TL;DR:
- Vendor risk assessment often focuses solely on security controls, neglecting operational resilience and continuity. A comprehensive program evaluates multiple domains, including operational plans, regulatory compliance, and financial health, to truly mitigate third-party risks. Implementing continuous monitoring and scenario testing transforms assessments into strategic advantages, ensuring readiness against operational disruptions.
Compliance and risk managers often treat vendor risk assessment as a glorified security checklist. If a vendor passes their SOC 2 audit and answers the right questions about encryption, the relationship gets a green light. That logic is dangerously incomplete. Operational readiness failures can hit your organization just as hard as a data breach, even when a vendor's confidentiality controls are perfectly sound. For tech and finance organizations managing dozens or hundreds of third-party relationships, understanding the full spectrum of vendor risk is not optional. It's a core operational responsibility.
Table of Contents
- The evolving risk landscape for tech and finance vendors
- What vendor risk assessment actually covers
- The hidden threats: Operational resilience and continuity
- Turning risk assessment into business advantage
- Why most risk assessments still fall short — and how to fix them
- Elevate your vendor risk assessment program with advanced automation
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| More than cybersecurity | Vendor risk assessments should address not only security but also operational and compliance risks. |
| Continuity matters | Vendor outages and supply chain disruptions can cause as much damage as data breaches. |
| Business value | Strong vendor assessments reduce risk and create lasting business advantages. |
| Continuous evaluation | Ongoing and scenario-based assessments outperform one-time checklist reviews. |
The evolving risk landscape for tech and finance vendors
The nature of vendor risk has shifted dramatically over the past several years. What once meant "do they have a firewall and a privacy policy" now covers an interconnected web of geopolitical exposure, supply chain dependencies, regulatory obligations, and business continuity threats. For medium and large organizations in tech and finance, this complexity is not theoretical. It's a daily operational reality.
Understanding vendor risk management fundamentals has become table stakes for anyone running a compliance or risk program. But knowing the fundamentals is not enough if your program hasn't evolved alongside the threat environment. Consider how many of your vendors rely on sub-processors, cloud infrastructure providers, or hardware manufacturers based in politically sensitive regions.
The modern vendor ecosystem introduces risks that didn't exist a decade ago:
- Geopolitical exposure: Vendors operating in sanctioned regions or dependent on restricted technology components can become liabilities overnight.
- Supply chain concentration: When multiple vendors rely on the same upstream supplier, a single disruption cascades across your entire portfolio.
- Regulatory divergence: As data privacy laws multiply across jurisdictions, your vendors must demonstrate compliance in regions they may not have previously considered.
- Business continuity gaps: A vendor can have excellent access controls but no realistic disaster recovery plan.
"Vendors can fail due to disruption from chip shortages, sanctions, and regional shutdowns, creating availability risk even when confidentiality controls look strong."
This last point often catches organizations off guard. Compliance teams focused on risk management for security may evaluate a vendor's penetration testing cadence while completely overlooking whether that vendor has a tested failover plan or meaningful business interruption insurance. The gap between security readiness and operational readiness is where most hidden risk lives.
What vendor risk assessment actually covers
A robust vendor risk assessment is not a single document. It's a structured process that examines multiple risk domains simultaneously and involves stakeholders from across the organization. When compliance managers treat assessment as solely an IT security task, they miss at least half the picture.
The core domains any modern assessment must address include:
- Information security controls: Access management, encryption standards, vulnerability management, incident response.
- Operational resilience: Disaster recovery plans, redundancy architecture, tested recovery time objectives.
- Regulatory compliance: Data privacy obligations (GDPR, CCPA, DORA for financial entities), industry-specific requirements (PCI-DSS, HIPAA), and geographic regulatory exposure.
- Financial stability: Whether a vendor's financial health could affect their ability to deliver services.
- Contractual accountability: SLAs, liability clauses, right-to-audit provisions, and notification obligations.
The contrast between traditional and modern assessment frameworks is stark:
| Assessment dimension | Traditional approach | Modern approach |
|---|---|---|
| Security controls | Questionnaire-based, annual | Continuous monitoring, automated scoring |
| Operational resilience | Rarely evaluated | Tested DR plans, SLA verification |
| Regulatory compliance | Single-jurisdiction focus | Multi-jurisdiction mapping |
| Financial health | Informal review | Structured financial due diligence |
| Supply chain depth | First-party only | Nth-party visibility |
| Assessment frequency | Annual or onboarding only | Risk-tiered, event-triggered |
Following secure vendor management best practices means accepting that a vendor's cybersecurity posture is just one variable in a much larger equation. Cross-functional buy-in is essential. Your IT security team, procurement leads, legal counsel, and operations stakeholders all see different dimensions of vendor risk. When assessments happen in silos, critical risks fall through the gaps.
Streamlining security compliance also requires recognizing where traditional programs waste effort. Manually reviewing 150-question spreadsheets from every vendor you onboard is not a scalable model for a growing enterprise.
Pro Tip: Assign a risk tier to each vendor based on access level, data sensitivity, and business criticality before you start the assessment. Tier 1 vendors (critical, high-access) should get your most thorough review. Tier 3 vendors (low-access, easily replaceable) can use a streamlined track. This keeps your team focused where it matters most.
Even secure vendors can cause major business impact through disruptions that have nothing to do with information security. Acknowledging that reality is the first step toward building an assessment program that actually protects your operations.
The hidden threats: Operational resilience and continuity
Operational resilience is the most consistently underassessed dimension of vendor risk. Security teams know how to evaluate a vendor's pen test results. Far fewer know how to evaluate whether a vendor can maintain service during a regional power failure, a key employee departure, or a critical hardware shortage.

Operational resilience testing matters precisely because vendors can fail operationally even when their security controls are textbook-perfect. Consider three scenarios that reflect real patterns across the tech and finance sectors:
Scenario 1: The chip shortage cascade. A payment processing vendor relies on proprietary hardware for their fraud detection system. A global semiconductor shortage delays replacement parts by six months. Their fraud detection performance degrades, increasing false positives and blocking legitimate transactions. Your customers experience friction. Revenue takes a hit. The vendor's security controls? Perfectly intact throughout.
Scenario 2: Regional shutdown. A SaaS vendor hosts part of their infrastructure in a region subject to sudden regulatory restrictions. Their data center access gets suspended without warning. Services go dark for 72 hours. Your internal teams scramble to find workarounds. The incident has no security component whatsoever. It's purely an availability failure.
Scenario 3: Single-point staffing risk. A specialized compliance software vendor is maintained almost entirely by a two-person engineering team. One leaves. System updates stall, bugs pile up, and customer support quality drops sharply. Again, no breach. Just operational collapse.
The business impact of these types of failures can be quantified:
| Disruption type | Average business impact | Recovery timeline |
|---|---|---|
| Vendor system downtime (critical) | $5,600 to $9,000 per minute | Hours to days |
| Supply chain disruption | 6 to 8 weeks on average | Weeks to months |
| Vendor compliance failure | Regulatory fines plus remediation costs | Months |
| Vendor staffing failure | Service degradation, SLA breach | Weeks |
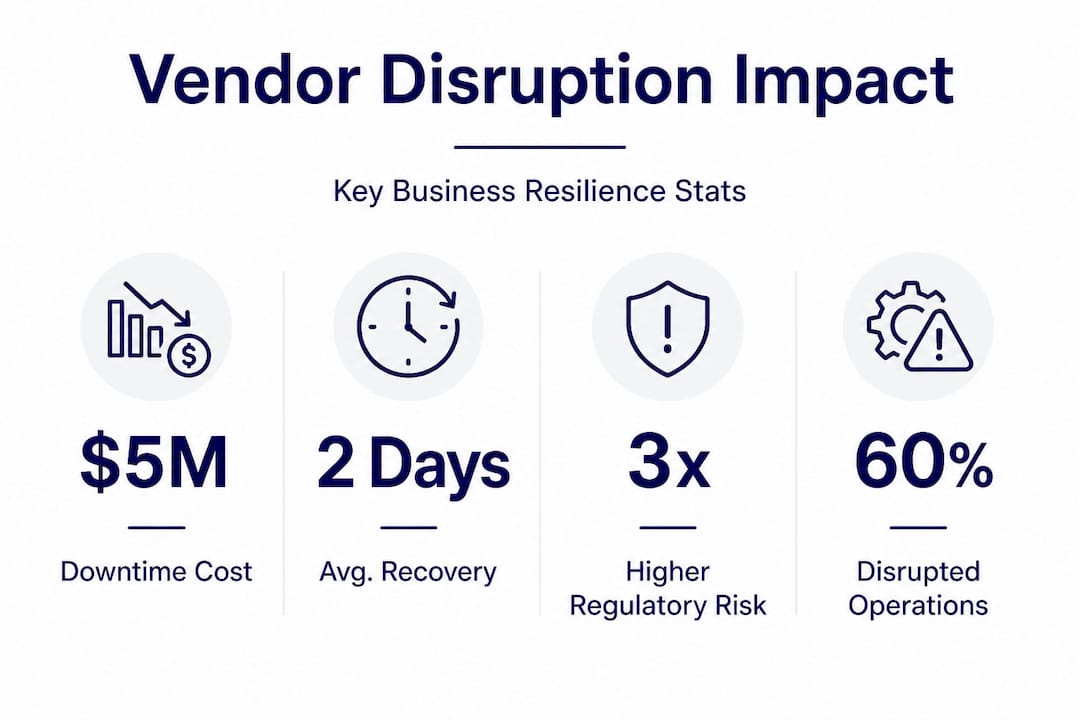
For finance organizations specifically, vendor downtime during market hours can trigger regulatory scrutiny in addition to revenue loss. For tech companies, availability failures directly erode customer trust and NPS scores.
The streamlined vendor risk review steps that actually address continuity risk include requesting documented and tested disaster recovery plans (not just policies), verifying recovery time objectives and recovery point objectives against your own operational requirements, and asking vendors to walk you through their incident response playbook with specific scenarios.
Pro Tip: Request evidence of a tabletop exercise or a real recovery test from your Tier 1 vendors, not just a written DR plan. A plan that has never been tested is barely worth the document it's written on. The evidence requirement shifts the conversation from checkbox compliance to operational accountability.
Turning risk assessment into business advantage
Every risk assessment conversation tends to focus on what could go wrong. But organizations that build robust vendor risk programs also gain tangible business advantages. This reframe matters for compliance leaders making the case internally for better resources and tooling.
A thorough assessment provides a competitive edge by ensuring availability even when competitors experience vendor disruptions. When everyone is scrambling during a supply chain event and your organization continues operating smoothly, that operational continuity becomes a customer retention and acquisition argument.
Here are actionable steps to turn your assessment program into a business advantage:
- Map vendor criticality to business outcomes. Understand which vendors, if disrupted, would directly affect revenue, customer experience, or regulatory standing. This creates a prioritized protection strategy rather than a uniform compliance burden.
- Build a vendor scorecard that includes resilience metrics. Combine security scores with availability history, DR test results, and financial stability ratings. Share these internally with procurement and finance to inform contract negotiations.
- Use assessment findings to negotiate better SLAs. When you identify a vendor with weak continuity controls, you have leverage. Either they improve their posture or you negotiate stronger contractual protections, including financial remedies for downtime.
- Establish a vendor monitoring cadence. Point-in-time assessments miss the drift that happens between reviews. Implement continuous signals like security ratings services, news monitoring for vendor incidents, and regular SLA performance reviews.
- Leverage assessment data for regulatory reporting. Regulators in finance increasingly want evidence of third-party risk management. A well-documented assessment program becomes an asset during audits rather than a liability.
Reviewing insights for risk management vendors also reveals that organizations with mature assessment programs tend to select higher-quality vendors over time because their criteria get sharper. The assessment process itself becomes a vendor quality filter that raises the baseline across your entire third-party ecosystem.
Effective risk mitigation also supports customer trust. When enterprise clients ask about your third-party risk program during their own due diligence, a well-documented, modern approach signals organizational maturity and earns faster deal closures.
Pro Tip: Create a one-page vendor risk summary for each Tier 1 vendor that covers security score, resilience rating, compliance status, and open findings. Share it quarterly with your executive team. This keeps risk visible at the leadership level and makes it easier to get budget approved when gaps need addressing.
Why most risk assessments still fall short — and how to fix them
Here is the uncomfortable truth: most vendor risk assessment programs in tech and finance organizations are security theater dressed up as governance. Teams spend weeks collecting responses to 200-question spreadsheets, manually reviewing answers, and filing reports that nobody reads until something goes wrong. The problem isn't effort. It's focus.
The security questionnaire has become the de facto proxy for vendor risk. Organizations send them. Vendors fill them out (often with templated answers that haven't been updated in two years). Compliance teams archive the results and move on. This process provides the appearance of risk management without much of the substance.
True risk management requires three things that most questionnaire-driven programs lack. First, ongoing monitoring rather than point-in-time snapshots. A vendor's security posture can change between assessments. So can their financial health, staffing depth, and regulatory standing. Programs that only look at vendors during onboarding or annual renewal are working with stale data most of the time.
Second, scenario-based thinking. Most assessments ask vendors to describe what controls they have. Almost none ask vendors to walk through what happens when those controls fail. Tabletop scenarios, business impact discussions, and recovery timeline verification require a different kind of assessment skill set, one that blends risk management with operational thinking.
Third, business impact framing. When you evaluate a vendor's risk, you need to connect every finding to a specific business outcome. Not "they don't have MFA on admin accounts" but "they don't have MFA on admin accounts, which means a single compromised credential could take down the payment processing integration that handles 40% of your daily transaction volume." That framing creates urgency and priority. The compliance officer risk management guide for 2026 emphasizes exactly this shift from controls-based to impact-based assessment language.
The fix is not necessarily more assessments. It's smarter ones. Automation reduces the manual burden of collecting and reviewing questionnaire responses, freeing your team to focus on higher-order analysis. Continuous monitoring tools provide the ongoing signal that annual reviews miss. And cross-functional involvement ensures that when a vendor has a continuity gap, the right people inside your organization know about it and have a plan.
The organizations getting this right are not necessarily the ones with the biggest compliance teams. They're the ones using better processes and better tools to turn their assessment program from a documentation exercise into a genuine risk intelligence function.
Elevate your vendor risk assessment program with advanced automation
Managing the full scope of vendor risk, security, resilience, compliance, and continuity, requires more than manual effort. Skypher's platform is built specifically for compliance and risk professionals in tech and finance who need to run efficient, thorough assessment programs without burying their teams in spreadsheets.

Skypher's security questionnaire automation handles even 200-question assessments in under a minute, with AI-powered parsing that works across every document format. The platform integrates with over 40 TPRM platforms, connects to Slack, Microsoft Teams, Confluence, and SharePoint, and supports multilingual assessments for enterprise teams operating across regions. The AI recommendation engine provides confidence-scored answers drawn from your own knowledge base, so your team spends time on decisions rather than data entry. If your current program is struggling to scale, Skypher gives you the infrastructure to run a modern, comprehensive vendor risk assessment program without the overhead.
Frequently asked questions
What is the main goal of vendor risk assessment?
The main goal is to identify, evaluate, and reduce risks posed by third-party vendors to protect your operations, data, and regulatory standing. Vendor assessments help avoid not just security breaches but also major business disruptions that can be equally damaging.
How often should companies assess vendor risk?
Companies should reassess vendor risk at least annually, and more frequently for Tier 1 vendors or when a vendor's circumstances change significantly. Operational resilience testing schedules should adapt as business needs and the vendor's risk profile evolve.
Does vendor risk assessment cover only cybersecurity risks?
No. A thorough vendor risk assessment covers operational resilience, regulatory compliance, financial stability, and business continuity, not just cybersecurity. Availability and continuity failures can occur even when a vendor's confidentiality controls are fully intact.
What are examples of operational risks in vendor relationships?
Common examples include supply chain disruptions from component shortages, regional service outages, and failures to meet contractual SLAs. Vendors can fail due to disruption from events like chip shortages or regional shutdowns that have no security component at all.
