Data breaches in SaaS applications cost an average of $5.4 million, yet many organizations underestimate the complexity of securing cloud platforms. You face multifaceted threats ranging from architectural flaws to human error, each capable of exposing sensitive customer data. This guide equips IT security professionals and compliance officers with actionable strategies for managing SaaS cybersecurity risks through proper data isolation, compliance frameworks, and automation. You'll learn how to strengthen your security posture, reduce audit costs, and minimize the human factors that cause most incidents. By implementing these proven practices, you can protect your organization from costly breaches while improving operational efficiency.
Table of Contents
- Understanding SaaS Cybersecurity Risks And Data Isolation
- Leveraging Compliance Frameworks To Strengthen SaaS Security
- Mitigating Human Error And Operational Risks In SaaS Cybersecurity
- Applying Automation And Best Practices For Enhancing SaaS Cybersecurity Posture
- Enhance Your SaaS Security With Skypher Automation Tools
- Frequently Asked Questions
Key takeaways
| Point | Details |
|---|---|
| Data isolation prevents breaches | Proper architecture stops 90% of SaaS security flaws from cascading across customers |
| SOC 2 cuts audit costs | Compliance reduces audit expenses by half while building client trust |
| Human error dominates incidents | Training and automation address the 95% of cyber incidents caused by people |
| Audit trails ensure compliance | Detailed logging satisfies HIPAA, GDPR, and PCI-DSS regulatory requirements |
| Automation improves accuracy | AI-powered questionnaire tools reduce manual workload and response errors |
Understanding SaaS cybersecurity risks and data isolation
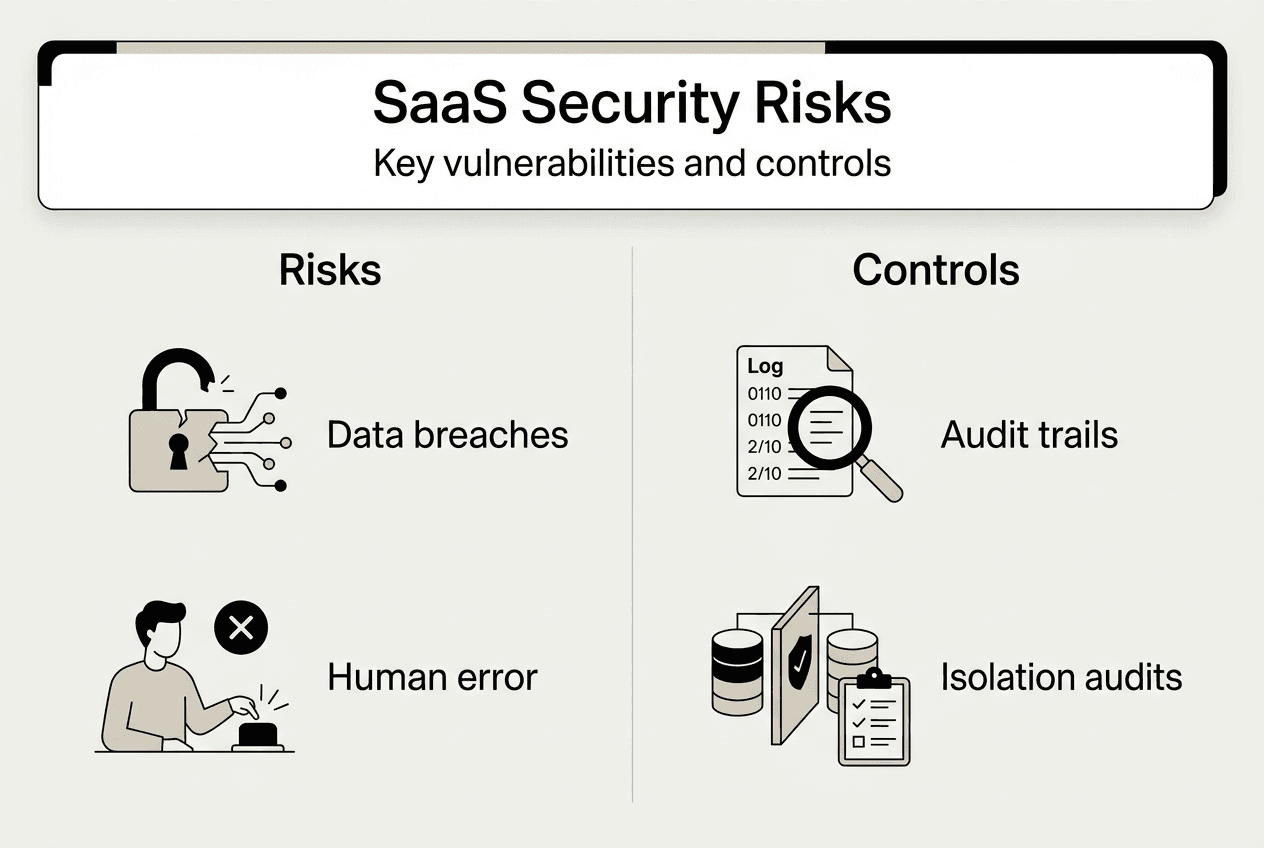
SaaS platforms attract sophisticated cyberattacks because they centralize massive amounts of customer data in shared infrastructure. Unlike traditional on-premises systems where each organization maintains physical separation, SaaS environments rely on logical boundaries to keep data secure. When these boundaries fail, the consequences ripple across your entire customer base. Understanding these unique risks is your first step toward building resilient security.
Data isolation segregates each customer's information within the same physical infrastructure, creating virtual walls that prevent unauthorized access between tenants. This architectural approach forms the foundation of SaaS security, yet 60% of SaaS security breaches stem from inadequate data isolation. The stakes are high because a single data isolation vulnerability can expose all customers' data, turning what should be a contained incident into a catastrophic breach.
Common architectural pitfalls weaken data isolation in ways that aren't immediately obvious:
- Shared database schemas without proper row-level security controls
- Inadequate API authentication allowing cross-tenant data queries
- Misconfigured access control lists that grant excessive permissions
- Insufficient encryption key management exposing data at rest
These vulnerabilities often emerge during rapid scaling when development teams prioritize features over security architecture. You might deploy new functionality without fully testing isolation controls, or inherit legacy code that predates modern security standards. The complexity of microservices architectures compounds these challenges, as each service boundary represents a potential isolation failure point.
Pro Tip: Schedule quarterly isolation audits that simulate cross-tenant access attempts, going beyond your initial deployment security review to catch configuration drift and new vulnerabilities introduced by system updates.
Mastering data isolation requires both technical controls and organizational discipline. You need robust architecture combined with continuous monitoring to detect anomalies that signal potential breaches. As you strengthen these foundational elements, integrating formal compliance frameworks provides additional structure and accountability. Understanding SOC 2 compliance requirements helps you align technical controls with industry standards, while following a comprehensive SOC 2 compliance guide ensures you implement best practices systematically.
Leveraging compliance frameworks to strengthen SaaS security
Compliance frameworks transform abstract security principles into concrete, auditable controls that systematically reduce risk. SOC 2 stands out as particularly relevant for SaaS platforms because it focuses on the security, availability, and confidentiality of customer data in cloud environments. This framework isn't just a checkbox exercise; it enforces the disciplined security practices that prevent breaches.

SOC 2 compliance reduces audit costs by 50% by establishing standardized controls that satisfy multiple stakeholder requirements simultaneously. Instead of conducting separate security reviews for each prospect or partner, you provide a single SOC 2 report that demonstrates your security posture comprehensively. This efficiency accelerates sales cycles and builds trust faster than ad hoc security questionnaires ever could.
Audit trails form a critical component of compliance, providing the detailed activity logs that regulators and auditors demand. These trails must capture who accessed what data, when they accessed it, and what actions they performed. Audit trails are required for HIPAA, GDPR, and PCI-DSS compliance, making them non-negotiable for organizations handling sensitive information. Without comprehensive logging, you cannot prove compliance or investigate security incidents effectively.
Different frameworks emphasize distinct aspects of security:
| Framework | Primary Focus | Key Benefit |
|---|---|---|
| SOC 2 | Cloud service security controls | Reduces audit costs, accelerates trust |
| HIPAA | Healthcare data protection | Ensures patient privacy, avoids penalties |
| GDPR | Personal data rights and privacy | Enables EU market access, protects reputation |
| PCI-DSS | Payment card data security | Prevents fraud, maintains payment processing |
Each framework requires audit trails, but they differ in retention periods, access controls, and reporting formats. HIPAA mandates six-year retention for healthcare records, while GDPR requires demonstrating data processing legitimacy throughout the data lifecycle. PCI-DSS focuses specifically on cardholder data environments, demanding quarterly network scans and annual assessments. Understanding these nuances helps you design logging systems that satisfy multiple requirements efficiently.
Pro Tip: Implement automated audit trail collection and analysis tools that continuously monitor for compliance violations, alerting you to issues before they become audit findings or security incidents.
Integrating compliance into your security strategy creates a virtuous cycle. The controls required for certification strengthen your actual security posture, not just your documentation. Regular audits by qualified SOC 2 auditors provide external validation and identify gaps you might have missed. Understanding the differences between SOC 2 type reports helps you choose the right certification level for your business stage and customer requirements. Following a structured SOC 2 compliance guide ensures you implement controls systematically rather than reactively.
Mitigating human error and operational risks in SaaS cybersecurity
Technology alone cannot secure your SaaS platform because 95% of cyber incidents are caused by human error. This staggering statistic reveals that your people, not your firewalls, represent your greatest vulnerability. Misconfigurations, weak passwords, successful phishing attacks, and inadvertent data exposure all trace back to human decisions and actions.
Common human-related vulnerabilities manifest in predictable patterns. Developers accidentally commit credentials to public repositories, exposing API keys and database passwords. Administrators grant overly broad permissions because restrictive controls seem to slow productivity. Employees fall for sophisticated phishing emails that bypass technical defenses. Each mistake creates an entry point for attackers who specifically target these human weaknesses.
Reducing human error requires a multi-layered approach:
- Implement mandatory security awareness training covering current threat tactics and social engineering techniques
- Enforce least-privilege access controls that limit damage from compromised accounts
- Deploy automated configuration management preventing manual mistakes in production environments
- Establish peer review processes for infrastructure changes and security-sensitive code
- Create incident response playbooks that guide teams through security events systematically
- Use automation to handle repetitive security tasks where human attention wanders
These strategies work together to create defense in depth against human error. Training improves decision-making at the individual level, while automation removes opportunities for mistakes entirely. Access controls contain the blast radius when errors occur, and peer review catches problems before they reach production.
Automating security questionnaires exemplifies how technology can eliminate error-prone manual processes. When you respond to dozens of vendor security assessments manually, inconsistencies creep in, outdated information gets copied forward, and critical details get overlooked. Security questionnaire automation ensures accurate, consistent responses while freeing your team to focus on strategic security improvements rather than repetitive data entry. Tools like a security automation browser extension integrate directly into your workflow, reducing friction and improving adoption.
"The weakest link in any security system is the human element. No amount of technology can compensate for inadequate training and awareness."
This reality demands that you invest as heavily in your people as you do in your security tools. Regular training updates keep pace with evolving threats. Simulated phishing exercises test readiness and identify individuals who need additional support. Post-incident reviews focus on learning rather than blame, encouraging transparency about mistakes so the entire organization can improve.
Applying automation and best practices for enhancing SaaS cybersecurity posture
Architectural best practices provide the blueprint for secure SaaS platforms, and 90% of data isolation issues are preventable with proper architecture. This preventability underscores that security isn't mysterious or impossibly complex; it's the result of deliberate design choices and consistent implementation. You can dramatically reduce risk by following proven patterns.
Core architectural principles for data isolation include:
- Implement row-level security in multi-tenant databases to enforce separation at the data layer
- Use separate encryption keys per tenant to prevent cross-customer data exposure
- Deploy network segmentation isolating customer workloads from each other
- Enforce strict API authentication verifying tenant context on every request
- Maintain separate backup streams preventing data mixing during recovery
These technical controls work best when combined with automated security questionnaire management. Manual questionnaire processes introduce delays and inconsistencies that undermine your security program:
| Aspect | Manual Process | Automated Process |
|---|---|---|
| Response time | Days to weeks | Minutes to hours |
| Accuracy | Prone to copy-paste errors | Consistent, validated answers |
| Compliance tracking | Spreadsheet chaos | Centralized audit trail |
| Team bandwidth | Consumes security experts | Frees experts for strategic work |
| Scalability | Bottlenecks with volume | Handles unlimited questionnaires |
Automation transforms security questionnaires from a burden into a competitive advantage. You respond faster to prospects, provide more detailed and accurate information, and maintain perfect consistency across all responses. This speed and reliability accelerates sales cycles while demonstrating your operational maturity to potential customers.
Deploying automation within your security workflows requires thoughtful integration:
- Audit your current questionnaire volume and identify response patterns
- Centralize security documentation in a searchable knowledge base
- Map common questions to authoritative information sources
- Configure automation tools to pull from verified documentation
- Establish review workflows for novel or sensitive questions
- Monitor automation accuracy and refine mappings continuously
Common pitfalls when implementing automation include:
- Failing to maintain the underlying knowledge base as systems change
- Over-automating without human review for context-specific questions
- Neglecting to train teams on when to override automated responses
- Treating automation as set-and-forget rather than continuously improving
Pro Tip: Schedule monthly reviews of automated questionnaire responses to identify drift between your documented security posture and actual implementation, using discrepancies as early warnings of configuration changes or gaps.
Security questionnaire automation becomes even more powerful when integrated with your compliance program. The same documentation supporting automated questionnaire responses also feeds audit preparation, vendor assessments, and internal security reviews. This single source of truth eliminates contradictions and ensures everyone works from current information. Understanding SOC 2 requirements helps you structure your knowledge base to address both questionnaires and compliance audits efficiently.
Enhance your SaaS security with Skypher automation tools
Managing security questionnaires manually drains your team's time and introduces errors that undermine confidence in your security program. Skypher transforms this burden into a streamlined process through AI security questionnaire automation that answers even 200 questions in under one minute. Our proprietary AI models parse every questionnaire format reliably, far exceeding generic solutions that struggle with complex documents.

Our powerful browser extension integrates directly into your workflow, enabling you to respond to security reviews without switching contexts or losing momentum. You maintain accuracy while dramatically reducing response times, helping your sales team close deals faster and your compliance team handle increasing assessment volumes. With 30+ API connectors to platforms like OneTrust and ServiceNow, plus integrations with Slack, Microsoft Teams, Confluence, and SharePoint, Skypher fits seamlessly into your existing security operations. Visit Skypher to see how automation can strengthen your security posture while freeing your team to focus on strategic initiatives rather than repetitive questionnaire responses.
Frequently asked questions
What are the main cybersecurity risks faced by SaaS platforms?
SaaS platforms face concentrated risks from data isolation failures, which can expose all customer data through a single vulnerability, and from human error, which causes the vast majority of security incidents. Architectural weaknesses in multi-tenant environments create opportunities for cross-customer data access, while misconfigurations and social engineering attacks exploit human decision-making. Following a comprehensive SOC 2 compliance guide helps address these risks systematically through proven controls and regular audits.
How does SOC 2 compliance benefit SaaS cybersecurity efforts?
SOC 2 compliance enforces rigorous security criteria covering access controls, encryption, monitoring, and incident response, creating a structured framework that reduces breach risk. SOC 2 compliance reduces audit costs by 50% by providing standardized documentation that satisfies multiple stakeholder requirements simultaneously. This efficiency accelerates trust-building with prospects while strengthening your actual security posture through regular external audits. Learn more through this detailed SOC 2 compliance guide.
What role does automation play in managing SaaS security questionnaires?
Automation eliminates the manual effort and inconsistencies that plague security questionnaire responses, ensuring accurate answers pulled from verified documentation sources. It dramatically reduces response times from days to minutes while freeing security experts to focus on strategic improvements rather than repetitive data entry. Security questionnaire automation scales effortlessly with increasing assessment volumes, maintaining perfect consistency across all responses regardless of who initiates the questionnaire.
How can organizations effectively reduce human error in cybersecurity?
Organizations reduce human error through layered strategies combining mandatory security training, automated configuration management, least-privilege access controls, and peer review processes for sensitive changes. Automation handles repetitive tasks where human attention wanders, while training improves decision-making for situations requiring judgment. Regular simulated phishing exercises test readiness and identify individuals needing additional support, creating a culture of continuous security awareness improvement.
Why are audit trails critical for SaaS compliance?
Audit trails provide the detailed activity logs that regulators and auditors require to verify security controls and investigate incidents, capturing who accessed what data, when, and what actions they performed. These logs satisfy mandatory requirements across HIPAA, GDPR, and PCI-DSS, making them non-negotiable for organizations handling sensitive information. Without comprehensive audit trails, you cannot prove compliance during assessments or conduct effective forensic analysis after security events.
