Skypher Blog
Cyber Security and Information Security for GRC Leaders
Cyber security and information security essentials: foundational concepts, core types, real-world strategies, compliance obligations, and key risk factors.
7 Key Types of SOC Every CISO Should Know
Explore 7 types of soc in this educational guide for CISOs and compliance managers, with tips to strengthen security and improve automation results.
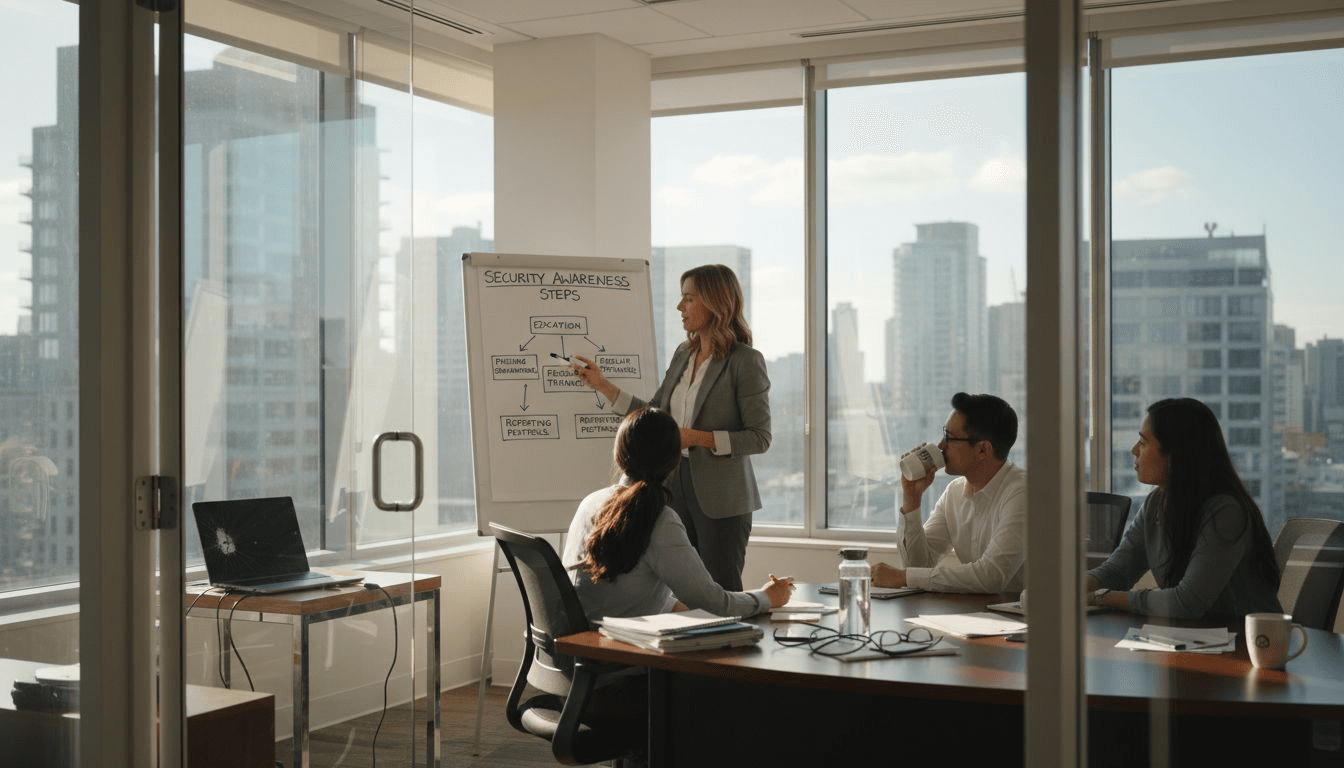
7 Essential Security Awareness Trainings for Fintech Leaders
Explore 7 must-have security awareness trainings for fintech compliance managers. Learn practical strategies to improve cybersecurity and team skills.

Compliance Risk Meaning: Impact on Security Reviews
Compliance risk meaning explained for CISOs: discover types, key drivers, practical impacts, and strategies for better security questionnaire response.

Perform a Secure Review Using Skypher Step by Step
Learn how to efficiently conduct a secure review with Skypher's AI automation tools, from setup to verification, for improved compliance and reduced risks.

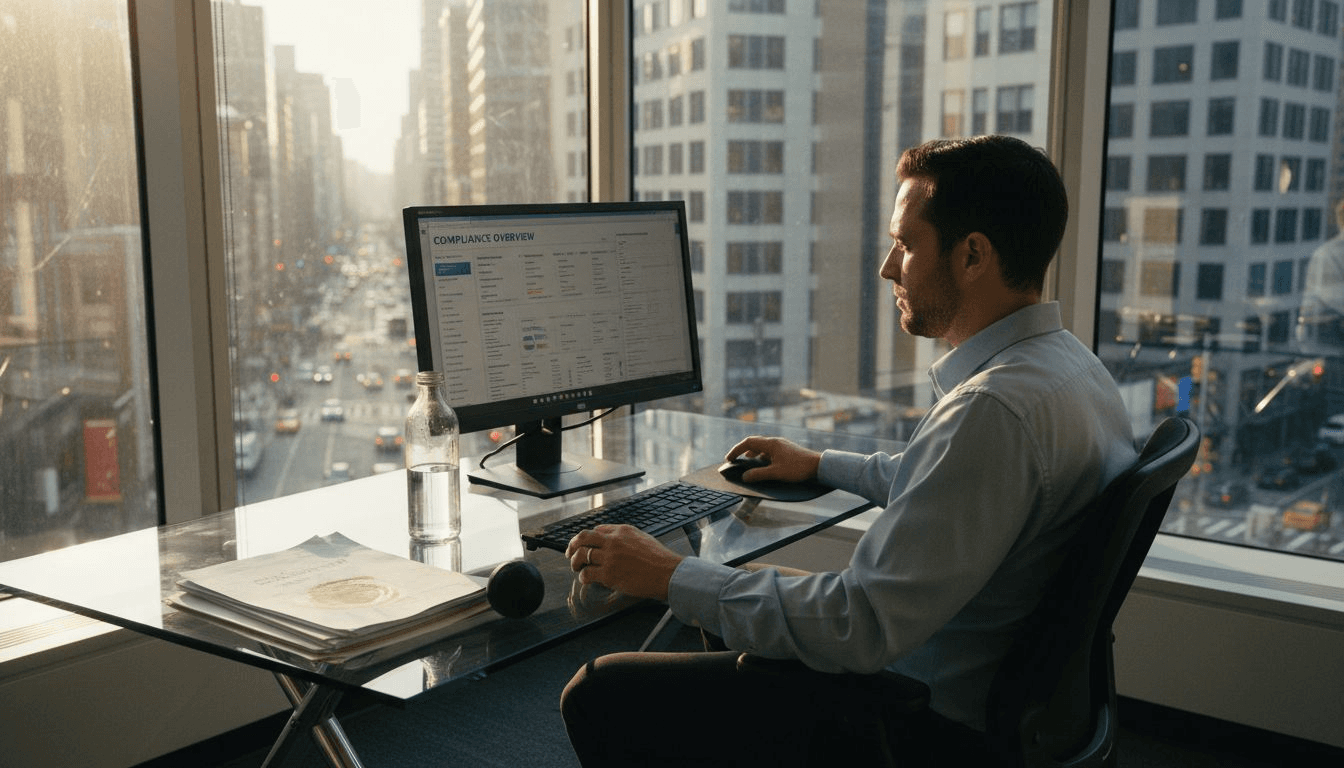
Automated Compliance: Transforming Security Reviews
Automated compliance streamlines security questionnaires, improves accuracy, and reduces risks for tech firms. Learn about tools, key processes, and pitfalls.
SOC 2 Requirements: Boosting SaaS Trust and Speed
SOC 2 requirements for SaaS: discover trust service criteria, implementation steps, audit types, and real-world compliance challenges.

SOC 1 Report Example: Boosting Trust in Tech Compliance
SOC 1 report example explained: definition, structure, requirements, key risks, and real-world uses for streamlined security reviews in tech and finance.

Best Practices Vendor Management for Secure Operations
Discover step-by-step best practices vendor management for secure, streamlined questionnaire processes and risk reduction. Achieve effective vendor oversight easily.