When 82% of breaches involve human error, security frameworks become non-negotiable. SOC 2 compliance validates that your organization protects customer data through tested controls, yet many compliance officers struggle to decode its requirements. This guide cuts through the confusion, explaining Trust Service Criteria, audit types, and actionable best practices tailored for tech and finance leaders navigating SOC 2 in 2026.
Table of Contents
- Understanding Soc 2 And Its Trust Service Criteria
- The Importance Of Access Controls And Risk Assessments In Soc 2
- Soc 2 Audit Types And How They Ensure Ongoing Security
- Best Practices For Achieving And Maintaining Soc 2 Compliance
- How Skypher Can Simplify Your Soc 2 Compliance Journey
- Frequently Asked Questions
Key takeaways
| Point | Details |
|---|---|
| Security is mandatory | SOC 2 requires Security criteria for all audits; Availability, Confidentiality, Processing Integrity, and Privacy are optional based on business risk. |
| Access controls drive success | Weak user access management causes 68% of qualified opinions in SOC 2 audits, making robust access reviews critical. |
| Type II validates sustained compliance | Type II audits evaluate control effectiveness over 6 to 12 months, providing ongoing assurance to enterprise clients. |
| Tailored controls beat templates | Auditors reject generic controls; risk-aligned, documented policies specific to your operations are essential for passing audits. |
Understanding SOC 2 and its Trust Service Criteria
SOC 2 is a principles-based framework built on five Trust Service Criteria: Security, Availability, Processing Integrity, Confidentiality, and Privacy. Unlike prescriptive standards, SOC 2 lets you design controls that fit your unique risk profile and business model.
Security is mandatory for every SOC 2 audit. The other four criteria become relevant based on what data you handle and what promises you make to customers. A SaaS platform handling payment data might add Confidentiality and Processing Integrity, while a healthcare analytics provider would include Privacy.
Your criteria selection directly impacts audit scope and cost. Each additional criterion requires more evidence collection, testing, and auditor hours. Choose criteria that genuinely reflect customer commitments and contractual obligations, not what sounds impressive on marketing materials.
The flexibility of SOC 2's principle-based approach means you can implement controls through technology, process, or policy. You might enforce access restrictions via role-based permissions in your identity platform, manual quarterly reviews, or a hybrid model. What matters is effectiveness and consistency, not specific tools.
Key Trust Service Criteria include:
- Security: Protection against unauthorized access, both physical and logical
- Availability: System uptime and operational performance meeting service level agreements
- Processing Integrity: Accurate, timely, and authorized transaction processing
- Confidentiality: Protection of sensitive information designated as confidential
- Privacy: Collection, use, retention, and disposal of personal information per commitments
For compliance officers evaluating SOC 2 requirements for SaaS trust, understanding how criteria selection shapes your program is foundational. Your internal stakeholders will ask which criteria apply, and you need clear rationale based on data types, regulatory requirements, and customer expectations.
The importance of access controls and risk assessments in SOC 2
Access controls represent the most scrutinized area in SOC 2 audits. Weak user and entity access controls account for 68% of qualified opinions, making this the single biggest compliance risk you face.
The principle of least privilege forms the foundation. Every user, service account, and API key should have exactly the permissions needed for their role, nothing more. Overprivileged accounts create attack vectors and complicate audit evidence when auditors question why a developer has production database admin rights.
Access reviews must happen regularly and leave documented evidence. Quarterly reviews work for most organizations, but you might need monthly reviews for privileged accounts touching sensitive data. Automated tools that flag dormant accounts, excessive permissions, or policy violations reduce manual effort and human error.
Risk assessments drive your entire SOC 2 program. Stale risk assessments cause 35% of deal losses because customers and auditors need current risk analysis supporting your controls. An assessment from 18 months ago doesn't reflect your current threat landscape, technology stack, or business model.

Your risk assessment should identify threats specific to your organization, not generic cybersecurity risks copied from templates. Consider your data types, third-party integrations, remote workforce, cloud infrastructure, and customer obligations. Map each risk to specific controls, creating clear traceability for auditors.
Critical access control practices include:
- Implementing multi-factor authentication for all production system access
- Conducting quarterly access reviews with documented approvals
- Automating account provisioning and deprovisioning tied to HR systems
- Maintaining separate development, staging, and production environments with distinct access tiers
- Logging and monitoring privileged account activity for anomaly detection
Pro Tip: Testing 100% of privileged accounts quarterly cuts breach risk by 80%. Automate this testing through identity governance platforms that integrate with your access management systems, creating audit trails auditors can verify easily.
Compliance officers managing SOC 2 auditor trust in SaaS environments need visibility into who can access what data and systems. Shadow IT, forgotten service accounts, and manual access provisioning create gaps that surface during audits as control deficiencies.
SOC 2 audit types and how they ensure ongoing security
SOC 2 audits come in two types, each serving distinct purposes. Type I audits assess whether controls are designed appropriately at a specific point in time. They answer: Are your documented policies and procedures adequate for meeting the Trust Service Criteria?
Type II audits go further by validating controls over 6 to 12 months, proving controls don't just exist on paper but operate effectively across time. Auditors test samples of access reviews, vulnerability scans, incident responses, and change management processes to verify consistent execution.
Most enterprise customers require Type II reports before signing contracts. A Type I report shows good intentions; Type II demonstrates proven capability. The difference matters when customers evaluate vendor risk, especially in regulated industries like finance and healthcare.
The Type II audit process involves several key stages:
- Planning and scoping: Define audit period, applicable criteria, and system boundaries with your auditor
- Readiness assessment: Internal teams validate controls operate correctly before formal testing begins
- Testing period: Auditors collect evidence samples, interview personnel, and observe control execution over the defined timeframe
- Reporting: Auditor issues opinion on control design and operating effectiveness, noting any exceptions or findings
Type II audits create accountability for continuous compliance. You can't implement controls in month 11 and expect a clean opinion. Controls must function throughout the entire audit period, meaning your compliance program operates year-round, not just during audit season.
Auditors sample evidence from across the audit period. If your quarterly access review failed in month 3, that exception appears in your report even if months 1, 2, and 4 through 12 passed cleanly. This reality drives the need for automated compliance workflows that reduce manual process failures.
For compliance officers building programs around SOC Type II report requirements, understanding the operational burden of sustained control execution is critical. Budget for tools, staff time, and remediation cycles that support continuous compliance, not point-in-time preparation.
Best practices for achieving and maintaining SOC 2 compliance
Successful SOC 2 programs start with controls tailored to your specific risk landscape. Generic templates downloaded from compliance vendors fail because auditors immediately spot boilerplate language that doesn't reflect your actual operations. Your incident response plan should reference your ticketing system, escalation chains, and communication tools, not placeholder text.
Automation reduces human error and creates consistent audit evidence. Automated access reviews and regular audits ensure reviews happen on schedule with documented outcomes. Manual processes relying on calendar reminders and spreadsheets fail when team members leave, priorities shift, or email notifications get ignored.
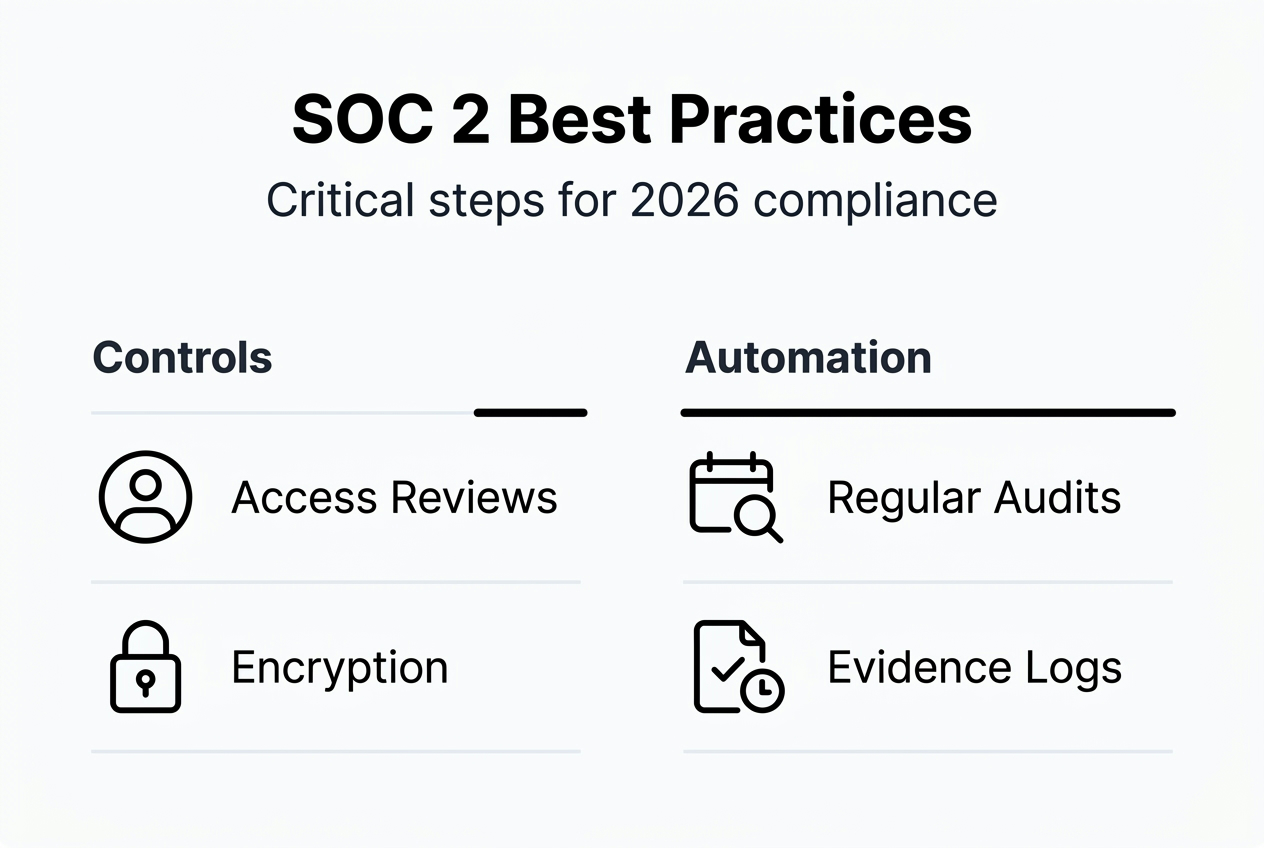
Data protection requires encryption both in transit and at rest. Transport Layer Security for data moving across networks protects against interception. Encryption at rest using standards like AES-256 safeguards data on servers, databases, and backup systems. Key management becomes critical, with separate encryption keys for production and non-production environments.
Vulnerability management can't be sporadic. Monthly vulnerability scans identify emerging threats in your infrastructure. Annual penetration testing validates whether vulnerabilities can be exploited and whether your detection and response controls work. Auditors want evidence of remediation timelines tied to vulnerability severity, not just scan reports.
Common pitfalls that sink SOC 2 audits:
- Using vendor-provided templates without customization to your environment
- Failing to update risk assessments when business models or technology stacks change
- Implementing controls without documenting procedures employees can actually follow
- Relying on manual processes for critical controls that need consistent execution
- Ignoring control failures or exceptions instead of documenting and remediating them
Pro Tip: Testing 100% of privileged accounts quarterly catches access creep before it becomes an audit finding. Configure automated reports that flag accounts with permissions exceeding role requirements, then route these to managers for review and approval.
| Control Area | Frequency | Owner | Evidence |
|---|---|---|---|
| Access Reviews | Quarterly | IT Security | Approved access lists with manager sign-off |
| Vulnerability Scans | Monthly | Infrastructure | Scan reports with remediation tracking |
| Penetration Testing | Annual | External Vendor | Test report with management response |
| Risk Assessment | Annual | Compliance Officer | Updated risk register with control mapping |
| Incident Response Testing | Semi-annual | Security Team | Test scenarios with lessons learned |
Maintaining SOC 2 compliance means treating it as an ongoing operational discipline, not an annual audit event. Build controls into existing workflows. Make access provisioning part of employee onboarding. Integrate vulnerability scanning with your change management process. Connect incident response testing to your disaster recovery exercises.
For teams managing SOC 2 type reports and evaluating SOC 2 compliance cost factors, remember that upfront investment in automation and documentation reduces long-term operational burden and audit costs. Point solutions create gaps; integrated platforms provide the visibility and control auditors need to issue clean opinions.
How Skypher can simplify your SOC 2 compliance journey
SOC 2 compliance generates endless security questionnaires from customers evaluating your controls. Responding manually consumes hours that compliance teams can't spare during audit preparation. Skypher's security questionnaire automation uses AI to complete reviews in minutes, not days, giving you time to focus on control operation.

Our AI-powered recommendation engine suggests responses aligned to your SOC 2 controls, ensuring consistency across customer questionnaires and audit evidence. Easy import and export workflows connect with over 40 third-party risk management platforms, eliminating manual data entry and reducing errors that create audit exceptions.
Frequently asked questions
What is SOC 2 compliance and why does it matter?
SOC 2 is a security and privacy standard defining how service organizations protect customer data through documented, tested controls. It matters because enterprise customers in tech and finance require SOC 2 reports before signing contracts, using them to evaluate vendor risk and data protection capabilities.
What's the difference between SOC 2 Type I and Type II audits?
Type I audits evaluate control design at a single point in time, confirming policies and procedures are adequate. Type II audits test whether controls operate effectively over 6 to 12 months, providing evidence of sustained compliance. Enterprise customers typically require Type II reports.
How long does SOC 2 compliance take?
Initial SOC 2 readiness takes 3 to 6 months for organizations building programs from scratch. The Type II audit period requires 6 to 12 months of control operation before auditors can issue a report. Well-prepared organizations with existing security programs can accelerate timelines.
Which Trust Service Criteria should my organization choose?
Security is mandatory for all SOC 2 audits. Add Availability if uptime commitments matter to customers, Processing Integrity for transaction accuracy requirements, Confidentiality for sensitive data handling, and Privacy when collecting personal information. Base choices on customer contracts and data types, not marketing goals.
How much does SOC 2 compliance cost?
Costs range from $20,000 to $100,000 depending on organization size, number of Trust Service Criteria, audit type, and control maturity. Expect higher costs for Type II audits, multiple criteria, complex infrastructure, and first-time audits requiring significant remediation. Automation tools reduce ongoing operational costs.