Many compliance teams believe completing vendor questionnaires satisfies third-party risk management requirements. That assumption misses the broader landscape of third-party risk management, which extends far beyond initial assessments to continuous monitoring, governance integration, and emerging threats like fourth-party dependencies. In 2026, tech and finance organizations face unprecedented vendor complexity, regulatory scrutiny, and geopolitical disruptions that demand sophisticated, automated approaches. This guide clarifies what TPRM truly encompasses, walks through the complete lifecycle, and shows how modern methodologies and AI-driven automation transform security questionnaire workflows into strategic risk control.
Table of Contents
- Understanding Third-Party Risk Management: Definitions And Lifecycle
- Modern Methodologies And Key Challenges In Third-Party Risk Management
- Applying Automation And Ai To Optimize Third-Party Risk Management Processes
- Aligning Tprm With Regulatory Frameworks And Organizational Governance
- Optimize Your Third-Party Risk Management With Skypher
- Faq
Key takeaways
| Point | Details |
|---|---|
| TPRM definition | Systematic process identifying, assessing, and mitigating risks from vendors that affect security, compliance, and operations. |
| Lifecycle approach | Covers vendor discovery, tiering, due diligence, onboarding, ongoing monitoring, performance management, and offboarding. |
| Automation benefits | AI-powered tools reduce questionnaire response time by over 90% while improving accuracy and enabling continuous monitoring. |
| Regulatory alignment | Frameworks like BCBS and NYDFS require cross-functional governance, proportional risk tiering, and contract enforcement. |
| Emerging complexities | Fourth-party risks, geopolitical disruptions, and AI/cloud dependencies challenge traditional point-in-time assessments. |
Understanding third-party risk management: definitions and lifecycle
Third-party risk management is the process of identifying, assessing, and mitigating risks from external vendors, suppliers, partners, and service providers that could impact an organization's security, compliance, operations, or reputation. For compliance professionals in tech and finance, this definition translates into a structured program that evaluates vendor relationships across their entire lifecycle, not just at contract signature. Understanding the stages of third-party risk management helps teams build proactive controls rather than reactive firefighting.
The TPRM lifecycle includes vendor discovery and inventory, risk assessment and tiering, due diligence, contracting and onboarding, ongoing monitoring, performance management, and offboarding or termination. Each phase serves distinct objectives. Discovery creates visibility into your vendor ecosystem, often revealing shadow IT and unmanaged relationships. Risk tiering applies risk management basics to categorize vendors by inherent and residual risk, enabling proportional resource allocation. Due diligence validates security posture through questionnaires, audits, and third-party assessments before onboarding.
Ongoing monitoring represents the most resource-intensive phase, requiring continuous validation of vendor controls, security incidents, financial health, and regulatory compliance. Performance management tracks SLA adherence and business value, while offboarding ensures secure data return and access revocation. Organizations that skip or rush any phase expose themselves to undetected vulnerabilities.
TPRM lifecycle phases and corresponding activities:
| Phase | Primary Activities | Key Outputs |
|---|---|---|
| Discovery | Vendor inventory, shadow IT detection, relationship mapping | Complete vendor registry |
| Risk Tiering | Inherent risk scoring, data classification, regulatory impact | Risk-based vendor tiers |
| Due Diligence | Security questionnaires, audits, certifications review | Risk assessment reports |
| Onboarding | Contract review, access provisioning, training | Approved vendor status |
| Monitoring | Continuous controls testing, threat intelligence, incident tracking | Ongoing risk scores |
| Performance | SLA tracking, business review, value assessment | Performance dashboards |
| Offboarding | Data return, access removal, contract closure | Secure termination |
Objectives of each lifecycle phase:
- Discovery establishes comprehensive vendor visibility and ownership accountability
- Risk tiering enables efficient resource allocation based on actual threat exposure
- Due diligence validates security claims before granting system access or data sharing
- Onboarding formalizes controls, expectations, and escalation procedures in contracts
- Monitoring detects control drift, new vulnerabilities, and emerging threats in real time
- Performance ensures vendors deliver promised value and maintain service quality
- Offboarding protects sensitive data and prevents orphaned access during transitions
Pro Tip: Prioritize automating discovery and monitoring phases first, as these generate the highest manual workload and deliver immediate efficiency gains through continuous data feeds and automated alerts.
Modern methodologies and key challenges in third-party risk management
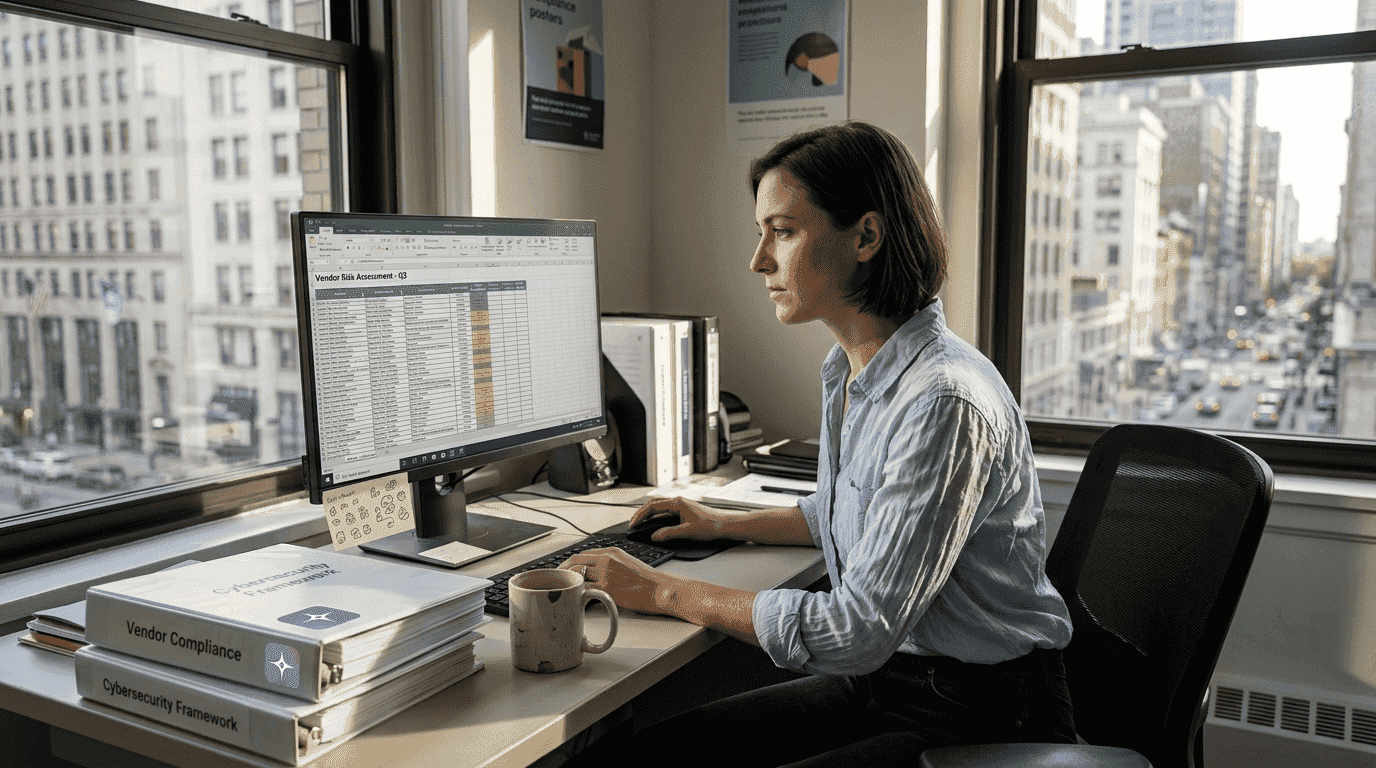
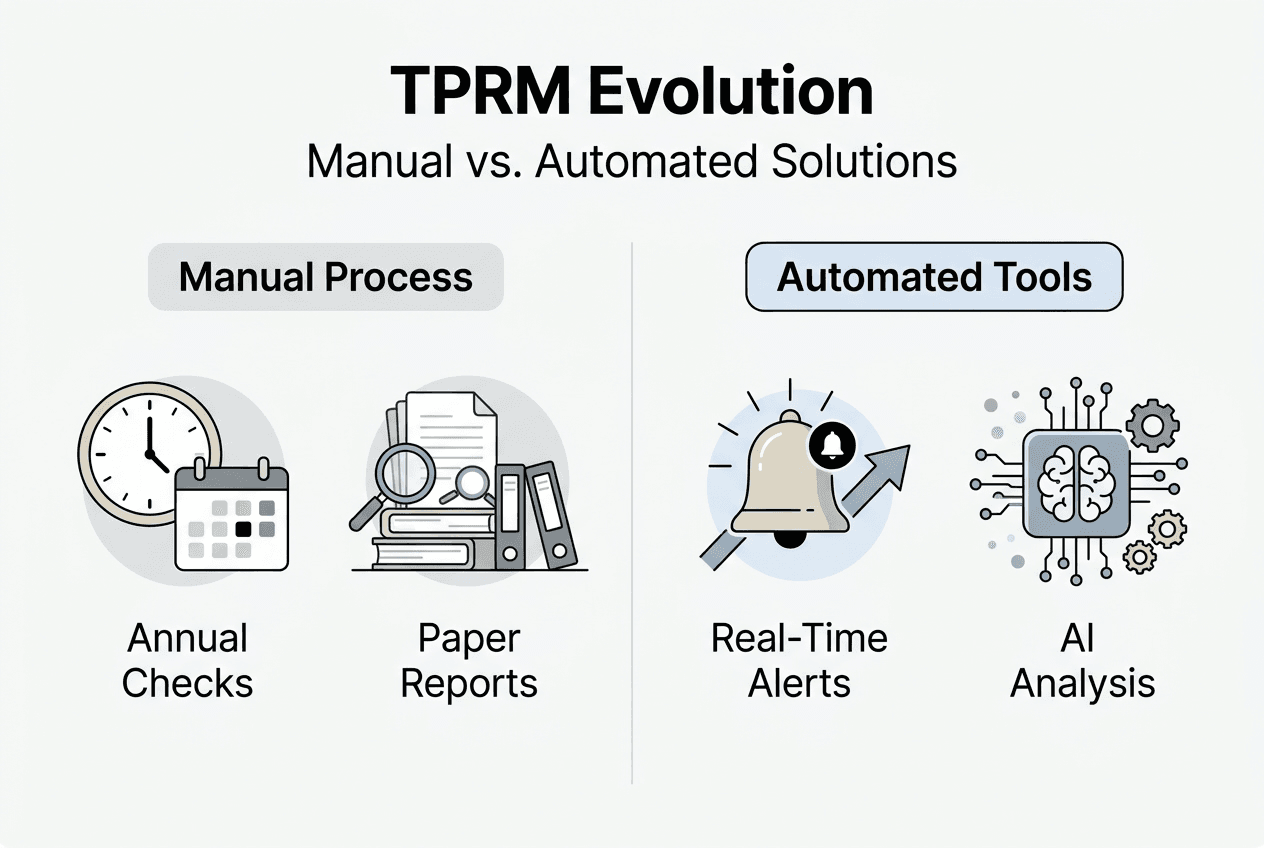
Traditional TPRM relied on annual questionnaires and point-in-time assessments, creating dangerous visibility gaps between reviews. Modern methodologies emphasize proportionality, automation for questionnaires and monitoring, continuous monitoring over point-in-time assessments, and integration with enterprise risk management. This shift reflects the reality that vendor risk profiles change constantly due to breaches, acquisitions, regulatory changes, and infrastructure updates. Tech and finance firms adopting continuous monitoring methodologies detect threats months faster than peers using annual reviews.

Proportional risk tiering directs intensive scrutiny toward high-risk vendors while applying lighter-touch controls to low-risk relationships. A payment processor handling customer financial data warrants quarterly assessments, penetration testing, and on-site audits. An office supply vendor may only need annual certification reviews. This tiering prevents resource waste and assessment fatigue.
Comparison of traditional vs. continuous TPRM approaches:
| Dimension | Traditional Point-in-Time | Continuous Monitoring |
|---|---|---|
| Assessment frequency | Annual or biennial | Real-time with automated triggers |
| Data sources | Questionnaires, static reports | Threat feeds, news, certifications, financial data |
| Resource intensity | High manual effort in bursts | Automated with exception-based reviews |
| Risk detection speed | 6-12 month lag | Days to weeks |
| Vendor coverage | 20-40% of portfolio | 80-100% with tiering |
Edge cases include fourth-party and nth-party risks, high-risk startups and innovators, concentration risk, geopolitical disruptions, and AI/cloud-specific risks. Fourth-party risk arises when your vendor relies on subcontractors you never assessed. A cloud provider's data center operator or a SaaS vendor's authentication service creates hidden dependencies. Geopolitical factors like sanctions, supply chain attacks, and data localization laws add complexity, especially for global operations.
Common TPRM challenges in tech and finance:
- High vendor volumes (500+ relationships) with limited assessment capacity
- Reactive incident response rather than proactive risk hunting
- Siloed vendor data across procurement, legal, IT, and compliance teams
- Questionnaire fatigue leading to incomplete or inaccurate vendor responses
- Lack of standardized metrics to measure program maturity and effectiveness
- Difficulty validating fourth-party and supply chain risks beyond direct vendors
- Balancing innovation speed with thorough due diligence for emerging technologies
Organizations with mature TPRM programs experience 30% fewer third-party related breaches, yet only 35% of firms report proactive, automated monitoring capabilities in 2026.
Pro Tip: Avoid overconfidence in program maturity. Benchmark your TPRM capabilities against industry data annually and conduct tabletop exercises simulating vendor breach scenarios to test response readiness and cross-team coordination.
Applying automation and AI to optimize third-party risk management processes
AI-powered automation transforms security questionnaire workflows from weeks of manual effort into minutes of intelligent processing. Automation with AI and TPRM platforms and tiering vendors by inherent risk enables efficient scoping and monitoring, including validating fourth-party risks. For compliance teams drowning in questionnaire backlogs, AI in security questionnaires delivers immediate productivity gains while improving response accuracy through knowledge base consistency.
AI systems parse incoming questionnaires in any format, map questions to your existing answer library, suggest responses based on historical data and current controls, and flag questions requiring subject matter expert review. This intelligent triage means compliance analysts spend time on genuinely new or high-risk questions rather than copying answers from previous assessments. Machine learning models improve with each completed questionnaire, learning organizational preferences and control language.
Steps for integrating AI in vendor risk tiering and response validation:
- Consolidate vendor data from procurement, contracts, and IT asset management into a unified registry
- Apply inherent risk scoring based on data access, criticality, regulatory scope, and industry sector
- Deploy AI models to analyze vendor security posture from questionnaires, certifications, and external ratings
- Automate response generation for standard questions while routing complex items to experts
- Validate AI-generated responses through sampling and subject matter expert review cycles
- Feed validation results back into models to improve accuracy and reduce false positives
- Integrate continuous monitoring feeds to trigger reassessments when vendor risk profiles change
How automation reduces manual tasks and improves accuracy:
- Eliminates copy-paste errors and inconsistent answers across similar questions
- Maintains version control and audit trails for all questionnaire responses automatically
- Reduces average questionnaire completion time from 15-20 hours to under 2 hours
- Enables real-time collaboration between security, legal, and compliance teams on shared platforms
- Provides analytics on question trends, vendor risk distribution, and program coverage gaps
- Scales questionnaire capacity without proportional headcount increases
Automation benefits in compliance extend beyond questionnaires to ongoing monitoring. AI systems ingest threat intelligence feeds, news alerts, financial data, and certification databases to detect vendor risk changes. When a vendor suffers a breach, faces regulatory action, or loses a key certification, automated alerts trigger reassessment workflows. This continuous validation catches issues that annual reviews miss.
Pro Tip: Combine vendor self-assessments with external security ratings and financial health data for validation. AI platforms can correlate these data sources to identify discrepancies between vendor claims and independent evidence, flagging potential misrepresentation.
Continuous monitoring advantages enabled by AI include early warning of vendor financial distress, real-time breach notification and impact assessment, automated compliance drift detection when certifications expire, and dynamic risk scoring that reflects current threat landscape. TPRM automation shifts teams from reactive questionnaire processing to strategic risk analysis and vendor relationship optimization.
Aligning TPRM with regulatory frameworks and organizational governance
Regulatory expectations for TPRM have intensified across tech and finance sectors. BCBS and NYDFS require firms to align TPRM with regulations and use RACI models for cross-functional ownership involving legal, procurement, IT, and compliance. These frameworks mandate proportional risk management, ongoing monitoring, contract enforcement mechanisms, and board-level oversight. Organizations that treat TPRM as a compliance checkbox rather than integrated risk management face regulatory findings and increased examination intensity.
Relevant TPRM regulations and core requirements:
- BCBS 239 and outsourcing principles require banks to maintain vendor inventories, perform risk assessments, and ensure business continuity for critical vendors
- NYDFS 23 NYCRR 500 mandates cybersecurity programs covering third-party service provider risk management and due diligence
- NIST 800-161 provides supply chain risk management guidance emphasizing continuous monitoring and incident response coordination
- GDPR and CCPA impose data protection obligations on processors and require contracts specifying security responsibilities
- SOX and financial regulations require controls over vendors with access to financial systems or data
Steps to build cross-team accountabilities with RACI:
- Define TPRM process steps from vendor discovery through offboarding in detailed workflow maps
- Identify stakeholders across procurement, legal, IT, security, compliance, and business units
- Assign Responsible parties who execute each task (typically compliance or IT security)
- Designate Accountable owners who approve decisions and bear ultimate responsibility (often CIO or CISO)
- Specify Consulted subject matter experts who provide input (legal for contracts, IT for technical reviews)
- Determine Informed parties who receive updates (business owners, audit, executive leadership)
- Document RACI matrix in policy and communicate through training and onboarding programs
Cross-functional governance prevents common failures where procurement signs contracts without security review, or IT provisions access before compliance completes due diligence. TPRM regulatory alignment requires breaking down silos and establishing clear escalation paths for risk exceptions and vendor issues.
Reactive vs. proactive TPRM governance outcomes:
| Approach | Characteristics | Business Impact |
|---|---|---|
| Reactive | Questionnaires after contract signature, manual tracking, siloed ownership | Delayed risk detection, compliance findings, vendor incidents |
| Proactive | Pre-contract risk assessment, automated monitoring, integrated governance | Early risk mitigation, regulatory confidence, fewer breaches |
Contractual best practices for enforcement:
- Include specific security requirements, audit rights, and incident notification timelines in vendor contracts
- Require vendors to maintain industry certifications relevant to services provided (SOC 2, ISO 27001, PCI DSS)
- Establish performance metrics and service level agreements with financial penalties for non-compliance
- Reserve termination rights for material security failures or regulatory violations
- Mandate insurance coverage appropriate to vendor criticality and data exposure
- Specify data handling, retention, and return procedures aligned with privacy regulations
Empirical benchmarks show many programs remain reactive and manual, with maturity improving through governance integration and contract enforcement. Organizations should measure TPRM effectiveness through metrics like percentage of vendors assessed within tiering timelines, mean time to detect vendor incidents, questionnaire completion rates, and audit findings related to third parties. Vendor risk governance programs that integrate these risk management system modules demonstrate measurably better risk outcomes.
Optimize your third-party risk management with Skypher
Transforming TPRM from manual questionnaire processing to strategic risk management requires purpose-built technology. Skypher's AI security questionnaire automation platform helps tech and finance compliance teams complete security reviews in minutes rather than weeks, enabling the continuous monitoring and proportional risk management this guide recommends.

Skypher's intelligent platform parses questionnaires in any format, automatically maps questions to your knowledge base, and generates accurate responses based on your current security controls. Easy import and export workflows integrate with over 40 TPRM platforms including OneTrust and ServiceNow, eliminating manual data entry and version control headaches. The smart security knowledge base maintains consistent, audit-ready responses across all vendor assessments while learning from each interaction.
Benefits for compliance and risk teams:
- Reduce questionnaire response time by over 90%, from 15-20 hours to under 2 hours per assessment
- Eliminate copy-paste errors and inconsistent answers through centralized knowledge management
- Scale vendor assessment capacity without proportional headcount increases
- Maintain complete audit trails and version history for regulatory examinations
- Enable real-time collaboration across security, legal, and compliance teams on shared platform
Pro Tip: Leverage Skypher's workflow integrations with Slack and Microsoft Teams to route complex questions to subject matter experts automatically, ensuring continuous monitoring doesn't create bottlenecks while maintaining response quality and accuracy.
FAQ
What is third-party risk management?
Third-party risk management is the systematic process of identifying, assessing, and mitigating risks from external vendors, suppliers, and service providers that could impact an organization's security, compliance, operations, or reputation. It encompasses the entire vendor lifecycle from initial discovery through offboarding. For tech and finance organizations, TPRM focuses particularly on cybersecurity risks, data protection, regulatory compliance, and business continuity. Effective programs use proportional risk tiering, continuous monitoring, and cross-functional governance to manage vendor relationships strategically rather than reactively.
How can automation improve handling of third-party security questionnaires?
Automation dramatically reduces the time and manual effort required to complete security questionnaires while improving response accuracy and consistency. AI-powered platforms parse incoming questionnaires, map questions to existing knowledge bases, generate responses based on current controls, and flag items requiring expert review. This enables compliance teams to complete assessments in hours rather than weeks. Automation also maintains version control, creates audit trails, and enables continuous updates when security controls change, ensuring questionnaire responses remain accurate over time without manual tracking.
What are the common challenges tech and finance firms face in TPRM?
Tech and finance organizations typically manage hundreds of vendor relationships but lack resources to assess more than 20 to 40 percent of their portfolio annually. Most programs remain reactive, responding to questionnaires and incidents rather than proactively monitoring vendor risk. Complex challenges include fourth-party risks from vendor subcontractors, geopolitical factors affecting supply chains, concentration risk when critical services depend on few providers, and emerging technology risks from AI and cloud services. Siloed vendor data across procurement, legal, IT, and compliance teams further hampers effective risk visibility and decision making.
How does aligning TPRM with regulations benefit organizations?
Regulatory frameworks like BCBS, NYDFS, and NIST provide proven methodologies and maturity benchmarks that improve TPRM effectiveness beyond basic compliance. These standards require proportional risk tiering, continuous monitoring, contract enforcement, and board oversight that collectively reduce third-party breach risk. Cross-functional governance models mandated by regulations break down silos between procurement, legal, IT, and compliance, ensuring vendors undergo security review before contract signature and access provisioning. Organizations with mature, regulation-aligned programs demonstrate measurably better risk outcomes and face fewer regulatory findings during examinations.