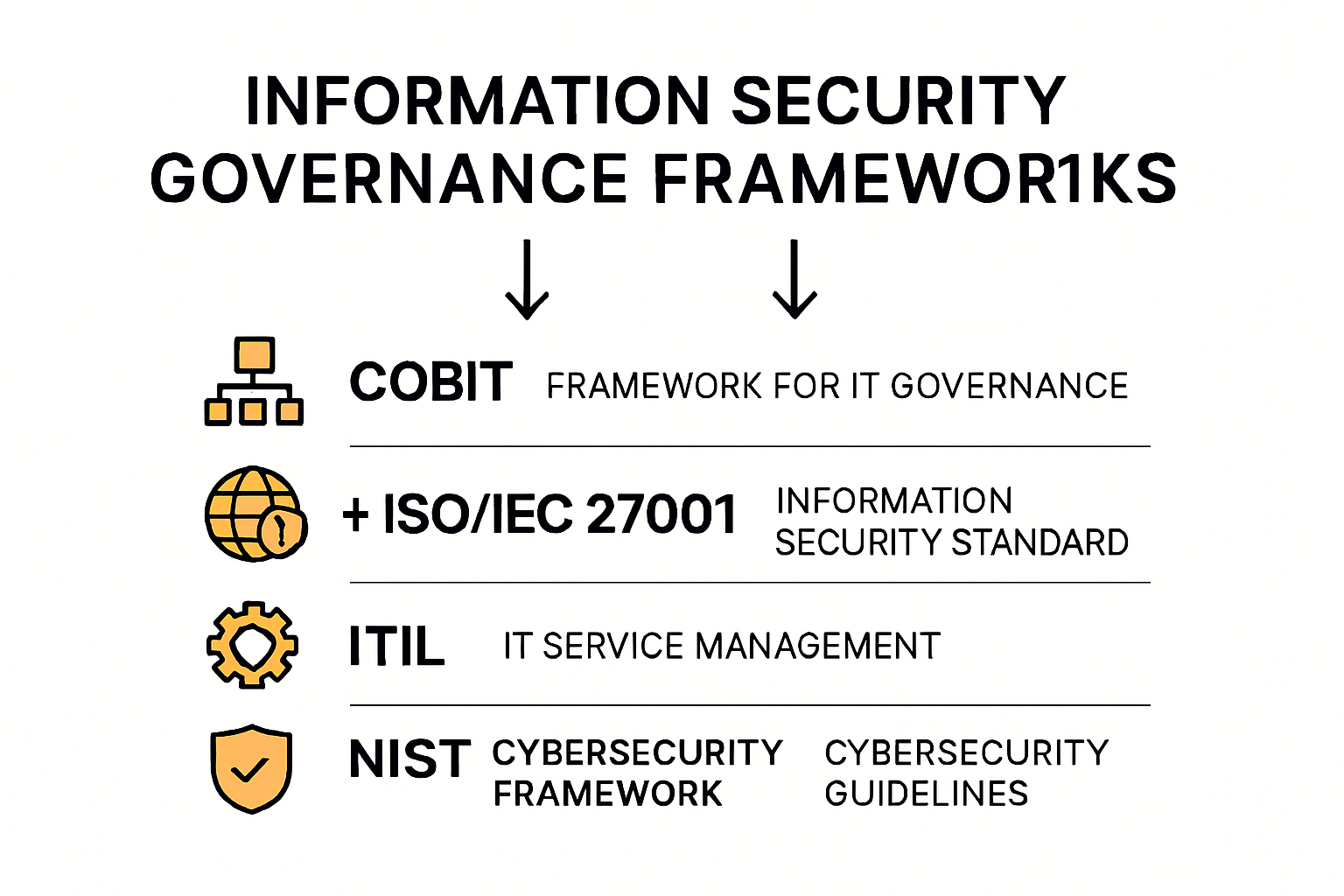
NIST Special Publication 800-53 provides a comprehensive overview of the most prominent information security governance frameworks. Organizations must carefully assess multiple frameworks based on their unique operational contexts. Key frameworks to consider include:
- COBIT (Control Objectives for Information and Related Technologies)
- ISO/IEC 27001
- ITIL (Information Technology Infrastructure Library)
- NIST Cybersecurity Framework
Each framework offers distinct advantages. Gartner's research suggests that successful organizations often adopt a hybrid approach, combining elements from multiple frameworks to create a tailored governance strategy that precisely matches their specific operational requirements.
Customization and Organizational Alignment
No single framework provides a one-size-fits-all solution. Research from MIT Sloan emphasizes the importance of framework customization. Organizations must:
- Conduct thorough organizational risk assessments
- Identify specific security requirements
- Develop a flexible framework that can evolve with technological changes
- Align governance approaches with industry-specific regulatory requirements
Successful framework selection involves understanding an organization's unique risk profile, technological infrastructure, and strategic objectives. This requires a nuanced approach that goes beyond generic implementation guidelines, focusing instead on creating a living, adaptable governance model.
Implementation and Continuous Improvement
Choosing a framework is just the beginning of the governance journey. Deloitte's cybersecurity research highlights the critical importance of ongoing assessment and refinement. Effective implementation involves:
- Regular framework performance evaluations
- Continuous skills development
- Creating robust feedback mechanisms
- Developing adaptive governance processes
Organizations must view their chosen framework as a dynamic tool rather than a static document. The most effective governance approaches are those that can quickly adapt to emerging technological challenges, evolving threat landscapes, and changing business objectives.
Ultimately, the right governance framework is not about strict adherence to a predefined set of rules, but about creating a flexible, responsive approach to managing information security risks. It requires a strategic mindset that views security as an integral part of business innovation rather than a mere compliance exercise.
By carefully selecting, customizing, and continuously improving their governance framework, organizations can transform information security from a potential liability into a strategic advantage that supports overall business resilience and growth.
Frequently Asked Questions
What is information security governance?
Information security governance is a strategic framework that integrates security practices with organizational goals to protect sensitive data. It involves aligning security investments with business objectives, establishing clear accountability, and implementing proactive risk management strategies.
Why is information security governance important?
Information security governance is essential because it helps organizations mitigate digital risks, comply with regulations, and foster a culture of security awareness. By doing so, businesses can protect their assets, build trust with stakeholders, and reduce the financial impact of security breaches.
What are the key principles of security governance?
The key principles of security governance include strategic alignment and leadership commitment, comprehensive risk management frameworks, and cultural embedding of security awareness within the organization. These principles guide organizations in transforming their security practices into a proactive business strategy.
How can organizations implement an effective security governance program?
Organizations can implement an effective security governance program by developing a comprehensive security framework, defining clear roles and responsibilities, and establishing continuous monitoring and improvement processes. This holistic approach ensures that security considerations are integrated into every aspect of business operations.
Elevate Your Security Governance with Skypher
In the realm of information security governance, addressing complex challenges is more than a necessity—it's a strategic imperative. With 53% higher success rates in mitigating digital risks for organizations that implement robust security frameworks, the stakes are undeniably high. Is your organization prepared to transform security from a reactive measure to a proactive strategy?

At Skypher, we understand that effective security governance involves not only managing risks but also ensuring that every team member is engaged and informed. Our AI Questionnaire Automation Tool empowers organizations like yours—especially in the tech and finance sectors—to streamline and automate security reviews, ensuring efficiency and accuracy in every step. Imagine reducing the time needed for proof of concepts and contracts while enhancing your cybersecurity posture through a comprehensive Trust Center.
Don’t wait for breaches to happen! Take the first step toward a resilient security future. Discover how our real-time collaboration and API integrations with over 40 third-party platforms can elevate your security governance strategy. Visit Skypher today and transform your approach to security questionnaires!
