Did you know that nearly 45 percent of data breaches in the cloud come from SaaS misconfigurations? As organizations depend more on cloud-based applications to drive productivity, the risks around SaaS security grow. Understanding SaaS security means knowing how access controls, encryption, and compliance shape your defense against evolving threats. This guide breaks down the essentials to help you protect sensitive data and maintain trust in every cloud transaction.
Table of Contents
- Defining SaaS Security And Core Concepts
- Major Types Of SaaS Security Threats
- How SaaS Security Works In Practice
- Best Practices For Enterprise SaaS Protection
- Compliance Requirements And Integration Challenges
Key Takeaways
| Point | Details |
|---|---|
| Comprehensive SaaS Security | SaaS security involves strategies, practices, and technologies to protect cloud applications and sensitive data, requiring shared responsibility between providers and users. |
| Proactive Threat Mitigation | Organizations must adopt a multilayered security approach, including continuous monitoring and diverse protection measures, to address evolving threats effectively. |
| Compliance Necessity | Enterprises should ensure adherence to regulatory frameworks like GDPR and HIPAA while implementing robust data privacy and security measures. |
| Vendor Assessment Importance | A thorough evaluation of SaaS providers’ security credentials is essential to safeguard organizational data and maintain integrity in cloud environments. |
Defining SaaS Security and Core Concepts
In the modern enterprise technology landscape, SaaS security represents the comprehensive set of strategies, practices, and technologies designed to protect cloud-based software applications and the sensitive data they process. CIC defines Software as a Service (SaaS) as a model where software applications are delivered over the Internet on a subscription basis, with providers managing critical infrastructure, maintenance, and security components.
At its core, SaaS security encompasses multiple layers of protection that safeguard both the application and user data. Unlike traditional software deployment models, SaaS introduces unique security challenges where responsibility is shared between the cloud service provider and the organization. Stanford UIT highlights that while providers handle software and infrastructure management, users retain critical responsibilities for data security and regulatory compliance.
Key elements of robust SaaS security include:
- Authentication Controls: Multi-factor authentication and single sign-on mechanisms
- Data Encryption: Protecting data both in transit and at rest
- Access Management: Granular user permission controls
- Compliance Monitoring: Continuous tracking of security standards and potential vulnerabilities
- Threat Detection: Real-time monitoring for potential security breaches
Successful SaaS security strategies require a proactive, comprehensive approach that integrates technological solutions, organizational policies, and continuous risk assessment.
 Enterprises must view security not as a one-time implementation but as an ongoing, dynamic process that adapts to evolving digital threats and technological innovations.
Enterprises must view security not as a one-time implementation but as an ongoing, dynamic process that adapts to evolving digital threats and technological innovations.
Major Types of SaaS Security Threats
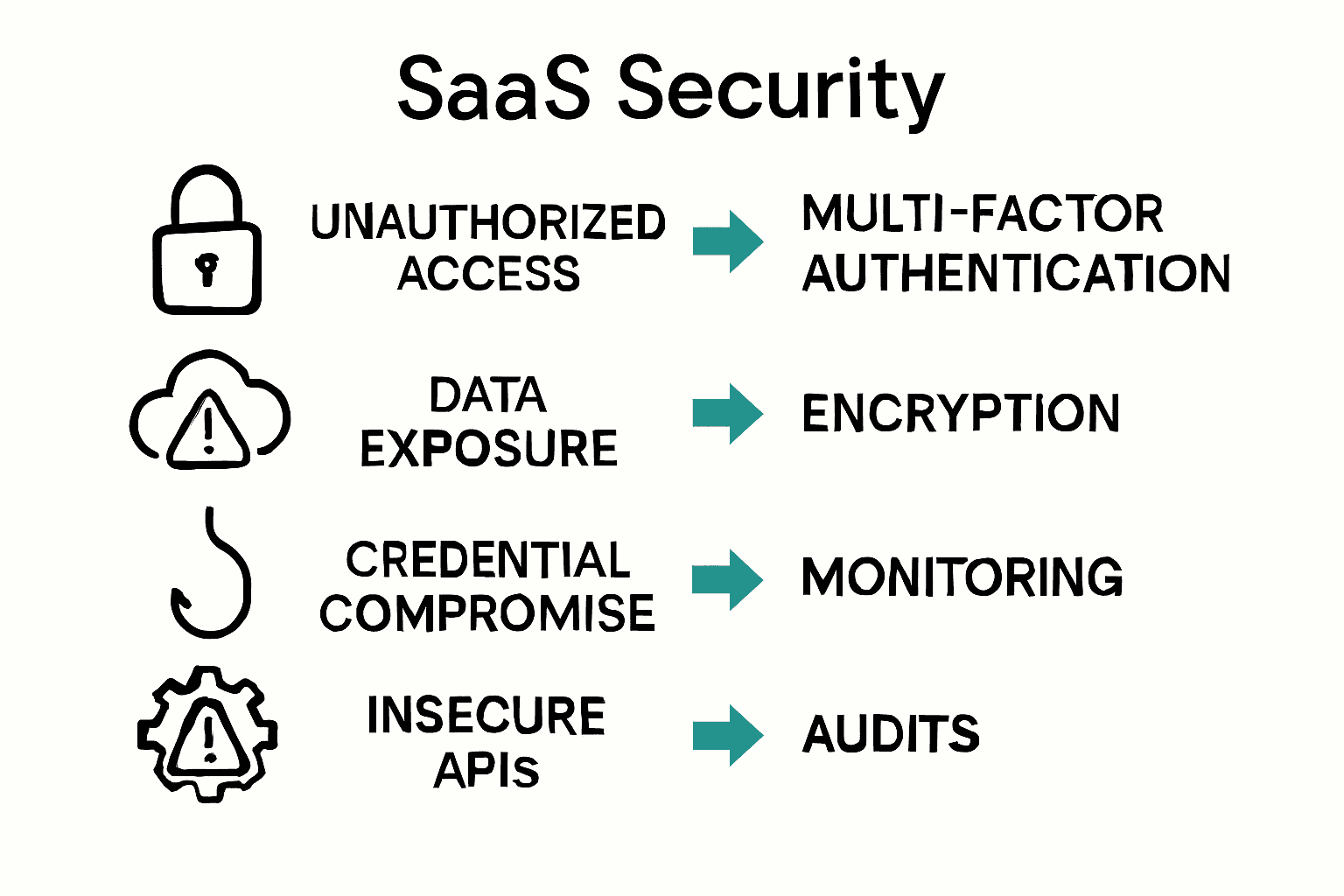
In the rapidly evolving digital landscape, SaaS security threats represent sophisticated challenges that can compromise organizational data integrity and operational continuity. Cloud Security Alliance identifies key vulnerabilities inherent in cloud environments, particularly around data exposure from persistent external data shares and dynamic cloud infrastructures with frequent configuration changes.
The most prevalent SaaS security threats can be categorized into several critical domains that demand comprehensive mitigation strategies. According to Cloud Security Alliance, significant risks emerge from unchecked data access permissions that create potential pathways for unauthorized system penetration.
Key SaaS security threat categories include:
Here's a summary comparing the major types of SaaS security threats:
| Threat Category | Description | Common Example |
|---|---|---|
| Unauthorized Access | Weak authentication or overshared permissions | Excessive admin privileges |
| Data Exposure | Misconfigured cloud settings | Publicly exposed data |
| Credential Compromise | Phishing or stolen credentials | Email phishing attacks |
| Insecure APIs | Vulnerabilities in system integrations | Poorly secured API endpoints |
| Compliance Violations | Breach of legal or regulatory standards | Non-compliance with GDPR |
- Unauthorized Access Risks: Weak authentication mechanisms and indefinite sharing permissions
- Data Exposure Vulnerabilities: Misconfigured cloud settings enabling unintended data visibility
- Credential Compromise: Phishing attacks and stolen login credentials
- Insecure APIs: Integration points that can be exploited by malicious actors
- Compliance Violations: Unintentional breaches of regulatory requirements
Successful threat mitigation requires a proactive, multilayered approach that combines technological solutions, continuous monitoring, and robust organizational policies. Enterprises must develop adaptive security frameworks that can quickly identify, isolate, and neutralize potential risks before they escalate into significant breaches.
How SaaS Security Works in Practice
SaaS security operates through a complex, multilayered approach that requires continuous vigilance and strategic implementation. Cloud Security Alliance emphasizes the critical importance of meticulous application configuration, particularly in preventing potential security vulnerabilities such as excessive administrative privileges that could lead to unauthorized system access.
In practical implementation, SaaS security involves a comprehensive framework of technical and organizational controls. UMA Technology highlights the necessity of addressing complex risk domains including data breaches, insider threats, and potential misconfigurations through rigorous access management and persistent monitoring strategies.
Key practical implementation strategies include:
- Identity and Access Management: Implementing multi-factor authentication and granular permission controls
- Continuous Monitoring: Real-time threat detection and automated security alerting systems
- Data Encryption: Protecting sensitive information both in transit and at rest
- Regular Security Audits: Comprehensive assessments of system configurations and potential vulnerabilities
- Compliance Validation: Ensuring alignment with industry-specific security standards and regulations
For enterprises seeking to enhance their SaaS security posture, a tutorial on SOC 2 compliance can provide deeper insights into establishing robust security frameworks. Successful implementation requires a proactive, adaptive approach that anticipates emerging threats and continuously evolves security protocols to maintain optimal protection.
Best Practices for Enterprise SaaS Protection
Enterprise SaaS protection demands a strategic, comprehensive approach that goes beyond basic security measures. Stanford UIT emphasizes the critical importance of developing robust product selection workflows and comprehensive pre-implementation planning to safeguard organizational data and systems effectively.
Cloud Security Alliance highlights the paramount significance of avoiding common configuration vulnerabilities that can compromise system integrity. This requires meticulous attention to administrative privilege management and systematic security protocol implementation.
Core best practices for enterprise SaaS protection include:
- Comprehensive Vendor Assessment: Rigorous evaluation of potential SaaS providers' security credentials
- Zero Trust Architecture: Implementing strict access controls and continuous authentication
- Advanced Encryption Protocols: Protecting data transmission and storage with cutting-edge encryption technologies
- Regular Security Audits: Conducting periodic comprehensive assessments of system vulnerabilities
- Incident Response Planning: Developing robust strategies for rapid threat detection and mitigation
To further enhance your vendor risk management approach, our guide to third-party vendor risk assessment provides additional insights into creating a resilient security ecosystem. Successful SaaS protection is an ongoing process that requires continuous adaptation, proactive monitoring, and a commitment to maintaining the highest standards of cybersecurity resilience.
Compliance Requirements and Integration Challenges
SaaS compliance represents a complex landscape of regulatory requirements and technical integration challenges that enterprises must navigate carefully. UMA Technology emphasizes the critical need for organizations to ensure their SaaS solutions align with stringent regulatory frameworks like GDPR and HIPAA, while simultaneously addressing potential technical vulnerabilities such as misconfigured cloud settings and insecure API endpoints.
Cloud Security Alliance underscores the importance of continuous monitoring and comprehensive lifecycle management for shared data, highlighting the dynamic nature of cloud environments that demand persistent vigilance and adaptive security strategies.
Key compliance and integration challenges include:
- Regulatory Alignment: Ensuring complete adherence to industry-specific security standards
- Data Privacy Management: Protecting sensitive information across distributed cloud environments
- API Security: Securing integration points and preventing unauthorized data access
- Cross-Platform Compatibility: Managing seamless and secure interactions between different SaaS platforms
- Continuous Monitoring: Implementing real-time threat detection and compliance validation mechanisms
For enterprises seeking to streamline their compliance efforts, our guide to creating a SOC 2 compliance checklist offers a structured approach to navigating these complex technological and regulatory landscapes. Successful compliance is not a destination but an ongoing journey of adaptation, vigilance, and proactive risk management.
Enhance Your Enterprise SaaS Security with Smarter Automation
Protecting your organization against SaaS security threats starts with fast and accurate responses to essential security questionnaires. The challenges of managing complex access controls, continuous monitoring, and compliance demands require a streamlined approach that prevents delays and miscommunication. Skypher understands these pain points and offers an AI-driven Questionnaire Automation Tool that dramatically reduces the time and effort needed to complete security reviews.
Our platform supports multiple formats and integrates seamlessly with over 40 third-party risk management systems, including popular tools like ServiceNow and Slack. With real-time collaboration and a customizable Trust Center, your teams can maintain tight control over data exposure risks and compliance requirements while improving operational productivity.
Ready to accelerate your SaaS security processes and build stronger client trust?

Discover how Skypher’s cutting-edge AI automation can transform your security questionnaire workflows today. Start optimizing your SaaS protection strategy now at Skypher. Learn more about our AI Questionnaire Automation Tool and explore best practices in managing third-party vendor risk assessment to safeguard your enterprise comprehensively.
Frequently Asked Questions
What is SaaS security and why is it important?
SaaS security encompasses strategies, practices, and technologies that protect cloud-based applications and sensitive data. It is crucial for safeguarding organizational data integrity and ensuring regulatory compliance in the cloud environment.
What are the main types of threats to SaaS security?
Common threats to SaaS security include unauthorized access, data exposure due to misconfigurations, credential compromise through phishing attacks, insecure APIs, and compliance violations. Each of these vulnerabilities requires strategic mitigation efforts.
How can enterprises implement effective SaaS security measures?
Entering a comprehensive SaaS security framework involves implementing identity and access management, continuous monitoring, data encryption, regular security audits, and maintaining compliance with industry regulations.
What are best practices for ensuring compliance in SaaS applications?
Best practices for SaaS compliance include performing comprehensive vendor assessments, employing a Zero Trust Architecture, utilizing advanced encryption protocols, conducting regular security audits, and having an incident response plan in place.
