Passing a compliance audit feels like a win. But a passing score on a checklist does not mean your systems are actually secure. Many organizations in tech and finance discover this the hard way, when a vendor with a clean audit record becomes the source of a breach. Security assurance goes beyond compliance by providing ongoing, evidence-based confidence in risk mitigation. For IT and security professionals managing vendor reviews, security questionnaires, and regulatory pressure, understanding this distinction is not optional. It is the foundation of a mature security program.
Table of Contents
- Understanding security assurance: Definition and foundations
- Core methodologies: Common Criteria, EALs, and ISASecure explained
- Security assurance in practice: Activities and operationalization
- Assurance vs. compliance: More than a checklist
- Streamlining questionnaires and third-party assessments with assurance evidence
- How Skypher helps you turn assurance evidence into faster questionnaire responses
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Assurance vs. compliance | Security assurance extends beyond compliance to offer ongoing, evidence-based confidence that controls work as intended. |
| Standards and frameworks | Common Criteria, ISASecure, and comparable frameworks deliver quantifiable assurance and streamline third-party reviews. |
| Efficient responses | Mapping questionnaire items to existing assurance evidence cuts manual effort and builds stakeholder trust. |
| Continuous validation | Integrating assurance into development and operations drives security maturity and simplifies audits. |
Understanding security assurance: Definition and foundations
Security assurance is not a product you buy or a box you check. It is a level of confidence, built through evidence, that your systems actually do what they are supposed to do under real conditions. Security assurance is the level of confidence that a system, software, or product meets its specified security requirements and is resilient to vulnerabilities and threats throughout its lifecycle.
That lifecycle framing matters. Assurance is not just about how a system is built. It covers design, development, deployment, and ongoing operation. A system that was secure at launch can drift out of assurance as threats evolve, configurations change, or new integrations are added. Understanding security management system basics helps teams see where assurance activities need to be embedded across the full stack.
"Assurance is the evidence-backed confidence that controls work as intended, even under adversarial conditions."
Here is what security assurance actually addresses:
- Functional correctness: Controls perform as designed, not just as documented
- Resilience: Systems hold up under attack, not just under normal conditions
- Supply chain integrity: Third-party components meet the same standards as internal ones
- Operational continuity: Assurance is maintained as systems change over time
For organizations managing AI security implementation or complex multi-vendor environments, this evidence-based approach is what separates genuine risk reduction from paperwork.
Core methodologies: Common Criteria, EALs, and ISASecure explained
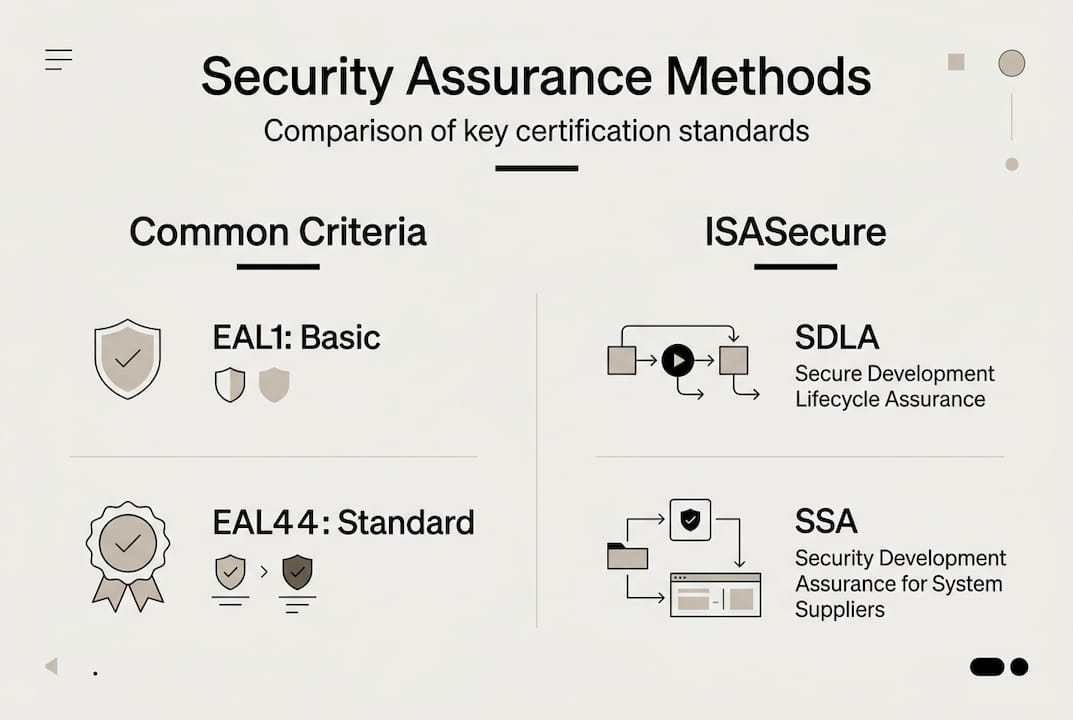
Assurance needs to be measurable to be useful. That is where global standards come in. Common Criteria is the internationally recognized framework for evaluating IT product security, and it uses Evaluation Assurance Levels (EALs) to specify how deeply a product has been tested and verified.
Key methodologies include Common Criteria with EAL1 to EAL7, where higher levels involve more rigorous testing, design verification, and penetration testing. Critically, a higher EAL does not mean a product is more secure in absolute terms. It means the evaluation was more thorough. EAL4 is the most common level for commercial products because it balances rigor with practical cost and time investment.
| EAL Level | Description | Typical Use Case |
|---|---|---|
| EAL1 | Functionally tested | Low-risk, general IT |
| EAL2 | Structurally tested | Basic commercial products |
| EAL3 | Methodically tested | Standard enterprise software |
| EAL4 | Methodically designed and tested | Most commercial security products |
| EAL5 | Semiformally designed | High-assurance environments |
| EAL6 | Semiformally verified | Critical infrastructure |
| EAL7 | Formally verified | Highest rigor, government/defense |
For critical infrastructure and industrial environments, ISASecure SDLA/SSA certification based on IEC 62443 is the relevant standard. It is increasingly referenced in tech and finance sectors where operational technology intersects with IT systems.
Standardized collaborative Protection Profiles (cPPs) offer another practical path. They define agreed-upon security requirements for product categories, giving organizations repeatable assurance without the overhead of a full EAL6 or EAL7 evaluation. When reviewing vendors, applying vendor management best practices alongside these standards helps you ask the right questions and interpret certifications accurately. You can also use these frameworks to streamline vendor security evaluation workflows across your organization.
Security assurance in practice: Activities and operationalization
Knowing the standards is one thing. Embedding assurance into daily operations is another. Security assurance activities include threat analysis, vulnerability assessments, penetration testing, audits, and configuration management. These are not one-time events. They are repeatable processes that generate the evidence stakeholders and auditors actually need.
Here is how organizations typically operationalize assurance:
- Define assurance requirements early: Establish what level of confidence is needed for each system or product before design begins, not after deployment.
- Conduct threat modeling: Map realistic attack scenarios to your specific operational and supply chain context, not generic threat libraries.
- Run continuous validation: Use DevSecOps pipelines to automate security testing at every stage of development and deployment.
- Maintain assurance documentation: Every test result, audit finding, and remediation action becomes part of your evidence base for future reviews.
- Review third-party assurance: Require vendors to provide assurance artifacts, not just attestations, as part of your procurement process.
Pro Tip: Treat your assurance documentation as a living asset. Every time a system changes, update the relevant evidence. Auditors and enterprise buyers will ask for it, and having it ready cuts review cycles significantly.
For development teams, investing in secure development training ensures that assurance is built in from the start rather than bolted on later. Referencing an AI deployment checklist can also help teams validate assurance at each stage of an AI system rollout.
Assurance vs. compliance: More than a checklist
This is where many organizations get stuck. Compliance and assurance are related, but they are not the same thing, and confusing them creates real risk.
Compliance checks policy adherence and is checklist-driven and point-in-time; assurance provides evidence-based confidence in risk mitigation and resilience and is risk-based and ongoing. A vendor can pass a SOC 2 audit in January and be compromised by March. Compliance captured a moment. Assurance would have caught the drift.
| Dimension | Compliance | Assurance |
|---|---|---|
| Approach | Checklist-driven | Evidence-based |
| Frequency | Periodic (annual audits) | Continuous |
| Focus | Policy adherence | Risk mitigation |
| Outcome | Pass/fail | Confidence level |
| Adaptability | Static | Dynamic |
"A compliant system is not necessarily a secure system. Assurance is what closes that gap."
Both are necessary. Compliance satisfies regulators and auditors. Assurance protects your organization in the real world. Understanding the compliance vs. assurance distinction helps security teams make the case internally for investing in ongoing assurance activities, not just audit preparation. Pairing this with the right software compliance tools ensures neither side of the equation gets neglected.
The practical implication: when you evaluate a vendor, do not stop at their compliance certifications. Ask for assurance evidence. What testing have they done? How recent is it? What does their threat modeling cover? A vendor with strong assurance posture will have answers. One relying purely on compliance will not.
Streamlining questionnaires and third-party assessments with assurance evidence
Security questionnaires are where assurance evidence becomes immediately practical. Whether you are responding to a SIG, CAIQ, or a custom vendor questionnaire, the organizations that answer fastest and most credibly are the ones with organized assurance artifacts ready to map to each question.
Use assurance certifications and standardized questionnaires like CAIQ and SIG to streamline vendor assessments and build stakeholder confidence efficiently. This means doing the mapping work upfront: linking each common questionnaire category to the specific evidence your organization holds, whether that is a penetration test report, an EAL4 certificate, or a configuration audit log.
Here is how to make this work in practice:
- Build an evidence library: Organize assurance artifacts by control domain so they are ready to pull when a questionnaire arrives
- Pre-qualify with certifications: EAL4+ or ISASecure certifications can answer entire sections of a TPRM questionnaire automatically
- Automate evidence collection: Connect your assurance documentation to your questionnaire response workflow to cut manual effort
- Avoid generic statements: Saying "we follow industry best practices" without artifacts is a red flag for sophisticated buyers
For teams managing vendor risk assessment at scale, this approach transforms questionnaire response from a reactive scramble into a proactive, repeatable process. It also strengthens your position in third-party risk management programs, where buyers increasingly expect evidence, not just attestations. Understanding the importance of TPRM and the nuances of third-party cybersecurity risk helps you build a program that satisfies both compliance requirements and genuine assurance expectations.
Pro Tip: Map your assurance artifacts to the CSA CAIQ control domains once, and you will have a reusable foundation for most cloud-focused vendor questionnaires. This single investment pays off across dozens of reviews per year.
How Skypher helps you turn assurance evidence into faster questionnaire responses
Building an assurance evidence library is the right strategy. But managing that library and mapping it to incoming questionnaires at speed is where most security teams hit a wall. Skypher is built specifically to solve that problem.

With Skypher's AI Questionnaire Automation Tool, your team can upload assurance artifacts in any format and let the platform parse, index, and map them to questionnaire items automatically. The platform connects to over 40 TPRM platforms and can answer up to 200 questions in under a minute, using your actual assurance evidence rather than generic responses. Real-time collaboration features mean your security, legal, and compliance teams work from the same evidence base simultaneously. Whether you are responding to a SIG, CAIQ, or a custom enterprise questionnaire, Skypher turns your assurance investment into a competitive advantage on every vendor review.
Frequently asked questions
Why isn't complying with security policies enough for true assurance?
Compliance is checklist-driven and point-in-time, while assurance provides ongoing, evidence-based confidence in real-world risk management and resilience. A system can be compliant today and vulnerable tomorrow without continuous assurance activities.
What's the difference between EAL levels in Common Criteria?
EAL1 to EAL7 offer increasing assurance rigor, not absolute security guarantees. EAL4 is the standard for most commercial security products, balancing thorough testing with practical cost, while EAL7 represents the highest level of formal verification used in government and defense contexts.
How can security assurance simplify vendor security questionnaires?
Mapping questionnaire items to existing assurance evidence and certifications speeds responses, increases accuracy, and gives buyers the concrete artifacts they need to make confident decisions rather than relying on generic statements.
Is security assurance relevant for cloud environments?
Absolutely. Frameworks like the CSA CAIQ and assurance activities such as penetration testing and configuration audits apply directly to cloud and SaaS environments, providing buyers with confidence in secure cloud operations across shared responsibility models.
