Many tech and finance teams treat compliance frameworks as a list of boxes to check before an audit. That mindset is exactly what leads to expensive surprises, repeated evidence requests, and security programs that look strong on paper but crumble under real scrutiny. The organizations that actually reduce risk and sail through audits are the ones that understand how frameworks like NIST CSF, SOC 2, ISO 27001, and DORA interconnect, what each genuinely demands, and how to build a unified compliance practice rather than four separate ones. This article gives you that understanding, a direct comparison, and practical steps to integrate multiple frameworks without drowning your team.
Table of Contents
- What are compliance frameworks and why do they matter?
- Inside the major frameworks: NIST CSF, SOC 2, ISO 27001, and DORA
- Comparing compliance frameworks: Key differences, overlaps, and integration tips
- Implementing multiple frameworks: Efficiency strategies for tech and finance teams
- The hidden cost of check-the-box compliance and how leading teams win
- Supercharge your compliance process with streamlined automation
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Frameworks overlap | Many controls are shared, so mapping them can save time and effort. |
| Start broad, then specialize | Begin with NIST or ISO for foundational coverage, adding SOC 2 or DORA as needed. |
| Efficiency is critical | Leveraging multi-framework strategies and automation tools streamlines evidence and audit processes. |
| Avoid checklists only | Focusing solely on passing audits fails to deliver real security improvements. |
What are compliance frameworks and why do they matter?
A compliance framework is a structured set of guidelines, controls, and best practices that organizations use to manage information security risk, meet regulatory obligations, and satisfy customer requirements. Think of it as a shared language between your security team, your auditors, and your clients. Without one, every vendor questionnaire, every client security review, and every internal audit starts from scratch.
The drivers for adopting a framework vary. Regulatory pressure is one. Legal liability is another. But the most immediate trigger for most tech and finance companies is a client or prospect asking for proof of your security posture. That demand is where compliance risk meaning becomes very concrete: if you cannot demonstrate control over your environment, you lose deals and trust simultaneously.
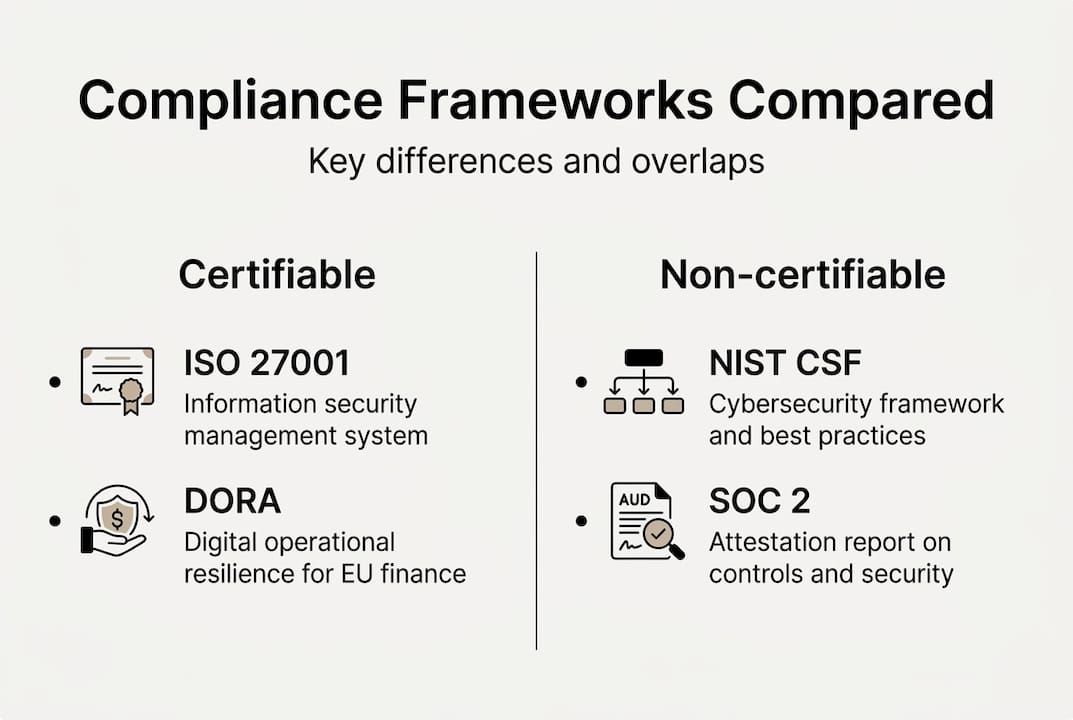
The most recognized frameworks in 2026 include:
- NIST CSF (Cybersecurity Framework): A voluntary, risk-based framework from the U.S. National Institute of Standards and Technology, widely used across industries globally.
- SOC 2: An audit standard from the AICPA focused on Trust Services Criteria, most relevant for SaaS and cloud service providers.
- ISO 27001: An internationally certifiable standard for information security management systems, recognized across geographies and industries.
- DORA (Digital Operational Resilience Act): An EU regulatory mandate covering ICT risk management for financial entities and their critical technology providers.
Here is a key insight that changes how most teams approach this work: 30 to 40% overlap exists between NIST or ISO controls and SOC 2 requirements. Starting with a broad framework first is not extra work. It is a multiplier.
"Harmonizing frameworks is not about doing more compliance work. It is about doing the same work once and making it count across multiple requirements." This is the operating principle that separates efficient compliance teams from overwhelmed ones.
Multi-framework adoption is now the norm rather than the exception for organizations operating at scale in tech and finance. The NIST CSF overview makes clear that the framework is designed to integrate with, not replace, other standards. That design philosophy is worth internalizing early.
Inside the major frameworks: NIST CSF, SOC 2, ISO 27001, and DORA
Each framework has a distinct structure, scope, and intended audience. Understanding those differences saves you from applying the wrong tool to the wrong problem.

NIST CSF 2.0 was updated in 2024 and now organizes cybersecurity activities into six core functions: Govern, Identify, Protect, Detect, Respond, and Recover. It includes 106 subcategories across 22 categories, and uses Profiles and Tiers to help organizations benchmark their current state and set improvement targets. NIST is flexible by design, which makes it powerful for U.S. organizations and increasingly popular globally, but that flexibility also means it does not produce a certifiable credential on its own.
SOC 2 centers on the Trust Services Criteria, where the Security criterion is mandatory and others (Availability, Confidentiality, Processing Integrity, Privacy) are optional based on your service commitments. There are two report types: Type I evaluates whether your controls are designed correctly at a point in time, while Type II evaluates whether those controls operated effectively over a period, typically six to twelve months. The average SOC 2 audit takes about 5.2 months and costs around $84,000. Critically, 73% of organizations underestimate both cost and timeline. SOC 2 is not certifiable but is the de facto baseline for SaaS companies selling to enterprise clients. See SOC 2 requirements and the SOC 2 in 2026 guide for deeper guidance.
ISO 27001 is the global gold standard for information security management. It is certifiable, audited by accredited third parties, and recognized in virtually every market. The tradeoff is resource intensity: implementation typically takes 12 to 18 months and requires formal risk treatment plans, documented policies, and ongoing surveillance audits.
DORA covers five pillars: ICT risk management, incident reporting, digital operational resilience testing, third-party risk management, and information sharing. It applies to EU financial entities and, importantly, extends obligations to critical ICT service providers. That last point is significant for any SaaS company serving European banks or insurers.
| Framework | Certifiable | Primary audience | Avg. timeline | Scope |
|---|---|---|---|---|
| NIST CSF 2.0 | No | US and global orgs | Ongoing | Cyber risk |
| SOC 2 | No | SaaS, cloud providers | 5 to 12 months | Trust criteria |
| ISO 27001 | Yes | Global, all sectors | 12 to 18 months | ISMS |
| DORA | Regulatory | EU finance and ICT | Mandatory by law | Operational resilience |
Pro Tip: Most organizations overestimate what counts as adequate documentation. A policy document that no one follows is worse than no policy at all. Auditors look for evidence of consistent practice, not just written procedures.
Comparing compliance frameworks: Key differences, overlaps, and integration tips
Once you understand each framework individually, the real strategic value comes from seeing how they interact. The differences matter as much as the overlaps.
The most important structural distinction is voluntary versus regulatory. NIST CSF and SOC 2 are customer and market-driven. ISO 27001 is market-driven but globally certifiable. DORA is a legal mandate with enforcement consequences. When regulatory requirements are in play, those lead the decision. When customer trust is the primary driver, SOC 2 or ISO 27001 typically take priority.
The framework selection strategy that consistently works best for tech and finance organizations follows this sequence:
- Map your regulatory environment first. If DORA applies to your business, it is non-negotiable.
- Identify your primary customer market. U.S. enterprise clients expect SOC 2. European and global clients often require ISO 27001.
- Build your foundational control set using NIST CSF or ISO 27001, since both have 30 to 40% control overlap with SOC 2.
- Map existing controls to each framework's requirements before building new ones.
- Consolidate evidence collection so a single artifact satisfies multiple frameworks simultaneously.
The SOC 2 report types decision also intersects with your integration strategy. If you are building toward ISO 27001 certification, a SOC 2 Type II audit running concurrently creates significant evidence reuse. Understanding SOC 2 cost factors upfront helps you budget for this overlap rather than treating each framework as a separate line item.
Where frameworks diverge most sharply: NIST is flexible but lacks external comparability since there is no certificate to show clients. ISO is certifiable but resource-intensive. SOC 2 is the SaaS baseline but not a certification. DORA extends well beyond cybersecurity into operational resilience and third-party governance. Knowing these edges prevents scope creep and misaligned effort.
Implementing multiple frameworks: Efficiency strategies for tech and finance teams
Knowing where frameworks converge is the foundation. Turning that knowledge into an efficient compliance operation is where most teams either gain a real advantage or lose months of productivity.
The single highest-leverage move is building a unified control library before you start any audit preparation. Map each control to every framework it satisfies. A single access control policy, for example, may satisfy NIST CSF PR.AC controls, ISO 27001 Annex A.9 requirements, and SOC 2 CC6 criteria simultaneously. That multi-framework efficiency approach means one piece of evidence does triple duty.
Here is a practical implementation sequence:
- Start with NIST CSF or ISO 27001 as your foundational control set. Their breadth covers the most ground.
- Run a gap analysis against your next target framework (SOC 2 or DORA) using your existing controls as the baseline.
- Build a reusable evidence library: policies, system configurations, access logs, vendor contracts, and training records organized by control, not by framework.
- Assign control owners who are accountable year-round, not just during audit season.
- Schedule continuous control testing rather than point-in-time reviews to catch drift before auditors do.
Pro Tip: Tackle broad frameworks like NIST or ISO first, then layer on specific requirements like SOC 2 or DORA. Reversing this order creates rework because narrow frameworks rarely provide enough foundational coverage to satisfy broader ones.
Key pitfalls to avoid when running multi-framework compliance:
- Siloed teams: Security, legal, and engineering working separately creates duplicated effort and gaps.
- Framework sprawl: Adopting every framework a client requests without a consolidation strategy leads to audit fatigue fast.
- Static documentation: Policies written once and never updated fail both audits and real security tests.
- Ignoring principles-based frameworks: Prescriptive frameworks feel easier but often miss the intent behind controls.
When new mandates like DORA require retrofitting existing workflows, the organizations with a unified control library adapt in days. Those without one spend months rebuilding from scratch. See SOC 2 report insights and compliance risk guidance for additional context on building durable programs.
The hidden cost of check-the-box compliance and how leading teams win
Here is an uncomfortable truth: passing an audit and actually being secure are not the same thing. We have seen organizations with pristine SOC 2 Type II reports suffer significant incidents within months of certification. The audit passed. The controls did not hold under real conditions.
Conventional wisdom in compliance over-emphasizes documentation volume over security outcomes. The teams that consistently outperform on both dimensions do something different. They integrate framework controls into actual business processes rather than treating compliance as a parallel workstream. Access reviews happen because engineers use them, not because an auditor asked for evidence.
Relying on generic templates lowers both efficiency and resilience. Templates are a starting point, not a destination. The organizations winning at compliance customize controls to reflect their actual risk environment, which makes audits faster and security genuinely stronger. Read how SOC 2 auditors evaluate SaaS compliance programs to understand what separates surface-level from substantive compliance. The checklist mindset fails long term because threats evolve, but checkbox controls stay frozen.
Supercharge your compliance process with streamlined automation
Managing multi-framework compliance manually is where even well-resourced teams hit a wall. Evidence collection, control mapping, and audit preparation across NIST, SOC 2, ISO 27001, and DORA simultaneously is a coordination challenge as much as a security one.

Skypher's security questionnaire automation platform is built for exactly this environment. The AI recommendation engine maps your existing documentation to framework requirements automatically, surfacing gaps without manual cross-referencing. With import and export workflows that support every major format and connect to over 40 TPRM platforms, your compliance evidence becomes reusable across every audit cycle. Less duplication, faster responses, and a compliance program that scales with your organization rather than against it.
Frequently asked questions
Which compliance framework should my tech organization prioritize first?
Start with NIST CSF or ISO 27001 for broad coverage, then layer SOC 2 or DORA based on your regulatory environment and customer requirements. NIST and ISO foundations share 30 to 40% overlap with SOC 2, making them the most efficient starting point.
How are SOC 2 Type I and Type II reports different?
Type I evaluates whether your controls are properly designed at a single point in time, while Type II assesses whether those controls operated effectively over a defined period, typically six to twelve months, providing deeper assurance.
What makes DORA unique among compliance frameworks?
DORA covers five operational pillars and uniquely extends compliance obligations to third-party ICT providers, going well beyond traditional cybersecurity-only frameworks into full operational resilience.
Is ISO 27001 more difficult to achieve than SOC 2?
ISO 27001 is globally certifiable but resource-intensive, typically requiring 12 to 18 months, while SOC 2 is a non-certifiable audit standard that U.S.-based SaaS companies often find more accessible as a starting point.
Do compliance frameworks really help reduce data breaches?
Yes, when integrated into actual security operations, but a checkbox-only approach that prioritizes documentation over real control effectiveness provides limited protection against real-world threats.
Recommended
- Compliance Platforms: Streamlining Security and Trust
- 15 security compliance best practices to streamline audits
- Why automate compliance in 2026: benefits for finance & tech firms
- Compliance Admin: Streamline Security Questionnaire Workflow
- Why prioritize cybersecurity in AI for business 2026 | Artificial Intelligence
