TL;DR:
- Vendor questionnaire compliance requires evidence verification, not just self-reports or checkboxes.
- Automating and tailoring assessments enhances accuracy, scalability, and ongoing risk monitoring.
- Moving beyond static forms and embracing AI-driven solutions improves overall third-party security posture.
Most organizations treat vendor security questionnaires as a formality. Fill out the form, collect the responses, file them away, and move on. The problem is that this approach leaves critical gaps in your risk posture that only become visible after a breach or a failed audit. Vendor questionnaire compliance is not a checkbox exercise. It is a structured, evidence-backed process that directly shapes how your organization understands, manages, and responds to third-party risk. This article breaks down what the term actually means, how the process works end to end, where most programs break down, and where AI and automation are taking the field in 2026.
Table of Contents
- What vendor questionnaire compliance means
- How vendor security questionnaires work in practice
- Challenges and common pitfalls in questionnaire compliance
- New trends: Automation, AI, and beyond in vendor compliance
- What most compliance programs get wrong—and how to fix it
- Simplify compliance with automated solutions
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Compliance is ongoing | Vendor questionnaire compliance is a continual process, not a one-time task. |
| Risk-based tiers work best | Tailoring questionnaire depth to vendor risk reduces fatigue and improves results. |
| Automation adds value | AI and automation speed up workflows and increase accuracy in compliance programs. |
| Evidence is essential | Always require evidence, not just self-reported answers, for strong compliance. |
What vendor questionnaire compliance means
Vendor questionnaire compliance is the process of verifying that external vendors meet your organization's required security, privacy, and business continuity controls. That verification happens through standardized or customized questionnaires issued during procurement, onboarding, contract renewal, or whenever a vendor's risk profile changes significantly.
The term is often used loosely, but it has a precise meaning in risk management. Compliance here does not mean the vendor simply answered all the questions. It means the vendor's answers were reviewed, validated against evidence, and determined to satisfy your control requirements. A vendor who answers "yes" to every question without supporting documentation is not compliant. They are unverified.
Common questionnaire domains typically span governance and organizational security, access control, data protection, incident response, and third-party management. Certifications like SOC 2, ISO 27001, HIPAA, and GDPR compliance are standard areas of inquiry. Understanding why security questionnaires matter to your overall risk posture is the starting point for building a program that actually works.
Three widely used frameworks define what a thorough questionnaire looks like:
- SIG (Standardized Information Gathering): Covers 18 risk domains and is common in enterprise procurement.
- CAIQ (Consensus Assessments Initiative Questionnaire): Focused on cloud security, maintained by the Cloud Security Alliance.
- VSA (Vendor Security Alliance Questionnaire): Ranges from 20 to over 300 questions depending on vendor criticality.
Here is a quick reference for how common domains map to business risk:
| Domain | Primary risk addressed | Common evidence requested |
|---|---|---|
| Governance | Accountability and policy gaps | Security policies, org charts |
| Access control | Insider threat and privilege misuse | IAM screenshots, audit logs |
| Data protection | Breach and leakage risk | Encryption configs, DLP reports |
| Incident response | Recovery capability | IR plan, past incident records |
| Compliance certifications | Regulatory exposure | SOC 2 reports, ISO certificates |
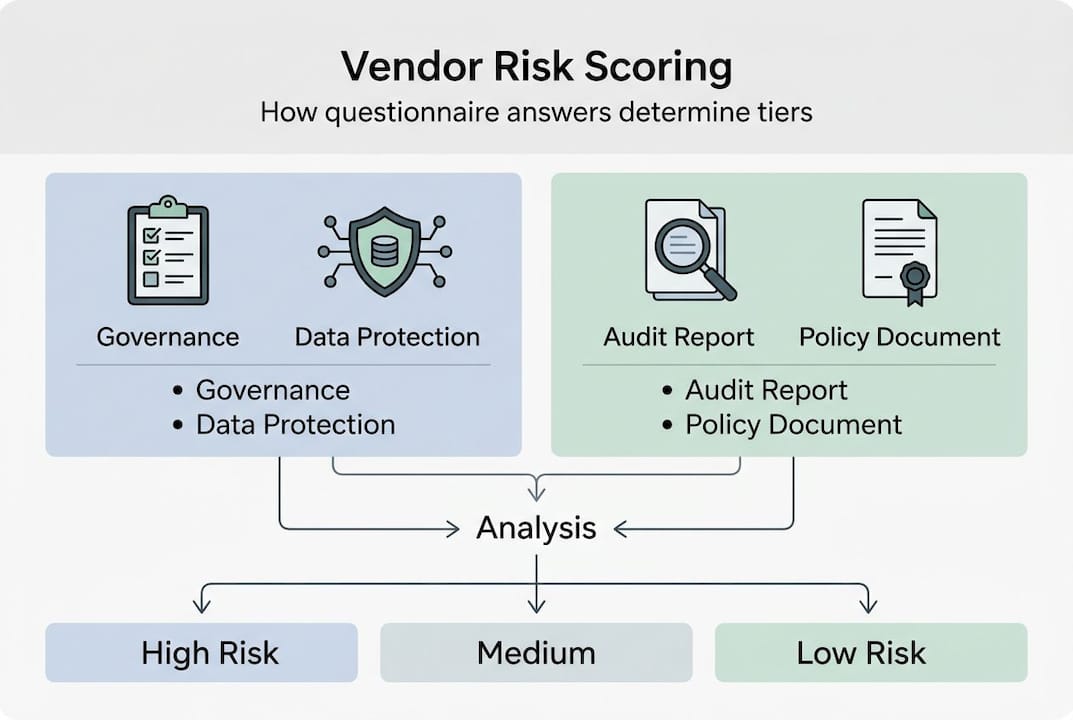
Answers collected through these domains feed directly into vendor risk scoring, which determines what tier a vendor falls into and what level of oversight they receive. Without this structure, questionnaire compliance becomes noise rather than signal.
How vendor security questionnaires work in practice
Knowing what compliance means is one thing. Running the process without gaps is another. Here is how a well-structured questionnaire workflow operates at organizations that treat vendor risk seriously.
- Risk profile assessment: Before sending anything, determine the vendor's risk tier based on data access, system criticality, and regulatory exposure.
- Template selection: Choose a base framework (SIG, CAIQ, VSA) that fits the vendor's category and risk level.
- Customization: Add or remove questions based on the vendor's specific services, data handling, and your industry requirements.
- Distribution: Send the questionnaire through a secure channel, ideally with a defined response deadline and a point of contact on both sides.
- Evidence collection: Require vendors to attach supporting documentation for high-risk responses, not just written answers.
- Review and validation: Your team reviews answers and flags inconsistencies, missing evidence, or concerning controls.
- Risk scoring: Responses are scored and weighted by domain importance. One practical scoring model: Risk Score = (Data Access x 3) + (System Access x 3) + (Criticality x 2) + (Regulatory Exposure x 2).
- Remediation and follow-up: Vendors with gaps receive remediation requests with defined timelines.
- Contract integration: Key security requirements confirmed through the questionnaire are embedded in the vendor contract.
Questionnaire responses are scored, verified with evidence, and integrated into risk tiering to create a defensible record. Understanding the vendor risk manager workflow can help your team design a process that scales without sacrificing accuracy.
The critical fork in this process is whether you use a one-size-fits-all template or a risk-based approach.
| Approach | Depth | Time to complete | Accuracy | Best for |
|---|---|---|---|---|
| One-size-fits-all | Uniform | Moderate | Low for edge cases | Basic vendor lists |
| Risk-based | Tiered | Variable | High | Critical or regulated vendors |
Pro Tip: Require at least one piece of verifiable evidence for every high-risk control response. Written answers without documentation are assumptions, not assurance. And always include confirmed security requirements in your contracts. If it is not in writing, it is not enforceable.
Challenges and common pitfalls in questionnaire compliance
Even teams with a defined process run into serious problems. Most of the failures are predictable and preventable once you know where to look.
The most common pitfalls include:
- Generic questions: Broad questions produce broad answers. "Do you have a data protection policy?" tells you almost nothing without knowing what the policy covers and when it was last updated.
- Self-reported answers without verification: Vendors answer in their own interest. Without evidence requirements, compliance is based on trust, not assurance.
- Outdated templates: A questionnaire designed in 2021 may not address current cloud configurations, AI tool usage, or updated regulatory requirements.
- Questionnaire fatigue: Sending the same 300-question form to every vendor, including the low-risk ones, exhausts vendor contacts and reduces response quality over time.
- Missing fourth-party risk: Your vendor's vendors create exposure you cannot see unless you ask. Fourth-party risk is a growing blind spot in most programs.
"A single one-size-fits-all questionnaire creates more risk than it removes."
One-size-fits-all questionnaires are ineffective for low-risk vendors, and the challenges extend to unverified self-reports, outdated forms, and fourth-party risks that go unaddressed. Static, one-and-done compliance is also structurally broken. A vendor who passes your questionnaire on day one is not automatically compliant on day 365. Systems change. Teams change. Threat landscapes change.

The gap between ISO 27001 vs SOC 2 requirements, for example, is significant enough that treating them as interchangeable in your questionnaire design leads to real coverage gaps depending on your regulatory environment.
Pro Tip: Tailor questionnaire depth to vendor criticality. A cloud provider processing customer financial data needs a fundamentally different assessment than a vendor supplying office supplies. Match the rigor to the actual risk, not to the convenience of sending one standard form.
New trends: Automation, AI, and beyond in vendor compliance
The traditional approach to vendor questionnaire compliance is under significant pressure. Manually reviewing hundreds of vendor responses, chasing down evidence, and updating templates every 12 months does not scale. The field is shifting fast.
75% of organizations now use customized questionnaire approaches, and automation, trust exchanges, and multi-source ratings are overtaking static forms as the primary tools for third-party due diligence. Traditional questionnaires are widely recognized as broken at scale.
Here is what the shift looks like in practice:
| Factor | Traditional approach | AI-driven approach |
|---|---|---|
| Speed | Days to weeks | Hours to minutes |
| Accuracy | Depends on reviewer | Consistent, model-driven |
| Scalability | Linear with headcount | Scales without added staff |
| Vendor fatigue | High | Reduced via smart forms |
| Continuous monitoring | Annual or ad hoc | Real-time or near-real-time |
Key trends reshaping the space include:
- AI-powered answer analysis: AI tools review vendor responses for inconsistencies, flag incomplete answers, and surface emerging risk signals that a human reviewer would likely miss.
- Multi-source data integration: Rather than relying solely on vendor self-reports, leading programs combine questionnaire data with external security ratings, shared assessment repositories, and industry trust exchanges.
- Continuous monitoring: One-time assessments are being replaced by ongoing feeds that alert your team when a vendor's risk profile changes between formal review cycles.
- Evidence-driven checklists: Instead of yes/no answers, modern questionnaires require linked documentation, making validation faster and audit records stronger.
- Automatic risk tier adjustment: As new data comes in, AI models recalculate a vendor's risk score without waiting for the next annual review cycle.
Exploring AI in compliance questionnaires and the AI-driven questionnaire essentials shaping 2026 programs gives a clear picture of where the industry is heading and what your team should be building toward now.
What most compliance programs get wrong—and how to fix it
Most vendor questionnaire programs are built around the fear of an audit, not around the goal of actual security. That distinction matters more than most teams realize. Programs designed to produce a paper trail generate exactly that. Programs designed to identify and reduce risk produce something genuinely useful.
The highest-performing compliance teams we see share one trait: they treat vendor questionnaire compliance as an ongoing partnership, not a one-off transaction. They revisit assessments when vendor environments change. They require evidence not as a formality but as a genuine control verification tool. And they write security requirements into contracts so there is a legal mechanism to enforce what the questionnaire revealed.
Good questions are specific and verifiable, always require evidence, and integrate requirements into contracts to enforce compliance. The organizations doing this well use AI-driven compliance transformation not to replace judgment but to scale it.
"A strong compliance program evolves. Static forms are a sign of risk, not maturity."
If your questionnaire looks the same as it did two years ago, that is a risk indicator, not a sign of stability.
Simplify compliance with automated solutions
Managing vendor questionnaire compliance at scale is genuinely hard without the right infrastructure behind it.

Skypher's automated questionnaire solution gives risk and compliance teams the tools to run structured, evidence-backed vendor assessments without the manual bottlenecks. From AI-powered answer analysis to risk scoring, evidence collection, and contract integration, every part of the workflow is built to reduce time and improve accuracy. Skypher's AI-powered compliance recommendations surface risks your team might otherwise miss and help you prioritize remediation where it matters most. If you are ready to move beyond spreadsheets and static forms, Skypher is built for exactly that.
Frequently asked questions
What does a vendor questionnaire typically include?
A standard vendor questionnaire covers governance, access controls, data protection, incident response, and compliance certifications like SOC 2 or ISO 27001. The depth and format vary based on vendor risk tier and industry requirements.
How are questionnaire responses validated?
Responses should be verified with documentation, audits, or direct evidence, not just self-reported answers. Responses are scored and integrated into risk tiering only after validation is complete.
Why not use the same questionnaire for every vendor?
A one-size-fits-all approach misses key risks for critical vendors and overburdens low-risk ones. One-size-fits-all questionnaires are ineffective and often lead to vendor fatigue and lower-quality responses over time.
How does automation improve questionnaire compliance?
Automation streamlines evidence collection, cuts review time significantly, and enables continuous risk monitoring between formal assessment cycles. 75% of programs now use customized or automated approaches for exactly this reason.
What are examples of risk-based tiering in vendor compliance?
Risk-based tiering ranks vendors as critical, high, medium, or low based on data access, system criticality, and regulatory impact. Verification methods like audits, penetration tests, and shared assessments are then matched to each tier for focused, proportionate oversight.
