In today's digital era, cybersecurity is more crucial than ever. With cyber attacks on the rise, organizations must rethink their security strategies. A staggering 70 percent of breaches result from compromised credentials. But here's the twist: adopting a zero trust security model can significantly reduce this risk. Unlike traditional methods that often provide users blanket access, zero trust focuses on continuous verification and strict access controls. This approach not only enhances protection but also strengthens overall business resilience.
Table of Contents
- Understanding The Principles Of Zero Trust
- Key Benefits Of A Zero Trust Model
- How Zero Trust Architecture Works
- Implementing Zero Trust Step-By-Step
Quick Summary
| Takeaway | Explanation |
|---|---|
| Zero Trust Embraces Continuous Verification | Zero trust security operates on the principle of 'never trust, always verify,' ensuring that every access request is thoroughly authenticated and authorized at all times. |
| Implementation Requires a Holistic Strategy | Transitioning to a zero trust model involves a comprehensive transformation of an organization’s cybersecurity architecture, focusing on robust identity management, device security, and micro-segmentation. |
| Enhanced Security Reduces Vulnerabilities | By enforcing strict access controls and implementing real-time threat detection, organizations can significantly minimize their attack surface and enhance overall resilience against cyber threats. |
| Cultural Shift is Crucial for Success | Successful zero trust implementation necessitates an ongoing cultural transformation within organizations, encouraging continuous reassessment of security policies and employee training on new protocols. |
| Adaptability to Emerging Threats is Key | A dynamic security environment created through zero trust architecture allows organizations to quickly respond to sophisticated cyber threats, ensuring ongoing protection of valuable digital assets. |
Understanding the Principles of Zero Trust
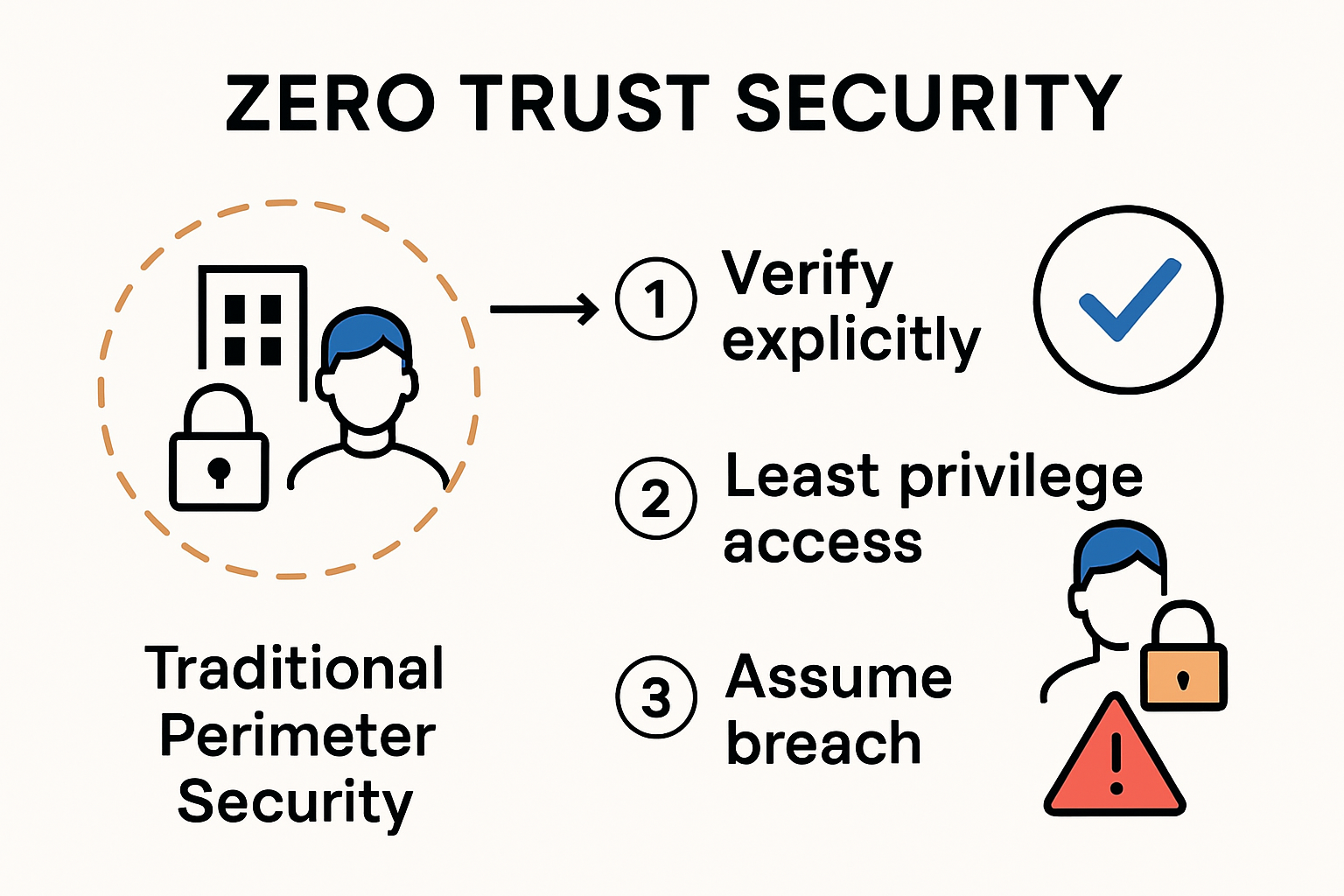
In the rapidly evolving landscape of cybersecurity, zero trust security represents a fundamental paradigm shift from traditional network defense strategies. Unlike conventional security models that operate on the assumption of internal network safety, zero trust embraces a more rigorous approach: "never trust, always verify."
The Core Philosophy of Zero Trust
Zero trust is not just a technology, but a comprehensive security model that challenges the outdated perimeter-based security framework. The U.S. Department of Homeland Security emphasizes that no implicit trust should be granted to assets or user accounts based solely on their location or ownership. Every single access request must be thoroughly verified, authorized, and encrypted.
The fundamental principles driving zero trust include:
- Least Privilege Access: Users and systems are granted minimal access rights necessary to perform their specific tasks
- Continuous Verification: Identity and device health are constantly re-evaluated
- Micro-segmentation: Network resources are divided into small, manageable segments to limit potential breach impacts
Implementation and Strategic Approach
Cloud Security Alliance research highlights that implementing zero trust requires a holistic strategy beyond simple technological solutions. Organizations must redesign their entire security architecture to create a dynamic, adaptive environment that can respond to emerging threats in real-time.
Key implementation strategies include:
- Comprehensive asset and user inventory
- Multi-factor authentication
- Real-time threat detection and response mechanisms
- Encryption of all network traffic
Transforming Cybersecurity Landscape
Zero trust transforms traditional security paradigms by treating every network connection as potentially hostile. Instead of maintaining a hard external shell with a soft interior, zero trust creates multiple layers of security verification throughout the entire digital ecosystem. This approach significantly reduces potential attack surfaces and provides granular control over access and data movement.
By assuming that threats can emerge from both external and internal sources, zero trust security mandates continuous authentication, strict access controls, and rapid incident response capabilities. The model ensures that even if a breach occurs, its potential damage is minimized through precise, context-aware security protocols.
As cyber threats become increasingly sophisticated, zero trust is not just a recommendation—it's becoming a critical necessity for organizations seeking to protect their most valuable digital assets.
Key Benefits of a Zero Trust Model
In today's hyper-connected digital landscape, organizations face unprecedented cybersecurity challenges that demand more sophisticated defense mechanisms. The zero trust security model emerges as a powerful strategy, offering comprehensive protection that goes far beyond traditional perimeter-based approaches.
Enhanced Security and Risk Mitigation

Forrester Research highlights that Zero Trust significantly amplifies business resilience by creating a more robust security framework. By enforcing strict access controls and continuous verification, organizations can dramatically reduce their vulnerability to sophisticated cyber threats.
Key security enhancements include:
- Minimized Attack Surface: Reducing potential entry points for malicious actors
- Granular Access Controls: Precise management of user and system permissions
- Comprehensive Threat Detection: Real-time monitoring and immediate response capabilities
Operational Efficiency and Flexibility
The Cloud Security Alliance emphasizes that Zero Trust is not just a security strategy, but a transformative approach to organizational IT infrastructure. The model supports secure integration of emerging technologies while maintaining exceptional user experiences.
Operational benefits encompass:
- Streamlined authentication processes
- Reduced complexity in security management
- Improved compliance with regulatory requirements
- Seamless support for remote and hybrid work environments
Business Resilience and Strategic Advantage
Zero Trust goes beyond traditional defensive strategies by transforming security from a potential business inhibitor to a strategic enabler. The Department of Homeland Security recognizes that this approach allows organizations to confidently expand into new markets and digital ecosystems.
The model provides critical advantages:
- Proactive threat prevention
- Reduced financial risks associated with data breaches
- Enhanced customer and stakeholder trust
- Adaptability to evolving technological landscapes
By treating every access request as potentially suspicious, Zero Trust creates a dynamic security environment that adapts in real-time. This approach ensures that organizations can protect their most valuable digital assets while maintaining the agility necessary to compete in today's rapidly changing business world.
As cyber threats continue to grow in sophistication, Zero Trust is not merely a technological choice—it's a strategic imperative for organizations committed to robust, future-proof security architecture.
How Zero Trust Architecture Works
Zero Trust architecture represents a sophisticated approach to cybersecurity that fundamentally transforms how organizations manage digital access and protect their resources. Unlike traditional security models, zero trust security operates on a dynamic, context-aware principle that assumes no inherent trust, even within internal networks.
Core Architectural Components
NIST Special Publication 800-207 defines Zero Trust Architecture as an abstract approach requiring continuous authentication, authorization, and validation for every access request. The architecture consists of several critical components working in concert:
- Policy Decision Point (PDP): Central control mechanism that evaluates access requests
- Policy Enforcement Point (PEP): Implements and enforces access decisions
- Continuous Verification Mechanisms: Real-time assessment of user identity, device health, and context
Technical Implementation Strategies
Research from the National Institutes of Health reveals that Zero Trust implementation combines multiple advanced technologies to create a robust security ecosystem. These technologies work together to create a dynamic, adaptive security environment:
- Lightweight Authentication: Multi-factor authentication and adaptive identity verification
- Fine-Grained Access Control: Granular permissions based on user roles, device status, and contextual factors
- Microsegmentation: Dividing network resources into small, isolated segments to limit potential breach impacts
- Data Encryption: Protecting data in transit and at rest with advanced cryptographic techniques
Dynamic Trust Assessment Mechanism
The Zero Trust model fundamentally differs from traditional security approaches by treating every access request as potentially suspicious. Instead of establishing a trusted internal network and untrusted external environment, Zero Trust creates a continuous verification loop that dynamically assesses multiple factors:
- User identity and authentication history
- Device security posture and compliance
- Network and application context
- Historical access patterns
- Real-time threat intelligence
This approach ensures that access is never permanently granted but continually re-evaluated. If any anomaly is detected—such as an unusual login location, unexpected device configuration, or suspicious network behavior—access can be immediately restricted or denied.
By implementing these sophisticated architectural principles, organizations can create a resilient security framework that adapts in real-time to emerging threats. Zero Trust transforms security from a static, perimeter-based model to a dynamic, intelligent system that protects critical assets with unprecedented precision and flexibility.
As cyber threats become increasingly complex, Zero Trust architecture represents not just a technological solution, but a fundamental reimagining of digital security strategies.
Implementing Zero Trust Step-by-Step
Transitioning to a zero trust security model requires a strategic, methodical approach that goes beyond simple technological implementation. Organizations must carefully plan and execute a comprehensive transformation of their cybersecurity infrastructure.
Assessing Current Security Landscape
NIST Special Publication 800-207 recommends beginning with a comprehensive assessment of existing security environments. This initial phase involves:
- Conducting a thorough inventory of all digital assets
- Mapping current network and data flows
- Identifying potential vulnerabilities and access points
- Evaluating existing authentication and authorization mechanisms
Organizations must develop a clear understanding of their current security posture before implementing Zero Trust principles. This baseline assessment provides critical insights into the transformation required.
Phased Implementation Strategy
Research from Boise State University highlights a modular approach to Zero Trust implementation, focusing on five core pillars:
- Identity Management: Implementing robust multi-factor authentication
- Device Security: Establishing continuous device health verification
- Network Environment: Creating microsegmentation and granular access controls
- Application Workload: Securing individual application access
- Data Protection: Encrypting and controlling data access at granular levels
Key implementation steps include:
- Prioritize critical assets and high-risk areas
- Develop comprehensive access policies
- Deploy advanced authentication mechanisms
- Implement continuous monitoring systems
Technology and Cultural Transformation
National Institutes of Health research emphasizes that successful Zero Trust implementation requires more than technological solutions—it demands a fundamental cultural shift in organizational approach to security.
Critical technological components include:
- Advanced identity and access management systems
- Continuous authentication technologies
- Context-aware access control mechanisms
- Real-time threat detection and response platforms
The implementation process is not a one-time event but an ongoing journey of continuous improvement. Organizations must:
- Regularly reassess and update security policies
- Train employees on new security protocols
- Maintain flexibility in security architecture
- Continuously monitor and adapt to emerging threats
Successful Zero Trust implementation transforms security from a static defense mechanism to a dynamic, adaptive system. By treating each access request as potentially suspicious and requiring continuous verification, organizations can significantly reduce their vulnerability to sophisticated cyber threats.
Ultimately, Zero Trust is not just a technology strategy, but a comprehensive approach to protecting digital assets in an increasingly complex and interconnected technological landscape.
Frequently Asked Questions
What is Zero Trust Security?
Zero Trust Security is a cybersecurity model that operates on the principle of 'never trust, always verify.' It requires continuous authentication and strict access controls for every request, regardless of whether it originates from inside or outside the organization.
What are the key principles of Zero Trust?
The key principles of Zero Trust include least privilege access, continuous verification of users and devices, and micro-segmentation of networks to limit the impact of potential breaches.
How does Zero Trust enhance organizational security?
Zero Trust enhances security by minimizing the attack surface, implementing granular access controls, and enabling real-time threat detection, which collectively reduce vulnerabilities to sophisticated cyber threats.
What steps are involved in implementing a Zero Trust model?
Implementing a Zero Trust model involves assessing the current security landscape, following a phased implementation strategy focusing on identity management and device security, and fostering a cultural transformation towards ongoing security assessment and training.
Elevate Your Security with Skypher's Zero Trust Solutions
As cyber threats continue to evolve, adopting a Zero Trust security model is essential for organizations seeking to protect their critical assets. Thankfully, achieving maximum security doesn’t have to be an uphill battle. With Skypher's AI-driven Questionnaire Automation Tool, you can implement and maintain a robust security posture while streamlining the process of managing security questionnaires. Our platform empowers you to quickly assess risks using real-time collaboration and customize your own Trust Center, ensuring that every access request—whether internal or external—is meticulously verified.

Don’t let the challenges of Zero Trust implementation overwhelm you! Our solution not only enhances your cybersecurity strategy but also boosts efficiency in your teams' responses and communication. Join the ranks of savvy organizations in the tech and finance sectors today! Visit https://skypher.co and see how we can transform your security processes, making every access decision more secure and informed. Your journey towards a resilient cyber defense starts NOW!