Skypher Blog
SOC 2 Type 1: Fast-Track Security Assurance for SaaS
SOC 2 Type 1 offers rapid compliance for SaaS vendors. Learn its definition, audit steps, cost factors, and how it compares to Type 2 certification.

GDPR Software Compliance: Key Actions for SaaS Success
GDPR software compliance empowers SaaS firms by clarifying requirements, automation benefits, user rights, risks, and legal essentials for security teams.
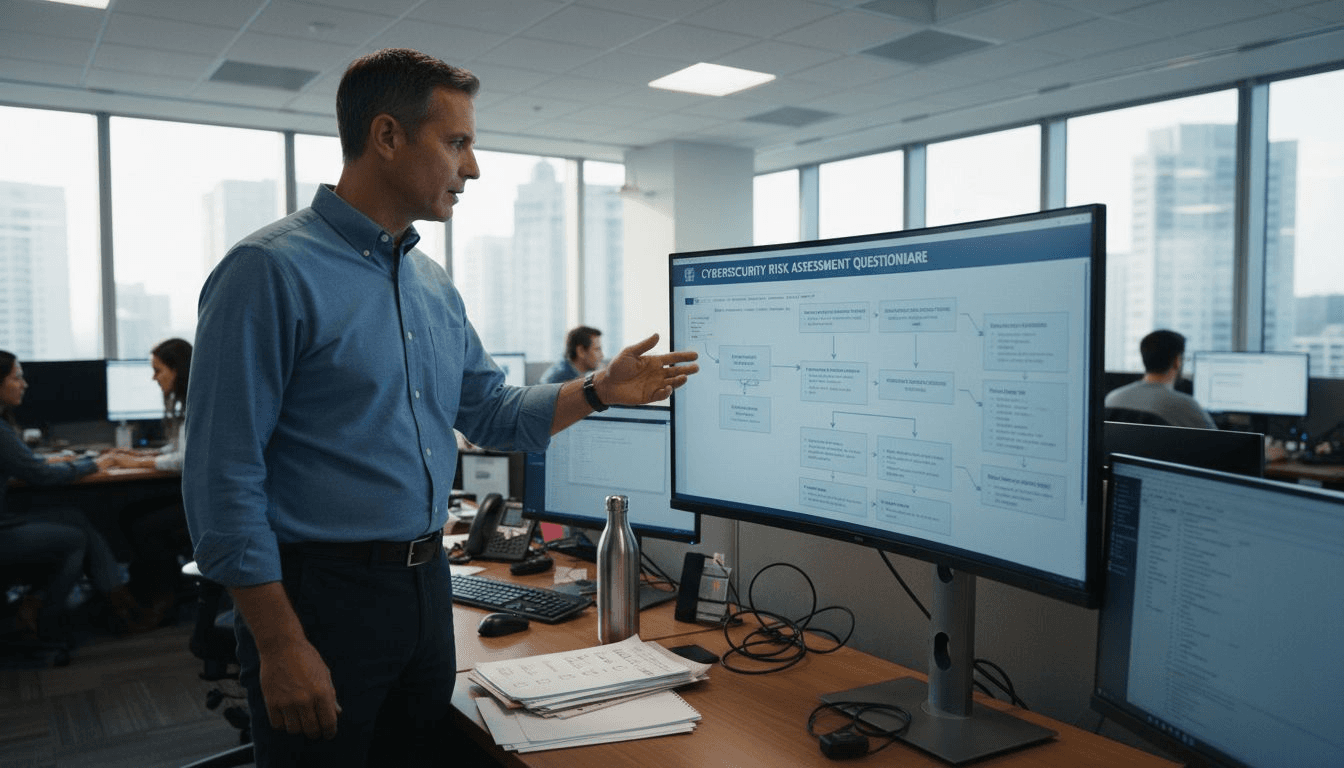
Security Build Guide for Streamlined Questionnaire Automation
Discover a step-by-step security build process for automating security questionnaire responses, streamlining collaboration, and ensuring compliance for tech teams.
SOC 3 Reports: Ensuring Public Trust in SaaS
SOC 3 reports build customer trust for SaaS by verifying security controls, clarifying differences from SOC 2, and outlining audit essentials.
GRC Tools: Transforming Enterprise Security Compliance
GRC tools streamline risk, compliance, and security processes. Learn types, real-world uses, integration challenges, and strategies for enterprise ROI.
SOC 2 Audit Cost Explained: Key Factors for 2026
Learn the true cost of SOC 2 audits, from audit types to hidden fees and cost-saving strategies for SaaS and tech firms in 2026.
How to Streamline Questionnaire for Vendors Efficiently
Learn to automate and simplify the security questionnaire for vendors. Follow step-by-step actions to improve speed, accuracy, and client trust in your process.
ISO 27001: Impact on Tech Security Compliance
ISO 27001 explained for tech leaders—definition, certification steps, controls, business value, and how ISO 27001 boosts trust in vendor security.
7 Key Steps for Effective Vendors Review in Cybersecurity
Discover 7 actionable steps for vendors review that help cybersecurity teams automate risk management and security questionnaire processes efficiently.