TL;DR:
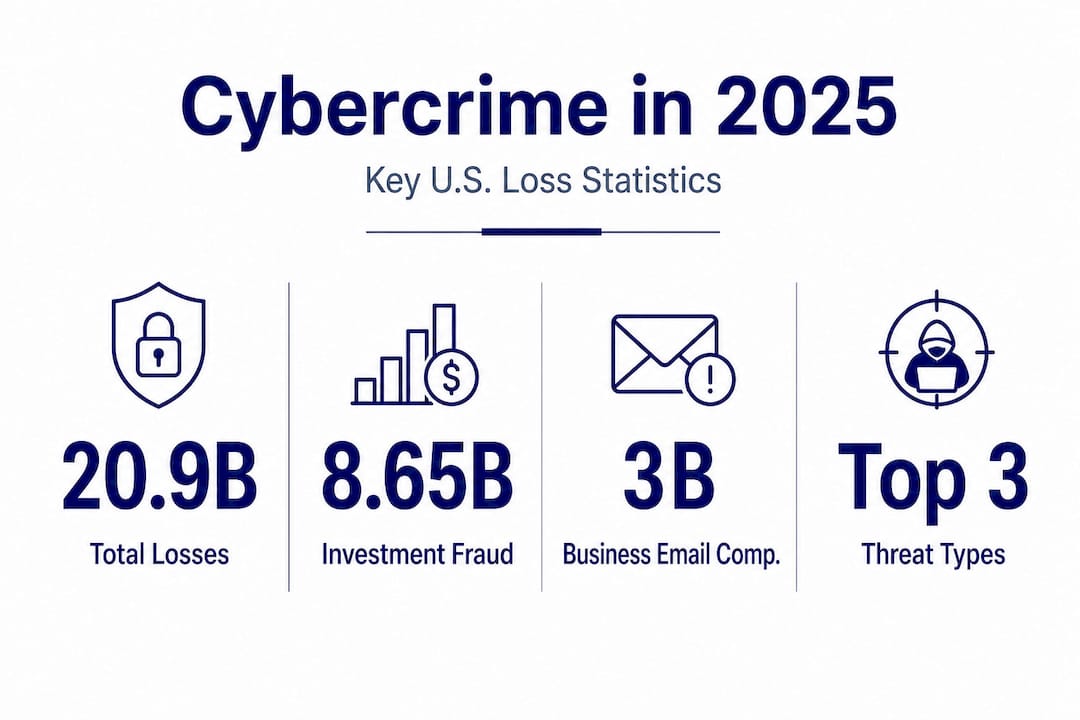
- Cybercrime losses in the U.S. reached $20.9 billion in 2025, driven mainly by investment fraud and BEC.
- Zero Trust Architecture and continuous verification are essential for managing hybrid and cloud environments.
- AI accelerates threat detection, data protection, and compliance, but organizations must adopt a risk-based, adaptive approach.
U.S. organizations absorbed $20.9 billion in cybercrime losses in 2025 alone, a 26% jump from the prior year, and finance and tech firms bore the heaviest share of that damage. The pressure on security leaders has never been more direct: boards want accountability, regulators want documentation, and attackers want whatever you have left unguarded. This article walks through the most critical trends reshaping risk management and compliance right now, from Zero Trust rollouts and AI-driven threats to talent shortfalls and machine identity sprawl, and gives you concrete frameworks for responding.
Table of Contents
- The state of cyber threats: Key statistics and recent shifts
- Zero Trust Architecture and dynamic defense: Evolving access in hybrid environments
- AI's impact on unstructured data and machine identity management
- Talent crisis and insider risk: Skills shortages meet advanced threats
- Tactical AI implementations: Real-world security risk management in 2025
- Why "best practices" for 2025 may not be enough: A risk-based, adaptive mindset
- Next steps: Reinforce your risk and compliance strategy with Skypher
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Cybercrime surge | Cybercrime losses reached $20.9 billion in 2025, emphasizing the need for updated defense strategies. |
| Zero Trust essentials | Zero Trust Architecture is a must for hybrid and cloud environments to minimize risks in 2025. |
| AI shifts risk focus | Generative AI puts unstructured data and machine identities at the forefront of security priorities. |
| Talent shortage persists | A critical skills gap and high insider risks require automation and ongoing training for effective defense. |
| Tactical AI advantage | AI's real-world application brings measurable improvements to risk management and compliance. |
The state of cyber threats: Key statistics and recent shifts
With the threat landscape changing rapidly, understanding its current state is foundational to any planning conversation.
The FBI's Internet Crime Complaint Center confirmed that cybercrime losses hit $20.9B in the U.S. last year, with three attack types dominating total losses.
| Attack type | 2025 reported losses | Notable detail |
|---|---|---|
| Investment fraud | $8.65 billion | Largest single category |
| Business email compromise (BEC) | $3.0 billion | Targets finance and ops teams |
| Ransomware | High complaint volume | Over 3,600 complaints filed |
What makes these numbers particularly alarming for security architects is not just the scale, but the speed. Phishing, the delivery mechanism behind most of these attacks, increased by 1,200% after the widespread adoption of generative AI (GenAI) tools. Threat actors use GenAI to craft contextually accurate spear-phishing emails at industrial scale, eliminating the grammatical errors that used to serve as warning flags for users.
The risk profile for 2025 is therefore different from previous years in a meaningful structural way. It is not just that attacks are more frequent. It is that they are harder to distinguish from legitimate business communication. Social engineering now targets employees who are well-trained but still susceptible to carefully personalized messages.
- Business email compromise remains the highest-ROI attack for organized criminal groups, often requiring zero technical exploits.
- Ransomware is increasingly targeting operational technology (OT) environments in finance and critical infrastructure sectors.
- AI-enhanced phishing can now mimic internal tone, formatting, and seniority accurately enough to deceive senior staff.
- Third-party exposure continues to expand attack surfaces as organizations rely on more SaaS vendors and API integrations.
"The conversation has shifted from 'if we get attacked' to 'how quickly can we contain it and continue operating.' Every board we work with now wants a response timeline, not just a prevention story."
Understanding where and how attacks happen is only part of the picture. Reviewing 2025 security questionnaire trends shows that even vendor risk programs are increasingly factoring in GenAI attack vectors as a standard due-diligence requirement.
Zero Trust Architecture and dynamic defense: Evolving access in hybrid environments
Against this backdrop of evolving threats, organizations must rethink the very basics of access and trust.
Zero Trust Architecture (ZTA) operates on one foundational rule: trust nothing, verify everything, every time. It replaces the old perimeter model where users and systems inside a network boundary received implicit trust. In its place, every access request is authenticated, authorized, and continuously evaluated regardless of where it originates.
NIST SP 1800-35 provides 19 concrete implementation examples using commercially available technology, covering hybrid and cloud environments. This is one of the most actionable federal guidance documents for enterprise security teams working through phased ZTA adoption.
Traditional perimeter vs. Zero Trust: A side-by-side comparison
| Dimension | Traditional perimeter | Zero Trust |
|---|---|---|
| Trust model | Implicit inside the network | Continuous verification required |
| Access scope | Broad, role-based assumptions | Least privilege, session-by-session |
| Lateral movement risk | High once perimeter is breached | Contained by micro-segmentation |
| Cloud compatibility | Limited; built for on-premise | Native support for hybrid/cloud |
| Monitoring | Perimeter-focused logging | Continuous behavioral analytics |
Implementing ZTA in a hybrid environment is a phased effort, not a single project. Here is a practical sequence for organizations just starting or mid-journey:
- Map all identities and assets. You cannot apply Zero Trust controls to what you cannot see. Inventory includes human identities, service accounts, APIs, and machine identities.
- Enforce multi-factor authentication (MFA) universally. This is the lowest-effort, highest-return ZTA control available and should be non-negotiable for any user or system with sensitive access.
- Implement least-privilege access policies. Review standing permissions quarterly and remove what is unnecessary. Temporary, just-in-time access models are increasingly standard in financial services.
- Segment networks and workloads. Micro-segmentation limits how far an attacker can move after compromising a single account or endpoint.
- Enable continuous monitoring and anomaly detection. Behavioral baselines help you identify when a legitimate account starts behaving unusually, which is often the first signal of a compromised credential or insider threat.
Pro Tip: Do not try to achieve full ZTA maturity in one cycle. NIST's guidance specifically acknowledges that most organizations operate in a hybrid state for years. Prioritize your highest-risk access paths first, typically privileged accounts, third-party connections, and cloud workloads, and build from there.
Combining ZTA with solid compliance hygiene also reduces the friction of vendor audits. Following cybersecurity compliance tips built around a Zero Trust framework often shortens security review cycles because your controls are already documented and verifiable.
AI's impact on unstructured data and machine identity management
Reimagining access is only part of the story; AI has redefined what needs to be protected and how.

Gartner's top cybersecurity trends for 2025 flag two specific shifts that security teams in tech and finance need to internalize: the move toward protecting unstructured data at scale, and the explosion of machine identities from AI, cloud, and DevOps pipelines.
Unstructured data includes text documents, images, audio files, videos, and model outputs. Historically, these were secondary concerns compared to structured databases. GenAI has flipped that priority. Sensitive intellectual property, customer communications, internal analyses, and proprietary model training data all live in unstructured formats, and they are actively targeted.
- AI-generated outputs (reports, code, models) now need classification and access controls just like structured financial records.
- Cloud storage sprawl means unstructured data sits across dozens of environments with inconsistent permission models.
- Data lineage becomes critical: you need to know where AI-ingested data came from and what it was used to produce.
- Regulatory frameworks like GDPR and emerging AI governance rules increasingly require documentation of unstructured data flows.
Machine identity management is the parallel challenge. Every API key, service account, container, bot, and AI agent that interacts with your environment is a machine identity. As DevOps pipelines accelerate and AI agents proliferate, the number of machine identities in a typical enterprise now significantly exceeds human identities. The attack surface this creates is enormous.
Pro Tip: Treat machine identities with the same rigor you apply to privileged human accounts. Rotate credentials automatically, apply least-privilege policies, and audit usage logs regularly. Most organizations do not discover orphaned service account abuse until long after the compromise.
Operationalizing these protections requires AI-enabled compliance frameworks that can move at the pace of your AI deployments. Manual reviews simply cannot keep up with the rate at which new machine identities and data flows are created in modern tech and finance environments. Investing in AI-driven risk management tooling closes that gap.
Talent crisis and insider risk: Skills shortages meet advanced threats
Technology alone is not enough. People and processes play a critical role in evolving security strategies.
The cybersecurity talent shortage is not a future problem. It is active and measurable right now. There were 514,000 open cybersecurity positions in the U.S. between May 2024 and April 2025. At the same time, insider threats cost organizations an average of $17.4 million annually according to Ponemon Institute data. These two problems compound each other: understaffed teams have less capacity to monitor for insider risk, and insider incidents consume disproportionate response resources.
| Insider threat category | Average annual cost | Common vectors |
|---|---|---|
| Negligent insider | $7.2M | Misconfiguration, accidental exposure |
| Malicious insider | $4.8M | Data theft, sabotage, credential abuse |
| Credential theft | $5.4M | Phishing, password reuse, social engineering |
"Insider threat programs are often treated as an HR issue when they are fundamentally a security architecture issue. The technology, the policy, and the people response all have to work together."
Responding to this dual pressure requires pragmatic prioritization:
- Automate repetitive security operations tasks. Threat triage, log analysis, alert correlation, and compliance documentation are all candidates for automation. This frees analysts to focus on high-complexity work.
- Build structured onboarding and continuous training programs. Security awareness training is most effective when it is role-specific and scenario-based, not generic annual checkbox training.
- Implement behavioral analytics for insider risk detection. User and entity behavior analytics (UEBA) tools establish baselines and flag deviations that indicate potential insider activity without requiring constant manual monitoring.
- Segment access tightly for sensitive roles. Least-privilege policies reduce the blast radius if an insider account is misused or compromised.
- Create clear and trusted reporting channels. Many insider incidents are discovered when colleagues report suspicious behavior. Make it easy and safe to do so.
Addressing insider threat mitigation through a combination of access controls, behavioral monitoring, and workforce development gives organizations a more resilient posture without requiring a proportional increase in headcount.
Tactical AI implementations: Real-world security risk management in 2025
Solving for people and process challenges creates opportunity. AI offers speed and scale for risk reduction that no purely human-driven program can match.
Gartner confirms that tactical AI implementations are now delivering measurable security risk management (SRM) outcomes, not just future-state projections. Organizations that have moved beyond pilots are reporting faster detection times, lower false-positive rates, and dramatically reduced compliance review cycles.
Here is where AI is delivering the most concrete impact right now:
- Automated compliance reviews. AI tools can ingest questionnaires, cross-reference existing policy documentation, and generate accurate responses in a fraction of the time manual processes require. This is especially high-value in finance where vendor due diligence cycles are frequent and documentation-intensive.
- Threat detection and correlation. AI-driven SIEM (security information and event management) platforms correlate signals across massive event volumes that human analysts cannot process at speed, surfacing genuine threats faster.
- Vulnerability prioritization. AI models score vulnerabilities based on exploitability, asset criticality, and business context, helping teams focus remediation effort where it matters most rather than working from a raw CVSS score list.
- Incident response acceleration. AI-assisted playbooks guide analysts through response steps dynamically, reducing response time and ensuring consistent handling across incidents.
- Third-party risk scoring. AI tools assess vendor security posture continuously rather than at point-in-time questionnaire cycles, providing real-time risk visibility into your supply chain.
Pro Tip: Do not let perfect be the enemy of good when deploying tactical AI in security operations. Start with the workflows that are already well-documented and repetitive, compliance questionnaire responses, alert triage, and patch prioritization, and measure the time savings rigorously. Those early wins build the internal credibility to fund larger SRM investments.
Reviewing AI security automation trends shows that the organizations getting the most value are those treating AI as an augmentation layer on top of existing processes rather than a wholesale replacement. Similarly, AI for risk management platforms are increasingly integrated with governance workflows, giving security teams a single system of record for risk data.
Why "best practices" for 2025 may not be enough: A risk-based, adaptive mindset
The gap between organizational confidence and actual threat reality is striking. CompTIA data shows 68% of organizations rate their security capabilities as highly effective, yet phishing rates rose 1,200% after GenAI adoption. Both facts are true at the same time. That tension tells us something important: best practices keep organizations defensible in audits, but they do not automatically keep them safe from adaptive adversaries.
Standard frameworks, SOC 2, ISO 27001, NIST CSF, are necessary. They create structure, accountability, and a shared language with customers and regulators. But threat actors do not operate inside framework timelines. They iterate in days. They test against the controls your organization most recently documented and look for what changed since your last audit.
The practical implication for security leaders is this: treat your security posture as a living system, not a certification you renew annually. Risk-based prioritization means continuously asking which controls have the highest marginal impact given your current threat exposure, not which ones appear on a compliance checklist. For organizations using AI agents, managing third-party vendors, or expanding into new markets, the risk profile can shift faster than any static best practice can accommodate.
Adaptive review strategies powered by AI give teams the ability to reassess risk exposure dynamically as the environment changes. The organizations that will be most resilient heading into the next wave of GenAI-driven threats are those that have built flexibility into their defense posture rather than simply hardening around the last set of known threats.
Next steps: Reinforce your risk and compliance strategy with Skypher
The trends covered in this article share a common thread: speed. Attacks are faster, AI-generated threats are more convincing, vendor ecosystems are larger, and compliance expectations are rising. Manual processes simply cannot keep up.

Skypher's AI-powered platform is built specifically for the compliance and risk management workflows that consume the most security team bandwidth. With security questionnaire automation that handles every format and integrates with over 40 TPRM platforms, your team can complete vendor reviews in minutes instead of days. The platform's AI recommendation engine draws on your existing policy library to generate accurate, consistent responses, and real-time collaboration tools keep every stakeholder aligned without version-control chaos. If your team is managing multiple entities, multilingual requirements, or complex enterprise setups, Skypher handles those without custom development work. The result is faster sales cycles, cleaner audit trails, and a compliance function that actually scales with your business.
Frequently asked questions
Which cyber threats are projected to cause the most damage in 2025?
Investment fraud ($8.65B), business email compromise ($3B), and ransomware represent the three costliest attack categories according to FBI IC3 data, with total U.S. losses reaching $20.9 billion in 2025.
How can organizations address the cybersecurity talent shortage?
Automating repetitive security tasks, such as compliance reviews and alert triage, frees existing staff for higher-complexity work, helping offset the pressure from 514,000 unfilled positions across the industry.
What is the core benefit of Zero Trust Architecture in 2025?
Zero Trust enforces continuous verification and least-privilege access on every request, dramatically reducing the risk of lateral movement in breach scenarios. NIST SP 1800-35 outlines 19 implementation approaches suited to hybrid and cloud environments.
How has GenAI changed the cybersecurity risk landscape?
GenAI has made unstructured data a primary target and enabled 1,200% increases in phishing sophistication and volume, fundamentally shifting what organizations need to protect and how quickly they need to respond.
What are organizations doing to respond to rising insider threats?
Leading security teams are combining behavioral analytics, tighter access segmentation, and structured training programs to contain incidents that average $17.4M annually in total organizational cost.
Recommended
- Top cybersecurity compliance tips for tech & finance teams
- Compliance Risk Meaning: Impact on Security Reviews
- Security automation trends 2026: AI, efficiency, and risk
- Stay ahead of security questionnaire trends for 2025
- Cybersecurity Best Practices: Protect Your Business & Data
- 21 CFR Part 11 Cybersecurity Compliance Guide | Symmetry Network Management
