The importance of cybersecurity in today's digital landscape cannot be overstated. A staggering 72% of large businesses have experienced data breaches, highlighting the urgent need for organizations to demonstrate strong data protection practices. But here’s the twist: many people underestimate the profound impact that a simple compliance report can have on their business. While SOC 2 Type 2 certification may seem like just another regulatory hurdle, it actually signifies a robust commitment to security that can differentiate an organization in a crowded market. This certification is not just about meeting standards; it's about building trust and establishing a competitive edge in an increasingly security-conscious world.
Table of Contents
- What Is Soc 2 Type 2 Compliance
- Soc 2 Type 2 Vs Soc 2 Type 1
- Who Needs A Soc 2 Type 2 Report
- Steps To Achieve Soc 2 Type 2
- Benefits Of Soc 2 Type 2 Certification
Quick Summary
| Takeaway | Explanation |
|---|---|
| Understanding SOC 2 Type 2 Compliance | SOC 2 Type 2 compliance is essential for organizations to demonstrate strong cybersecurity practices through a continuous evaluation of security controls, covering a six to twelve-month audit period. |
| Differences Between SOC 2 Type 1 and Type 2 | SOC 2 Type 1 offers a snapshot of security controls at a specific moment, while SOC 2 Type 2 assesses their operational effectiveness over time, making Type 2 certification more credible and comprehensive. |
| Key Industries for SOC 2 Type 2 Reports | Organizations in sectors such as cloud services, FinTech, healthcare technology, and SaaS need SOC 2 Type 2 reports to meet client demands and regulatory requirements, signaling commitment to data security. |
| Steps to Achieve SOC 2 Type 2 Compliance | Achieving compliance involves preparing foundational documentation, implementing secure controls, and maintaining ongoing audits, emphasizing continuous monitoring of security practices. |
| Benefits of SOC 2 Type 2 Certification | Certification enhances trust, offers competitive advantages, and leads to long-term improvements in internal processes, risk management, and stakeholder confidence, making it a strong asset for organizations seeking to stand out. |
What is SOC 2 Type 2 Compliance?
In the complex landscape of cybersecurity and data protection, SOC 2 Type 2 compliance represents a critical standard for organizations committed to demonstrating robust security practices and earning client trust. SOC 2, which stands for Service Organization Control 2, is a rigorous framework developed by the American Institute of Certified Public Accountants (AICPA) that evaluates an organization's information security management systems and controls.
Understanding the SOC 2 Type 2 Audit Process
Unlike its counterpart SOC 2 Type 1, which assesses control design at a single point in time, a SOC 2 Type 2 audit provides a comprehensive evaluation of both control design and operational effectiveness over an extended period. Typically spanning six to twelve months, this audit involves a meticulous examination of an organization's security controls across five key trust service criteria: security, availability, processing integrity, confidentiality, and privacy.
During the audit, independent third-party certified public accountants conduct an in-depth review of the organization's systems, policies, and procedures. They don't just look at documentation but actively test and verify that these controls are consistently implemented and functioning as intended. Drata notes that this approach provides a more comprehensive and credible assessment of an organization's security posture.
Key Components of SOC 2 Type 2 Compliance
Achieving SOC 2 Type 2 compliance requires organizations to demonstrate a systematic approach to managing and protecting sensitive information. The process involves several critical elements:
- Comprehensive Documentation: Organizations must provide detailed evidence including a management assertion, system description, and a comprehensive control matrix.
- Continuous Monitoring: Implementing ongoing security practices that consistently meet the established trust criteria.
- Independent Verification: Allowing external auditors to thoroughly examine and validate the effectiveness of internal controls.
According to Secureframe, the compliance process is not a one-time event but a continuous commitment to maintaining high standards of information security. The resulting SOC 2 Type 2 report becomes a powerful tool for organizations to demonstrate their reliability to potential clients, partners, and stakeholders.
For businesses operating in sectors handling sensitive data—such as cloud service providers, financial technology companies, and healthcare software vendors†SOC 2 Type 2 certification is not just a recommendation but often a critical requirement. AuditBoard highlights that this certification serves as a competitive differentiator, signaling to clients that an organization takes data protection and security seriously.
While the path to SOC 2 Type 2 compliance can be complex and demanding, it offers significant benefits. Organizations that successfully navigate this process gain enhanced credibility, improved security practices, and a structured approach to managing technological risks in an increasingly interconnected digital landscape.
SOC 2 Type 2 vs. SOC 2 Type 1
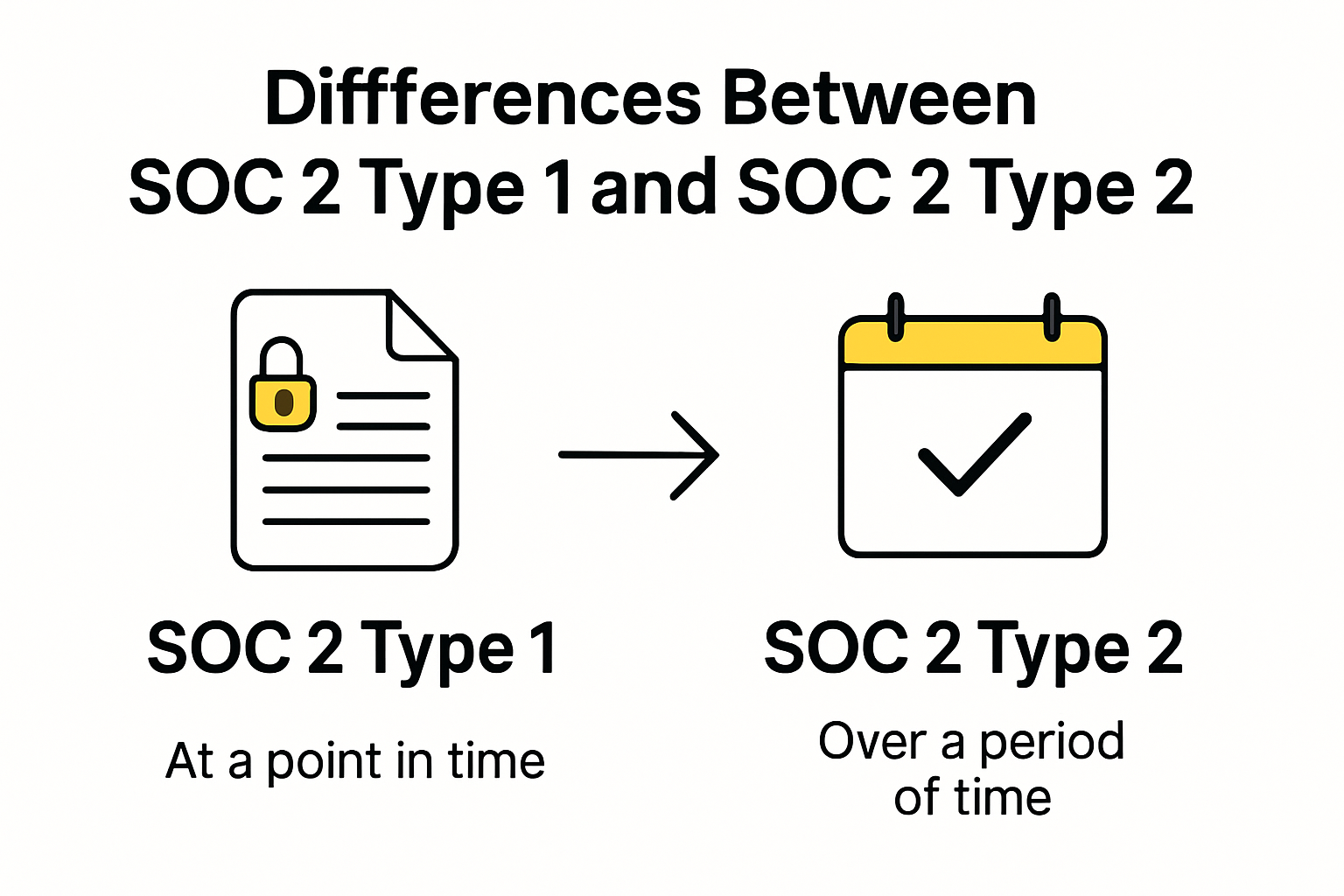
In the realm of cybersecurity and compliance, SOC 2 Type 1 and SOC 2 Type 2 represent two distinct approaches to assessing an organization's information security controls. While they share a common framework, these audit types differ significantly in scope, depth, and the level of assurance they provide to stakeholders.
Fundamental Differences in Audit Approach
SOC 2 Type 1 is essentially a snapshot assessment that examines the design of an organization's controls at a specific point in time. AuditBoard explains that this type of audit focuses on whether security controls are appropriately configured and implemented according to predefined standards. In contrast, SOC 2 Type 2 offers a more comprehensive evaluation, tracking the actual operational effectiveness of these controls over an extended period—typically six to twelve months.
Think of SOC 2 Type 1 as a quick health check, while SOC 2 Type 2 is more like a thorough medical examination that monitors performance over time. The Type 2 audit provides a much deeper and more credible assessment of an organization's security practices. StandardFusion notes that larger, security-conscious organizations and those in regulated industries typically prefer the more rigorous Type 2 certification.
Practical Implications and Strategic Considerations
The choice between SOC 2 Type 1 and Type 2 depends on several strategic factors:
- Initial Compliance: Type 1 serves as an excellent starting point for organizations beginning their compliance journey, offering a faster and less resource-intensive option.
- Depth of Assurance: Type 2 provides a more comprehensive view of control effectiveness, demonstrating sustained commitment to security.
- Stakeholder Requirements: Some clients and partners specifically request Type 2 reports as proof of robust, consistent security practices.
Key differences emerge in several critical areas:
- Time Investment: Type 1 audits are conducted at a single point in time, while Type 2 audits span 6-12 months.
- Operational Proof: Type 2 requires demonstrating that controls work consistently over an extended period.
- Credibility: Type 2 reports carry more weight with potential clients and partners due to their comprehensive nature.
For many organizations, SOC 2 Type 1 serves as an initial step towards more comprehensive security certification. It provides a baseline assessment of control design and helps identify potential security gaps. However, StandardFusion emphasizes that most organizations ultimately aim for Type 2 certification to demonstrate a sustained commitment to security.
The cost and complexity increase from Type 1 to Type 2 is significant. Type 2 audits require more extensive documentation, continuous monitoring, and a proven track record of maintaining security controls. Organizations must be prepared to invest considerable time and resources in preparing for and maintaining Type 2 compliance.
Ultimately, the choice between SOC 2 Type 1 and Type 2 depends on an organization's specific needs, industry requirements, and strategic goals. While Type 1 offers a quick initial assessment, Type 2 provides the gold standard of security assurance—a comprehensive, long-term demonstration of an organization's commitment to protecting sensitive information.
Who Needs a SOC 2 Type 2 Report?
In today's digital landscape, SOC 2 Type 2 reports have become a critical benchmark for organizations demonstrating their commitment to robust cybersecurity and data protection practices. While not universally mandatory, these reports have emerged as a gold standard for businesses handling sensitive customer information across various industries.
Industries Prioritizing SOC 2 Type 2 Compliance
Microsoft's Compliance Guide highlights that SOC 2 Type 2 reports are especially crucial for organizations in specific sectors that manage substantial volumes of customer data. Key industries include:
- Cloud Service Providers: Companies offering infrastructure, platform, or software-as-a-service solutions
- Financial Technology (FinTech): Online payment processors, digital banking platforms, and investment management systems
- Healthcare Technology: Electronic health record systems, telemedicine platforms, and medical billing software
- Software-as-a-Service (SaaS) Companies: Enterprise software providers handling confidential business data
Determining Organizational Readiness
Not every organization requires a SOC 2 Type 2 report, but certain indicators suggest it might be necessary. According to Drata, organizations should consider pursuing SOC 2 Type 2 compliance if they:
- Store or process customer data in cloud environments
- Have enterprise clients requesting security documentation
- Operate in regulated industries with strict data protection requirements
- Want to differentiate themselves from competitors through demonstrated security practices
Strategic Implications of SOC 2 Type 2 Reporting
Beyond regulatory compliance, SOC 2 Type 2 reports serve critical business functions. StandardFusion emphasizes that many enterprise procurement departments now require vendors to provide current SOC 2 Type 2 reports before initiating or renewing business relationships.
For technology service providers, a SOC 2 Type 2 report acts as a powerful trust signal. It demonstrates to potential clients that the organization has not just designed security controls, but consistently maintains them over an extended period. This continuous commitment becomes particularly important in industries where data breaches can result in significant financial and reputational damage.
Startups and emerging technology companies often view SOC 2 Type 2 compliance as a competitive differentiator. By proactively obtaining this certification, they can:
- Accelerate sales cycles with enterprise customers
- Build immediate credibility in competitive markets
- Demonstrate a mature approach to information security
- Potentially reduce cybersecurity insurance costs
While smaller organizations or those with limited customer data might not immediately need a SOC 2 Type 2 report, businesses experiencing rapid growth or targeting enterprise customers should seriously consider pursuing this certification. The investment in comprehensive security practices often yields substantial returns through increased customer trust and expanded market opportunities.
Ultimately, SOC 2 Type 2 reports are not just about compliance—they represent an organization's fundamental commitment to protecting the most valuable asset in the digital age: customer data. For businesses serious about establishing themselves as trustworthy, transparent, and technologically sophisticated, a SOC 2 Type 2 report is increasingly becoming an essential credential.
Steps to Achieve SOC 2 Type 2
Achieving SOC 2 Type 2 compliance is a comprehensive journey that requires strategic planning, meticulous documentation, and a sustained commitment to robust information security practices. Organizations must navigate a complex landscape of controls, assessments, and ongoing monitoring to successfully obtain this critical certification.
Preparing the Foundation
AuditBoard emphasizes that the initial phase of SOC 2 Type 2 compliance involves establishing a solid framework across five key trust service criteria: Security, Availability, Processing Integrity, Confidentiality, and Privacy. This preparation requires organizations to:
- Conduct a comprehensive internal security assessment
- Identify existing gaps in current security controls
- Develop a detailed roadmap for implementing necessary improvements
- Create comprehensive documentation of security policies and procedures
Preparing for SOC 2 Type 2 audit involves assembling three critical documents: a management assertion, a system description, and a controls matrix. Sprinto highlights that these documents serve as the backbone of demonstrating an organization's commitment to maintaining rigorous security standards.
Implementing and Documenting Controls
The implementation phase is where organizations translate their security strategies into actionable controls. This involves:
- Developing Robust Policies: Creating detailed, comprehensive security policies that address each of the trust service criteria
- Technical Control Implementation: Installing and configuring technical safeguards such as:
- Multi-factor authentication
- Encryption protocols
- Access control mechanisms
- Continuous monitoring systems
- Employee Training: Ensuring all team members understand and can consistently follow established security protocols
Microsoft's Compliance Guide recommends a systematic approach to control implementation, focusing on creating repeatable, documented processes that can be consistently demonstrated over the audit period.
Audit Preparation and Ongoing Compliance
The final stage involves preparing for the actual SOC 2 Type 2 audit and maintaining compliance. This critical phase includes:
- Engaging an independent certified public accountant (CPA) specializing in SOC 2 audits
- Conducting internal readiness assessments
- Preparing comprehensive documentation of control effectiveness
- Demonstrating consistent implementation of security controls over 6-12 months
Organizations must recognize that SOC 2 Type 2 compliance is not a one-time achievement but an ongoing commitment. The audit process requires proving that implemented controls work effectively and consistently over an extended period. This means continuous monitoring, regular internal assessments, and a proactive approach to addressing potential security vulnerabilities.
The journey to SOC 2 Type 2 compliance can be complex and resource-intensive. However, the benefits far outweigh the challenges. Organizations that successfully navigate this process gain significant competitive advantages, including enhanced customer trust, improved internal security practices, and a robust framework for protecting sensitive information.
 Ultimately, achieving SOC 2 Type 2 compliance is about more than just passing an audit—it's about demonstrating a genuine, sustained commitment to information security and building trust with customers, partners, and stakeholders.
Ultimately, achieving SOC 2 Type 2 compliance is about more than just passing an audit—it's about demonstrating a genuine, sustained commitment to information security and building trust with customers, partners, and stakeholders.
Benefits of SOC 2 Type 2 Certification
In an era of escalating cybersecurity threats and increasing data privacy concerns, SOC 2 Type 2 certification has emerged as a powerful strategic asset for organizations seeking to establish trust, enhance security, and differentiate themselves in competitive markets.
Trust and Credibility Enhancement
Secureframe reveals a startling statistic: 72% of large businesses and 28% of small businesses have experienced data breaches, underscoring the critical importance of robust security certifications. SOC 2 Type 2 certification serves as a powerful trust signal, demonstrating an organization's commitment to comprehensive, consistently applied security practices.
For potential clients and partners, this certification represents more than a mere compliance document. It's a tangible proof of an organization's dedication to protecting sensitive data, managing risks, and maintaining high standards of operational integrity. Gallagher Security emphasizes that the certification acts as a symbol of transparency, providing independent validation of an organization's security controls.
Competitive and Strategic Advantages
Beyond trust-building, SOC 2 Type 2 certification offers significant strategic benefits:
- Market Differentiation: Organizations with SOC 2 Type 2 certification stand out in crowded markets, particularly in technology and service-driven industries
- Sales Acceleration: Many enterprise clients require this certification before engaging in business relationships
- Risk Mitigation: Proactive identification and remediation of potential security vulnerabilities
- Potential Cost Savings: Reduced cybersecurity insurance premiums and decreased likelihood of costly data breaches
RSI Security highlights that the certification not only protects organizations from potential reputational damage but also demonstrates a mature, systematic approach to information security management.
Long-Term Organizational Benefits
The SOC 2 Type 2 certification process drives meaningful internal improvements beyond external perception. By systematically evaluating and documenting security controls, organizations gain:
- Enhanced Internal Processes: Comprehensive review and optimization of security protocols
- Continuous Improvement Culture: Regular assessments that encourage ongoing security refinement
- Comprehensive Risk Management: Structured approach to identifying and mitigating potential security risks
- Improved Stakeholder Confidence: Tangible evidence of commitment to data protection and operational excellence
The certification's rigorous requirements compel organizations to develop robust, repeatable security practices. This isn't just about passing an audit—it's about fundamentally strengthening an organization's technological infrastructure and risk management capabilities.
While achieving SOC 2 Type 2 certification requires significant investment of time and resources, the returns extend far beyond compliance. Organizations that successfully navigate this process gain a comprehensive framework for protecting sensitive information, building customer trust, and demonstrating technological sophistication in an increasingly complex digital landscape.
Ultimately, SOC 2 Type 2 certification represents more than a credential—it's a strategic commitment to excellence, transparency, and responsible data stewardship in the digital age.
Frequently Asked Questions
What is SOC 2 Type 2 compliance?
SOC 2 Type 2 compliance is a standard for organizations to demonstrate robust cybersecurity practices through a comprehensive evaluation of security controls over a period of six to twelve months.
How does SOC 2 Type 2 differ from SOC 2 Type 1?
SOC 2 Type 1 provides a snapshot of an organization's security controls at a specific point in time, while SOC 2 Type 2 evaluates the effectiveness of those controls over a longer, continuous audit period.
Which industries need SOC 2 Type 2 certification?
Industries that typically require SOC 2 Type 2 certification include cloud service providers, financial technology (FinTech), healthcare technology, and Software-as-a-Service (SaaS) companies that handle sensitive customer data.
What are the benefits of obtaining SOC 2 Type 2 certification?
Benefits include enhanced trust with clients, a competitive edge in the market, improved internal security practices, and reduced risks associated with data breaches.
Elevate Your Security Compliance with Skypher
In today's digital landscape, achieving SOC 2 Type 2 compliance is a demanding yet essential journey for organizations committed to safeguarding sensitive information. The pressure is on: with 72% of large businesses experiencing data breaches, demonstrating robust security practices isn’t just beneficial—it’s crucial. This is where many organizations struggle. Completing complex security questionnaires can be time-consuming and prone to errors, leaving teams overwhelmed. That's where Skypher comes in!

Imagine a solution that transforms your compliance process from chaotic to seamless. Our AI Questionnaire Automation Tool simplifies security reviews, helping you complete them significantly faster and with higher accuracy. By integrating with over 40 TPRM platforms, our solution enhances collaboration and communication among teams, ensuring every detail is attended to while you focus on securing trust with your clients. Don’t let the complexities of compliance stall your progress; empower your organization to achieve SOC 2 Type 2 certification with confidence. Visit Skypher now to streamline your security questionnaire response process and elevate your cybersecurity posture today!