One missed step in a vendor risk review can cost your organization far more than time. A single overlooked third-party relationship has triggered data breaches and regulatory fines that ran into the tens of millions for companies in tech and finance. Compliance officers and risk managers know the pressure: vendor ecosystems keep growing, regulatory scrutiny keeps tightening, and the margin for error keeps shrinking. This guide gives you a clear, practical framework to run vendor risk reviews that actually hold up under audit, protect your organization, and save your team from the exhausting cycle of rework.
Table of Contents
- Why vendor risk reviews are critical for tech and finance
- What you need: prerequisites and tools for effective reviews
- The essential vendor risk review steps: a practical roadmap
- Common missteps and how to avoid them
- Ensuring ongoing compliance and continuous improvement
- Streamline your vendor risk reviews with advanced automation
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Preparation is essential | Having complete documents and the right tools at the start prevents review delays and missteps. |
| Follow each step carefully | A structured review ensures all risks are identified, documented, and remediated without gaps. |
| Continuous improvement matters | Regular monitoring, evaluation, and process refinement maintain high compliance and security standards. |
| Automation streamlines results | Leveraging automation tools minimizes manual work and accelerates the entire review cycle. |
Why vendor risk reviews are critical for tech and finance
Tech and finance companies operate in some of the most heavily regulated environments on the planet. Your vendors touch sensitive customer data, critical infrastructure, and proprietary systems. When one of them fails a security or compliance standard, your organization shares the exposure.
Here is why compliance teams treat vendor risk reviews as non-negotiable:
- Regulatory mandates: Frameworks like SOC 2, ISO 27001, GDPR, and DORA require documented evidence of third-party due diligence.
- Contractual liability: Vendor agreements often shift liability back to you if you cannot prove adequate oversight.
- Operational continuity: A vendor outage or breach can halt your own services, triggering SLA penalties and reputational damage.
- Supply chain attacks: Threat actors increasingly target vendors as a backdoor into larger organizations.
Multimillion-dollar penalties in regulated industries have resulted directly from inadequate vendor risk reviews. That is not a hypothetical. It is a pattern regulators have documented repeatedly.
"The question is no longer whether your vendors will be targeted. It is whether your review process will catch the gap before regulators or attackers do."
A solid risk management guide will tell you the same thing: the cost of prevention is always lower than the cost of response. Build the process now, before the incident forces your hand.
What you need: prerequisites and tools for effective reviews
Preparation separates a review that produces real insight from one that just generates paperwork. Before you send a single questionnaire, make sure you have the right inputs in place.
Key documents to gather:
- Current vendor contracts and amendments
- Service level agreements (SLAs) and data processing agreements (DPAs)
- Previous risk assessments and audit reports
- Vendor-provided certifications (SOC 2 Type II, ISO 27001, PCI DSS, etc.)
- Incident history and remediation records
Stakeholders to involve:
| Role | Responsibility in the review |
|---|---|
| Compliance officer | Owns the process and regulatory alignment |
| IT/security team | Validates technical controls and evidence |
| Legal counsel | Reviews contractual obligations and liability |
| Procurement | Manages vendor relationships and escalations |
| Business owner | Confirms vendor criticality and operational impact |
Technology checklist:
- A centralized vendor inventory system
- Questionnaire automation platform with format support
- Document management integration (SharePoint, Google Drive, Confluence)
- TPRM platform connectors (OneTrust, ServiceNow, etc.)
- Workflow and notification tools (Slack, MS Teams)
Organized documentation and the right technology platform help avoid duplicate work and keep your team focused on analysis rather than administration. Use a risk assessment checklist to confirm nothing falls through the cracks before you begin.

The essential vendor risk review steps: a practical roadmap
With your team and tools ready, here is how to move through each stage of the review with confidence.
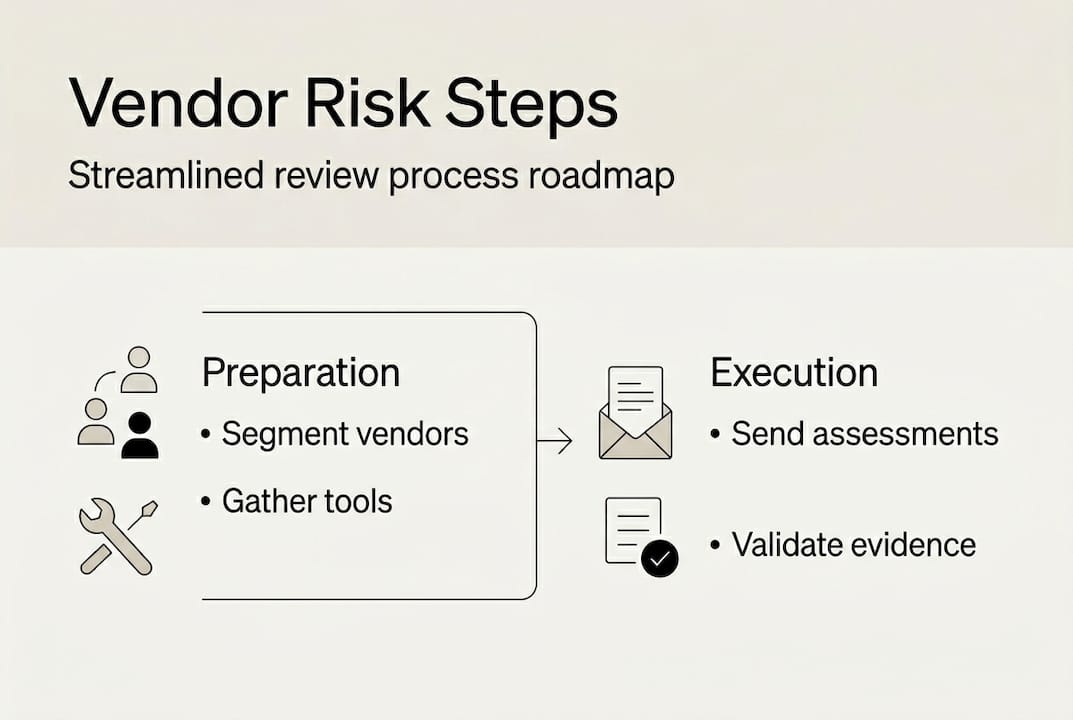
Step 1: Build and segment your vendor inventory List every active vendor and categorize them by risk tier: critical, high, medium, and low. Criticality is determined by data access, system integration depth, and regulatory relevance. This segmentation drives everything that follows.
Step 2: Tailor the assessment scope Do not apply the same 200-question questionnaire to a low-risk office supply vendor and a cloud infrastructure provider. Match the depth of your assessment to the vendor's risk tier. Critical vendors get full technical, financial, and operational reviews. Lower tiers get streamlined versions.
Step 3: Distribute questionnaires and track responses Send assessments through a platform that supports automated follow-up and response tracking. Manual email chains create version control nightmares. A structured, stepwise review reduces both risk exposure and audit fatigue for your team.
Step 4: Validate evidence Do not accept self-attestation alone. Request and verify supporting documentation: current certifications, penetration test results, financial statements for critical vendors, and audit reports. Cross-reference claims against third-party sources where possible.
Step 5: Document findings and assign risk ratings Score each vendor against your risk criteria. Use a consistent rating scale (for example, 1 to 5 or low/medium/high/critical) and document the rationale for every score. This creates the audit trail regulators expect.
Step 6: Build a mitigation plan and assign follow-up actions For every identified gap, assign a remediation owner, a deadline, and a verification method. Unresolved findings with no owner are the most common reason reviews fail at audit time.
"A review without a remediation plan is just a list of problems. The value is in what happens next."
Pro Tip: Use your vendor risk management insights to benchmark your rating criteria against industry standards before you finalize your scoring model. It saves significant rework when regulators ask how you calibrated your thresholds. Also review key insights for selecting risk management vendors to make sure your tooling supports the full workflow.
Comparison: manual vs. automated vendor risk review
| Factor | Manual process | Automated process |
|---|---|---|
| Time per vendor | 4 to 8 hours | Under 30 minutes |
| Error rate | High (human entry) | Low (AI-validated) |
| Audit trail quality | Inconsistent | Standardized and complete |
| Scalability | Limited | Handles hundreds of vendors |
| Follow-up tracking | Manual reminders | Automated workflows |
Common missteps and how to avoid them
Even well-resourced compliance teams make predictable mistakes. Knowing them in advance puts you ahead.
Overlooking lower-tier vendors. A tier-3 vendor with access to even one system containing personal data can become a significant liability. Do not let low criticality scores translate into zero scrutiny.
Letting documentation go stale. A vendor assessment completed 18 months ago tells you very little about today's risk posture. Certifications expire. Personnel changes. Systems get updated. Your records need to reflect current reality.
Using outdated assessment frameworks. Regulatory expectations evolve. An assessment template built for 2022 compliance requirements may miss controls now required under DORA, updated NIST guidance, or new state-level privacy laws.
Skipping remediation follow-up. Incomplete documentation and lack of follow-up are among the most cited pitfalls in vendor risk programs. Identifying a gap and not closing it is worse than not finding it, because now you have documented knowledge of a risk you chose not to address.
Pro Tip: Build a 30-day, 60-day, and 90-day follow-up cadence into every review cycle. Assign a named owner for each open finding. When you implement vendor management programs with clear accountability structures, remediation rates improve significantly.
- Set calendar-based review triggers for every vendor tier
- Use automated alerts when certifications are approaching expiration
- Require vendors to notify you of material changes within a defined window
- Conduct spot checks between formal review cycles for critical vendors
Ensuring ongoing compliance and continuous improvement
A vendor risk review is not a one-time event. It is a cycle. The organizations that stay ahead of risk are the ones that treat monitoring as a permanent function, not a project.
When to trigger a review outside the normal schedule:
- A vendor experiences a security incident or data breach
- Significant changes to the vendor's ownership, leadership, or financial status
- Your organization expands the scope of data or systems the vendor can access
- New regulatory requirements take effect that affect the vendor relationship
- A vendor fails to meet SLA thresholds over a defined period
Continuous monitoring improves detection of latent risks and compliance gaps that periodic reviews alone would miss. This is especially true in fast-moving tech environments where vendor configurations and access permissions change frequently.
Best practices for maintaining your audit trail:
- Store all assessment records in a centralized, access-controlled repository
- Version-control every document so reviewers can see what changed and when
- Log all communications with vendors related to risk findings
- Maintain a remediation register with status updates and closure evidence
Automation plays a major role here. Platforms that integrate with your document management tools (Confluence, Notion, SharePoint, OneDrive) and communication channels (Slack, MS Teams) keep your records current without requiring manual updates. Review vendor management best practices to build a monitoring cadence that fits your organization's size and vendor volume.
Statistic callout: Organizations that implement continuous vendor monitoring report significantly faster detection of compliance gaps compared to those relying solely on annual reviews. Speed of detection directly reduces the window of exposure.
Streamline your vendor risk reviews with advanced automation
Running a rigorous vendor risk review process at scale is genuinely hard when your team is doing it manually. Questionnaires pile up. Evidence requests go unanswered. Findings sit in spreadsheets with no clear owner. The process becomes a bottleneck instead of a safeguard.

Skypher is built specifically for compliance and risk teams in tech and finance who need to move faster without cutting corners. The platform's security questionnaires automation handles everything from distributing assessments to tracking responses and flagging gaps, all in one place. The AI recommendation engine surfaces the most relevant answers from your existing documentation, so your team spends time on decisions rather than data entry. With integrations across 40-plus TPRM platforms, Slack, MS Teams, and major document repositories, Skypher fits into the workflow you already have. If your vendor review process is taking weeks when it should take days, it is worth seeing what purpose-built automation can do.
Frequently asked questions
What is the most critical first step in a vendor risk review?
Segmenting vendors by risk level is the most important first step. It determines how deep your assessment needs to go and where to focus your team's limited time and resources.
How often should vendor risk reviews be conducted?
Annually is the baseline, but periodic reviews catch emerging risks that a fixed schedule misses. Critical vendors often warrant quarterly check-ins or event-triggered reviews when material changes occur.
What are common tools used during a risk review?
The right technology stack typically includes questionnaire automation platforms, document management integrations, TPRM connectors, and AI-driven assessment tools that reduce manual effort and improve accuracy.
How do regulatory requirements affect vendor risk reviews?
Compliance risk shapes the rigor applied to every stage of the review. Regulations set minimum standards for due diligence depth, documentation quality, and how frequently assessments must be refreshed.
