TL;DR:
- Security automation significantly reduces vulnerabilities and enhances response efficiency in modern organizations.
- Proper deployment drives measurable improvements, such as 70% vulnerability reduction and a 90% increase in pre-deployment defect detection.
Security automation is not an incremental upgrade. Organizations that treat it as one are leaving serious risk reduction on the table. Stripe's DevSecOps automation cut vulnerabilities by 70%, reduced mean time to remediate (MTTR) for critical CVEs to just 14 days, and pushed pre-deployment defect detection from 32% to 89%. Those are not marginal gains. This guide breaks down the real mechanics of security automation for CISOs and GRC executives in tech and finance, covering measurable outcomes, honest comparisons with manual processes, and the strategic moves that separate successful deployments from expensive mistakes.
Table of Contents
- Why security automation matters in 2026
- Core benefits of security automation: Real-world outcomes
- Comparing manual vs. automated security processes
- How to maximize security automation ROI: Pitfalls and expert strategies
- Beyond efficiency: The uncomfortable truths about security automation
- Unlock advanced security automation with Skypher
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Vulnerability reduction | Security automation can decrease vulnerabilities by up to 70% in real-world deployments. |
| MTTR improvement | Automated workflows can cut mean time to remediate critical issues by as much as 90%. |
| Avoid automation pitfalls | Automating low-value tasks may undermine ROI; prioritize impactful, context-aware solutions. |
| Strategic integration | True benefits come from integrating automation deeply into workflows and realigning with evolving threats. |
| Skypher solutions | Adopting Skypher's automation tools helps organizations achieve compliance and security efficiency. |
Why security automation matters in 2026
The threat and compliance landscape has fundamentally shifted over the past few years. Regulatory frameworks like SOC 2, ISO 27001, PCI DSS, and the newer DORA requirements for financial institutions are adding layers of evidence collection and audit preparation that manual teams simply cannot keep pace with. At the same time, threat actors are faster. Ransomware groups and supply chain attackers move from initial access to lateral movement in hours, not days.
For medium to large organizations in tech and finance, the gap between what manual security teams can process and what the environment actually demands has become a genuine operational risk. A single analyst triaging alerts from dozens of tools, cross-referencing vendor assessments, and manually populating compliance evidence spreadsheets will always be a bottleneck. Scale that picture across a 5,000-person organization and the problem becomes critical.
Key pressures driving automation adoption in 2026 include:
- Regulatory velocity: New frameworks and updates are arriving faster than teams can revise manual playbooks.
- Third-party risk volume: Enterprise organizations now manage hundreds or thousands of vendor relationships, each requiring security assessments.
- Talent shortages: The cybersecurity workforce gap remains severe, making headcount-based scaling unrealistic.
- Audit fatigue: Security and GRC teams spend disproportionate hours on repetitive evidence gathering rather than risk analysis.
- Speed of attacker innovation: Automated threat tooling on the adversarial side demands automated detection and response on the defensive side.
Real deployments confirm this. Empirical benchmarks show 60 to 90% MTTR reductions and 70% vulnerability drops when automation is properly deployed, though failures arise when teams automate low-value tasks or ignore operational context. The patterns driving success or failure are remarkably consistent. Organizations that stay ahead of these dynamics can track security automation trends to calibrate their roadmaps, while teams navigating specific regulatory environments can apply targeted compliance tips for tech and finance to stay audit-ready.
Core benefits of security automation: Real-world outcomes
The numbers from real production environments are striking. Rather than relying on vendor marketing, let's look at what organizations actually measure after deploying automation at scale.

Stripe's two-year DevSecOps program produced results that set a useful benchmark for what is achievable:
| Metric | Before automation | After automation | Improvement |
|---|---|---|---|
| Total vulnerabilities | Baseline | Reduced by 70% | 70% reduction |
| MTTR for critical CVEs | Weeks | 14 days | Significant reduction |
| Pre-deployment defect catch rate | 32% | 89% | +57 percentage points |
| Team capacity for strategic work | Limited | Substantially increased | Qualitative gain |
These outcomes did not happen by accident. Stripe invested in integrating automated scanning directly into CI/CD pipelines, established clear escalation workflows, and built feedback loops so engineers received actionable findings rather than noise. That last detail matters enormously and is often skipped.
The core benefit categories worth prioritizing are:
- Vulnerability reduction: Automation catches defects that manual code review and periodic scanning miss, especially in fast-moving deployment environments where releases happen daily.
- Faster MTTR: Automated triage, prioritization, and routing mean that critical findings reach the right engineer with full context in minutes rather than days.
- Pre-deployment detection: Shifting security checks left into the development pipeline catches the majority of issues before they ever reach production, drastically reducing remediation cost.
- Compliance evidence automation: Automated evidence collection for SOC 2, ISO 27001, and similar frameworks removes weeks of manual labor from each audit cycle.
- Consistent process quality: Automation applies the same logic every time, eliminating the variability introduced by analyst fatigue, knowledge gaps, or turnover.
"The shift from reactive to proactive security is only sustainable at scale when automation handles the repetitive, high-volume detection work. Human judgment should be reserved for decisions that genuinely require it."
Teams looking to apply these gains specifically to vendor and third-party assessment workflows can automate security reviews to reduce cycle times significantly. Pairing that with solid security review best practices ensures the automation is built on a sound methodological foundation rather than just speed for its own sake.
Comparing manual vs. automated security processes
Seeing the measurable benefits, it is important to understand exactly where and why automation outperforms manual approaches. The differences are not just about speed.
| Dimension | Manual process | Automated process |
|---|---|---|
| Detection speed | Hours to days | Seconds to minutes |
| Consistency | Variable, depends on analyst | Consistent, rule-based |
| Coverage | Limited by human bandwidth | Comprehensive and continuous |
| Error rate | Higher, especially under fatigue | Lower, predictable failure modes |
| Scalability | Linear with headcount | Near-linear with compute |
| Audit trail | Often incomplete | Automated logging |
| Cost per finding | High | Low at scale |
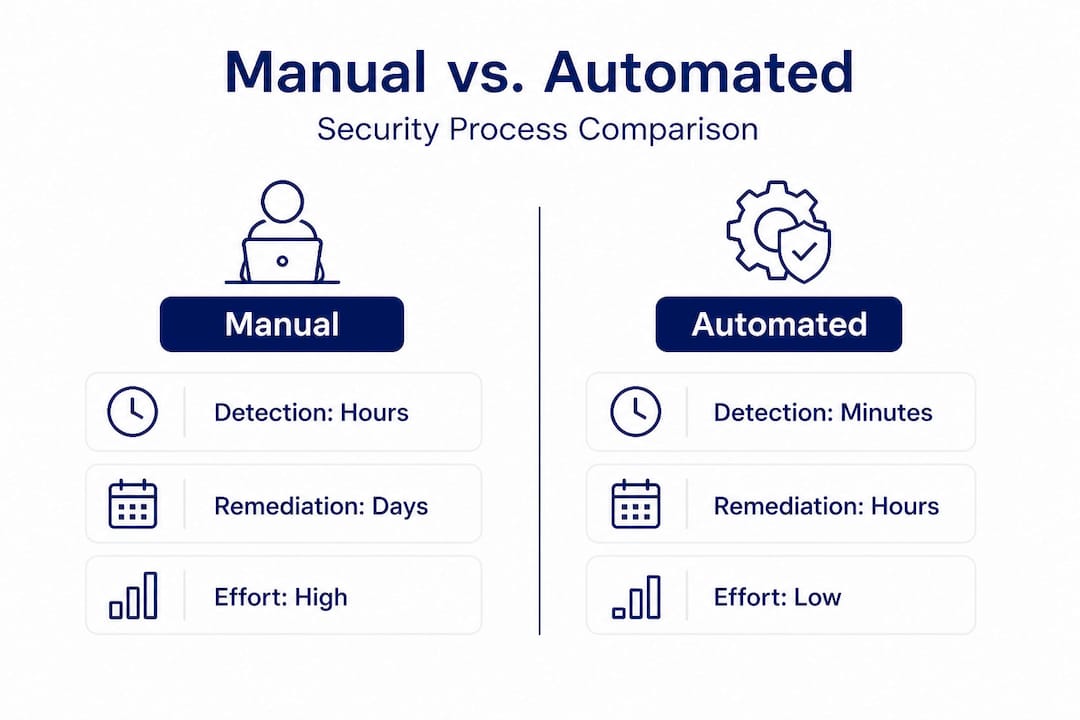
Manual security processes carry hidden costs that rarely appear in budget discussions. Analyst burnout from repetitive triage work increases turnover. Inconsistent application of security controls creates audit findings. The time from alert to ticket to fix in manual workflows can stretch vulnerabilities' exposure windows by days or weeks.
Here is a practical sequence for evaluating where automation delivers the most value in your organization:
- Map your highest-volume, most repetitive security tasks. Alert triage, vulnerability scanning, compliance evidence collection, and security questionnaire responses are common candidates.
- Measure current cycle time and error rate for each. You need a baseline to demonstrate ROI post-automation.
- Assess which tasks have clear, rule-based logic. These automate cleanly. Tasks requiring significant contextual judgment should be augmented, not fully automated.
- Pilot automation on one high-volume workflow. Measure the same metrics after 30 and 90 days.
- Expand based on evidence, not assumption. Do not automate the next workflow until you have confirmed results from the first.
The pitfall that derails most automation programs is prioritizing what is technically easiest to automate rather than what has the highest impact. Failures consistently arise from automating low-value tasks or building automation that ignores the operational context in which findings need to be acted on.
Pro Tip: Before investing in any new automation tooling, run a two-week manual log of every recurring security task your team performs. Rate each task on volume, time cost, and business impact. Automate the top quartile by impact first, not the bottom quartile by effort.
For organizations navigating ongoing audit requirements, the ability to streamline monitoring for compliance through automation is one of the highest-ROI moves available to GRC teams today.
How to maximize security automation ROI: Pitfalls and expert strategies
To realize the full value, CISOs must move beyond technology selection and deploy automation strategically. Having the right tooling matters far less than having the right deployment strategy and the operational discipline to maintain it.
The most common pitfalls that kill automation ROI include:
- Automating for optics, not outcomes: Some teams automate workflows that are visible to leadership but low in actual security impact. This creates the appearance of a mature program without the substance.
- Ignoring integration depth: Automation tools that do not connect to your existing ticketing, communication, and evidence management systems create new manual handoffs rather than eliminating them.
- Setting and forgetting: Threat environments and organizational contexts change. Automation rules and workflows that are not regularly reviewed drift out of alignment with actual risk.
- No measurement framework: Without defined metrics established before deployment, it is impossible to demonstrate ROI or identify underperforming components.
- Underinvesting in human oversight: Full automation of high-stakes decisions without human review points introduces risk. The goal is to amplify human judgment, not replace it entirely.
The strategic moves that consistently produce strong returns are worth detailing. High-impact automation candidates in tech and finance organizations typically include vulnerability detection and triage, compliance evidence collection and mapping, security questionnaire response, third-party risk assessment workflows, and security awareness training completion tracking.
Expert analysis confirms that failures arise when organizations automate low-value tasks or build automation that cannot adapt to context. The fix is straightforward in principle but requires discipline: define success metrics before you start, measure them consistently, and make decisions based on data rather than vendor promises.
Pro Tip: Build a simple automation scorecard. For each automated workflow, track three numbers monthly: volume handled, time saved versus manual baseline, and accuracy rate. If any of the three degrades significantly, investigate before expanding the automation to new areas.
Staying informed about evolving expectations in vendor risk management is also valuable. Reviewing security questionnaire trends helps teams anticipate what buyers and auditors will expect next. And for teams focused on operationalizing questionnaire response specifically, the security questionnaire response best practices guide covers the workflow design considerations that most implementations overlook.
Beyond efficiency: The uncomfortable truths about security automation
Here is the honest take that most vendor-sponsored content avoids. The organizations that fail to see meaningful returns from security automation are not failing because they picked the wrong tool. They are failing because they automated the wrong things, or automated the right things without integrating them into the workflows where decisions actually get made.
The "easy win" trap is real and common. Teams under pressure to show progress pick automation projects with visible outputs but limited security impact. A dashboard fills up with green checkmarks. Alert volumes drop because automated rules suppress noise. But the underlying risk posture has not improved because the automation was never connected to where real exposure lives.
The second uncomfortable truth is about ownership. Effective security automation is not a technology project. It is an organizational change program. When CISOs treat it as a procurement decision rather than a cross-functional initiative, the results suffer. Engineering teams who did not contribute to the design resent the overhead. GRC teams who were not consulted produce evidence that does not satisfy auditors. Sales teams fielding security questionnaires find that their automated responses do not match what the security team actually built.
The organizations that get this right share a common pattern: ongoing, structured collaboration between security, engineering, GRC, and where relevant, sales and legal. Automation is built to serve shared workflows, not to optimize a single team's internal metrics. Feedback loops are established so the humans consuming automation outputs can flag when the logic is wrong or the context has changed.
One area where this integration payoff is particularly clear is security questionnaire automation. The volume of inbound questionnaires in tech and finance organizations has grown sharply as procurement and security review processes have become more rigorous. Teams that automate security questionnaires effectively are not just saving response time. They are building a living, searchable knowledge base of their security posture that benefits every team that interacts with external stakeholders.
The final truth is about maintenance. Automation is not a one-time investment. The threat environment changes. Frameworks update. Your product changes. Your vendor portfolio changes. An automation program that was correctly calibrated 18 months ago may be producing misleading outputs today if nobody has reviewed the logic. Build the operational cadence for review into the program from day one, or plan for the hidden cost of drift.
Unlock advanced security automation with Skypher
CISOs and GRC leaders who are ready to move from strategy to execution need tools that are built for the complexity of real enterprise environments, not idealized ones. Skypher was designed specifically for that gap.

Skypher's security questionnaires automation platform handles the full response workflow, from ingesting questionnaires in any format using proprietary AI parsing models to surfacing accurate, context-aware answers in under a minute across even 200-question assessments. With 30-plus API connectors to platforms like OneTrust and ServiceNow, plus native integrations with Slack, Microsoft Teams, Confluence, Notion, Google Drive, OneDrive, and SharePoint, Skypher fits into existing workflows rather than creating new ones. The AI-powered recommendation engine continuously learns from your organization's content, supporting complex multi-entity setups and multilingual responses. For teams serious about measurable efficiency gains in 2026, Skypher is worth a close look.
Frequently asked questions
How much can security automation reduce vulnerability risk?
Industry data shows up to 70% vulnerability reduction with properly deployed automation, as demonstrated by Stripe's two-year DevSecOps program. Results depend on targeting high-impact workflows rather than superficial ones.
What is MTTR and how does automation impact it?
MTTR, or mean time to remediate, measures how long it takes to fix a confirmed vulnerability after discovery. Automation drives 60 to 90% MTTR reductions by accelerating triage, routing, and context delivery to the responsible engineer.
Are there risks in automating security workflows?
Yes. Automating low-value tasks or building automation that ignores operational context wastes budget and can actually degrade security posture by creating false confidence in incomplete coverage.
How can CISOs ensure ROI from security automation?
Focus automation investment on the highest-volume, highest-impact workflows, establish measurable baselines before deployment, and schedule regular reviews to keep automation logic aligned with evolving threats and organizational changes.
