TL;DR:
- Manual risk tracking is often ineffective during critical moments, leading to regulatory and security gaps.
- Integrating structured frameworks like NIST IR 8286 and automating data flows improves real-time risk visibility.
- Successful risk management combines automation with a strong risk culture and proactive frontline ownership.
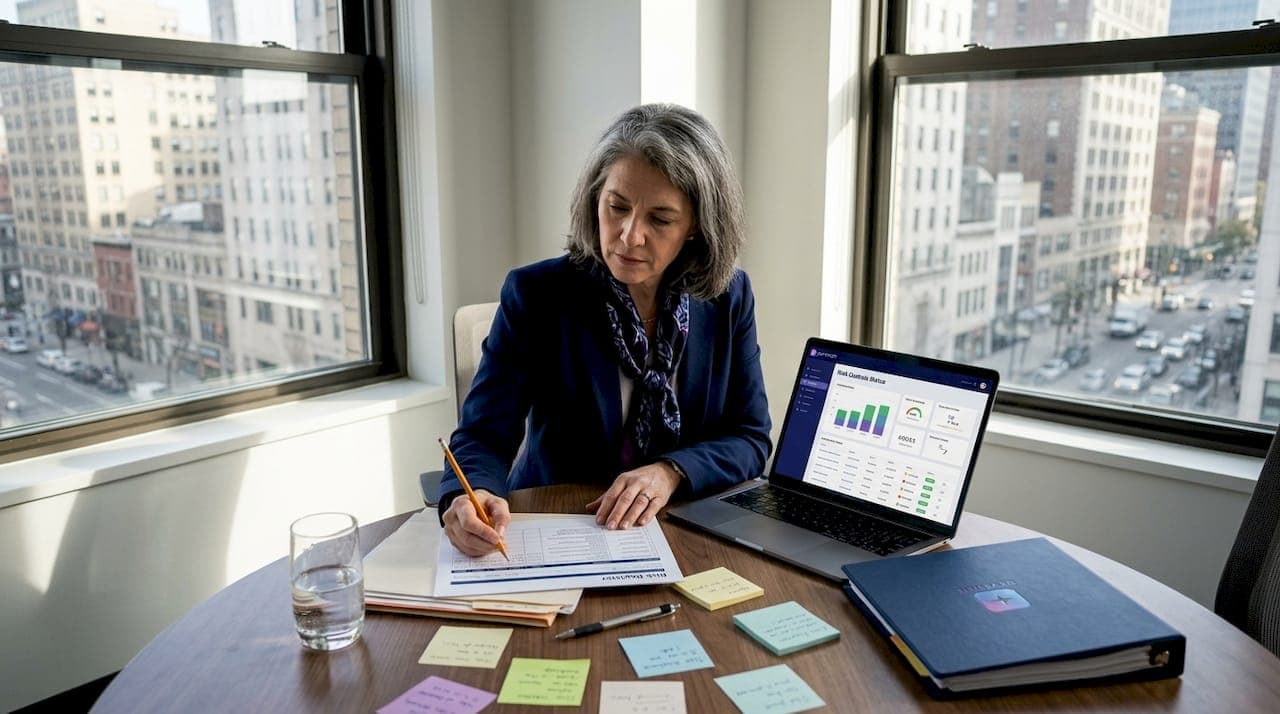
Manual risk tracking fails at the worst possible moment. A mid-size fintech firm discovers a critical vendor has been storing customer data without encryption, not from a proactive audit, but from a client complaint during contract renewal. By then, regulatory exposure is real, remediation costs are mounting, and the security questionnaire that should have caught the gap was sitting in someone's inbox for three weeks. This guide walks you through a practical, structured path to modernize your risk management program using automation, dynamic controls, and proven frameworks, so your team catches problems before they become headlines.
Table of Contents
- Modern challenges in risk management for tech and finance
- Essential components and tools for effective risk management
- Step-by-step process to enhance risk management with automation
- Monitoring, stress testing, and verifying your risk strategy
- The uncomfortable truth: Automation alone isn't enough for great risk management
- Take your risk management strategy to the next level
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Centralize risk data | Bringing all risk information into one platform improves oversight and enables automation. |
| Use modern frameworks | Applying NIST IR 8286 and similar standards builds strong, scalable processes. |
| Leverage automation | Automating assessments and monitoring increases speed and reduces manual errors. |
| Empower the front line | Giving teams ownership strengthens response time and risk awareness. |
| Monitor and optimize | Continual stress testing and KPI monitoring ensure your risk program adapts to change. |
Modern challenges in risk management for tech and finance
Risk and compliance officers in tech and finance face a uniquely difficult environment. Regulatory requirements shift constantly. New threat types emerge faster than most teams can update their controls. And the volume of third-party relationships that need ongoing scrutiny keeps growing.
The core problem is not a lack of effort. It is structural. Most organizations still rely on fragmented systems, spreadsheet-based risk registers, and email-driven workflows that were never designed for the speed or complexity of modern risk management. When your risk data lives in five different tools and three shared drives, you cannot get a reliable picture of your exposure at any given moment.
Here is what that fragmentation actually costs you:
- Delayed detection: Siloed data means threats go unnoticed for weeks or months, dramatically increasing the cost of response.
- Inconsistent measurement: Different teams use different scoring methods, making it impossible to aggregate risk at the enterprise level.
- Regulatory blind spots: When new requirements drop, manual processes cannot adapt quickly enough, leaving gaps that auditors find.
- Vendor risk gaps: Third-party assessments get deprioritized or completed inconsistently, creating exposure that only surfaces during incidents.
Consider a realistic scenario. A large insurance technology company maintains a risk register that is updated quarterly. A critical SaaS vendor introduces a new data processing practice mid-quarter. Nobody flags it. The next quarterly review catches it, but by then the vendor has processed millions of records under the new practice. The compliance gap is now a regulatory reporting obligation. This is exactly the kind of failure that compliance risks in automation programs are designed to prevent, but only when the underlying risk management infrastructure supports real-time visibility.
The NIST IR 8286B guidance is explicit: integrating cybersecurity risks into enterprise risk management using the NIST IR 8286 series, Cybersecurity Risk Registers (CSRRs), and Business Impact Analysis means you can prioritize and aggregate risks across organizational levels rather than managing them in isolation. That integration is the baseline. Without it, everything else is guesswork.
Essential components and tools for effective risk management
Before you can automate anything meaningfully, you need the right building blocks in place. A framework without supporting tools is just documentation. Tools without a framework produce noise. The combination is what creates reliable, scalable risk management.
The NIST IR 8286 series provides a structured approach to connecting cybersecurity risk registers with enterprise-level risk appetite and Business Impact Analysis. This matters because it gives your team a common language and a consistent methodology, which is the prerequisite for meaningful automation.
Here is a practical overview of the key components and how they work together:
| Component | Purpose | Automation potential |
|---|---|---|
| Cybersecurity Risk Register (CSRR) | Centralize and track identified risks | High: auto-populate from assessments |
| Business Impact Analysis (BIA) | Prioritize risks by operational impact | Medium: structured templates, AI scoring |
| Key Risk Indicators (KRIs) | Early warning signals for emerging threats | High: real-time dashboards and alerts |
| Third-party assessments | Evaluate vendor security posture | High: automated questionnaires and scoring |
| Assurance and audit tools | Validate controls are working | Medium: automated evidence collection |
| Dynamic risk modeling | Simulate scenarios and stress test exposure | Medium to high: AI-assisted modeling |
The shift from static to dynamic risk modeling is one of the most significant improvements you can make. Static models tell you what your risk looked like last quarter. Dynamic models, powered by real-time data feeds and AI-assisted analysis, tell you what your risk looks like right now and where it is trending. That is a fundamentally different level of insight, and it is increasingly accessible through modern security automation trends in the GRC space.
Key Risk Indicators deserve special attention. A KRI is a measurable metric that signals when a risk is approaching or exceeding your appetite threshold. Examples include the number of overdue vendor assessments, the percentage of critical controls with expired evidence, or the volume of unresolved findings from penetration testing. When these indicators are monitored automatically and trigger alerts, your team can act before a threshold is breached rather than after.
Pro Tip: Start with five to seven KRIs that map directly to your top enterprise risks. More than that, and the signal gets lost in the noise. Fewer than that, and you have blind spots. Review and refine the list every six months as your risk profile evolves.
Centralized risk data is non-negotiable. Every tool you use, whether it is a GRC platform, a vendor management system, or a security questionnaire tool, needs to feed into a single source of truth. Without that centralization, you are managing risk by committee and hoping everyone has the same information. They rarely do.
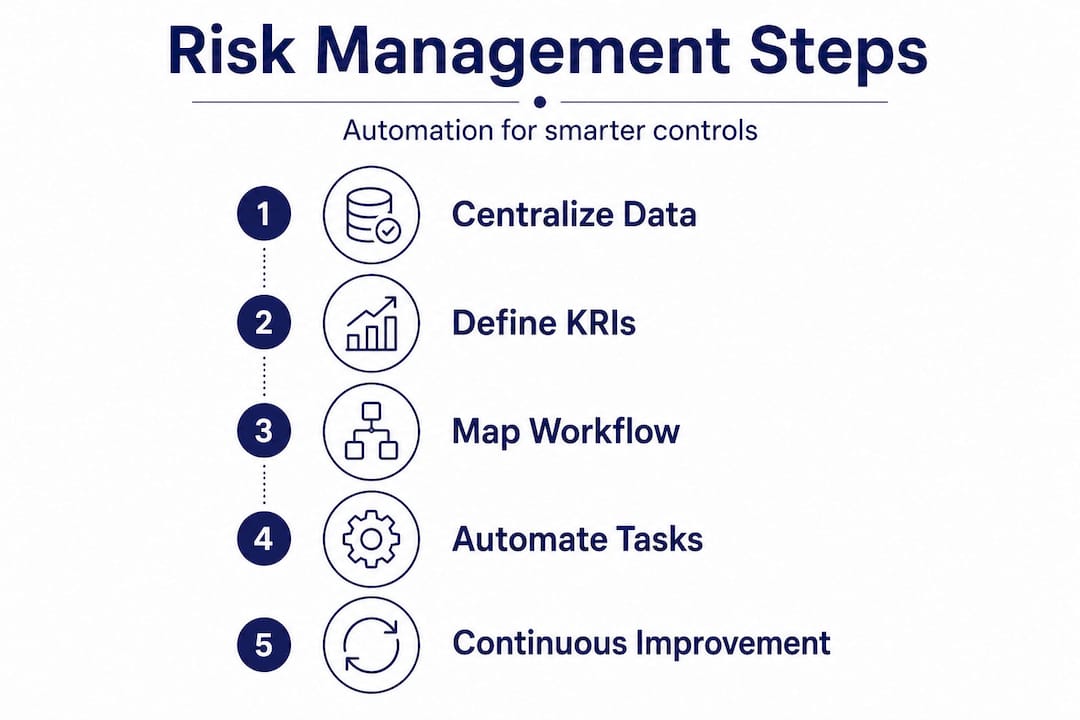
Step-by-step process to enhance risk management with automation
Knowing what you need is different from knowing how to build it. Here is a structured workflow that takes you from initial risk identification through ongoing optimization, with automation integrated at each stage.
-
Identify and categorize risks using a structured framework. Start with the NIST IR 8286 series to map cybersecurity risks to business objectives. Use your CSRR to capture each risk with consistent attributes: likelihood, impact, owner, and current controls. This step creates the inventory that everything else depends on.
-
Conduct Business Impact Analysis for prioritization. Not all risks deserve equal attention. BIA helps you rank risks by their potential effect on critical business processes. Automate the data collection phase using structured templates and integrate outputs directly into your risk register so prioritization is always current.
-
Aggregate and centralize risk data. Pull data from all sources, vendor assessments, internal audits, penetration test results, and compliance monitoring tools, into a single platform. This is where integration capability becomes critical. Platforms that connect with your existing tools eliminate the manual data transfer that creates delays and errors.
-
Automate risk assessments and reporting cycles. Replace manual questionnaire distribution and follow-up with automated workflows. Modern platforms can send, collect, score, and escalate security questionnaires without human intervention at each step. Reporting that used to take days can run in minutes. For a deeper look at making this work in practice, GRC automation tips cover common implementation pitfalls worth avoiding.
-
Empower front-line teams with risk ownership. The 2026 practitioner guidance is clear: centralizing data and automating assurance only works when front-line ownership is built into the model. Risk owners need dashboards, alerts, and clear escalation paths. Without that, automation creates reports that nobody acts on.
-
Implement dynamic risk modeling and KRI monitoring. Set up automated alerts when KRIs breach thresholds. Use scenario modeling to understand how a single vendor failure or regulatory change would cascade through your risk profile. This is where risk management tips for tech leaders often focus, because dynamic modeling is the clearest differentiator between reactive and proactive programs.
-
Integrate third-party risk management into the same workflow. Vendor risk cannot be managed in a separate silo. Your third-party risk management process should feed directly into your enterprise risk register, with automated reassessment triggers based on contract milestones, incident reports, or changes in vendor security posture.
Here is a comparison of manual versus automated approaches at key workflow stages:
| Workflow stage | Manual approach | Automated approach |
|---|---|---|
| Vendor assessment | Email questionnaires, weeks of follow-up | Auto-send, collect, and score in hours |
| Risk register updates | Quarterly manual review | Real-time updates from integrated data sources |
| Reporting | Days of spreadsheet consolidation | On-demand dashboards and scheduled reports |
| Escalation | Relies on individual judgment | Rules-based alerts with defined thresholds |
| Evidence collection | Manual document requests | Automated evidence pulls from integrated systems |
"The most resilient risk programs we see are not the ones with the most sophisticated tools. They are the ones where automation handles the routine work and people focus on judgment-intensive decisions." This reflects the practitioner consensus that digital fraud risk management and broader risk programs share: technology accelerates, but human oversight governs.
Common mistakes to avoid at this stage: treating automation as a one-time implementation rather than an ongoing program, failing to define clear data ownership before centralizing, and automating broken processes instead of fixing them first.
Pro Tip: Before automating any assessment workflow, map the current process end to end and identify every handoff point. Handoffs are where delays and errors concentrate. Automation should eliminate unnecessary handoffs, not just speed up the existing ones.
Monitoring, stress testing, and verifying your risk strategy
Building a risk management program is not a project with an end date. It is an ongoing operational discipline. Monitoring and stress testing are how you verify that what you built is actually working.

Effective monitoring uses both leading and lagging indicators. Lagging indicators, like the number of incidents in the past quarter or the average time to remediate findings, tell you how you performed. Leading indicators, like the percentage of vendors with overdue reassessments or the trend in open critical findings, tell you where you are heading. Both matter, but leading indicators are what give you the ability to intervene before a problem becomes a crisis.
Key monitoring practices for mature risk programs include:
- Automated KRI dashboards that update in real time and alert owners when thresholds are approached, not just breached.
- Continuous control monitoring that validates evidence of control operation without waiting for annual audits.
- Vendor posture tracking that flags changes in a third party's security ratings, breach history, or compliance certifications.
- Regulatory change monitoring that identifies new requirements and maps them to existing controls, surfacing gaps automatically.
Stress testing is a discipline borrowed from financial risk management, and it translates well to cybersecurity and operational risk. The idea is straightforward: define extreme but plausible scenarios, then test whether your controls and your risk appetite would hold. What happens if your top three vendors all have a simultaneous incident? What if a new regulation requires data localization within 90 days? Working through these scenarios reveals weaknesses in your program that routine monitoring will not catch.
The practitioner guidance for 2026 emphasizes that stress testing oversight, combined with dynamic risk modeling and KRI-based proactivity, is what separates programs that survive scrutiny from those that only look good on paper. Stress testing should be a scheduled activity, not something triggered only by a near-miss.
Continuous improvement closes the loop. Every monitoring finding, every stress test result, and every incident post-mortem should feed back into your risk register and your control framework. The benefits of automating compliance are most fully realized when the automation infrastructure supports this feedback loop, not just the initial assessment cycle.
The uncomfortable truth: Automation alone isn't enough for great risk management
Here is something the vendor marketing materials will not tell you. Organizations that invest heavily in automation without investing equally in risk culture consistently underperform compared to those that do both. The tools surface the risks. People have to care enough to act on them.
The "checkbox" automation trap is real. A team deploys an automated questionnaire platform, scores improve, completion rates go up, and leadership declares the vendor risk program fixed. Six months later, a vendor breach reveals that the questionnaire responses were copy-pasted from a previous year and nobody reviewed the answers for accuracy. The automation worked perfectly. The program still failed.
Sustainable risk management improvement requires three things to align: people who understand and own risk, processes that are designed for the actual threat environment, and technology that makes both more effective. When any one of those is weak, the other two cannot compensate. We have seen this pattern repeatedly, and it is why security review automation insights consistently point to governance and accountability structures as the differentiating factor between programs that improve and programs that stagnate.
The contrarian lesson is this: before you add more automation, audit your risk culture. Are risk owners engaged? Do front-line teams understand why the controls exist? Is leadership asking the right questions when KRIs flash red? If the answer to any of those is no, more technology will not fix it. It will just produce better-looking reports of the same underlying problems.
Take your risk management strategy to the next level
The path from fragmented, manual risk management to a dynamic, automated program is well-defined. The challenge is execution at scale, especially when your team is already managing a full compliance calendar, vendor relationships, and evolving regulatory requirements.

Skypher is built for exactly this environment. Our security questionnaires automation platform handles the full assessment lifecycle, from distributing questionnaires in any format to scoring responses and escalating findings, all integrated with the GRC and TPRM platforms your team already uses. The AI-powered recommendation engine goes further, surfacing the most accurate answers from your existing documentation so your team spends time on judgment, not data entry. With support for over 40 platform integrations, real-time collaboration, multilingual capabilities, and enterprise-grade security, Skypher fits into your existing workflow without requiring a rip-and-replace approach. Request a demo and see how much faster your next vendor assessment cycle can move.
Frequently asked questions
What is the most effective way to identify emerging risks?
Dynamic risk modeling and KRIs give you the earliest possible signal of emerging threats by tracking measurable indicators against defined thresholds, so you can act before a risk materializes into an incident.
How do automation tools reduce risk management workload?
Automation handles the repetitive, high-volume tasks like questionnaire distribution, evidence collection, and status reporting, and when you centralize data and automate assurance, your team is freed to focus on analysis and decision-making instead of data wrangling.
What frameworks are recommended for integrating cybersecurity into ERM?
The NIST IR 8286 series, combined with Cybersecurity Risk Registers and Business Impact Analysis, is the leading practice for connecting cybersecurity risk to enterprise-level risk management in a structured, auditable way.
What is the role of stress testing in improving risk management?
Stress testing oversight validates that your risk appetite and controls hold up under extreme but realistic scenarios, revealing weaknesses that routine monitoring and annual audits typically miss.
How can front-line teams help strengthen risk management?
When you empower front-line ownership by giving staff clear accountability, real-time dashboards, and defined escalation paths, risk response becomes faster and more proactive across the entire organization rather than concentrated in a central compliance team.
Recommended
- Security automation trends 2026: AI, efficiency, and risk
- Why automate compliance in 2026: benefits for finance & tech firms
- Vendor Risk Manager: Streamlining Security Compliance
- 7 Essential Risk Management Tips for Tech Leaders
- Enterprise Automation: Optimizing Business Processes Effectively
- Step-by-step guide to managing digital fraud risks effectively