TL;DR:
- Trust centers provide continuous, verifiable transparency, reducing reliance on outdated security questionnaires.
- They streamline vendor assessments, saving time and resources while building buyer trust.
- Effective trust centers are maintained as core assets and integrated with automation and AI tools.
Security teams at enterprise tech and finance organizations know this pain intimately: another security questionnaire lands in the inbox, and suddenly your most experienced engineers are spending a full week answering the same 150 questions they answered three months ago for a different prospect. Only 34% of questionnaire responses are trusted by the recipients who requested them, which means all that effort may not even move the needle on the relationship. Trust centers are changing this dynamic, offering a continuous, verifiable, and far more efficient path to demonstrating security posture without the recurring questionnaire grind.
Table of Contents
- Why traditional security questionnaires fall short
- What are trust centers? Defining the new standard in cybersecurity transparency
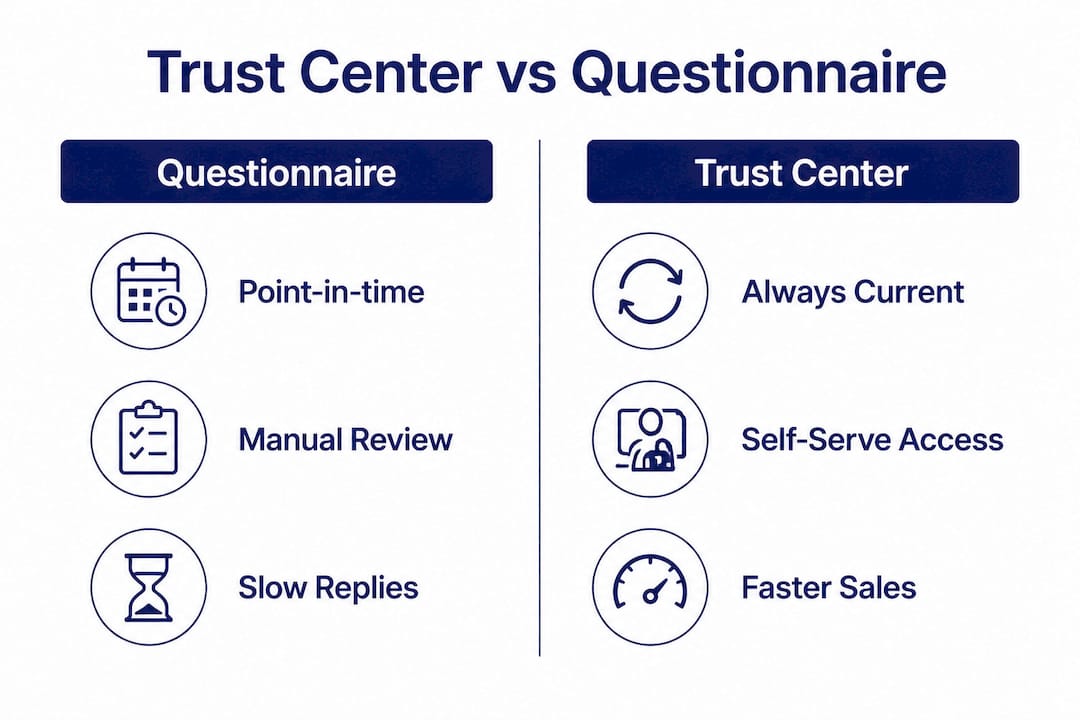
- Trust centers vs. security questionnaires: Evidence and efficiency
- How trust centers work in practice: Integrating automation and AI
- Limits and considerations: When trust centers might not be enough
- A modern perspective: Getting the most from trust centers
- Streamline your security process with Skypher's trust center solutions
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Trust centers boost transparency | They provide a single, always-available source for up-to-date security documentation and evidence. |
| Reduce compliance workload | Trust centers can significantly reduce the time and resources spent on repetitive security questionnaires. |
| Automation is critical | Automating updates and responses ensures your trust center delivers continual value and deflects the most requests. |
| Not a total replacement | Some buyers, especially in regulated sectors, may still request personalized questionnaires. |
| Context matters | Understanding technical distinctions—like trust centers versus zero-trust boundaries—prevents process confusion and optimizes security strategy. |
Why traditional security questionnaires fall short
To understand the appeal of trust centers, it's essential to first see why the current approach is falling behind.
Security questionnaires have been the default vendor risk assessment tool for decades. The logic seems sound: ask a vendor a structured set of questions, review the answers, and decide whether to trust them. In practice, the process breaks down at almost every step.
Here is what the questionnaire cycle typically looks like in a large organization:
- A vendor receives a questionnaire with 100 to 300 questions covering everything from encryption standards to incident response procedures.
- The security team pulls in subject matter experts from infrastructure, legal, and compliance to draft accurate answers.
- The process consumes anywhere from 5 to 15 hours or more of skilled labor per questionnaire.
- The completed questionnaire is submitted, and by the time the buyer reviews it, some answers may already be outdated.
- The buyer's team has no reliable way to verify whether any claim is accurate.
The result? A document that is expensive to produce and difficult to trust. Buyers who receive these documents often treat them as a starting point rather than a definitive answer, which leads to follow-up calls, additional document requests, and prolonged procurement timelines.
Managing security questionnaire challenges at scale becomes particularly painful when your sales pipeline includes dozens of active prospects, each with their own preferred format and unique question sets. Aligning responses across formats like Excel, Word, and PDF while keeping answers consistent is a serious operational burden.
"Questionnaires are point-in-time snapshots. The moment they're submitted, the information begins to drift from reality. For any buyer relying on that snapshot to make a risk decision, the margin for error is significant."
Following cybersecurity best practices for vendor assessment means moving beyond static documents and toward continuous, verifiable evidence. That shift is exactly what trust centers are designed to enable.
What are trust centers? Defining the new standard in cybersecurity transparency
With the flaws of questionnaires established, let's define what makes trust centers fundamentally different and more effective.
A trust center is a secure, centralized online portal where a vendor proactively publishes its security, compliance, and privacy documentation. Instead of waiting for a buyer to send a questionnaire, the vendor maintains a living record of their security posture that any qualified stakeholder can access on demand. Certifications, penetration test summaries, data processing agreements, and compliance reports are organized and kept current in one place.
This distinction matters: trust centers provide continuous, verifiable transparency, not a one-time snapshot. A buyer reviewing your trust center at any moment is seeing documentation that reflects your current state, not where you were six months ago when you answered their predecessor's questionnaire.
It is also worth clarifying a terminology confusion that comes up frequently in enterprise security conversations. "Trust centers" in the vendor transparency context are completely different from "trust zones" or "trust boundaries" in zero-trust network architecture. Trust zones, as defined by frameworks like NCSC and NIST, refer to internal network segmentation and controls over data flows between systems. They are infrastructure concepts. Trust centers, by contrast, are communication and transparency platforms. Conflating the two leads to misaligned conversations between security architects and procurement teams.
Here is a side-by-side view of what a trust center typically contains versus what a traditional questionnaire captures:
| Feature | Traditional questionnaire | Trust center |
|---|---|---|
| Information currency | Point-in-time snapshot | Continuously updated |
| Stakeholder access | Reactive, per request | Always-on, self-serve |
| Evidence verifiability | Difficult to verify | Linked to real documentation |
| Maintenance model | Repeated from scratch | Managed centrally |
| Format flexibility | Varies per buyer | Standardized, searchable |
| Buyer trust level | 34% trust rate | Significantly higher |
This shift from reactive to proactive is what makes trust centers so attractive to teams pursuing AI-driven compliance transformation at scale. Rather than spinning up a fresh response effort for each prospect, your evidence is already organized and ready.
Pro Tip: When setting up a trust center, organize your evidence into categories that map directly to common frameworks like SOC 2, ISO 27001, and GDPR. Prospects researching your security posture will navigate to familiar categories first, and clear organization dramatically reduces inbound security questions before a deal even progresses.
Trust centers vs. security questionnaires: Evidence and efficiency
Understanding what trust centers are, it's time to directly compare them with the old status quo.
The efficiency gap between the two approaches is striking. A questionnaire trust rate of only 34% means the enormous effort invested in completing them produces a document that two out of three buyers are skeptical of anyway. Meanwhile, trust centers flip this dynamic by surfacing documentation that buyers can independently evaluate, and in many cases, download and integrate into their own risk management workflows.
The time dimension alone is worth examining closely. A single security questionnaire can consume 5 to 15 hours of internal labor, sometimes more for complex enterprise assessments covering multi-product or multi-entity environments. If your organization is handling 50 questionnaires per year across your sales pipeline, that's potentially 750 hours of skilled security and compliance labor redirected away from actual security work. Trust centers, once established and properly maintained, dramatically reduce this recurring cost by deflecting a large percentage of incoming questionnaire requests before they're even formally submitted.
The questionnaire automation tool model that forward-thinking security teams are adopting pairs trust centers with AI to cover both ends of this problem. The trust center handles the majority of inbound inquiries proactively. For questionnaires that still come in because of buyer preference or regulatory requirements, AI-powered automation handles the response generation against your existing knowledge base, enabling faster questionnaire responses without sacrificing accuracy.
Here is a direct comparison across the metrics that matter most to enterprise procurement teams:
| Metric | Security questionnaire | Trust center |
|---|---|---|
| Response time | Days to weeks | Immediate, self-serve |
| Trust level from buyers | 34% | Substantially higher |
| Resource cost per interaction | 5 to 15+ hours | Minimal ongoing maintenance |
| Evidence verification | Unverifiable assertions | Linked, downloadable documents |
| Scalability | Linear cost increase | Near-zero marginal cost |
| Coverage of follow-up questions | Requires new questionnaire | Updated in real time |
The evidence is clear. Organizations that maintain current, well-structured trust centers are shortening their sales cycles, reducing security team burnout, and building credibility with buyers in a way that a spreadsheet full of yes/no answers simply cannot replicate.

How trust centers work in practice: Integrating automation and AI
Having mapped out the advantages, let's look at how trust centers are practically deployed and where automation comes into play.
Standing up a trust center is a structured process, not a one-time event. Here is the typical flow for an enterprise organization implementing one effectively:
- Audit your existing security documentation. Gather all current certifications, audit reports, policies, and compliance summaries. Identify what needs to be refreshed before it goes live.
- Categorize and organize evidence by framework. Structure your content around the compliance frameworks your buyers care about: SOC 2, ISO 27001, PCI DSS, HIPAA, GDPR. Make it easy to find.
- Configure access controls and NDA workflows. Some documentation, like penetration test reports, should be gated behind an NDA request. Others, like your privacy policy, can be fully public.
- Integrate with your internal knowledge base. Connect your trust center to your documentation sources, whether that's Confluence, Notion, SharePoint, or Google Drive, so updates in your source systems flow through automatically.
- Monitor stakeholder requests and measure deflection. Track which documents are accessed, which requests are still coming in as formal questionnaires, and use that data to fill gaps in your trust center content.
- Layer in AI for remaining questionnaires. Even the best trust center will not deflect 100% of incoming requests. Hybrid AI and trust center approaches automate the remaining questionnaires using your evidence library as the source of truth, maximizing deflection while ensuring accuracy.
This last step is where platforms with deep AI integration separate themselves. Systems that perform document vectorization and chunking against your actual security documentation, as Skypher does, can answer even 200-question assessments in under a minute with high confidence scores tied to the specific source documents being referenced.
Managing the intersection of trust centers and formal questionnaire requests also connects to broader strategies for managing digital fraud risk, particularly for financial services organizations where buyers are operating under strict regulatory scrutiny and require documented evidence chains.
The AI-driven questionnaire essentials for 2026 are increasingly focused on this hybrid model: trust center for proactive transparency, AI for reactive precision. Together, they form the basis for deflecting security questionnaires at scale without compromising on accuracy or buyer confidence.
Pro Tip: Set up automated alerts within your trust center to notify your security team when certifications or compliance documents are approaching expiration. Expired evidence in a trust center is worse than no evidence at all since it signals to buyers that your security program lacks operational discipline.
Limits and considerations: When trust centers might not be enough
No solution is without its challenges; it's important to acknowledge the practical limits and best practices necessary with trust centers.
Trust centers are powerful, but they are not a universal replacement for every security assessment interaction. Understanding where they fall short helps you plan a realistic implementation strategy.
Key limitations to account for include:
- Regulated-sector buyers often require formal questionnaires regardless. Banks, insurance carriers, and other highly regulated financial institutions frequently have mandated third-party risk assessment processes that require vendors to complete specific questionnaires as part of their compliance obligations. A trust center can supplement this process, but it will not replace it entirely.
- Ongoing maintenance is non-negotiable. A trust center with outdated certifications or stale policies actually damages credibility rather than building it. This is why automation is not optional; it's foundational to operating a trust center responsibly over time.
- SMBs selling to less mature buyers may see limited return. Trust centers deliver the most value when selling to high-security-maturity buyers who are actively evaluating vendor security posture. Smaller organizations selling to buyers with minimal security requirements may not justify the investment.
- The "trust boundaries" terminology confusion persists in technical conversations. As the NCSC cross-domain model illustrates, "trust boundaries" in zero-trust architecture refer specifically to data flow controls between network segments, not vendor transparency portals. Getting this terminology wrong in conversations with security architects creates confusion that slows decisions.
"The organizations that treat their trust center as a living, maintained asset rather than a one-time deployment are the ones that actually see a measurable reduction in questionnaire volume and sales cycle length."
For teams looking to navigate both the opportunity and the operational complexity, expert questionnaire tips focused on automation and process discipline are the practical starting point for building a sustainable model.
A modern perspective: Getting the most from trust centers
Most organizations that invest in a trust center make one of two mistakes. They either treat it as a one-time marketing asset that gets uploaded and forgotten, or they focus so heavily on the platform itself that they underinvest in the process discipline that makes the platform valuable. The technology alone does not create trust. Consistent, accurate, and proactively maintained evidence creates trust.
What forward-thinking organizations are doing differently is treating their trust center as a core business function, not a security team side project. Their security leadership owns a quarterly review cycle for all trust center content. Their sales engineering teams are trained to point prospects to specific trust center sections during early conversations, which reframes the vendor evaluation from an adversarial questionnaire process to a collaborative transparency exchange.
The reputational and competitive advantages of this approach are real and measurable. When a security-conscious buyer compares two vendors and one has an always-on, well-organized trust center while the other promises to get back to them with a completed questionnaire in two weeks, the decision often tilts before the formal evaluation even begins.
We believe the most important insight here is that trust centers are not primarily a security tool. They are a sales and relationship tool that happens to live in the security domain. Organizations that recognize this build trust centers that serve both their security team and their revenue goals simultaneously. The security automation case for this investment is compelling when you measure it in deal velocity and analyst hours recaptured, not just questionnaire volumes.
Streamline your security process with Skypher's trust center solutions
Ready to put trust centers to work for your organization? Here's where to begin.
Skypher is built specifically for enterprise security and compliance teams that are tired of the questionnaire treadmill. Our platform combines a customizable trust center with AI-powered questionnaire automation that can process even the most complex 200-question assessments in under a minute, backed by a confidence score generated by our own proprietary models rather than generic AI outputs.

With Skypher questionnaire automation, your team connects directly to over 30 third-party risk management portals, integrates with Slack, MS Teams, Confluence, Google Drive, and SharePoint, and handles multi-entity enterprise setups with multilingual support. The Skypher trust center platform lets you build a proactive transparency hub that deflects questionnaire volume, accelerates your sales cycle, and gives buyers the verifiable evidence they actually trust. Book a demo and see how fast the shift from reactive to proactive can happen.
Frequently asked questions
Can trust centers completely eliminate security questionnaires?
Trust centers significantly reduce incoming questionnaire volume, but high-risk buyers in regulated industries like banking and finance often have mandated assessment processes that still require formal completion.
How often should trust center content be updated?
Evidence should be refreshed continuously as compliance status, policies, or certifications change, and automated maintenance workflows are strongly recommended to avoid outdated content that undermines buyer confidence.
Is there a difference between trust centers and zero-trust boundaries?
Yes, trust centers are vendor transparency portals for sharing security evidence, while trust boundaries in zero-trust architecture are infrastructure concepts governing internal network segmentation and data flow controls between systems.
Does a trust center make sense for SMBs?
Trust centers deliver the strongest return when selling to security-mature enterprise buyers; SMBs whose customers have minimal security requirements may find the investment difficult to justify.
Recommended
- Trust Center Platform | Share Security & Compliance Posture | Skypher
- Best Practices Vendor Management for Secure Operations
- How to Deflect 30% of Security Questionnaires with an Automated Trust Center
- Security review best practices: efficient strategies for 2026
- Step-by-step guide to managing digital fraud risks effectively
- From 10,000 CVEs to Zero: How GovSignals built FedRAMP-Ready automated CVE remediation in 2 weeks
