TL;DR:
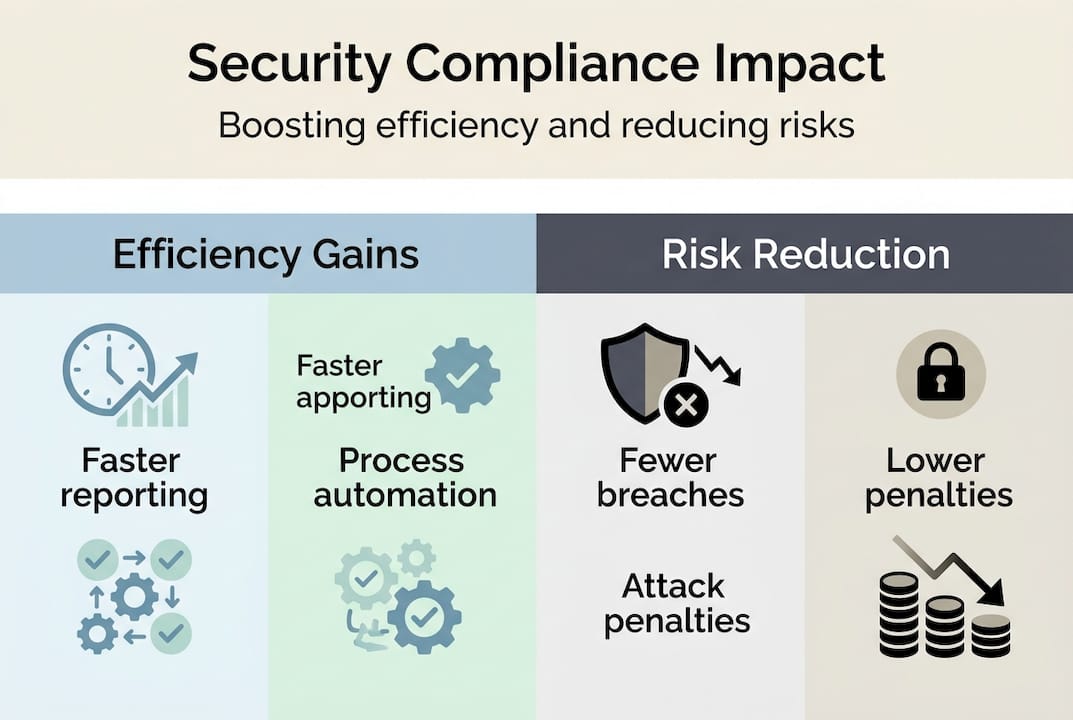
- Effective compliance reduces breaches and costs, turning security into a strategic business asset.
- Risk-based frameworks prioritize controls, increasing operational efficiency and demonstrating measurable ROI.
- Automating compliance processes accelerates documentation, reduces manual efforts, and enhances cross-team visibility.
The average data breach now costs US organizations $10.22 million, up from $5.97 million in 2023. That jump alone should reframe how IT and compliance leaders think about security programs. Compliance is not a legal formality you fulfill once a year and forget. When built correctly, it becomes a core operational asset that reduces incidents, accelerates documentation, and builds the kind of trust that wins enterprise deals. This article breaks down what effective security compliance looks like in practice, why the ROI is real, and how risk-based approaches help tech and finance organizations stop reacting and start leading.
Table of Contents
- Foundations of security compliance: Beyond checkbox audits
- Real-world benefits: Efficiency, ROI, and risk reduction
- Risk-based frameworks: Aligning resources to what matters
- Measurable outcomes and pitfalls: What success and failure look like
- A perspective: Why real compliance means real business impact
- Take the next step in security compliance efficiency
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Strategic risk reduction | Security compliance goes beyond regulations to actively reduce risk and protect organization value. |
| High ROI and efficiency | Well-implemented compliance programs deliver measurable returns and streamline operations. |
| Frameworks matter | Choosing the right framework—NIST, CIS, or ISO—enables regulatory fit and maturity-based scaling. |
| Avoid checkbox pitfalls | Treat compliance as a cultural and strategic asset, not a checklist, to maximize impact. |
Foundations of security compliance: Beyond checkbox audits
Security compliance is the process of aligning your organization's controls, policies, and practices with a defined set of standards or regulations. In finance and tech, that means satisfying requirements from bodies like the SEC, FINRA, NYDFS, GLBA, and FFIEC, among others. But the definition only scratches the surface of what compliance actually demands.
The old model treated compliance as an audit event. Teams scrambled to produce documentation, passed the review, and moved on. That approach creates a dangerous gap between what your policies say and what your systems actually do. Integrated risk management closes that gap by embedding controls into daily operations, not just annual reviews.
Understanding compliance risk meaning is the first step toward building something durable. Compliance risk is not just the risk of getting fined. It includes operational disruption, reputational damage, and loss of client trust, all of which carry financial consequences that dwarf most regulatory penalties.
The most widely adopted security compliance frameworks for tech and finance organizations include:
- NIST CSF (Cybersecurity Framework): A flexible, risk-based framework organized around five core functions: Identify, Protect, Detect, Respond, and Recover. Widely recognized by US regulators.
- CIS Controls: A prioritized set of 18 controls designed for practical implementation. Organized into Implementation Groups (IG1, IG2, IG3) based on organizational maturity.
- ISO 27001: An international standard for information security management systems (ISMS). Requires formal certification and is often demanded by enterprise clients globally.
"Frameworks like NIST, CIS, and ISO align directly with SEC, FINRA, NYDFS, GLBA, and FFIEC requirements, enabling financial organizations to avoid fines, pass examinations, and demonstrate regulatory adherence."
The key insight here is alignment. Choosing the right framework is not about picking the most prestigious standard. It is about selecting one that maps cleanly to your regulatory obligations and scales with your organization's complexity.
Real-world benefits: Efficiency, ROI, and risk reduction
Compliance programs are often framed as cost centers. The data tells a different story. Organizations that invest in structured compliance see measurable returns across multiple dimensions, from reduced breach exposure to faster audit cycles.

Third-party research makes the numbers hard to ignore. Compliance ROI from identity governance programs reached 211% over three years in Forrester's Total Economic Impact analysis. The Snyk security platform delivered 288% ROI, and Google SecOps came in at 240%, with benefits including $232K in audit cost savings and $231K in breach risk reduction per organization studied.
| Platform | ROI (3-year) | Key benefit |
|---|---|---|
| Okta Identity Governance | 211% | Reduced audit overhead, faster access reviews |
| Snyk Security Platform | 288% | Fewer vulnerabilities, faster remediation |
| Google SecOps | 240% | Lower incident response costs, improved detection |
Beyond raw ROI, compliance automation benefits show up across daily operations. Teams using structured compliance platforms consistently report:
- Faster evidence collection and documentation for audits
- Reduced time spent on manual questionnaire responses
- Lower cost per incident due to standardized response playbooks
- Improved cross-team visibility into control gaps
- Stronger vendor and client trust during due diligence
Pro Tip: Automation compounds efficiency gains over time. A team that automates questionnaire responses in year one will see the benefit multiply as their knowledge base grows and response accuracy improves with each cycle.
The business case is not theoretical. It is measurable, repeatable, and increasingly expected by boards and investors who want quantifiable evidence that risk is being managed.
Risk-based frameworks: Aligning resources to what matters
Not every organization needs to implement every control at maximum depth from day one. Risk-based frameworks exist precisely to help you prioritize. The NIST CSF uses four tiers, from Partial (Tier 1) to Adaptive (Tier 4), to benchmark how well your organization integrates cybersecurity into its risk management processes. Moving up a tier is not just a compliance milestone. It reflects a genuine shift in how your teams think about and respond to threats.
CIS Controls take a similar approach with Implementation Groups. IG1 through IG3 represent increasing levels of maturity and resource investment:
| Implementation group | Target org size | Controls focus |
|---|---|---|
| IG1 | Small, limited IT | Basic cyber hygiene (6 controls) |
| IG2 | Medium, moderate risk | Expanded detection and response (16 controls) |
| IG3 | Large, high risk | Advanced threat defense (all 18 controls) |
For most medium to large tech and finance organizations, starting at IG2 and building toward IG3 is the practical path. Security by Design principles further reinforce this by embedding security requirements into system architecture from the start, rather than bolting them on after deployment.
Here is a practical sequence for implementing a risk-based compliance framework:
- Assess your current state. Map existing controls to your chosen framework and identify gaps.
- Prioritize by risk. Focus first on controls that address your highest-probability, highest-impact threats.
- Assign ownership. Each control needs a named owner accountable for implementation and evidence.
- Automate evidence collection. Manual processes create bottlenecks. Automate wherever the tooling exists.
- Review and iterate. Schedule quarterly reviews to update your risk register and adjust priorities.
Pro Tip: Start with IG1 controls even if you are targeting IG3 maturity. The foundational hygiene controls in IG1 eliminate the most common attack vectors and give your team early wins that build momentum.
Risk-based approaches also make it easier to defend your program to leadership. Instead of reporting on how many policies you updated, you can show which risks decreased and by how much. That shift in language changes how compliance is perceived at the executive level.
For deeper context on ISO information standards, the ISO 27001 framework adds a formal management system layer that is particularly valuable when your client base spans multiple geographies with different regulatory expectations.
Measurable outcomes and pitfalls: What success and failure look like
The evidence for compliance effectiveness is increasingly empirical. Organizations that adopted Security by Design principles in finance and healthcare reported a 54% reduction in critical vulnerabilities, 50% faster compliance documentation, and 39% lower incident response costs. These are not projections. They are measured outcomes from real deployments.
For IT and compliance leaders, these numbers translate directly into budget justification, headcount planning, and vendor selection criteria. If your current program cannot demonstrate similar metrics, that is a signal worth acting on.
Effective compliance risk mitigation programs share a few common traits: they are continuous rather than periodic, they integrate with existing tooling rather than running in parallel, and they treat third-party risk as seriously as internal risk.
Common pitfalls that undermine otherwise well-designed programs include:
- Checkbox mentality. Treating controls as items to mark complete rather than behaviors to sustain.
- Ignoring third-party risk. Vendors and partners are frequently the entry point for breaches. Finance regulatory guidance consistently flags this as a critical gap.
- Underestimating cloud complexity. Hybrid and multi-cloud environments require control mappings that many legacy frameworks do not address out of the box.
- Over-indexing on certification cost. ISO 27001 certification is valuable, but organizations sometimes pursue it before their internal controls are mature enough to sustain it.
- Siloed ownership. When compliance lives only in the legal or IT team, it fails to influence the product and engineering decisions where most risk originates.
"Integration and culture matter more than framework selection. Organizations that embed compliance into how teams build and operate consistently outperform those that treat it as a separate governance function."
The pattern across successful programs is consistent: compliance works when it is woven into operations, not layered on top of them.
A perspective: Why real compliance means real business impact
Here is something most compliance guides will not tell you: the organizations that treat compliance as a strategic function, not a regulatory obligation, tend to move faster than their peers, not slower. When your controls are well-documented, your risk posture is clear, and your teams know exactly what is expected, you spend less time firefighting and more time building.
The conventional wisdom is that compliance slows innovation. In our experience working with tech and finance organizations, the opposite is true when compliance is done right. A mature security automation for compliance program means your engineers do not have to reinvent security decisions on every project. Your sales team can answer vendor questionnaires in hours, not weeks. Your leadership can walk into a board meeting with quantified risk data instead of qualitative reassurances.
The shift from audit-driven to risk-driven compliance is not just a methodology change. It is a cultural one. Teams that internalize risk thinking become more adaptable, more proactive, and more credible with clients and regulators alike. That credibility is a competitive advantage that no audit report can manufacture. Build compliance into your operational DNA, and it stops being a cost center. It becomes a growth enabler.
Take the next step in security compliance efficiency
Understanding the frameworks and ROI of compliance is one thing. Executing it efficiently at scale is another challenge entirely, especially when security questionnaires from clients and partners consume hours of your team's time every week.

Skypher is built specifically for this problem. Our security questionnaire automation platform uses AI to complete even 200-question reviews in under a minute, drawing from your security knowledge base with high accuracy and full audit trails. With integrations across 40+ TPRM platforms, Slack, MS Teams, and major document repositories, Skypher fits directly into your existing compliance workflow. If you are serious about turning compliance into a competitive advantage, see what Skypher can do for your team.
Frequently asked questions
How does security compliance lower breach costs?
Security compliance frameworks reduce breach costs by standardizing controls, ensuring more effective risk mitigation, and enabling faster detection and response, all of which limit the scope and duration of incidents.
Which compliance frameworks are most suitable for tech and finance?
NIST CSF, CIS Controls, and ISO 27001 are the most widely adopted by tech and finance organizations because they align with finance regulations like SEC, FINRA, and NYDFS while scaling across different organizational sizes.
Can compliance programs really improve operational efficiency?
Yes. Structured compliance programs deliver measurable efficiency gains, with research showing 50% faster documentation and 39% lower incident response costs in organizations that implement Security by Design principles.
What are the main pitfalls in compliance efforts?
The most damaging pitfalls are treating compliance as a checkbox exercise, underestimating third-party risk oversight, and failing to adapt control frameworks to cloud or hybrid infrastructure environments.
How can organizations measure ROI from compliance?
ROI is best measured through reduced incident frequency, audit cost savings, and efficiency benchmarks. Research shows 211% ROI over three years from identity governance alone, making the financial case straightforward to build.
Recommended
- Key compliance frameworks: Streamlining security for tech and finance
- Compliance Risk Meaning: Impact on Security Reviews
- What Is Compliance Risk? 70% Cite Regulation Impact in 2026
- What Is Compliance Risk? 40% Fewer Violations Proven
- The ultimate operational efficiency checklist for SMBs
- Top 5 IT Security Essentials Every Business Needs in 2026 - Carsonix Inc.
